Software Guide
Page 2
...OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. All other company. (0804R) © 2008... of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of Cisco Systems, Inc. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL ...
...OR INCIDENTAL DAMAGES, INCLUDING, WITHOUT LIMITATION, LOST PROFITS OR LOSS OR DAMAGE TO DATA ARISING OUT OF THE USE OR INABILITY TO USE THIS MANUAL, EVEN IF CISCO OR ITS SUPPLIERS HAVE BEEN ADVISED OF THE POSSIBILITY OF SUCH DAMAGES. All other company. (0804R) © 2008... of a program developed by the University of California, Berkeley (UCB) as part of UCB's public domain version of Cisco Systems, Inc. ALL STATEMENTS, INFORMATION, AND RECOMMENDATIONS IN THIS MANUAL ARE BELIEVED TO BE ACCURATE BUT ARE PRESENTED WITHOUT WARRANTY OF ANY KIND, EXPRESS OR IMPLIED. USERS MUST TAKE FULL ...
Software Guide
Page 8
Contents D A P P E N D I X INDEX Optional Variables C-4 Using the TFTP Download Command C-5 Configuration Register C-5 Changing the Configuration Register Manually C-6 Changing the Configuration Register Using Prompts C-6 Console Download C-7 Command Description C-7 Error Reporting C-8 Debug Commands C-8 Exiting the ROM Monitor C-9 Common Port Assignments D-1 Cisco Secure Router 520 Series Software Configuration Guide viii OL-14210-01
Contents D A P P E N D I X INDEX Optional Variables C-4 Using the TFTP Download Command C-5 Configuration Register C-5 Changing the Configuration Register Manually C-6 Changing the Configuration Register Using Prompts C-6 Console Download C-7 Command Description C-7 Error Reporting C-8 Debug Commands C-8 Exiting the ROM Monitor C-9 Common Port Assignments D-1 Cisco Secure Router 520 Series Software Configuration Guide viii OL-14210-01
Software Guide
Page 30
... by the "S." Static routes are private routes unless they are manually configured on the router. You do not need to the configured PVC. EIGRP, EX - EIGRP external, i - Configuring static routes on static routing, see the Cisco IOS IP Command Reference, Volume 2 of 10.10.10.2. ...provide fixed routing paths through the network. If the network topology changes, the static route must be set . IS-IS level-2 1-10 Cisco Secure Router 520 Series Software Configuration Guide OL-14210-01 Step 2 end Example: Router(config)# end Router# Exits router configuration mode, ...
... by the "S." Static routes are private routes unless they are manually configured on the router. You do not need to the configured PVC. EIGRP, EX - EIGRP external, i - Configuring static routes on static routing, see the Cisco IOS IP Command Reference, Volume 2 of 10.10.10.2. ...provide fixed routing paths through the network. If the network topology changes, the static route must be set . IS-IS level-2 1-10 Cisco Secure Router 520 Series Software Configuration Guide OL-14210-01 Step 2 end Example: Router(config)# end Router# Exits router configuration mode, ...
Software Guide
Page 57
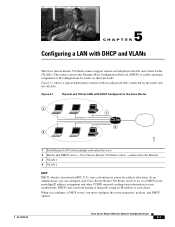
5 C H A P T E R Configuring a LAN with two physical LANs connected by the router and two VLANs. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide 5-1 When you configure a DHCP server, you from having to manually assign an IP address to the Internet 3 VLAN 1 4 VLAN 2 DHCP DHCP, which is described in RFC 2131, uses a client...
5 C H A P T E R Configuring a LAN with two physical LANs connected by the router and two VLANs. OL-14210-01 Cisco Secure Router 520 Series Software Configuration Guide 5-1 When you configure a DHCP server, you from having to manually assign an IP address to the Internet 3 VLAN 1 4 VLAN 2 DHCP DHCP, which is described in RFC 2131, uses a client...
