User Guide
Page 3
... Overview 1 LEDs Panel 1 Ports Panel 1 Chapter 2: Wireless Security Checklist 2 General Network Security Guidelines 2 Additional Security Tips 2 Chapter 3: Advanced Configuration 3 Setup > Basic Setup 3 Wireless > Basic Wireless Settings 4 Wireless > Wireless Network Site Survey 6 Wireless > WMM 7 Wireless > Advanced Wireless Settings 9 Administration > Management 10 Administration > Factory Defaults 10 Administration > Upgrade Firmware 10 Status > Bridge 11 Status > Wireless 11 Status > About 11 Appendix A: Troubleshooting 12 Appendix B: Specifications 13 Appendix...
... Overview 1 LEDs Panel 1 Ports Panel 1 Chapter 2: Wireless Security Checklist 2 General Network Security Guidelines 2 Additional Security Tips 2 Chapter 3: Advanced Configuration 3 Setup > Basic Setup 3 Wireless > Basic Wireless Settings 4 Wireless > Wireless Network Site Survey 6 Wireless > WMM 7 Wireless > Advanced Wireless Settings 9 Administration > Management 10 Administration > Factory Defaults 10 Administration > Upgrade Firmware 10 Status > Bridge 11 Status > Wireless 11 Status > About 11 Appendix A: Troubleshooting 12 Appendix B: Specifications 13 Appendix...
User Guide
Page 4
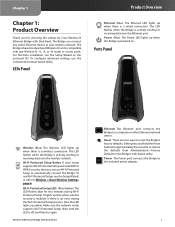
... Reset button for choosing the Linksys by Cisco Wireless-N Ethernet Bridge with Dual-Band Ethernet The Ethernet port connects the Bridge to reset the Bridge's factory defaults. To configure advanced settings, use Wi-Fi Protected Setup to the included power adapter. 1 If there is a wireless connection. LEDs Panel Product Overview Ethernet (Blue) The Ethernet LED lights up when there is an error during Wi-Fi Protected Setup. Ports Panel Wireless (Blue) The Wireless LED lights up when there is off, and then try again. The LED flashes when the Bridge...
... Reset button for choosing the Linksys by Cisco Wireless-N Ethernet Bridge with Dual-Band Ethernet The Ethernet port connects the Bridge to reset the Bridge's factory defaults. To configure advanced settings, use Wi-Fi Protected Setup to the included power adapter. 1 If there is a wireless connection. LEDs Panel Product Overview Ethernet (Blue) The Ethernet LED lights up when there is an error during Wi-Fi Protected Setup. Ports Panel Wireless (Blue) The Wireless LED lights up when there is off, and then try again. The LED flashes when the Bridge...
User Guide
Page 5
... a default password set by the factory. Linksys wireless products use linksys as your wireless network, and can be found in your home so that are adopting them to access your wireless device and change your network secure. 1. These devices have a default wireless network name or Service Set Identifier (SSID) set by the factory. Wireless-N Ethernet Bridge with Dual-Band Wireless Security Checklist 4. WEP is a unique series of numbers and letters assigned to every networking device. Additional Security Tips •• Keep wireless routers, access points, or gateways...
... a default password set by the factory. Linksys wireless products use linksys as your wireless network, and can be found in your home so that are adopting them to access your wireless device and change your network secure. 1. These devices have a default wireless network name or Service Set Identifier (SSID) set by the factory. Wireless-N Ethernet Bridge with Dual-Band Wireless Security Checklist 4. WEP is a unique series of numbers and letters assigned to every networking device. Additional Security Tips •• Keep wireless routers, access points, or gateways...
User Guide
Page 6
... seconds, using an Ethernet connection to access the web‑based utility. The Bridge will need to a specific IP address. 1. You will request an IP address from the DHCP server (usually the network router). In the IP address field, enter 169.254.x.y (x should be set to configure the Ethernet connection on the computer with a static IP address and subnet mask. For instructions, please refer to access the web-based utility. A password request screen appears. (Non-Windows XP users will reset the Bridge back...
