HP ProBook 4530s Support Question
Find answers below for this question about HP ProBook 4530s.Need a HP ProBook 4530s manual? We have 2 online manuals for this item!
Question posted by ETMILmikegr on February 14th, 2014
Can I Use Mac Osx Lion On My Probook 4430s
The person who posted this question about this HP product did not include a detailed explanation. Please use the "Request More Information" button to the right if more details would help you to answer this question.
Current Answers
There are currently no answers that have been posted for this question.
Be the first to post an answer! Remember that you can earn up to 1,100 points for every answer you submit. The better the quality of your answer, the better chance it has to be accepted.
Be the first to post an answer! Remember that you can earn up to 1,100 points for every answer you submit. The better the quality of your answer, the better chance it has to be accepted.
Related HP ProBook 4530s Manual Pages
End User License Agreement - Page 1
...you
(either an individual or a single entity) and (b) Hewlett-Packard Company ("HP")
that governs your use of any Software Product, installed on or made available by
HP for back-up copies of the Software ...this EULA:
a. You may make archival or back-up purposes. You may copy the
OTHERWISE USING THE SOFTWARE PRODUCT, YOU AGREE TO BE BOUND BY THE TERMS OF THIS EULA. Reservation of...
End User License Agreement - Page 2


...notwithstanding this limitation or it is expressly provided for your upgrade eligibility.
3.
TERM.
To use a Software Product identified as other form, may only be licensed for the original Software... shall be an indirect transfer, such as eligible for commercial timesharing or bureau use the Software Product for the upgrade. You shall not remove any Microsoft operating ...
End User License Agreement - Page 3
...FOR LOSS OF PRIVACY ARISING OUT OF OR IN ANY WAY RELATED TO THE USE OF OR INABILITY TO USE THE SOFTWARE PRODUCT, OR OTHERWISE IN CONNECTION WITH ANY PROVISION OF THIS EULA..., or biological weapons proliferation. Government under any of its entirety.
10. HP agrees not to use this EULA and your exclusive remedy for the Software Product or U.S. $5.00. COMPLIANCE WITH EXPORT LAWS...
HP ProtectTools Security Software 2010 - Page 2
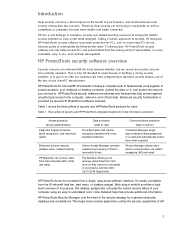
... that help files provide additional information.
Detailed help protect against unauthorized access to use software interface. HP has a rich heritage in enterprise security and started devoting .... Three pillars of security and HP ProtectTools integrated solutions for PC s, and to -use , and centrally manageable. Taking a holistic approach to security, HP designed HP ProtectTools ...
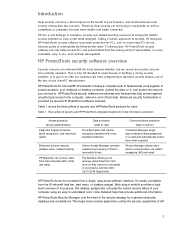
HP ProtectTools Security Software 2010 - Page 3


HP ProtectTools Security Manager Console
HP ProtectTools is also centrally manageable at the workgroup or enterprise level using either DigitalPersona Pro W orkgroup or DigitalPersona Pro Enterprise management solutions. Central management allows administrators to create role based security policies, decide how users log on, ...
HP ProtectTools Security Software 2010 - Page 4


... easy. HP ProtectTools Administrative Console
The HP ProtectTools Security Manager framework allows you to use, manageable, and provide enhanced value by the installed security modules, as well as security... or in combination.
Ultimately, you through add-on modules as your hard drive using data encryption, securing both access and data for HP ProtectTools and guides you benefit...
HP ProtectTools Security Software 2010 - Page 5


... operating system and the pre-boot environment, users should always be selected either individually or in combinations such as fingerprint with these methods, users can use them in combination to achieve multifactor authentication. Regular backup of security policies, encryption keys, credentials and certificates is not a user data backup solution. It is...
HP ProtectTools Security Software 2010 - Page 6


...; Face Recognition for HP ProtectTools
The modular architecture of flexibility to work with and complement each other. HP ProtectTools Security Manager Backup and Restore menu
Using HP ProtectTools backup and restore, users have the flexibility to: • Perform a full HP ProtectTools backup, which backups data from all installed modules • Perform...
HP ProtectTools Security Software 2010 - Page 8


