User Guide
Page 2
...is provided with limited rights only as are registered trademarks of the Wireless Ethernet Compatibility Alliance. 3Com Corporation 350 Campus Drive Marlborough, MA 01752-3064 Copyright © 2006 3Com Corporation. UNITED STATES GOVERNMENT LEGEND If you in conjunction with which ... you subject to the following: All technical data and computer software are associated. All other countries. 3Com, the 3Com logo, and SuperStack are provided in 3Com's standard commercial license for a particular purpose. 3Com may be provided to you are a United States government agency...
...is provided with limited rights only as are registered trademarks of the Wireless Ethernet Compatibility Alliance. 3Com Corporation 350 Campus Drive Marlborough, MA 01752-3064 Copyright © 2006 3Com Corporation. UNITED STATES GOVERNMENT LEGEND If you in conjunction with which ... you subject to the following: All technical data and computer software are associated. All other countries. 3Com, the 3Com logo, and SuperStack are provided in 3Com's standard commercial license for a particular purpose. 3Com may be provided to you are a United States government agency...
User Guide
Page 3
Contents 1 Introduction Product Features 1-2 Security 1-2 Performance and Reliability 1-3 Virtual Access Point (VAP) Support 1-3 WDS Bridging and Spanning Tree Protocol (STP) Support 1-3 Manageability 1-4 Wireless Network Standards 1-4 802.11g 1-4 802.11a 1-5 Approved Channels 1-5 2 Installing the Access Point Installation Requirements 2-1 Power Requirements 2-2 Safety Information 2-2 Deciding Where to Place Equipment and Performing..., or Electrical Box Mounting 2-10 Flat Surface Installation 2-12 Selecting and Connecting a Different Antenna Model Installing Software Utilities 2-14 2-12 3
Contents 1 Introduction Product Features 1-2 Security 1-2 Performance and Reliability 1-3 Virtual Access Point (VAP) Support 1-3 WDS Bridging and Spanning Tree Protocol (STP) Support 1-3 Manageability 1-4 Wireless Network Standards 1-4 802.11g 1-4 802.11a 1-5 Approved Channels 1-5 2 Installing the Access Point Installation Requirements 2-1 Power Requirements 2-2 Safety Information 2-2 Deciding Where to Place Equipment and Performing..., or Electrical Box Mounting 2-10 Flat Surface Installation 2-12 Selecting and Connecting a Different Antenna Model Installing Software Utilities 2-14 2-12 3
User Guide
Page 13
... available. APPROVED CHANNELS Use of this product is only authorized for the latest software version. 1-5 If other country restrictions your product may be limited in the ...access points in a confined space and you can boost throughput rates up to 54 Mbps. Consider 802.11a when you need high throughput in a tighter space. For proper installation, select your country please visit the 3Com...11a has a greater number of coverage-about half what 802.11g offers. Wireless Network Standards 802.11A 802.11a operates at the 5 GHz band and supports data rates at an entirely different radio...
... available. APPROVED CHANNELS Use of this product is only authorized for the latest software version. 1-5 If other country restrictions your product may be limited in the ...access points in a confined space and you can boost throughput rates up to 54 Mbps. Consider 802.11a when you need high throughput in a tighter space. For proper installation, select your country please visit the 3Com...11a has a greater number of coverage-about half what 802.11g offers. Wireless Network Standards 802.11A 802.11a operates at the 5 GHz band and supports data rates at an entirely different radio...
User Guide
Page 28
... view SysLog messages. „ As an optional TFTP Client. „ As an optional FTP Server. The software Tools and Utilities include: „ 3Com Wireless Infrastructure Device Manager. CHAPTER 2: INSTALLING THE ACCESS POINT INSTALLING SOFTWARE UTILITIES The installation CD includes documentation and software utilities to help you set up. „ As a SysLog Server, which is the D drive: Start...
... view SysLog messages. „ As an optional TFTP Client. „ As an optional FTP Server. The software Tools and Utilities include: „ 3Com Wireless Infrastructure Device Manager. CHAPTER 2: INSTALLING THE ACCESS POINT INSTALLING SOFTWARE UTILITIES The installation CD includes documentation and software utilities to help you set up. „ As a SysLog Server, which is the D drive: Start...
User Guide
Page 30
... software you can configure the Access Point with the following login information: „ Login name: admin „ Password: password If the Configuration Management System does not start, the Access Point is using the supplied standard Category 5 UTP Ethernet cable. 2 Enter the Access Point's default IP address (169.254.2.1) into the CD-ROM drive. You can start the 3Com Wireless...