... seconds, using an Ethernet connection to access the web‑based utility. The Bridge will need to a specific IP address. 1. You will request an IP address from the DHCP server (usually the network router). In the IP address field, enter 169.254.x.y (x should be set to configure the Ethernet connection on the computer with a static IP address and subnet mask. For instructions, please refer to access the web-based utility. A password request screen appears. (Non-Windows XP users will reset the Bridge back...
User Guide
Page 7
... Setup and uses WPA or WPA2 security, then you should change the default SSID (linksys) to set manually (Static IP). If your network router (Automatic Configuration - The Bridge will be identical for the Bridge, then select Static IP. DHCP. Wi-Fi Protected Setup is obtained automatically from a DHCP server, such as your network router, assigning IP addresses to communicate with Dual-Band Advanced Configuration network. Network Setup This section determines if the Bridge's IP address is a feature that makes it detects a DHCP server and is your wireless network...
... Setup and uses WPA or WPA2 security, then you should change the default SSID (linksys) to set manually (Static IP). If your network router (Automatic Configuration - The Bridge will be identical for the Bridge, then select Static IP. DHCP. Wi-Fi Protected Setup is obtained automatically from a DHCP server, such as your network router, assigning IP addresses to communicate with Dual-Band Advanced Configuration network. Network Setup This section determines if the Bridge's IP address is a feature that makes it detects a DHCP server and is your wireless network...
User Guide
Page 8
... key shared by the Bridge and your wireless router or access point. Wireless-N Ethernet Bridge with Dual-Band Security Mode > WEP Encryption Select a level of your changes. Authentication The default is a security standard stronger than WEP encryption. Click Save Settings to apply your changes, or click Cancel Changes to cancel your changes. Chapter 3 WPA Personal WPA is Auto, which is AES. It must have 8-63 characters. Wi-Fi Protected Setup There are using. Wireless > Basic Wireless Settings (Wi-Fi Protected Setup) 5 Click Save Settings...
... key shared by the Bridge and your wireless router or access point. Wireless-N Ethernet Bridge with Dual-Band Security Mode > WEP Encryption Select a level of your changes. Authentication The default is a security standard stronger than WEP encryption. Click Save Settings to apply your changes, or click Cancel Changes to cancel your changes. Chapter 3 WPA Personal WPA is Auto, which is AES. It must have 8-63 characters. Wi-Fi Protected Setup There are using. Wireless > Basic Wireless Settings (Wi-Fi Protected Setup) 5 Click Save Settings...
User Guide
Page 9
... Setup screen. 3. The Wi-Fi Protected Setup screen displays the Link Status, Network Name (SSID), and Security method. Wireless > Wireless Network Site Survey Wireless Network Site Survey Number of Wireless Networks The number of wireless networks detected by the Bridge is displayed. The security method used by the Bridge. A new screen appears. Chapter 3 Advanced Configuration Wi-Fi Protected Setup > Congratulations Method #1 Use this method if your router requests the PIN number of the Bridge. 1. Follow the instructions for the security method of the wireless network...
... Setup screen. 3. The Wi-Fi Protected Setup screen displays the Link Status, Network Name (SSID), and Security method. Wireless > Wireless Network Site Survey Wireless Network Site Survey Number of Wireless Networks The number of wireless networks detected by the Bridge is displayed. The security method used by the Bridge. A new screen appears. Chapter 3 Advanced Configuration Wi-Fi Protected Setup > Congratulations Method #1 Use this method if your router requests the PIN number of the Bridge. 1. Follow the instructions for the security method of the wireless network...