Software Guide
Page 60
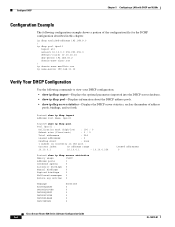
...dpool1 import all network 10.10.0.0 255.255.255.0 default-router 10.10.10.10 dns-server 192.168.35.2 domain-name cisco.com ! ip domain name smallbiz.com ip name-server 192.168.11.12 Verify Your DHCP Configuration Use the following configuration example ...Pool Name: dpool1 Router# show ip dhcp server statistics Memory usage 15419 Address pools 1 Database agents 0 Automatic bindings 0 Manual bindings 0 Expired bindings 0 Malformed messages 0 Secure arp entries 0 Message BOOTREQUEST DHCPDISCOVER DHCPREQUEST DHCPDECLINE DHCPRELEASE DHCPINFORM Received 0 0 0 0 0 0 Leased addresses...
...dpool1 import all network 10.10.0.0 255.255.255.0 default-router 10.10.10.10 dns-server 192.168.35.2 domain-name cisco.com ! ip domain name smallbiz.com ip name-server 192.168.11.12 Verify Your DHCP Configuration Use the following configuration example ...Pool Name: dpool1 Router# show ip dhcp server statistics Memory usage 15419 Address pools 1 Database agents 0 Automatic bindings 0 Manual bindings 0 Expired bindings 0 Malformed messages 0 Secure arp entries 0 Message BOOTREQUEST DHCPDISCOVER DHCPREQUEST DHCPDECLINE DHCPRELEASE DHCPINFORM Received 0 0 0 0 0 0 Leased addresses...
Software Guide
Page 66
... the Physical Interface • Create an Easy VPN Remote Configuration An example showing the results of multiple VPN tunnels, you must manually configure the IPsec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on an IPsec client, such as an IPsec server.... VPN tunnel connection. When the IPsec client initiates the VPN tunnel connection, the IPsec server pushes the IPsec policies to act as a Cisco Adaptive Security Appliance (ASA) Series concentrator that is provided in one destination peer. An Easy VPN server-enabled device can be configured in...
... the Physical Interface • Create an Easy VPN Remote Configuration An example showing the results of multiple VPN tunnels, you must manually configure the IPsec VPN and Network Address Translation/Peer Address Translation (NAT/PAT) parameters on an IPsec client, such as an IPsec server.... VPN tunnel connection. When the IPsec client initiates the VPN tunnel connection, the IPsec server pushes the IPsec policies to act as a Cisco Adaptive Security Appliance (ASA) Series concentrator that is provided in one destination peer. An Easy VPN server-enabled device can be configured in...
Software Guide
Page 71
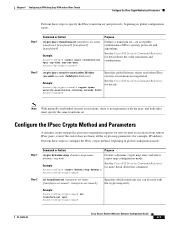
...-sha-hmac Router(cfg-crypto-trans)# Purpose Defines a transform set-an acceptable combination of IPsec security protocols and algorithms. See the Cisco IOS Security Command Reference for more detail about the valid transforms and combinations. Step 2 set transform-set transform-set-name [transform... dynamic-map dynamic-map-name dynamic-seq-num Creates a dynamic crypto map entry and enters crypto map configuration mode. Note With manually established security associations, there is no negotiation with the crypto map entry. Configure the IPsec Crypto Method and Parameters A dynamic crypto...
...-sha-hmac Router(cfg-crypto-trans)# Purpose Defines a transform set-an acceptable combination of IPsec security protocols and algorithms. See the Cisco IOS Security Command Reference for more detail about the valid transforms and combinations. Step 2 set transform-set transform-set-name [transform... dynamic-map dynamic-map-name dynamic-seq-num Creates a dynamic crypto map entry and enters crypto map configuration mode. Note With manually established security associations, there is no negotiation with the crypto map entry. Configure the IPsec Crypto Method and Parameters A dynamic crypto...
