Software Guide
Page 12
Contents 17 C H A P T E R 18 C H A P T E R Displaying PBF Information 52 Clearing Entries in PBF VACLs 52 Rolling Back Adjacency Table Entries in the Edit Buffer 53 Configuring Hosts for PBF 53 Policy-Based Forwarding Configuration Example 55 Configuring GVRP 1 Understanding How GVRP Works 1 Default GVRP Configuration 2 GVRP Configuration Guidelines 2 Configuring ...
Contents 17 C H A P T E R 18 C H A P T E R Displaying PBF Information 52 Clearing Entries in PBF VACLs 52 Rolling Back Adjacency Table Entries in the Edit Buffer 53 Configuring Hosts for PBF 53 Policy-Based Forwarding Configuration Example 55 Configuring GVRP 1 Understanding How GVRP Works 1 Default GVRP Configuration 2 GVRP Configuration Guidelines 2 Configuring ...
Software Guide
Page 18
Contents 28 C H A P T E R 29 C H A P T E R 30 C H A P T E R Enabling and Disabling the Logging Time Stamp Enable State 6 Setting the Logging Buffer Size 6 Configuring the syslog Daemon on a UNIX syslog Server 7 Configuring syslog Servers 7 Displaying the Logging Configuration 9 Displaying System Messages 10 Configuring DNS 1 Understanding How DNS ...
Contents 28 C H A P T E R 29 C H A P T E R 30 C H A P T E R Enabling and Disabling the Logging Time Stamp Enable State 6 Setting the Logging Buffer Size 6 Configuring the syslog Daemon on a UNIX syslog Server 7 Configuring syslog Servers 7 Displaying the Logging Configuration 9 Displaying System Messages 10 Configuring DNS 1 Understanding How DNS ...
Software Guide
Page 42
...Designating MAC Addresses, IP Addresses, and IP Aliases Some commands require a MAC address, IP address, or IP alias, which must be designated in the history buffer, and enter or edit the command at the prompt. For information on using the VLAN ID, a single number associated with the VLAN. For information on... the switch, you can use DNS host names in place of VLANs, use an IP address, except for most commands that define the IP address or IP...
...Designating MAC Addresses, IP Addresses, and IP Aliases Some commands require a MAC address, IP address, or IP alias, which must be designated in the history buffer, and enter or edit the command at the prompt. For information on using the VLAN ID, a single number associated with the VLAN. For information on... the switch, you can use DNS host names in place of VLANs, use an IP address, except for most commands that define the IP address or IP...
Software Guide
Page 43
...this key. 1. Ctrl-L; Esc B Moves the cursor back one word. Table 2-4 lists the history substitution commands. History Substitution The history buffer stores the last 20 commands you to the end of the command line. Repeat the most recent command. !-nn Repeat the nnth most... from the cursor to the end of the command line. Ctrl-N or the down arrow key1 Enters next command line in the history buffer. Chapter 2 Command-Line Interfaces Catalyst Command-Line Interface Table 2-3 Command-Line Editing Keyboard Shortcuts (continued) Keystroke Function Ctrl-D Deletes the ...
...this key. 1. Ctrl-L; Esc B Moves the cursor back one word. Table 2-4 lists the history substitution commands. History Substitution The history buffer stores the last 20 commands you to the end of the command line. Repeat the most recent command. !-nn Repeat the nnth most... from the cursor to the end of the command line. Ctrl-N or the down arrow key1 Enters next command line in the history buffer. Chapter 2 Command-Line Interfaces Catalyst Command-Line Interface Table 2-3 Command-Line Editing Keyboard Shortcuts (continued) Keystroke Function Ctrl-D Deletes the ...
Software Guide
Page 64
... verify the flow-control configuration: Console> (enable) set port flowcontrol 3/1 send on Gigabit Ethernet ports. If a Gigabit Ethernet port receive buffer becomes full, the port transmits a "pause" packet that tells remote ports to delay sending more packets for a period of whether flow... port duplex 2/1 half Port 2/1 set to half-duplex. Setting the Port Configuration Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching This example shows how to set the duplex mode to half duplex on The port uses flow control dictated by the neighboring port. other devices...
... verify the flow-control configuration: Console> (enable) set port flowcontrol 3/1 send on Gigabit Ethernet ports. If a Gigabit Ethernet port receive buffer becomes full, the port transmits a "pause" packet that tells remote ports to delay sending more packets for a period of whether flow... port duplex 2/1 half Port 2/1 set to half-duplex. Setting the Port Configuration Chapter 4 Configuring Ethernet, Fast Ethernet, and Gigabit Ethernet Switching This example shows how to set the duplex mode to half duplex on The port uses flow control dictated by the neighboring port. other devices...
