User Guide
Page 10
... 4.8.3 Testing the DDNS Setting 46 4.9 Configuring Static Route for Routing to Another Network 46 4.10 Remotely Managing Your WiMAX Device 48 4.11 Changing Certificate to Communicate with Other Networks 49 4.12 Using Virtual Networks ...50 4.12.1 Scenario 1 ...51 4.12.2 Scenario 2 ...52 4.12.3 Scenario 3 ...54 4.12.4 Scenario 4 ...56 4.12.5 Scenario 5 ...58 Part...
... 4.8.3 Testing the DDNS Setting 46 4.9 Configuring Static Route for Routing to Another Network 46 4.10 Remotely Managing Your WiMAX Device 48 4.11 Changing Certificate to Communicate with Other Networks 49 4.12 Using Virtual Networks ...50 4.12.1 Scenario 1 ...51 4.12.2 Scenario 2 ...52 4.12.3 Scenario 3 ...54 4.12.4 Scenario 4 ...56 4.12.5 Scenario 5 ...58 Part...
User Guide
Page 17
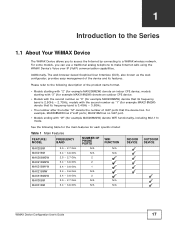
...Internet by connecting to make Internet calls using the WiMAX Device's Voice over IP (VoIP) communication capabilities. Additionally, The web browser-based Graphical User Interface (GUI), also known as the web... MAX318M2W) denote an outdoor CPE device. • Models with "W" (for each specific model: Table 1 Main Features FEATURE / MODEL FREQUENCY BAND MAX208M MAX218M MAX208M2W MAX218M2W MAX218M1W MAX218MW MAX318M2W MAX308M MAX318M 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz NUMBER OF PHONE PORTS N/A N/A ...
...Internet by connecting to make Internet calls using the WiMAX Device's Voice over IP (VoIP) communication capabilities. Additionally, The web browser-based Graphical User Interface (GUI), also known as the web... MAX318M2W) denote an outdoor CPE device. • Models with "W" (for each specific model: Table 1 Main Features FEATURE / MODEL FREQUENCY BAND MAX208M MAX218M MAX208M2W MAX218M2W MAX218M1W MAX218MW MAX318M2W MAX308M MAX318M 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz NUMBER OF PHONE PORTS N/A N/A ...
User Guide
Page 25
... in your home or office connect to the WiMAX Device. 2 Set up your WiMAX Device's broadcast frequency, which is the radio channel it uses to communicate with the ISP's base station. 3 Set up your WiMAX Device's login options, which are used to connect your LAN to the ISP's network and verify...
... in your home or office connect to the WiMAX Device. 2 Set up your WiMAX Device's broadcast frequency, which is the radio channel it uses to communicate with the ISP's base station. 3 Set up your WiMAX Device's login options, which are used to connect your LAN to the ISP's network and verify...
User Guide
Page 33
... the network will be using to join the network: Open System or Shared Key. Key 1 - 4 Pick one channel from 1 to use for wireless communications with the WiMAX Device. The key can be in the step above (64-bit or 128-bit). WPA Mode Select either Hexagecimal (HEX) or ASCII... the length must match the length picked in either WPA, WPA2 or Auto (WPA or WPA2). Encryption Type Select the type of authentication used to communicate: 802.11 B/G mixed, 802.11 B only, 802.11 G only, 802.11 N only, or 802.11 B/G/ N mixed. WLAN Channel Select one of the encryption key...
... the network will be using to join the network: Open System or Shared Key. Key 1 - 4 Pick one channel from 1 to use for wireless communications with the WiMAX Device. The key can be in the step above (64-bit or 128-bit). WPA Mode Select either Hexagecimal (HEX) or ASCII... the length must match the length picked in either WPA, WPA2 or Auto (WPA or WPA2). Encryption Type Select the type of authentication used to communicate: 802.11 B/G mixed, 802.11 B only, 802.11 G only, 802.11 N only, or 802.11 B/G/ N mixed. WLAN Channel Select one of the encryption key...
User Guide
Page 35
... WiMAX Device's features. For field descriptions for individual screens, see page 46 • Remotely Managing Your WiMAX Device on page 48 • Changing Certificate to Communicate with pointers for configuring the WiMAX Device to connect to an ISP. 1 Connect the WiMAX Device to the ISP's authentication servers. See Section 6.2 on page...
... WiMAX Device's features. For field descriptions for individual screens, see page 46 • Remotely Managing Your WiMAX Device on page 48 • Changing Certificate to Communicate with pointers for configuring the WiMAX Device to connect to an ISP. 1 Connect the WiMAX Device to the ISP's authentication servers. See Section 6.2 on page...
User Guide
Page 42
... it through the WiMAX Device. 4.7 Allowing Internet Users to the Xbox 360. His friends invited him to play online games with other fields set to communicate and play with them on Xbox LIVE. You may be able to check the IP address on the WiMAX network through the Xbox 360 console...