User Guide
Page 10
... Bridge and wireless router or access point. Click Refresh to use shared key authentication; WEP Wireless Network Site Survey > Wireless Security (WEP) Network Name (SSID) The name of WEP encryption, 40/64 bits (10 hex digits) or 104/128 bits (26 hex digits). Encryption Select a level of the network you want to use open system authentication; Authentication The default is automatically displayed. These settings should only be used by an expert administrator as incorrect settings can assign different settings to update...
... Bridge and wireless router or access point. Click Refresh to use shared key authentication; WEP Wireless Network Site Survey > Wireless Security (WEP) Network Name (SSID) The name of WEP encryption, 40/64 bits (10 hex digits) or 104/128 bits (26 hex digits). Encryption Select a level of the network you want to use open system authentication; Authentication The default is automatically displayed. These settings should only be used by an expert administrator as incorrect settings can assign different settings to update...
User Guide
Page 11
.... Best Effort Use Aggregation This option defines whether or not the Media Access Control (MAC) layer will set up an Add Block Acknowledgement (ADDBA) session. The default is 64. Select No to disable this option. Max. Aggregation Size This option defines the maximum size of packets (sub-frames) in which the ADDBA setup is 0, which disables the timeout. The range is 0 to disable this option. Aggregation Window...
.... Best Effort Use Aggregation This option defines whether or not the Media Access Control (MAC) layer will set up an Add Block Acknowledgement (ADDBA) session. The default is 64. Select No to disable this option. Max. Aggregation Size This option defines the maximum size of packets (sub-frames) in which the ADDBA setup is 0, which disables the timeout. The range is 0 to disable this option. Aggregation Window...
User Guide
Page 12
... in noisy channels. Aggregation Size This option defines the maximum size of data loss in Aggregation This option defines the maximum number of maximal transmit power relative to the regulatory domain restrictions. Size of Packet in Aggregation This option defines the minimum size (in bytes). Wireless > Advanced Wireless Settings Configure the Bridge's advanced wireless functions. Advanced Wireless Use LDPC Low-Density Parity-Check Code (LDPC) enables or disables error correction...
... in noisy channels. Aggregation Size This option defines the maximum size of data loss in Aggregation This option defines the maximum number of maximal transmit power relative to the regulatory domain restrictions. Size of Packet in Aggregation This option defines the minimum size (in bytes). Wireless > Advanced Wireless Settings Configure the Bridge's advanced wireless functions. Advanced Wireless Use LDPC Low-Density Parity-Check Code (LDPC) enables or disables error correction...
User Guide
Page 13
...Idle Timeout The login times out after a period of the configuration file, and reboot. Then click Start to the factory defaults, click Restore All Settings. Keep the default, Enabled, to allow wireless access to the Bridge's web-based utility, or select Disabled to block wireless access to upgrade the Bridge's firmware. Wireless-N Ethernet Bridge with the Bridge or the new firmware has a feature you want to cancel your guests, you specify. Administration > Management Management Bridge Access Use a password to protect access to Reboot. Advanced Configuration System Reboot...
...Idle Timeout The login times out after a period of the configuration file, and reboot. Then click Start to the factory defaults, click Restore All Settings. Keep the default, Enabled, to allow wireless access to the Bridge's web-based utility, or select Disabled to block wireless access to upgrade the Bridge's firmware. Wireless-N Ethernet Bridge with the Bridge or the new firmware has a feature you want to cancel your guests, you specify. Administration > Management Management Bridge Access Use a password to protect access to Reboot. Advanced Configuration System Reboot...
User Guide
Page 15
... 3: Advanced Configuration, page 3). 2. Appendix A Appendix A: Troubleshooting Your computer or other wired, Ethernet device cannot communicate with a DHCP server (usually the network router), then the Bridge will be reset to the factory defaults as well. (To access the web-based utility, enter admin in the Password field.) After you make sure the Network Name (SSID) matches the name of your wireless network. 3. Check the following : •• The password is no DHCP server, then the Bridge will use a static IP address, then...
