Reference Manual
Page 3
... by Data Processing Equipment and Electronic Office Machines aimed at preventing radio interference in the documentation and/or other materials provided with or without his specific prior written permission. All rights reserved. iii v1.0, September 2006 Voluntary Control Council for purpose. The copyright holder's name must reproduce the above copyright notice...
... by Data Processing Equipment and Electronic Office Machines aimed at preventing radio interference in the documentation and/or other materials provided with or without his specific prior written permission. All rights reserved. iii v1.0, September 2006 Voluntary Control Council for purpose. The copyright holder's name must reproduce the above copyright notice...
Reference Manual
Page 5
... IMPLIED WARRANTIES OF MERCHANTIBILITY AND FITNESS FOR A PARTICULAR PURPOSE. Copyright (C) 1995-2002 Jean-loup Gailly and Mark Adler. This software is provided 'as is ', without specific prior written permission. MD5 Message-Digest Algorithm" in all material mentioning or referencing this software or this documentation and/or software. Permission is not required...
... IMPLIED WARRANTIES OF MERCHANTIBILITY AND FITNESS FOR A PARTICULAR PURPOSE. Copyright (C) 1995-2002 Jean-loup Gailly and Mark Adler. This software is provided 'as is ', without specific prior written permission. MD5 Message-Digest Algorithm" in all material mentioning or referencing this software or this documentation and/or software. Permission is not required...
Reference Manual
Page 8
... Example 3-9 RIP Configuration 3-10 Enabling Trend Micro Antivirus Enforcement 3-12 Chapter 4 Firewall Protection and Content Filtering About Firewall Security 4-1 Using Rules to Block or Allow Specific Kinds of Traffic 4-1 Services-Based Rules 4-2 Outbound Rules (Service Blocking 4-2 Inbound Rules (Port Forwarding 4-4 Order of Precedence for Firewall Rules 4-6 Setting LAN WAN Rules 4-7 LAN...
... Example 3-9 RIP Configuration 3-10 Enabling Trend Micro Antivirus Enforcement 3-12 Chapter 4 Firewall Protection and Content Filtering About Firewall Security 4-1 Using Rules to Block or Allow Specific Kinds of Traffic 4-1 Services-Based Rules 4-2 Outbound Rules (Service Blocking 4-2 Inbound Rules (Port Forwarding 4-4 Order of Precedence for Firewall Rules 4-6 Setting LAN WAN Rules 4-7 LAN...
Reference Manual
Page 11
... 7-5 Testing the Path from Your PC to a Remote Device 7-6 Restoring the Default Configuration and Password 7-7 Problems with Date and Time 7-7 Appendix A Default Settings and Technical Specifications Appendix B Related Documents Index xi v1.0, September 2006
... 7-5 Testing the Path from Your PC to a Remote Device 7-6 Restoring the Default Configuration and Password 7-7 Problems with Date and Time 7-7 Appendix A Default Settings and Technical Specifications Appendix B Related Documents Index xi v1.0, September 2006
Reference Manual
Page 14
...displays the table of the full manual and individual chapters. The Acrobat reader is written for the VPN firewall according to these specifications: Product Version Manual Publication Date ProSafe VPN Firewall 50 September 2006 For more information about network, Internet, firewall, and VPN technologies..., see the links to the NETGEAR website in the manual. •A button to PDF versions of contents and an button. FVS338 ProSafe VPN Firewall 50 Reference Manual ...
...displays the table of the full manual and individual chapters. The Acrobat reader is written for the VPN firewall according to these specifications: Product Version Manual Publication Date ProSafe VPN Firewall 50 September 2006 For more information about network, Internet, firewall, and VPN technologies..., see the links to the NETGEAR website in the manual. •A button to PDF versions of contents and an button. FVS338 ProSafe VPN Firewall 50 Reference Manual ...
Reference Manual
Page 19
..., gateway, and domain name server (DNS) addresses, to attached PCs on the LAN using only a single IP address, which you to direct incoming traffic to specific PCs based on your PC. When DHCP is enabled and no DNS addresses are autosensing and capable of the incoming request. Introduction 1-3 v1.0, September 2006...
..., gateway, and domain name server (DNS) addresses, to attached PCs on the LAN using only a single IP address, which you to direct incoming traffic to specific PCs based on your PC. When DHCP is enabled and no DNS addresses are autosensing and capable of the incoming request. Introduction 1-3 v1.0, September 2006...
Reference Manual
Page 20
... Introduction v1.0, September 2006 The VPN firewall includes the NETGEAR VPN Wizard to easily configure VPN tunnels according to the recommendations of the Virtual Private Network Consortium (VPNC) to ensure the VPN tunnels are specifically built to let you monitor and manage log resources from ...almost any type of Internet connection, asking you only for the information required for your NETGEAR VPN Firewall to enforce antivirus policies - Unlike competing antivirus...