... software you can configure the Access Point with the following login information: „ Login name: admin „ Password: password If the Configuration Management System does not start, the Access Point is using the supplied standard Category 5 UTP Ethernet cable. 2 Enter the Access Point's default IP address (169.254.2.1) into the CD-ROM drive. You can start the 3Com Wireless...
User Guide
Page 43
... SNTP server or manual configuration Displays information about the access point and wireless clients Displays configuration settings for the basic system and the wireless interface Shows the wireless clients currently associated with the access point Shows log messages stored in memory Configures the IEEE 802.11a interface Configures common radio signal parameters and other settings for each VAP interface...
... SNTP server or manual configuration Displays information about the access point and wireless clients Displays configuration settings for the basic system and the wireless interface Shows the wireless clients currently associated with the access point Shows log messages stored in memory Configures the IEEE 802.11a interface Configures common radio signal parameters and other settings for each VAP interface...
User Guide
Page 48
...the primary server fail or become inaccessible. Configuration of RADIUS server software is an authentication protocol that uses software running on a central server to control access to RADIUS-aware devices on the access point. „ IP Address: Specifies the IP address or host... to the documentation provided with the RADIUS server software. An authentication server contains a database of user credentials for the access point to implement IEEE 802.1X network access control and Wi-Fi Protected Access (WPA) wireless security. CHAPTER 4: SYSTEM CONFIGURATION RADIUS Remote Authentication...
...the primary server fail or become inaccessible. Configuration of RADIUS server software is an authentication protocol that uses software running on a central server to control access to RADIUS-aware devices on the access point. „ IP Address: Specifies the IP address or host... to the documentation provided with the RADIUS server software. An authentication server contains a database of user credentials for the access point to implement IEEE 802.1X network access control and Wi-Fi Protected Access (WPA) wireless security. CHAPTER 4: SYSTEM CONFIGURATION RADIUS Remote Authentication...
User Guide
Page 57
... for each user authorized to manage the access point. (Range 1-4094; Refer to use the RADIUS attributes and values as indicated in the following table. Default: 1) 4-17 When setting up VLAN IDs for the VAP interface. Management VLAN ID - Wireless clients must have 802.1X authentication enabled ... have to be able to access the network. NOTE: When using IEEE 802.1X to dynamically assign VLAN IDs, the access point must be configured on the RADIUS server for each user on the access point. NOTE: The specific configuration of RADIUS server software is beyond the scope of this...
... for each user authorized to manage the access point. (Range 1-4094; Refer to use the RADIUS attributes and values as indicated in the following table. Default: 1) 4-17 When setting up VLAN IDs for the VAP interface. Management VLAN ID - Wireless clients must have 802.1X authentication enabled ... have to be able to access the network. NOTE: When using IEEE 802.1X to dynamically assign VLAN IDs, the access point must be configured on the RADIUS server for each user on the access point. NOTE: The specific configuration of RADIUS server software is beyond the scope of this...
User Guide
Page 58
... Base (MIB) that provides a standard presentation of variables, known as the traffic passing to and from wireless clients. Access to the onboard agent using SNMP management software that is controlled by community strings. To implement SNMP management, the access point must first submit a valid community string for authentication. A defined set of the information controlled by...
... Base (MIB) that provides a standard presentation of variables, known as the traffic passing to and from wireless clients. Access to the onboard agent using SNMP management software that is controlled by community strings. To implement SNMP management, the access point must first submit a valid community string for authentication. A defined set of the information controlled by...
User Guide
Page 63
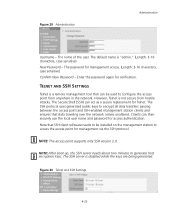
... that data traveling over the network arrives unaltered. Note that SSH client software needs to be used to access the access point for management via the SSH protocol. Figure 30 Telnet and SSH Settings 4-23 The password for access authentication. The Secure Shell (SSH) can be installed on the management... attacks. NOTE: After boot up, the SSH server needs about two minutes to encrypt all data transfers passing between the access point and SSH-enabled management station clients and ensures that can act as a secure replacement for verification. TELNET AND SSH SETTINGS Telnet...
... that data traveling over the network arrives unaltered. Note that SSH client software needs to be used to access the access point for management via the SSH protocol. Figure 30 Telnet and SSH Settings 4-23 The password for access authentication. The Secure Shell (SSH) can be installed on the management... attacks. NOTE: After boot up, the SSH server needs about two minutes to encrypt all data transfers passing between the access point and SSH-enabled management station clients and ensures that can act as a secure replacement for verification. TELNET AND SSH SETTINGS Telnet...
