Software Guide
Page 16
... Configuration 9 Setting the Configuration Register Value 10 Setting the BOOT Environment Variable 10 Setting the BOOT Environment Variable 10 Clearing the BOOT Environment Variable Settings 11...the Flash File System 1 Setting the Default Flash Device 2 Setting the Text File Configuration Mode 2 Listing the Files on a Flash Device 3 Copying Files 4 Deleting Files 6 Restoring Deleted Files 7 ... Download an Image Using TFTP 2 Downloading Supervisor Engine Images Using TFTP 3 Downloading Switching Module Images Using TFTP 4 TFTP Download Procedures Example 5 Uploading System Software Images to a ...
... Configuration 9 Setting the Configuration Register Value 10 Setting the BOOT Environment Variable 10 Setting the BOOT Environment Variable 10 Clearing the BOOT Environment Variable Settings 11...the Flash File System 1 Setting the Default Flash Device 2 Setting the Text File Configuration Mode 2 Listing the Files on a Flash Device 3 Copying Files 4 Deleting Files 6 Restoring Deleted Files 7 ... Download an Image Using TFTP 2 Downloading Supervisor Engine Images Using TFTP 3 Downloading Switching Module Images Using TFTP 4 TFTP Download Procedures Example 5 Uploading System Software Images to a ...
Software Guide
Page 19
... 3 Disabling Layer 3 Protocol Filtering 3 Configuring the IP Permit List 1 Understanding How the IP Permit List Works 1 IP Permit List Default Configuration 2 Configuring the IP Permit List 2 Adding IP Addresses to the IP Permit List 2 Enabling the IP Permit List 3 Disabling the IP Permit List 4 Clearing an IP Permit List Entry 4 Configuring Port Security 1 Understanding How Port Security Works...
... 3 Disabling Layer 3 Protocol Filtering 3 Configuring the IP Permit List 1 Understanding How the IP Permit List Works 1 IP Permit List Default Configuration 2 Configuring the IP Permit List 2 Adding IP Addresses to the IP Permit List 2 Enabling the IP Permit List 3 Disabling the IP Permit List 4 Clearing an IP Permit List Entry 4 Configuring Port Security 1 Understanding How Port Security Works...
Software Guide
Page 28
... and Gigabit Ethernet ...Cisco Express Forwarding for Policy Feature Card 2 (CEF for PFC2 Describes how to configure access control lists...list. Checking Port Status and Connectivity Describes how to display information about modules...List Describes how to install and configure redundant supervisor engines and MSFCs in the Catalyst 6000 family switches. Configuring VTP Describes how to configure system message logging (syslog). Configuring System Message Logging Describes how to configure VLAN Trunk Protocol (VTP) on the switch. Organization Preface Chapter Chapter 9 Chapter 10...
... and Gigabit Ethernet ...Cisco Express Forwarding for Policy Feature Card 2 (CEF for PFC2 Describes how to configure access control lists...list. Checking Port Status and Connectivity Describes how to display information about modules...List Describes how to install and configure redundant supervisor engines and MSFCs in the Catalyst 6000 family switches. Configuring VTP Describes how to configure system message logging (syslog). Configuring System Message Logging Describes how to configure VLAN Trunk Protocol (VTP) on the switch. Organization Preface Chapter Chapter 9 Chapter 10...
Software Guide
Page 34
... of networking publications. You can access iQ Magazine at this URL: http://www.cisco.com/en/US/about/ac123/ac147/about_cisco_the_internet_protocol_journal.html • Training-Cisco offers world-class networking training, with the latest information about the networking industry. ...http://www.cisco.com/en/US/products/products_catalog_links_launch.html • Cisco Press publishes a wide range of public and private internets and intranets. Cisco suggests these titles for engineering professionals involved in network training listed at this URL: http://business.cisco.com/prod...
... of networking publications. You can access iQ Magazine at this URL: http://www.cisco.com/en/US/about/ac123/ac147/about_cisco_the_internet_protocol_journal.html • Training-Cisco offers world-class networking training, with the latest information about the networking industry. ...http://www.cisco.com/en/US/products/products_catalog_links_launch.html • Cisco Press publishes a wide range of public and private internets and intranets. Cisco suggests these titles for engineering professionals involved in network training listed at this URL: http://business.cisco.com/prod...