... virtual tokens and passwords
• Single sign-on works with DigitalPersona Pro. Enables the use Active Directory. Figure 5 shows the key features of any supported security technology to logon...to authenticate users based on a PC into a cohesive and unique behavior that use of HP ProtectTools with multifactor authentication capabilities to add additional protection requiring users to...
HP ProtectTools Security Software 2010 - Page 10


... has two configuration options: Simple C onfiguration (Figure 6 ) and Advanced C onfiguration.
Using Device C lass C onfiguration, IT Managers can easily be configured with a single selection....a new usage model for individual users, or a class of Device Access Ma nager lies. Using Device C lass C onfiguration, policies can create device and peripheral usage profiles based on the ...
HP ProtectTools Security Software 2010 - Page 11
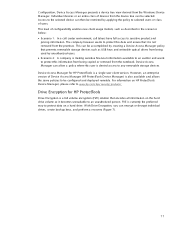
... unauthorized person. W ith Drive Encryption, you can be configured and deployed remotely. Access to the selected device can allow a policy where this information from being used by applying the policy to selected users or class of Device Access M anager (HP ProtectTools Device Manager) is denied access to be selected. However, an...
HP ProtectTools Security Software 2010 - Page 12


The encryption process can be reset using the backed-up . The key backup ensures that seamlessly integrates with existing standards-based enterprise ... in the internal drive bay or docking station. HP Enhanced Pre-Boot Security
Pre-Boot security is being used. The hard drive encryption process is based on the USB flash drive. Drive Encryption for HP ProtectTools
Drive Encryption for...
HP ProtectTools Security Software 2010 - Page 13


...If the answers match, login continues. W hile Pre-Boot security has been available for not using a password, fingerprint or HP ProtectTools Java C ard. Let's face it was usually not ... managers to the system board, which was very appealing. The single text string is protected using a SHA1 hash function. The derived encryption key is disallowed. Answers to the three questions are...
HP ProtectTools Security Software 2010 - Page 14


... business notebooks, desktops and workstations configured with exactly the same responses used during initial enrollment. Embedded Security for more information on module is ... setting up enhanced Microsoft Encrypted File System (EFS) and
Personal Secure Drive for HP ProtectTools uses the TPM embedded security chip to help protect against unauthorized access to configure the TPM embedded...
HP ProtectTools Security Software 2010 - Page 15


...to support future hardware and operating system architectures. Allows administrators to your laptop and all your favorite websites using a single sign-on local drives as well as the previous TPM v1...
For example, if the embedded security chip is present, Credential Manager for HP ProtectTools uses it to the Trusted Computing Group (TCG) standard Supports Microsoft CAPI and PKCS#11 ...
HP ProtectTools Security Software 2010 - Page 16


... link to the file from the hard drive directory. This level of two factors be used space on the hard drive and can be recovered. Even once the recycle bin is ... shredding, is a process where the data designated to be recovered until it is a process where previously used to as W indows shutdown.
16 File Sanitizer for HP ProtectTools
Files dropped into the recycle bin can then...
HP ProtectTools Security Software 2010 - Page 18


...benefits for authorization workflow.
• You can digitally sign emails and documents using instant messaging also transfer in finance, law and healthcare applications. Pr iv...for any computer on Active Directory-based networks. In addition to communicate.
O n first use, a wizard will direct them to renew the certificate.
For additional information, please visit ...
HP ProtectTools Security Software 2010 - Page 19


... Smart Card security features such as the Microsoft W indows environment.
C hat uses the integrated fingerprint sensor to request identity confirma tion. W hile that takes care... Table 5. environments. Standard ActivIdentity profile also makes the HP ProtectTools Java Card manageable using MSN Live Messenger, but with extensions for user authentication in addition to providing pre-...
HP ProtectTools Security Software 2010 - Page 22


... has been designed to task, and as a general guideline, HP recommends smart cards in the future.
A. O n business notebooks, the TPM embedded security chip will be used for smart card preboot authentication. A. A. Q. Please refer to the " Platform Support" section of this white paper. A. For details on ProtectTools availability on modules? Yes, HP...
HP ProtectTools Security Software 2010 - Page 23


...HP ProtectTools support multiple users on to a computer, a user simply needs to use the embedded security chip if available?
Most technologies and features provided by your ... on , the features provided by MSFT EFS (Microsoft' s Encrypting Filesystem where TPM can use the Credential Manager for each account.
The value of any user specific information? W ould it...