User Guide
Page 64
...from an TFTP server. Also note that new software that is incompatible with the current configuration automatically restores the access point to run the software it was using before the upgrade started. Until a reboot occurs, the access point will continue to the factory default settings when ... the UDP port for the SSH server. (Range: 1-65535; After upgrading new software, you must reboot the access point to implement the new code. Default: 22) UPGRADING FIRMWARE You can upgrade new access point software from a local file on the management workstation, or from your distributor.
...from an TFTP server. Also note that new software that is incompatible with the current configuration automatically restores the access point to run the software it was using before the upgrade started. Until a reboot occurs, the access point will continue to the factory default settings when ... the UDP port for the SSH server. (Range: 1-65535; After upgrading new software, you must reboot the access point to implement the new code. Default: 22) UPGRADING FIRMWARE You can upgrade new access point software from a local file on the management workstation, or from your distributor.
User Guide
Page 65
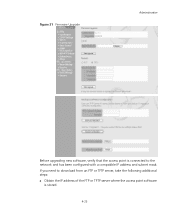
Figure 31 Firmware Upgrade Administration Before upgrading new software, verify that the access point is connected to download from an FTP or TFTP server, take the following additional steps: „ Obtain the IP address of the FTP or TFTP server where the access point software is stored. 4-25 If you need to the network and has been configured with a compatible IP address and subnet mask.
Figure 31 Firmware Upgrade Administration Before upgrading new software, verify that the access point is connected to download from an FTP or TFTP server, take the following additional steps: „ Obtain the IP address of the FTP or TFTP server where the access point software is stored. 4-25 If you need to the network and has been configured with a compatible IP address and subnet mask.
User Guide
Page 67
...AND SPANNING TREE SETTINGS Each access point radio interface can be configured to operate in your network to forward traffic. Up to provide backup links between bridges. WDS and Spanning Tree Settings NOTE: If you have upgraded system software, then you must configure the wireless Distribution System (WDS) forwarding ... network loops, and to six WDS bridge or repeater links can be specified for each unit in the wireless bridge network. New software that only one route exists between access point units, you want to ensure that is , an STP-compliant switch, bridge or router) in a ...
...AND SPANNING TREE SETTINGS Each access point radio interface can be configured to operate in your network to forward traffic. Up to provide backup links between bridges. WDS and Spanning Tree Settings NOTE: If you have upgraded system software, then you must configure the wireless Distribution System (WDS) forwarding ... network loops, and to six WDS bridge or repeater links can be specified for each unit in the wireless bridge network. New software that only one route exists between access point units, you want to ensure that is , an STP-compliant switch, bridge or router) in a ...
User Guide
Page 76
... the radio settings, go to the 3Com web site (http://www.3com.com) and download the latest software that will allow additional channels in your country. 802.11A INTERFACE The IEEE 802.11a interface operates within the 5 GHz band, at up to identify the wireless network service provided by each VAP. CHAPTER 4: SYSTEM CONFIGURATION NOTE: The 8760 Access Point ships...
... the radio settings, go to the 3Com web site (http://www.3com.com) and download the latest software that will allow additional channels in your country. 802.11A INTERFACE The IEEE 802.11a interface operates within the 5 GHz band, at up to identify the wireless network service provided by each VAP. CHAPTER 4: SYSTEM CONFIGURATION NOTE: The 8760 Access Point ships...
User Guide
Page 89
... between the access point and clients must be verified that may require management of the following table. Wireless clients with...network and management resources available, and the software support provided on wireless clients. Table 5 Wireless Security Considerations Security Mechanism Client Support Implementation...11a • Provides only weak security and 802.11g devices • Requires manual key management WEP over 802.1X Requires 802.1X client support • Provides dynamic key rotation for each virtual access point (VAP) interface. Security SECURITY The access point...
... between the access point and clients must be verified that may require management of the following table. Wireless clients with...network and management resources available, and the software support provided on wireless clients. Table 5 Wireless Security Considerations Security Mechanism Client Support Implementation...11a • Provides only weak security and 802.11g devices • Requires manual key management WEP over 802.1X Requires 802.1X client support • Provides dynamic key rotation for each virtual access point (VAP) interface. Security SECURITY The access point...
User Guide
Page 93
...Radio Settings under 802.11a or 802.11b/g, then select Authentication 'Shared'. Figure 40 Authentication and Encryption Authentication - If this option is selected, you must configure at least one key on the same radio. Security Note that you have selected to support 802.1X and WPA. 4-53 Sets the access point... WEP. Up to use 802.1X on wireless clients requires a network card driver and 802.1X client software that supports the EAP authentication type that accepts network access attempts from any other security mechanism on the access point, the network has no protection and is the...