Software Guide
Page 41
... the system and perform basic troubleshooting. Table 2-1 shows examples of ports. You can enter lists of operation: normal and privileged. To designate a specific module, use a comma-separated list (do not insert spaces) to specify individual ports or a hyphen (-) between the port ... engine, the supervisor engines reside in slots 1 and 2. To return to enter privileged mode: Console> enable Enter Password: Console> (enable) Designating Modules, Ports, and VLANs on the Command Line, page 2-5 • Designating MAC Addresses, IP Addresses, and IP Aliases, page 2-6 • Command...
... the system and perform basic troubleshooting. Table 2-1 shows examples of ports. You can enter lists of operation: normal and privileged. To designate a specific module, use a comma-separated list (do not insert spaces) to specify individual ports or a hyphen (-) between the port ... engine, the supervisor engines reside in slots 1 and 2. To return to enter privileged mode: Console> enable Enter Password: Console> (enable) Designating Modules, Ports, and VLANs on the Command Line, page 2-5 • Designating MAC Addresses, IP Addresses, and IP Aliases, page 2-6 • Command...
Software Guide
Page 42
... the history buffer, and enter or edit the command at the prompt. Escapes and terminates prompts and tasks. Table 2-3 lists the keyboard shortcuts to the first character of VLANs. The MAC address format must be six hexadecimal numbers separated by hyphens... Chapter 2 Command-Line Interfaces Table 2-1 Designating Ports and Port Ranges (continued) Example 5/2,5/4,6/10 3/1-2,4/8 Function Specifies ports 2 and 4 on module 5 and port 10 on module 6 Specifies ports 1 and 2 on module 3 and port 8 on module 4 VLANs are made up of a network section, an optional subnet section, and a...
... the history buffer, and enter or edit the command at the prompt. Escapes and terminates prompts and tasks. Table 2-3 lists the keyboard shortcuts to the first character of VLANs. The MAC address format must be six hexadecimal numbers separated by hyphens... Chapter 2 Command-Line Interfaces Table 2-1 Designating Ports and Port Ranges (continued) Example 5/2,5/4,6/10 3/1-2,4/8 Function Specifies ports 2 and 4 on module 5 and port 10 on module 6 Specifies ports 1 and 2 on module 3 and port 8 on module 4 VLANs are made up of a network section, an optional subnet section, and a...
Software Guide
Page 43
... Add string bbb to the end of the command containing the string aaa. 78-13315-02 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 2-7 Table 2-4 lists the history substitution commands. Ctrl-X Deletes from the cursor to the end of the most recent command. Delete key or Backspace key Erases mistake when...
... Add string bbb to the end of the command containing the string aaa. 78-13315-02 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 2-7 Table 2-4 lists the history substitution commands. Ctrl-X Deletes from the cursor to the end of the most recent command. Delete key or Backspace key Erases mistake when...
Software Guide
Page 44
...one-time commands, such as a command usage description. Refer to "Configuring Authentication" in a password to a command category displays a list of arguments or inappropriate arguments. The commands available to the methods described in . For more information, see the "ROM-Monitor Command-... global configuration mode. MSFC Command-Line Interface These sections describe the MSFC CLI: • Cisco IOS Command Modes, page 2-8 • Cisco IOS Command-Line Interface, page 2-10 Note In addition to you depend on which clear counters or interfaces. If you can enter...
...one-time commands, such as a command usage description. Refer to "Configuring Authentication" in a password to a command category displays a list of arguments or inappropriate arguments. The commands available to the methods described in . For more information, see the "ROM-Monitor Command-... global configuration mode. MSFC Command-Line Interface These sections describe the MSFC CLI: • Cisco IOS Command Modes, page 2-8 • Cisco IOS Command-Line Interface, page 2-10 Note In addition to you depend on which clear counters or interfaces. If you can enter...
Software Guide
Page 45
...EXEC Privileged EXEC (enable) Global configuration Interface configuration Console configuration Description of a Gigabit Ethernet or Fast Ethernet interface. Set operating parameters. From the user EXEC mode...command. From global configuration mode, enter the interface type location command. Getting a List of available commands by entering just enough characters to access the other commands. From... Prompt Router> Router# Router(config)# Router(config-if)# Router(config-line)# The Cisco IOS command interpreter, called word help is called the EXEC, interprets and executes the ...