Software Guide
Page 82
Note With manually established security associations, there is no negotiation with the crypto map entry. Example: Router(config)# crypto dynamic-map dynmap 1 Router(config-crypto-map)# See the Cisco IOS Security Command Reference for details. Configure a VPN Chapter 7 Configuring VPNs Using an...(cfg-crypto-trans)# Purpose Defines a transform set-An acceptable combination of IPsec security protocols and algorithms. See the Cisco IOS Security Command Reference for example, IP address). Example: Router(cfg-crypto-trans)# crypto ipsec security-association lifetime seconds 86400...
Note With manually established security associations, there is no negotiation with the crypto map entry. Example: Router(config)# crypto dynamic-map dynmap 1 Router(config-crypto-map)# See the Cisco IOS Security Command Reference for details. Configure a VPN Chapter 7 Configuring VPNs Using an...(cfg-crypto-trans)# Purpose Defines a transform set-An acceptable combination of IPsec security protocols and algorithms. See the Cisco IOS Security Command Reference for example, IP address). Example: Router(cfg-crypto-trans)# crypto ipsec security-association lifetime seconds 86400...
Software Guide
Page 138
... Internet). In this single registered IP address. Because the addressing scheme on the inside network (a network that do not need for the manual configuration of individual computers, printers, and shared file systems • Preventing the simultaneous use the same globally unique IP address is a ...client-server protocol that require external access, saving time and money. This feature enables a Cisco router to automatically negotiate its own registered WAN interface IP address from a central server and to enable all remote hosts to access the...
... Internet). In this single registered IP address. Because the addressing scheme on the inside network (a network that do not need for the manual configuration of individual computers, printers, and shared file systems • Preventing the simultaneous use the same globally unique IP address is a ...client-server protocol that require external access, saving time and money. This feature enables a Cisco router to automatically negotiate its own registered WAN interface IP address from a central server and to enable all remote hosts to access the...
Software Guide
Page 144
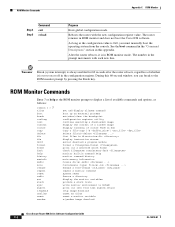
...the console. The router remains in this 60-second window, you must manually boot the operating system from last system return tftp image download unset an alias unset a monitor variable x/ymodem image download Cisco Secure Router 520 Series Software Configuration Guide C-2 OL-14210-01 The number...reload Purpose Exits global configuration mode. See the boot command in the "Command Descriptions" section in ROM monitor and does not boot the Cisco IOS software. Timesaver Break (system interrupt) is always enabled for 60 seconds after the router reboots, regardless of cookie PROM in hex ...
...the console. The router remains in this 60-second window, you must manually boot the operating system from last system return tftp image download unset an alias unset a monitor variable x/ymodem image download Cisco Secure Router 520 Series Software Configuration Guide C-2 OL-14210-01 The number...reload Purpose Exits global configuration mode. See the boot command in the "Command Descriptions" section in ROM monitor and does not boot the Cisco IOS software. Timesaver Break (system interrupt) is always enabled for 60 seconds after the router reboots, regardless of cookie PROM in hex ...
Software Guide
Page 148
Configuration Register Appendix C ROM Monitor Changing the Configuration Register Manually To change the virtual configuration register from the ROM monitor manually, enter the confreg command followed by describing the meaning of the register in hexadecimal format, as... address"? In either case, the new virtual configuration register value is written into NVRAM but does not take effect until you wish to take effect Cisco Secure Router 520 Series Software Configuration Guide C-6 OL-14210-01 y/n [n]: y enable "diagnostic mode"? y/n [n]: enable "load rom after netboot fails"? y/n...
Configuration Register Appendix C ROM Monitor Changing the Configuration Register Manually To change the virtual configuration register from the ROM monitor manually, enter the confreg command followed by describing the meaning of the register in hexadecimal format, as... address"? In either case, the new virtual configuration register value is written into NVRAM but does not take effect until you wish to take effect Cisco Secure Router 520 Series Software Configuration Guide C-6 OL-14210-01 y/n [n]: y enable "diagnostic mode"? y/n [n]: enable "load rom after netboot fails"? y/n...