... it through the WiMAX Device. 4.7 Allowing Internet Users to the Xbox 360. His friends invited him to play online games with other fields set to communicate and play with them on Xbox LIVE. You may be able to check the IP address on the WiMAX network through the Xbox 360 console...
User Guide
Page 49
...new ISP. In the EAP Supplicant section, click each Browse button and locate the security certificates that were provided by your device to communicate with other network servers. Chapter 4 Tutorials 2 Select Enable in both HTTP Server and HTTPS Server sections and leave the Port Number...443". 3 Select Allow Connection from the local network but also the WAN network (Internet). 4 Click Save. 4.11 Changing Certificate to Communicate with Other Networks This tutorial shows you how to the WiMAX > Profile > Authentication Settings screen. 1 Open the Maintenance > Remote MGMT > HTTP screen...
...new ISP. In the EAP Supplicant section, click each Browse button and locate the security certificates that were provided by your device to communicate with other network servers. Chapter 4 Tutorials 2 Select Enable in both HTTP Server and HTTPS Server sections and leave the Port Number...443". 3 Select Allow Connection from the local network but also the WAN network (Internet). 4 Click Save. 4.11 Changing Certificate to Communicate with Other Networks This tutorial shows you how to the WiMAX > Profile > Authentication Settings screen. 1 Open the Maintenance > Remote MGMT > HTTP screen...
User Guide
Page 68
... stations connect to the network through a single base station (BS), as an AAA (Authentication, Authorization and Accounting) server to subscriber stations and mobile stations, and communicates with other base stations.
... stations connect to the network through a single base station (BS), as an AAA (Authentication, Authorization and Accounting) server to subscriber stations and mobile stations, and communicates with other base stations.
User Guide
Page 91
... enter in the form of an information sheet, when s/he signs up . DNS Server Address DNS (Domain Name System) is for mapping a domain name to communicate across the network. IP Address IP addresses identify individual devices on . DHCP A DHCP (Dynamic Host Configuration Protocol) server can assign your WiMAX Device an IP...
... enter in the form of an information sheet, when s/he signs up . DNS Server Address DNS (Domain Name System) is for mapping a domain name to communicate across the network. IP Address IP addresses identify individual devices on . DHCP A DHCP (Dynamic Host Configuration Protocol) server can assign your WiMAX Device an IP...
User Guide
Page 94
... UPnP compatible device installed on your intention. Network information and configuration may communicate freely with UPnP The automated nature of an application that device. UPnP and ZyXEL ZyXEL has received UPnP certification from the official UPnP Forum (http://www.upnp.org). ZyXEL's UPnP implementation supports IGD 1.0 (Internet Gateway Device). Content filtering is an example...
... UPnP compatible device installed on your intention. Network information and configuration may communicate freely with UPnP The automated nature of an application that device. UPnP and ZyXEL ZyXEL has received UPnP certification from the official UPnP Forum (http://www.upnp.org). ZyXEL's UPnP implementation supports IGD 1.0 (Internet Gateway Device). Content filtering is an example...
User Guide
Page 95
... Protocol • Bridge - This puts the WiMAX Device in bridge mode, acting as shown next. Select this to use their own internal IP addresses while communicating with devices on the LAN to manually enter the IP address the WiMAX Device uses. • From ISP - WiMAX Device Configuration User's Guide 95
... Protocol • Bridge - This puts the WiMAX Device in bridge mode, acting as shown next. Select this to use their own internal IP addresses while communicating with devices on the LAN to manually enter the IP address the WiMAX Device uses. • From ISP - WiMAX Device Configuration User's Guide 95
User Guide
Page 112
... helps build FTP sessions through the WiMAX Device's NAT. 112 WiMAX Device Configuration User's Guide Enter the IP address of your WiMAX Device for audio communications) and helps build H.323 sessions through the WiMAX Device's NAT. Figure 61 ALG Screen This screen contains the following fields: Table 42 DMZ LABEL DMZ...
... helps build FTP sessions through the WiMAX Device's NAT. 112 WiMAX Device Configuration User's Guide Enter the IP address of your WiMAX Device for audio communications) and helps build H.323 sessions through the WiMAX Device's NAT. Figure 61 ALG Screen This screen contains the following fields: Table 42 DMZ LABEL DMZ...
User Guide
Page 140
... field, type the IP address of your computer in user) and can initiate the VPN tunnel. • Responder - Choose this field. A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. For example, in "0x0123456789ABCDEF", "0x" denotes that best describes your pre-shared key in the IKE SA. Chapter 8 Security This...
... field, type the IP address of your computer in user) and can initiate the VPN tunnel. • Responder - Choose this field. A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. For example, in "0x0123456789ABCDEF", "0x" denotes that best describes your pre-shared key in the IKE SA. Chapter 8 Security This...