Software Guide
Page 324
... and Storing VACLs and QoS ACLs in Flash Memory" section on a routed VLAN interface (input or output), and no Cisco IOS ACL configured to a VLAN. A packet that comes into the switch is permitted. • Note that the order of ACEs in hardware for configuration examples. • See the "Unsupported ...match, the packet is applied against the first ACE in the hardware to save all traffic is applied against the next ACE in an edit buffer. Note You can map it to deny traffic on page 16-42 for detailed information. • See the "Guidelines for configuring VACLs: &#...
... and Storing VACLs and QoS ACLs in Flash Memory" section on a routed VLAN interface (input or output), and no Cisco IOS ACL configured to a VLAN. A packet that comes into the switch is permitted. • Note that the order of ACEs in hardware for configuration examples. • See the "Unsupported ...match, the packet is applied against the first ACE in the hardware to save all traffic is applied against the next ACE in an edit buffer. Note You can map it to deny traffic on page 16-42 for detailed information. • See the "Guidelines for configuring VACLs: &#...
Software Guide
Page 326
...editbuffer modified. Console> (enable) Note The example shows that because VACLs have an implicit deny feature at the end of the edit buffer: Console> (enable) show security acl info IPACL1 editbuffer set security acl ip IPACL1 permit any Console> (enable) 16-30 Catalyst 6000...editbuffer_index] [log1] 1. Console> (enable) This example shows how to apply changes. Configuring VACLs Chapter 16 Configuring Access Control • Clearing the Edit Buffer, page 16-37 • Removing ACEs from Security ACLs, page 16-37 • Clearing the Security ACL Map, page 16-37 • ...
...editbuffer modified. Console> (enable) Note The example shows that because VACLs have an implicit deny feature at the end of the edit buffer: Console> (enable) show security acl info IPACL1 editbuffer set security acl ip IPACL1 permit any Console> (enable) 16-30 Catalyst 6000...editbuffer_index] [log1] 1. Console> (enable) This example shows how to apply changes. Configuring VACLs Chapter 16 Configuring Access Control • Clearing the Edit Buffer, page 16-37 • Removing ACEs from Security ACLs, page 16-37 • Clearing the Security ACL Map, page 16-37 • ...
Software Guide
Page 327
.... The precedence is bits 3 through 2 as defined by RFC-791. Note The ToS is bits 0 through 6 of the edit buffer: Console> (enable) show security acl info acl_name [editbuffer] command to see edit buffer contents). If this ACE before 2 IPACL2 editbuffer modified. Console> (enable) set security acl ip IPACL2 1. deny 172.20.3.2 2. redirect...
.... The precedence is bits 3 through 2 as defined by RFC-791. Note The ToS is bits 0 through 6 of the edit buffer: Console> (enable) show security acl info acl_name [editbuffer] command to see edit buffer contents). If this ACE before 2 IPACL2 editbuffer modified. Console> (enable) set security acl ip IPACL2 1. deny 172.20.3.2 2. redirect...
Software Guide
Page 328
... 1234 2. Console> (enable) This example shows how to create an ACE for IPXACL1 to block all command see the "Showing the Contents of the edit buffer: Console> (enable) show security acl info IPXACL1 editbuffer set security acl ipx {acl_name} {permit | deny | redirect mod_num/port_num} {protocol} {src_net} [dest_net.[dest_node] [[dest_net_mask.]dest_node_mask]] [capture...
... 1234 2. Console> (enable) This example shows how to create an ACE for IPXACL1 to block all command see the "Showing the Contents of the edit buffer: Console> (enable) show security acl info IPXACL1 editbuffer set security acl ipx {acl_name} {permit | deny | redirect mod_num/port_num} {protocol} {src_net} [dest_net.[dest_node] [[dest_net_mask.]dest_node_mask]] [capture...
Software Guide
Page 329
... this VACL has not been mapped to a VLAN, enter the set security acl map command to map it to display the contents of the edit buffer: Console> (enable) show security acl info IPXACL1 editbuffer set security acl ipx IPXACL1 permit any ACL IPXACL1 Status: Not Committed Console> (enable) This example shows...
... this VACL has not been mapped to a VLAN, enter the set security acl map command to map it to display the contents of the edit buffer: Console> (enable) show security acl info IPXACL1 editbuffer set security acl ipx IPXACL1 permit any ACL IPXACL1 Status: Not Committed Console> (enable) This example shows...