... Introduction v1.0, September 2006 The VPN firewall includes the NETGEAR VPN Wizard to easily configure VPN tunnels according to the recommendations of the Virtual Private Network Consortium (VPNC) to ensure the VPN tunnels are specifically built to let you monitor and manage log resources from ...almost any type of Internet connection, asking you only for the information required for your NETGEAR VPN Firewall to enforce antivirus policies - Unlike competing antivirus...
Reference Manual
Page 32
.... The Initial string is listed in the modem's user manual. e. use ISP assigned DNS server addresses (default). To use for manual intervention.: a. Enter any modem specific parameters to connect automatically. Check the Connect automatically disconnect after idle for pulse mode dialing. Internet (IP Address). The default setting of the router and...
.... The Initial string is listed in the modem's user manual. e. use ISP assigned DNS server addresses (default). To use for manual intervention.: a. Enter any modem specific parameters to connect automatically. Check the Connect automatically disconnect after idle for pulse mode dialing. Internet (IP Address). The default setting of the router and...
Reference Manual
Page 34
THe standard value is rarely required, and should not be done unless specifically required by the ISP, To change the standard MTU (Maximum Transmit Unit) value for your settings. 2-8 Connecting the FVS338 to save your dialup modem: 1. However, ...
THe standard value is rarely required, and should not be done unless specifically required by the ISP, To change the standard MTU (Maximum Transmit Unit) value for your settings. 2-8 Connecting the FVS338 to save your dialup modem: 1. However, ...
Reference Manual
Page 40
... not available. before restarting the counter. Internet Traffic Statistics This displays statistics on page 4-27). The volume of the Specific Time month. If this function to work (see "E-Mail counter Notifications of the month from the Internet will be applied...- FVS338 ProSafe VPN Firewall 50 Reference Manual Table 2-2. Traffic Meter Settings Parameter Description Enable Traffic Meter Check this is specific to continue accessing the Internet. the entire configuration is selected the specified restriction will be applied when traffic limit is reached...
... not available. before restarting the counter. Internet Traffic Statistics This displays statistics on page 4-27). The volume of the Specific Time month. If this function to work (see "E-Mail counter Notifications of the month from the Internet will be applied...- FVS338 ProSafe VPN Firewall 50 Reference Manual Table 2-2. Traffic Meter Settings Parameter Description Enable Traffic Meter Check this is specific to continue accessing the Internet. the entire configuration is selected the specified restriction will be applied when traffic limit is reached...
Reference Manual
Page 59
...It also provides various firewall activity reports and instant alerts via e-mail. About Firewall Security A firewall is in response to access specific resources. The default rules of router that protects one network (the "trusted" network, such as Block Sites and Keyword Blocking. ...the LAN side. Unlike simple Internet sharing NAT routers, a firewall uses a process called stateful packet inspection to block or allow specific traffic passing through from attacks and intrusions. Chapter 4 Firewall Protection and Content Filtering The ProSafe VPN Firewall 50 provides you with...
...It also provides various firewall activity reports and instant alerts via e-mail. About Firewall Security A firewall is in response to access specific resources. The default rules of router that protects one network (the "trusted" network, such as Block Sites and Keyword Blocking. ...the LAN side. Unlike simple Internet sharing NAT routers, a firewall uses a process called stateful packet inspection to block or allow specific traffic passing through from attacks and intrusions. Chapter 4 Firewall Protection and Content Filtering The ProSafe VPN Firewall 50 provides you with...
Reference Manual
Page 63
... map to the policy. Select the desired option: • Any - WAN Destination IP Address QoS Priority These settings determine the destination IP address applicable to a specific port. it accordingly. This setting determines the priority of a service, which in turn, determines the quality of that service for packets covered by this rule...
... map to the policy. Select the desired option: • Any - WAN Destination IP Address QoS Priority These settings determine the destination IP address applicable to a specific port. it accordingly. This setting determines the priority of a service, which in turn, determines the quality of that service for packets covered by this rule...
Reference Manual
Page 64
... is subjected to turn on the server application security and invoke the user password or privilege levels, if provided. If you should place the most specific services or addresses).
... is subjected to turn on the server application security and invoke the user password or privilege levels, if provided. If you should place the most specific services or addresses).
Reference Manual
Page 65
...; Up - Setting LAN WAN Rules FVS338 ProSafe VPN Firewall 50 Reference Manual The Default Outbound Policy is to allow all outbound traffic and enable only specific services to pass through . Firewall rules can be applied to block...