User Guide
Page 143
... options from the drop-down list box. Subnet Mask Remote Port If Subnet address is also slower. Both AH and ESP increase processing requirements and communications latency (delay). Longer keys require more processing power, resulting in this field. Authentication Select which key size and encryption algorithm to authenticate packet data. Select...
... options from the drop-down list box. Subnet Mask Remote Port If Subnet address is also slower. Both AH and ESP increase processing requirements and communications latency (delay). Longer keys require more processing power, resulting in this field. Authentication Select which key size and encryption algorithm to authenticate packet data. Select...
User Guide
Page 145
...IP header to use of the original IP header in the packet. Tunnel Mode Tunnel mode encapsulates the entire IP packet to gateway communications. Key Management Key management allows you to determine whether to verify the integrity of the entire packet by use of portions of AH... IKE (ISAKMP) or manual key configuration in the IP packet. Tunnel mode is fundamentally an IP tunnel with authentication and encryption. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of operation for gateway to...
...IP header to use of the original IP header in the packet. Tunnel Mode Tunnel mode encapsulates the entire IP packet to gateway communications. Key Management Key management allows you to determine whether to verify the integrity of the entire packet by use of portions of AH... IKE (ISAKMP) or manual key configuration in the IP packet. Tunnel mode is fundamentally an IP tunnel with authentication and encryption. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of operation for gateway to...
User Guide
Page 147
... either the source or destination address with authentication, the packet contents (in remote access situations where the address of security when the communicating parties are not encrypted. The VPN device at the receiving end doesn't know by computing its destination address is incompatible with NAT ...doesn't match. This mode features identity protection (your identity is not revealed in the middle, so it eliminates several steps when the communicating parties are performed over the combination of the sending VPN gateway, and its own hash value, and complain that the data has ...
... either the source or destination address with authentication, the packet contents (in remote access situations where the address of security when the communicating parties are not encrypted. The VPN device at the receiving end doesn't know by computing its destination address is incompatible with NAT ...doesn't match. This mode features identity protection (your identity is not revealed in the middle, so it eliminates several steps when the communicating parties are performed over the combination of the sending VPN gateway, and its own hash value, and complain that the data has ...
User Guide
Page 150
...-bit, 1024-bit 1536-bit, 2048-bit, and 3072-bit Diffie-Hellman groups are supported. Chapter 8 Security 8.12.8 Pre-Shared Key A pre-shared key identifies a communicating party during a phase 1 IKE negotiation (see Section 8.12.3 on page 146 for more on IKE phases). It is called "pre-shared" because you have a shared...) Key Groups Diffie-Hellman (DH) is not authenticated. Diffie-Hellman is used within IKE SA setup to share it with another party before you can communicate with them over an unsecured...
...-bit, 1024-bit 1536-bit, 2048-bit, and 3072-bit Diffie-Hellman groups are supported. Chapter 8 Security 8.12.8 Pre-Shared Key A pre-shared key identifies a communicating party during a phase 1 IKE negotiation (see Section 8.12.3 on page 146 for more on IKE phases). It is called "pre-shared" because you have a shared...) Key Groups Diffie-Hellman (DH) is not authenticated. Diffie-Hellman is used within IKE SA setup to share it with another party before you can communicate with them over an unsecured...
User Guide
Page 155
See Section 10.8 on the method supported and allowed by both of the communication peers to determine if the call session is a list of speed dial numbers. Figure 87 Speed Dial The following table describes the labels in the ...
See Section 10.8 on the method supported and allowed by both of the communication peers to determine if the call session is a list of speed dial numbers. Figure 87 Speed Dial The following table describes the labels in the ...
User Guide
Page 158
...) through Network Address Translators) allows the WiMAX Device to the WiMAX Device. 158 WiMAX Device Configuration User's Guide See RFC 3489 for peer-to-peer communications even though it is using client device C. 1 The client device (A in the SIP data stream. Chapter 10 The VoIP Account Screens SIP User Agent A SIP...
...) through Network Address Translators) allows the WiMAX Device to the WiMAX Device. 158 WiMAX Device Configuration User's Guide See RFC 3489 for peer-to-peer communications even though it is using client device C. 1 The client device (A in the SIP data stream. Chapter 10 The VoIP Account Screens SIP User Agent A SIP...
User Guide
Page 164
... action after it reaches half of the session expiry time. Session Timer When an incoming call will terminate automatically. The WiMAX Device will use when communicating with the SIP server. Enter the minimum session expiry time in seconds for the 2nd and 3rd codecs if your VoIP service provider only gave...
... action after it reaches half of the session expiry time. Session Timer When an incoming call will terminate automatically. The WiMAX Device will use when communicating with the SIP server. Enter the minimum session expiry time in seconds for the 2nd and 3rd codecs if your VoIP service provider only gave...