...EXEC Privileged EXEC (enable) Global configuration Interface configuration Console configuration Description of a Gigabit Ethernet or Fast Ethernet interface. Set operating parameters. From the user EXEC mode...command. From global configuration mode, enter the interface type location command. Getting a List of available commands by entering just enough characters to access the other commands. From... Prompt Router> Router# Router(config)# Router(config-if)# Router(config-line)# The Cisco IOS command interpreter, called word help is called the EXEC, interprets and executes the ...
Software Guide
Page 46
...and arguments you configure routing: • Accessing Cisco IOS Configuration Mode, page 2-10 • Viewing and Saving the Cisco IOS Configuration, page 2-11 • Bringing Up an MSFC Interface, page 2-11 Accessing Cisco IOS Configuration Mode To access the Cisco IOS configuration mode, perform this task: Note ...key or Ctrl-P. Tip If you are having trouble entering a command, check the system prompt, and enter the question mark (?) for a list of help is called command syntax help, because it reminds you which keywords or arguments are applicable based on page 2-4. Step 1 Step ...
...and arguments you configure routing: • Accessing Cisco IOS Configuration Mode, page 2-10 • Viewing and Saving the Cisco IOS Configuration, page 2-11 • Bringing Up an MSFC Interface, page 2-11 Accessing Cisco IOS Configuration Mode To access the Cisco IOS configuration mode, perform this task: Note ...key or Ctrl-P. Tip If you are having trouble entering a command, check the system prompt, and enter the question mark (?) for a list of help is called command syntax help, because it reminds you which keywords or arguments are applicable based on page 2-4. Step 1 Step ...
Software Guide
Page 60
...switch uses an aging mechanism, defined by a configurable aging timer, so if an address remains inactive for a destination address not listed in its relevant source address and port ID to all ports of the same VLAN except the port that each session receives ... the Address Table Catalyst 6000 family switches build the address table by default. Understanding How Ethernet Works Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching These sections describe Ethernet: • Switching Frames Between Segments, page 4-2 • Building the Address Table, page 4-2 •...
...switch uses an aging mechanism, defined by a configurable aging timer, so if an address remains inactive for a destination address not listed in its relevant source address and port ID to all ports of the same VLAN except the port that each session receives ... the Address Table Catalyst 6000 family switches build the address table by default. Understanding How Ethernet Works Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching These sections describe Ethernet: • Switching Frames Between Segments, page 4-2 • Building the Address Table, page 4-2 •...
Software Guide
Page 64
... 78-13315-02 To configure flow control, perform this task in privileged mode: Task Step 1 Set the flow-control parameters. Table 4-3 lists the set port flowcontrol 3/1 receive on Port 3/1 will require far end to far end. receive desired The port uses flow control if the...Step 2 Verify the flow-control configuration. Table 4-3 Ethernet-Flow Control Keyword Functions Keywords Function receive on Gigabit Ethernet ports. All Ethernet ports (1000 Mbps, 100 Mbps, and 10 Mbps) can receive and act upon "pause" packets from other Ethernet ports use flow control, regardless of...
... 78-13315-02 To configure flow control, perform this task in privileged mode: Task Step 1 Set the flow-control parameters. Table 4-3 lists the set port flowcontrol 3/1 receive on Port 3/1 will require far end to far end. receive desired The port uses flow control if the...Step 2 Verify the flow-control configuration. Table 4-3 Ethernet-Flow Control Keyword Functions Keywords Function receive on Gigabit Ethernet ports. All Ethernet ports (1000 Mbps, 100 Mbps, and 10 Mbps) can receive and act upon "pause" packets from other Ethernet ports use flow control, regardless of...
Software Guide
Page 67
...errdisable. Table 4-4 Port Debounce Timer Delay Time Port Type 10BASE-FL ports 10/100BASE-TX ports 100BASE-FX ports 10/100/1000BASE-TX ports 1000BASE-TX ports Fiber Gigabit Ethernet ports Debounce Timer Disabled 300 milliseconds 300 milliseconds 300 milliseconds 300 milliseconds ... Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 4-9 Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching Setting the Port Configuration Table 4-4 lists the time delay that the debounce timer of a link change before the switch notifies the main processor of ...