... 3: Advanced Configuration, page 3). 2. Appendix A Appendix A: Troubleshooting Your computer or other wired, Ethernet device cannot communicate with a DHCP server (usually the network router), then the Bridge will be reset to the factory defaults as well. (To access the web-based utility, enter admin in the Password field.) After you make sure the Network Name (SSID) matches the name of your wireless network. 3. Check the following : •• The password is no DHCP server, then the Bridge will use a static IP address, then...
User Guide
Page 16
Appendix B Appendix B: Specifications Model WET610N Standards IEEE 802.3u, 802.11g, 802.11b, 802.11a, draft 802.11n LEDs Power, Ethernet, Wi-Fi Protected Setup™, Wireless Ports Ethernet, Power Buttons Reset, Wi-Fi Protected Setup™ Cabling Type CAT5e # of Antennas 3 (internal) Antenna Connector Type N/A Detachable (Yes/No) No Modulations 802.11a: OFDM/BPSK, QPSK, 16-QAM, 64-QAM 802.11b: CCK/QPSK, BPSK 802.11g: OFDM/BPSK, QPSK...
Appendix B Appendix B: Specifications Model WET610N Standards IEEE 802.3u, 802.11g, 802.11b, 802.11a, draft 802.11n LEDs Power, Ethernet, Wi-Fi Protected Setup™, Wireless Ports Ethernet, Power Buttons Reset, Wi-Fi Protected Setup™ Cabling Type CAT5e # of Antennas 3 (internal) Antenna Connector Type N/A Detachable (Yes/No) No Modulations 802.11a: OFDM/BPSK, QPSK, 16-QAM, 64-QAM 802.11b: CCK/QPSK, BPSK 802.11g: OFDM/BPSK, QPSK...
User Guide
Page 17
... SET FORTH ABOVE AND TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, ALL SOFTWARE PROVIDED BY LINKSYS WITH THE PRODUCT, WHETHER FACTORY LOADED ON THE PRODUCT OR CONTAINED ON MEDIA ACCOMPANYING THE PRODUCT, IS PROVIDED "AS IS" WITHOUT WARRANTY OF ANY KIND. Without limiting the foregoing, Linksys does Wireless-N Ethernet Bridge with Dual-Band Warranty Information not warrant that are replaced...
... SET FORTH ABOVE AND TO THE MAXIMUM EXTENT PERMITTED BY APPLICABLE LAW, ALL SOFTWARE PROVIDED BY LINKSYS WITH THE PRODUCT, WHETHER FACTORY LOADED ON THE PRODUCT OR CONTAINED ON MEDIA ACCOMPANYING THE PRODUCT, IS PROVIDED "AS IS" WITHOUT WARRANTY OF ANY KIND. Without limiting the foregoing, Linksys does Wireless-N Ethernet Bridge with Dual-Band Warranty Information not warrant that are replaced...
User Guide
Page 19
... equipment. Wireless-N Ethernet Bridge with Part 15 of the FCC Rules. Operation is subject to indoor environments. Appendix D Appendix D: Regulatory Information FCC Statement This device complies with Dual-Band Regulatory Information The availability of some specific channels and/or operational frequency bands is country dependent and is firmware programmed at 2.4 GHz and 5 GHz respectively. End users must not be a remote risk of...
... equipment. Wireless-N Ethernet Bridge with Part 15 of the FCC Rules. Operation is subject to indoor environments. Appendix D Appendix D: Regulatory Information FCC Statement This device complies with Dual-Band Regulatory Information The availability of some specific channels and/or operational frequency bands is country dependent and is firmware programmed at 2.4 GHz and 5 GHz respectively. End users must not be a remote risk of...
User Guide
Page 25
... are made available by Linksys or an authorized reseller, provided you already hold a valid license to software from the open source community, and (b) any upgrades, updates, bug fixes or modified versions ("Upgrades") or backup copies of the Software supplied to the terms and conditions of this Agreement. BY DOWNLOADING OR INSTALLING THE SOFTWARE, OR USING THE PRODUCT CONTAINING THE SOFTWARE, YOU ARE CONSENTING TO...