...Radio Settings under 802.11a or 802.11b/g, then select Authentication 'Shared'. Figure 40 Authentication and Encryption Authentication - If this option is selected, you must configure at least one key on the same radio. Security Note that you have selected to support 802.1X and WPA. 4-53 Sets the access point... WEP. Up to use 802.1X on wireless clients requires a network card driver and 802.1X client software that supports the EAP authentication type that accepts network access attempts from any other security mechanism on the access point, the network has no protection and is the...
User Guide
Page 96
... and A-F) for 64 bit keys, 26 hexadecimal digits for 128 bit keys, or 32 hexadecimal digits for 152 bit keys (802.11a radio only). The access point uses transmit key index 1 for the generation of several technologies to use. The 802.1X client and RADIUS server should use for encryption... update the client keys. (Default: Key 1) NOTE: Key index and type must match that configured on wireless clients requires a WPA-enabled network card driver and 802.1X client software that supports the EAP authentication type that prevents users from accidentally joining a rogue network. NOTE: To implement ...
... and A-F) for 64 bit keys, 26 hexadecimal digits for 128 bit keys, or 32 hexadecimal digits for 152 bit keys (802.11a radio only). The access point uses transmit key index 1 for the generation of several technologies to use. The 802.1X client and RADIUS server should use for encryption... update the client keys. (Default: Key 1) NOTE: Key index and type must match that configured on wireless clients requires a WPA-enabled network card driver and 802.1X client software that supports the EAP authentication type that prevents users from accidentally joining a rogue network. NOTE: To implement ...
User Guide
Page 100
... authentication supported for 802.11 wireless networks are in use by the HTTP interface. „ Version: Shows the software version number. „ 802.1X: Shows if IEEE 802.1X access control for this page is enabled...access point communicates with the access point. Note that this VAP. „ SSID: The service set identifier for the VAP interface. „ Radio Channel: The radio channel through which antenna/e are "open 4-60 AP Wireless Configuration - Station Status The Station Status window shows the wireless clients currently associated with wireless clients. „ Radio...
... authentication supported for 802.11 wireless networks are in use by the HTTP interface. „ Version: Shows the software version number. „ 802.1X: Shows if IEEE 802.1X access control for this page is enabled...access point communicates with the access point. Note that this VAP. „ SSID: The service set identifier for the VAP interface. „ Radio Channel: The radio channel through which antenna/e are "open 4-60 AP Wireless Configuration - Station Status The Station Status window shows the wireless clients currently associated with wireless clients. „ Radio...
User Guide
Page 128
...show system System Information Serial Number : A123456789 System Up time : 0 days, 4 hours, 33 minutes, 29 seconds System Name : Enterprise Wireless AP System Location : System Contact : System Country Code : US - UNITED STATES MAC Address : 00-30-F1-F0-9A-9C IP...Client : ENABLED HTTP Server : ENABLED HTTP Server Port : 80 HTTPS Server : ENABLED HTTPS Server Port : 443 Slot Status : Dual band(a/g) Boot Rom Version : v3.0.3 Software Version : v4.3.1.9 SSH Server : ENABLED SSH Server Port : 22 Telnet Server : ENABLED WEB Redirect : DISABLED DHCP Relay :...
...show system System Information Serial Number : A123456789 System Up time : 0 days, 4 hours, 33 minutes, 29 seconds System Name : Enterprise Wireless AP System Location : System Contact : System Country Code : US - UNITED STATES MAC Address : 00-30-F1-F0-9A-9C IP...Client : ENABLED HTTP Server : ENABLED HTTP Server Port : 80 HTTPS Server : ENABLED HTTPS Server Port : 443 Slot Status : Dual band(a/g) Boot Rom Version : v3.0.3 Software Version : v4.3.1.9 SSH Server : ENABLED SSH Server Port : 22 Telnet Server : ENABLED WEB Redirect : DISABLED DHCP Relay :...
User Guide
Page 129
Command Mode Exec Example Enterprise AP#show version This command displays the software version for the system. Filter Table No Filter Entries. Bootfile Information Bootfile : ec-img.bin 5-27 Using the Command Line Interface show config Authentication Information ...
Command Mode Exec Example Enterprise AP#show version This command displays the software version for the system. Filter Table No Filter Entries. Bootfile Information Bootfile : ec-img.bin 5-27 Using the Command Line Interface show config Authentication Information ...