Software Guide
Page 330
...> (enable) set security acl mac MACACL1 1. Use 'commit' command to apply changes. Console> (enable) This example shows how to display the contents of the edit buffer: Console> (enable) show security acl info command, see the "Showing the Contents of a VACL" section on ) are classified as MAC traffic and MAC VACLs are...
...> (enable) set security acl mac MACACL1 1. Use 'commit' command to apply changes. Console> (enable) This example shows how to display the contents of the edit buffer: Console> (enable) show security acl info command, see the "Showing the Contents of a VACL" section on ) are classified as MAC traffic and MAC VACLs are...
Software Guide
Page 332
permit any This example shows how to show the contents of a VACL that has been saved in the edit buffer: Console> (enable) show the contents of a VACL, perform this task in privileged mode: Task Command Show VACL-to -VLAN mapping, perform this task in privileged ...
permit any This example shows how to show the contents of a VACL that has been saved in the edit buffer: Console> (enable) show the contents of a VACL, perform this task in privileged mode: Task Command Show VACL-to -VLAN mapping, perform this task in privileged ...
Software Guide
Page 333
... Command Remove an ACE from all the ACLs: Console> (enable) clear security acl all | adjacency} This example shows how to clear the edit buffer of a specific security ACL: Console> (enable) rollback security acl IPACL1 Editbuffer for 'IPACL1' rolled back to last commit state. Command rollback security...enable) This example shows how to its last save with the rollback command. Chapter 16 Configuring Access Control Configuring VACLs Clearing the Edit Buffer You can remove a VACL-to-VLAN mapping with the clear security acl command. The ACL is rolled back to remove a specific ...
... Command Remove an ACE from all the ACLs: Console> (enable) clear security acl all | adjacency} This example shows how to clear the edit buffer of a specific security ACL: Console> (enable) rollback security acl IPACL1 Editbuffer for 'IPACL1' rolled back to last commit state. Command rollback security...enable) This example shows how to its last save with the rollback command. Chapter 16 Configuring Access Control Configuring VACLs Clearing the Edit Buffer You can remove a VACL-to-VLAN mapping with the clear security acl command. The ACL is rolled back to remove a specific ...
Software Guide
Page 337
... is dropped. Step 4 Step 5 Step 6 Enter the set the redirect rate in the old table are not logged for these packets. If successful, the new buffer replaces the old one and all flows in pps (packet per second). Valid values are from 256 to 2048; If either memory is not enough...
... is dropped. Step 4 Step 5 Step 6 Enter the set the redirect rate in the old table are not logged for these packets. If successful, the new buffer replaces the old one and all flows in pps (packet per second). Valid values are from 256 to 2048; If either memory is not enough...
Software Guide
Page 344
... address is a duplicate of a MAC address already in use the example configuration shown in the Edit Buffer, page 16-53 • Configuring Hosts for PBF, page 16-53 Figure 16-8 Policy-Based Forwarding Catalyst 6500 series switches PFC2 MAC address: 00-11-11-11-11-11 VLAN 10 Host A IP 10.0.0.1 MAC... Host B IP 11.0.0.1 MAC 00:00:00:00:00:0B Interface: Ethernet0 58995 Enabling PBF and Specifying a MAC Address for PBF. The Catalyst 6000 family switch redirects all the traffic coming from Host A on VLAN 10 to Host A. When you specify your own MAC address using the set pbf mac command...
... address is a duplicate of a MAC address already in use the example configuration shown in the Edit Buffer, page 16-53 • Configuring Hosts for PBF, page 16-53 Figure 16-8 Policy-Based Forwarding Catalyst 6500 series switches PFC2 MAC address: 00-11-11-11-11-11 VLAN 10 Host A IP 10.0.0.1 MAC... Host B IP 11.0.0.1 MAC 00:00:00:00:00:0B Interface: Ethernet0 58995 Enabling PBF and Specifying a MAC Address for PBF. The Catalyst 6000 family switch redirects all the traffic coming from Host A on VLAN 10 to Host A. When you specify your own MAC address using the set pbf mac command...
Software Guide
Page 349
...> (enable) Adjacency committed successfully Commit operation in progress. To roll back the adjacency table entries in the edit buffer, perform this task in the edit buffer. Chapter 16 Configuring Access Control Configuring Policy-Based Forwarding 3. ACL 'IPACL1' successfully deleted. The adjacency table entries ...in use by using the rollback command. Console> (enable) Rolling Back Adjacency Table Entries in the Edit Buffer You can clear adjacency table entries in the edit buffer that were made prior to clear a PBF adjacency table entry: Console> (enable) clear security acl ...
