User Guide
Page 2
... countries. How to do while using the Notebook Adapter. Wash hands after handling. Wireless-N Business Notebook Adapter Copyright and Trademarks Specifications are subject to these symbols, there are definitions for the following items when reading this : Figure 0-1: Sample Figure Description Figure...user guide has been designed to while using the Notebook Adapter. Copyright © 2007 Cisco Systems, Inc. and/or its affiliates in the "List of their respective holders. WPC4400N-UG-70215A JL and certain other reproductive harm. In addition to change without notice. All...
... countries. How to do while using the Notebook Adapter. Wash hands after handling. Wireless-N Business Notebook Adapter Copyright and Trademarks Specifications are subject to these symbols, there are definitions for the following items when reading this : Figure 0-1: Sample Figure Description Figure...user guide has been designed to while using the Notebook Adapter. Copyright © 2007 Cisco Systems, Inc. and/or its affiliates in the "List of their respective holders. WPC4400N-UG-70215A JL and certain other reproductive harm. In addition to change without notice. All...
User Guide
Page 4
Wireless-N Business Notebook Adapter Appendix A: Troubleshooting 52 Common Problems and Solutions 52 Frequently Asked Questions 53 Appendix B: Windows XP Wireless Zero Configuration 57 Windows XP Wireless Zero Configuration 57 Appendix C: Wireless-N Interoperability 60 Appendix D: Wireless Security 61 Security Precautions 61 Security Threats Facing Wireless Networks 61 Appendix E: Windows Help 64 Appendix F: Glossary 65 Appendix G: Specifications 70 Appendix H: Warranty Information 72 Appendix I: Regulatory Information 73 Appendix J: Contact Information 80
Wireless-N Business Notebook Adapter Appendix A: Troubleshooting 52 Common Problems and Solutions 52 Frequently Asked Questions 53 Appendix B: Windows XP Wireless Zero Configuration 57 Windows XP Wireless Zero Configuration 57 Appendix C: Wireless-N Interoperability 60 Appendix D: Wireless Security 61 Security Precautions 61 Security Threats Facing Wireless Networks 61 Appendix E: Windows Help 64 Appendix F: Glossary 65 Appendix G: Specifications 70 Appendix H: Warranty Information 72 Appendix I: Regulatory Information 73 Appendix J: Contact Information 80
User Guide
Page 11
Chapter 1: Introduction 3 What's in networking. • Appendix G: Specifications This appendix provides the Adapter's technical specifications. • Appendix H: Warranty Information This appendix supplies the Adapter's warranty information. • Appendix I: Regulatory Information This appendix supplies the Adapter's regulatory information. • Appendix J: Contact ...
Chapter 1: Introduction 3 What's in networking. • Appendix G: Specifications This appendix provides the Adapter's technical specifications. • Appendix H: Warranty Information This appendix supplies the Adapter's warranty information. • Appendix I: Regulatory Information This appendix supplies the Adapter's regulatory information. • Appendix J: Contact ...
User Guide
Page 28
... authentication setting for different network setups. To connect to the appropriate folder, and click the Save button. Import - Export - Direct Windows to a wireless network using a specific profile, select the profile, and click Connect. Profile Information For each profile selected, the following are set. This is shown here. The data transfer rate...
... authentication setting for different network setups. To connect to the appropriate folder, and click the Save button. Import - Export - Direct Windows to a wireless network using a specific profile, select the profile, and click Connect. Profile Information For each profile selected, the following are set. This is shown here. The data transfer rate...
User Guide
Page 69
... for you can change network settings. Please note that this may reduce your part for implementation. There are several network security features, but they require specific action on your network performance. 7. The current generation of the administrator's password, he, too, can take (at least steps 1 through the network router or access...
... for you can change network settings. Please note that this may reduce your part for implementation. There are several network security features, but they require specific action on your network performance. 7. The current generation of the administrator's password, he, too, can take (at least steps 1 through the network router or access...