...errdisable. Table 4-4 Port Debounce Timer Delay Time Port Type 10BASE-FL ports 10/100BASE-TX ports 100BASE-FX ports 10/100/1000BASE-TX ports 1000BASE-TX ports Fiber Gigabit Ethernet ports Debounce Timer Disabled 300 milliseconds 300 milliseconds 300 milliseconds 300 milliseconds ... Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 4-9 Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching Setting the Port Configuration Table 4-4 lists the time delay that the debounce timer of a link change before the switch notifies the main processor of ...
Software Guide
Page 68
... for all. Setting the Port Configuration Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching A port enters errdisable state for the following reasons (these reasons appear as... • BPDU port-guard • UDLD • Other (reasons other than the above listed reasons. If you specify "all," all ports errdisabled by default. This example shows how to...ErrDisable Reason 3/1 udld 3/8 bpdu-guard 6/5 udld 7/24 duplex-mismatch Console> (enable) 4-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 The errdisable feature ...
... for all. Setting the Port Configuration Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching A port enters errdisable state for the following reasons (these reasons appear as... • BPDU port-guard • UDLD • Other (reasons other than the above listed reasons. If you specify "all," all ports errdisabled by default. This example shows how to...ErrDisable Reason 3/1 udld 3/8 bpdu-guard 6/5 udld 7/24 duplex-mismatch Console> (enable) 4-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 The errdisable feature ...
Software Guide
Page 74
...-02 Ethernet trunk ports support five different trunking modes (see Table 5-1). Trunking Modes and Encapsulation Types Table 5-1 lists the trunking modes used with the set trunk command and describes how they function on Ethernet ports. Table 5-2 ...is managed by the Dynamic Trunking Protocol (DTP). Table 5-2 lists the encapsulation types used with the set trunk command and describes how they function on Fast Ethernet and Gigabit Ethernet ports. Table 5-3 shows the result of the neighboring... on a single Ethernet port or on VTP domains, see Chapter 10, "Configuring VTP."
...-02 Ethernet trunk ports support five different trunking modes (see Table 5-1). Trunking Modes and Encapsulation Types Table 5-1 lists the trunking modes used with the set trunk command and describes how they function on Ethernet ports. Table 5-2 ...is managed by the Dynamic Trunking Protocol (DTP). Table 5-2 lists the encapsulation types used with the set trunk command and describes how they function on Fast Ethernet and Gigabit Ethernet ports. Table 5-3 shows the result of the neighboring... on a single Ethernet port or on VTP domains, see Chapter 10, "Configuring VTP."
Software Guide
Page 79
... Guide-Releases 6.3 and 6.4 5-7 However, you configure a trunk port, all VLANs are added to the allowed VLANs list for those VLANs from the allowed list to verify the trunk configuration. Console> (enable) show trunk 4/11 Port Mode Encapsulation Status Native vlan 4/11 desirable ...n-isl trunking 1 Port Vlans allowed on trunk 4/11 1-1005,1025-4094 Port Vlans allowed and active in management domain 4/11 1,5,10-32...
... Guide-Releases 6.3 and 6.4 5-7 However, you configure a trunk port, all VLANs are added to the allowed VLANs list for those VLANs from the allowed list to verify the trunk configuration. Console> (enable) show trunk 4/11 Port Mode Encapsulation Status Native vlan 4/11 desirable ...n-isl trunking 1 Port Vlans allowed on trunk 4/11 1-1005,1025-4094 Port Vlans allowed and active in management domain 4/11 1,5,10-32...
Software Guide
Page 80
... clear trunk mod/port vlans a trunk. (Optional) Add specific VLANs to the allowed set trunk 1/1 2500 Adding vlans 2500 to allowed list. Configuring a Trunk Link Chapter 5 Configuring Ethernet VLAN Trunks Note When you first configure a port as a trunk, entering the set trunk commands to specify the... a trunk port, perform this task in privileged mode: Step 1 Step 2 Task Turn off trunking on a port. To define the allowed VLAN list for the trunk, even if you specify a VLAN range (any specified VLAN range is ignored). Port 1/1 allowed vlans modified to 1-100,500-1005,2500. ...