...; Up - Setting LAN WAN Rules FVS338 ProSafe VPN Firewall 50 Reference Manual The Default Outbound Policy is to allow all outbound traffic and enable only specific services to pass through . Firewall rules can be applied to block...
Reference Manual
Page 66
... custom rules, you can also tailor these rules to save the data (see "Administrator Information" on page 4-3). 3. Complete the Outbound Service screen, and save your specific needs (see Table 4-1 on page 431). to select all rules. FVS338 ProSafe VPN Firewall 50 Reference Manual • Down - Incorrect configuration will display. 2.
... custom rules, you can also tailor these rules to save the data (see "Administrator Information" on page 4-3). 3. Complete the Outbound Service screen, and save your specific needs (see Table 4-1 on page 431). to select all rules. FVS338 ProSafe VPN Firewall 50 Reference Manual • Down - Incorrect configuration will display. 2.
Reference Manual
Page 67
WAN Users: Whether all existing rules for inbound traffic. Figure 4-3 LAN WAN Inbound Services Rules This Inbound Services Rules table lists all WAN addresses or specific IP addresses are included in the rule. Click Add under the Inbound Services Table. Click Reset to cancel your settings and return to the Inbound ...
WAN Users: Whether all existing rules for inbound traffic. Figure 4-3 LAN WAN Inbound Services Rules This Inbound Services Rules table lists all WAN addresses or specific IP addresses are included in the rule. Click Add under the Inbound Services Table. Click Reset to cancel your settings and return to the Inbound ...
Reference Manual
Page 68
... denial of service attack in the LAN and WAN networks. FVS338 ProSafe VPN Firewall 50 Reference Manual Figure 4-4 Attack Checks This screen allows you have a specific diagnostic reason to do so. - When enabled, the router will not respond to port scans from a SYN flood attack. 4-10 Firewall Protection and Content Filtering...
... denial of service attack in the LAN and WAN networks. FVS338 ProSafe VPN Firewall 50 Reference Manual Figure 4-4 Attack Checks This screen allows you have a specific diagnostic reason to do so. - When enabled, the router will not respond to port scans from a SYN flood attack. 4-10 Firewall Protection and Content Filtering...
Reference Manual
Page 78
...to save your settings and revert to the previous settings. 5. Select Security from the main menu and Schedule from the sub-menu. If you chose Specific Days, check the radio button for each day you to specify when blocking will be in effect. 3. Figure 4-13 4-20 Firewall Protection and ...of the Schedules-Schedule 1, Schedule 2 or Schedule 3. The firewall allows you want the schedule to be enforced by configuring one of day: All Day, or Specific Times. If you can set to a schedule for Schedule 2 and Schedule 3. Repeat these 5 steps to set up a schedule for when blocking occurs or ...
...to save your settings and revert to the previous settings. 5. Select Security from the main menu and Schedule from the sub-menu. If you chose Specific Days, check the radio button for each day you to specify when blocking will be in effect. 3. Figure 4-13 4-20 Firewall Protection and ...of the Schedules-Schedule 1, Schedule 2 or Schedule 3. The firewall allows you want the schedule to be enforced by configuring one of day: All Day, or Specific Times. If you can set to a schedule for Schedule 2 and Schedule 3. Repeat these 5 steps to set up a schedule for when blocking occurs or ...
Reference Manual
Page 89
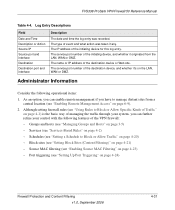
... Block Sites (Content Filtering)" on page 4-23) - Schedules (see "Setting Up Port Triggering" on page 4-20) - Port triggering (see "Setting a Schedule to Block or Allow Specific Kinds of Traffic" on page 4-1) is the basic way of the destination device, and whether it originated from a central location (see "Enabling Remote Management Access...
... Block Sites (Content Filtering)" on page 4-23) - Schedules (see "Setting Up Port Triggering" on page 4-20) - Port triggering (see "Setting a Schedule to Block or Allow Specific Kinds of Traffic" on page 4-1) is the basic way of the destination device, and whether it originated from a central location (see "Enabling Remote Management Access...
Reference Manual
Page 130
... is applied to a Group (you define your network are covered by this rule. FVS338 ProSafe VPN Firewall 50 Reference Manual Service Blocking You can control specific outbound traffic (for example., from LAN to a single Internet IP address. - If you have not defined any rules, only the default rule will be covered...
... is applied to a Group (you define your network are covered by this rule. FVS338 ProSafe VPN Firewall 50 Reference Manual Service Blocking You can control specific outbound traffic (for example., from LAN to a single Internet IP address. - If you have not defined any rules, only the default rule will be covered...