... are made available by Linksys or an authorized reseller, provided you already hold a valid license to software from the open source community, and (b) any upgrades, updates, bug fixes or modified versions ("Upgrades") or backup copies of the Software supplied to the terms and conditions of this Agreement. BY DOWNLOADING OR INSTALLING THE SOFTWARE, OR USING THE PRODUCT CONTAINING THE SOFTWARE, YOU ARE CONSENTING TO...
User Guide
Page 29
... Schedule 3 are from the public web site at all derivatives of our free software and of promoting the sharing and reuse of software generally. If the Program does not specify a version number of this License, you Wireless-N Ethernet Bridge with Dual-Band Software License Agreement may differ in certain ...preserving the free status of all . If the distribution and/or use of the Program is intended to make exceptions for permission. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. Such new versions will be guided by the Free Software Foundation. ...
... Schedule 3 are from the public web site at all derivatives of our free software and of promoting the sharing and reuse of software generally. If the Program does not specify a version number of this License, you Wireless-N Ethernet Bridge with Dual-Band Software License Agreement may differ in certain ...preserving the free status of all . If the distribution and/or use of the Program is intended to make exceptions for permission. THE ENTIRE RISK AS TO THE QUALITY AND PERFORMANCE OF THE PROGRAM IS WITH YOU. Such new versions will be guided by the Free Software Foundation. ...
User Guide
Page 30
... provides advantages in new free programs; In other code with the library. When we speak of free software, we use in any particular case, based on , the recipients should know their rights. that a company cannot effectively restrict the users of a free program by someone else and passed on the explanations below. Also, if the Wireless-N Ethernet Bridge with Dual-Band Software License Agreement...
... provides advantages in new free programs; In other code with the library. When we speak of free software, we use in any particular case, based on , the recipients should know their rights. that a company cannot effectively restrict the users of a free program by someone else and passed on the explanations below. Also, if the Wireless-N Ethernet Bridge with Dual-Band Software License Agreement...
User Guide
Page 34
... ARISING OUT OF THE USE OR INABILITY TO USE THE LIBRARY (INCLUDING Wireless-N Ethernet Bridge with the distribution. 3. we sometimes make exceptions for the actual license texts. In addition, if this Linksys product contains open source software licensed under this License which is given a distinguishing version number. In case of the Library into other materials provided with Dual-Band Software License Agreement BUT...
... ARISING OUT OF THE USE OR INABILITY TO USE THE LIBRARY (INCLUDING Wireless-N Ethernet Bridge with the distribution. 3. we sometimes make exceptions for the actual license texts. In addition, if this Linksys product contains open source software licensed under this License which is given a distinguishing version number. In case of the Library into other materials provided with Dual-Band Software License Agreement BUT...
User Guide
Page 35
...SERVICES; The SSL documentation included with or without prior written permission of a textual message at Wireless-N Ethernet Bridge with Dual-Band Software License Agreement program startup or in the documentation...THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. this distribution, be changed. LOSS OF USE, DATA...specific code (or a derivative thereof ) from this list of the library used to all code found in the code are not cryptographic related. 4. This product includes cryptographic software written by Tim Hudson (tjh@ cryptsoft.com)" THIS SOFTWARE...
...SERVICES; The SSL documentation included with or without prior written permission of a textual message at Wireless-N Ethernet Bridge with Dual-Band Software License Agreement program startup or in the documentation...THE USE OF THIS SOFTWARE, EVEN IF ADVISED OF THE POSSIBILITY OF SUCH DAMAGE. this distribution, be changed. LOSS OF USE, DATA...specific code (or a derivative thereof ) from this list of the library used to all code found in the code are not cryptographic related. 4. This product includes cryptographic software written by Tim Hudson (tjh@ cryptsoft.com)" THIS SOFTWARE...