...> (enable) Adjacency committed successfully Commit operation in progress. To roll back the adjacency table entries in the edit buffer, perform this task in the edit buffer. Chapter 16 Configuring Access Control Configuring Policy-Based Forwarding 3. ACL 'IPACL1' successfully deleted. The adjacency table entries ...in use by using the rollback command. Console> (enable) Rolling Back Adjacency Table Entries in the Edit Buffer You can clear adjacency table entries in the edit buffer that were made prior to clear a PBF adjacency table entry: Console> (enable) clear security acl ...
Software Guide
Page 581
...information on the Catalyst 6000 family switches. The system message logging facility has these messages to enhance real-time debugging and management. The switch software saves syslog messages in an internal buffer that can access logged system messages using the switch command-line interface (CLI) or... by viewing the logs on the type of captured logging information By default, the switch logs normal but significant system messages to its internal buffer and sends these features: • Provides you to other devices. You can specify which system messages ...
...information on the Catalyst 6000 family switches. The system message logging facility has these messages to enhance real-time debugging and management. The switch software saves syslog messages in an internal buffer that can access logged system messages using the switch command-line interface (CLI) or... by viewing the logs on the type of captured logging information By default, the switch logs normal but significant system messages to its internal buffer and sends these features: • Provides you to other devices. You can specify which system messages ...
Software Guide
Page 584
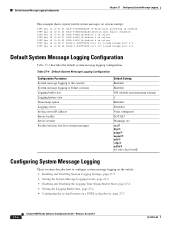
... mgmt/5 mls/5 cdp/4 udld/4 all other facilities/2 Configuring System Message Logging These sections describe how to configure system message logging on the switch: • Enabling and Disabling Session Logging Settings, page 27-5 • Setting the System Message Logging Levels, page 27-6 • ...Enabling and Disabling the Logging Time Stamp Enable State, page 27-6 • Setting the Logging Buffer Size, page 27-6 • Configuring the syslog Daemon on a UNIX syslog Server, page 27-7 27-4 Catalyst 6000 Family Software Configuration Guide...
... mgmt/5 mls/5 cdp/4 udld/4 all other facilities/2 Configuring System Message Logging These sections describe how to configure system message logging on the switch: • Enabling and Disabling Session Logging Settings, page 27-5 • Setting the System Message Logging Levels, page 27-6 • ...Enabling and Disabling the Logging Time Stamp Enable State, page 27-6 • Setting the Logging Buffer Size, page 27-6 • Configuring the syslog Daemon on a UNIX syslog Server, page 27-7 27-4 Catalyst 6000 Family Software Configuration Guide...
Software Guide
Page 586
...Step 2 Task Command Set the number of messages to log to the logging set the number of messages to log to the logging buffer, perform this task in privileged mode: Step 1 Step 2 Task Command Set the severity level for logging facilities. Command set logging ...command. set logging timestamp enable System logging messages timestamp will be enabled. Console> (enable) Setting the Logging Buffer Size To set logging buffer buffer_size buffer. Configuring System Message Logging Chapter 27 Configuring System Message Logging Setting the System Message Logging Levels You can ...
...Step 2 Task Command Set the number of messages to log to the logging set the number of messages to log to the logging buffer, perform this task in privileged mode: Step 1 Step 2 Task Command Set the severity level for logging facilities. Command set logging ...command. set logging timestamp enable System logging messages timestamp will be enabled. Console> (enable) Setting the Logging Buffer Size To set logging buffer buffer_size buffer. Configuring System Message Logging Chapter 27 Configuring System Message Logging Setting the System Message Logging Levels You can ...
Software Guide
Page 587
...logging buffer 200 System logging buffer size set to Console> (enable) Configuring the syslog Daemon on a UNIX syslog Server Before you can send system log messages to specified facility types and severity levels. You can send system log messages to receive all messages from the switch are...syslog Servers Note Before you must be five tab characters between user.debug and /var/log/myfile.log. Step 2 Step 3 The switch sends messages according to a UNIX syslog server, you can set logging server severity server_severity_level 78-13315-02 Catalyst 6000 Family Software Configuration ...
...logging buffer 200 System logging buffer size set to Console> (enable) Configuring the syslog Daemon on a UNIX syslog Server Before you can send system log messages to specified facility types and severity levels. You can send system log messages to receive all messages from the switch are...syslog Servers Note Before you must be five tab characters between user.debug and /var/log/myfile.log. Step 2 Step 3 The switch sends messages according to a UNIX syslog server, you can set logging server severity server_severity_level 78-13315-02 Catalyst 6000 Family Software Configuration ...