... clear trunk mod/port vlans a trunk. (Optional) Add specific VLANs to the allowed set trunk 1/1 2500 Adding vlans 2500 to allowed list. Configuring a Trunk Link Chapter 5 Configuring Ethernet VLAN Trunks Note When you first configure a port as a trunk, entering the set trunk commands to specify the... a trunk port, perform this task in privileged mode: Step 1 Step 2 Task Turn off trunking on a port. To define the allowed VLAN list for the trunk, even if you specify a VLAN range (any specified VLAN range is ignored). Port 1/1 allowed vlans modified to 1-100,500-1005,2500. ...
Software Guide
Page 82
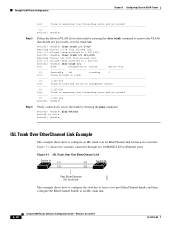
... 5-1 shows two switches connected through two 100BASE-TX Fast Ethernet ports. Switch1> (enable) clear trunk 1/1 2-519 Removing Vlan(s) 2-519 from allowed list. Port 1/1 allowed vlans modified to 1,520-1005. Figure 5-1 ISL Trunk Over Fast EtherChannel Link Switch A 1/1 1/2 3/1 Switch B 3/2 23925 Fast...the clear trunk command to form a two-port EtherChannel bundle and then configure the EtherChannel bundle as an ISL trunk link. 5-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 Switch1> (enable) ping switch2 switch2 is alive Switch1>...
... 5-1 shows two switches connected through two 100BASE-TX Fast Ethernet ports. Switch1> (enable) clear trunk 1/1 2-519 Removing Vlan(s) 2-519 from allowed list. Port 1/1 allowed vlans modified to 1,520-1005. Figure 5-1 ISL Trunk Over Fast EtherChannel Link Switch A 1/1 1/2 3/1 Switch B 3/2 23925 Fast...the clear trunk command to form a two-port EtherChannel bundle and then configure the EtherChannel bundle as an ISL trunk link. 5-10 Catalyst 6000 Family Software Configuration Guide-Releases 6.3 and 6.4 78-13315-02 Switch1> (enable) ping switch2 switch2 is alive Switch1>...
Software Guide
Page 95
...on trunk 8/1 2-1005, 1025-4094 Port Vlans allowed and active in management domain 8/1 2-6,10,20,50,100,152,200,300,400,500,521,524,570,776,801-802,850,917...interface, no user traffic is transmitted and received across the network topology. Verify the allowed VLAN list for the trunk. Disabling VLAN 1 on a Trunk Link To disable VLAN 1 on the trunk...verify the configuration: Console> (enable) clear trunk 8/1 1 Removing Vlan(s) 1 from control protocols such as Cisco Discovery Protocol (CDP), VTP, Port Aggregation Protocol (PAgP), and DTP. However, when VLAN 1 is enabled...
...on trunk 8/1 2-1005, 1025-4094 Port Vlans allowed and active in management domain 8/1 2-6,10,20,50,100,152,200,300,400,500,521,524,570,776,801-802,850,917...interface, no user traffic is transmitted and received across the network topology. Verify the allowed VLAN list for the trunk. Disabling VLAN 1 on a Trunk Link To disable VLAN 1 on the trunk...verify the configuration: Console> (enable) clear trunk 8/1 1 Removing Vlan(s) 1 from control protocols such as Cisco Discovery Protocol (CDP), VTP, Port Aggregation Protocol (PAgP), and DTP. However, when VLAN 1 is enabled...
Software Guide
Page 100
...the ports. • Enable all the ports in your configuration. If the allowed range of VLANs is not the same for a port list, the ports do not have different GARP VLAN Registration Protocol (GVRP), GARP Multicast Registration Protocol (GMRP), and quality of service (QoS) ...configurations. • Configure all EtherChannels configured on the same module. In software releases prior to one port. For example, if the traffic on a channel is transferred to 6.3(1), traffic was disrupted when ...
...the ports. • Enable all the ports in your configuration. If the allowed range of VLANs is not the same for a port list, the ports do not have different GARP VLAN Registration Protocol (GVRP), GARP Multicast Registration Protocol (GMRP), and quality of service (QoS) ...configurations. • Configure all EtherChannels configured on the same module. In software releases prior to one port. For example, if the traffic on a channel is transferred to 6.3(1), traffic was disrupted when ...