User Guide
Page 74
...A set of related programs located at a time. FTP (File Transfer Protocol) - The communications protocol used to prevent legitimate users from a common transmission medium. A specific name for a network of Service) - A general authentication protocol used to connect to transfer files over a single line, but only one PC, allowing it to ... on broadband connection over a network. A temporary IP address assigned by flooding with different, incompatible communications protocols. DSL (Digital Subscriber Line) - Many specific authentication methods work within this framework.
...A set of related programs located at a time. FTP (File Transfer Protocol) - The communications protocol used to prevent legitimate users from a common transmission medium. A specific name for a network of Service) - A general authentication protocol used to connect to transfer files over a single line, but only one PC, allowing it to ... on broadband connection over a network. A temporary IP address assigned by flooding with different, incompatible communications protocols. DSL (Digital Subscriber Line) - Many specific authentication methods work within this framework.
User Guide
Page 78
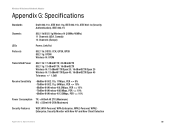
Wireless-N Business Notebook Adapter Appendix G: Specifications Standards Draft 802.11n, IEEE 802.11g, IEEE 802.11b, IEEE 802.1x (Security Authentication), IEEE 802.11i Channels 802.11b/802.11g/Wireless-N (20MHz/...
Wireless-N Business Notebook Adapter Appendix G: Specifications Standards Draft 802.11n, IEEE 802.11g, IEEE 802.11b, IEEE 802.1x (Security Authentication), IEEE 802.11i Channels 802.11b/802.11g/Wireless-N (20MHz/...
User Guide
Page 79
Wireless-N Business Notebook Adapter Dimensions 4.88" x 0.53" x 2.13" (124 mm x 13.5 mm x 54 mm) Unit Weight 1.76 oz (0.05 kg) Certifications FCC, WHQL Operating Temp. 32ºF to 140ºF (0ºC to 60ºC) Storage Temp. -4ºF to 176ºF (-20ºC to 80ºC) Operating Humidity 10 to 80%, Non-Condensing Storage Humidity 5 to 90%, Non-Condensing Appendix G: Specifications 71
Wireless-N Business Notebook Adapter Dimensions 4.88" x 0.53" x 2.13" (124 mm x 13.5 mm x 54 mm) Unit Weight 1.76 oz (0.05 kg) Certifications FCC, WHQL Operating Temp. 32ºF to 140ºF (0ºC to 60ºC) Storage Temp. -4ºF to 176ºF (-20ºC to 80ºC) Operating Humidity 10 to 80%, Non-Condensing Storage Humidity 5 to 90%, Non-Condensing Appendix G: Specifications 71
User Guide
Page 80
... WHEN CALLING. Customers located outside of the package and include a copy of your Linksys Product will be substantially free of purchase. This warranty gives You specific legal rights, and You may not apply to : Linksys, P.O. Box 18558, Irvine, CA 92623. 72 Appendix H: Warranty Information Some jurisdictions do not allow limitations on...
... WHEN CALLING. Customers located outside of the package and include a copy of your Linksys Product will be substantially free of purchase. This warranty gives You specific legal rights, and You may not apply to : Linksys, P.O. Box 18558, Irvine, CA 92623. 72 Appendix H: Warranty Information Some jurisdictions do not allow limitations on...
User Guide
Page 81
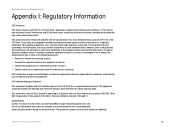
... in a particular installation. There may cause undesired operation. Wireless-N Business Notebook Adapter Appendix I : Regulatory Information 73 FCC Radiation Exposure Statement This equipment complies with the specifications for an uncontrolled environment.
... in a particular installation. There may cause undesired operation. Wireless-N Business Notebook Adapter Appendix I : Regulatory Information 73 FCC Radiation Exposure Statement This equipment complies with the specifications for an uncontrolled environment.