Reference Manual
Page 8
... and Content Filtering About Firewall Security 4-1 Using Rules to Block or Allow Specific Kinds of Traffic 4-1 Services-Based Rules 4-2 Outbound Rules (Service Blocking 4-2 Inbound Rules (Port Forwarding 4-4 Order of Precedence for Firewall Rules 4-6 Setting LAN WAN Rules 4-7 LAN WAN Outbound Services Rules 4-8 LAN WAN Inbound Services Rules 4-9 Attack Checks ...4-10 Inbound Rules...
... and Content Filtering About Firewall Security 4-1 Using Rules to Block or Allow Specific Kinds of Traffic 4-1 Services-Based Rules 4-2 Outbound Rules (Service Blocking 4-2 Inbound Rules (Port Forwarding 4-4 Order of Precedence for Firewall Rules 4-6 Setting LAN WAN Rules 4-7 LAN WAN Outbound Services Rules 4-8 LAN WAN Inbound Services Rules 4-9 Attack Checks ...4-10 Inbound Rules...
Reference Manual
Page 10
...Firewall Features That Reduce Traffic 6-1 Service Blocking 6-2 Block Sites ...6-3 Source MAC Filtering 6-4 VPN Firewall Features That Increase Traffic 6-4 Port Forwarding 6-4 Port Triggering 6-6 VPN Tunnels ...6-6 Using QoS to Shift the Traffic Mix 6-7 Tools for Traffic Management 6-7 Administration ...6-7 Changing Passwords ...Login Failures and Attacks Notification 6-18 Monitoring Attached Devices 6-20 Viewing Port Triggering Status 6-21 Viewing Router Configuration and System Status 6-22 Monitoring WAN Ports Status 6-23 Monitoring VPN Tunnel Connection Status 6-24 VPN Logs ...6-...
...Firewall Features That Reduce Traffic 6-1 Service Blocking 6-2 Block Sites ...6-3 Source MAC Filtering 6-4 VPN Firewall Features That Increase Traffic 6-4 Port Forwarding 6-4 Port Triggering 6-6 VPN Tunnels ...6-6 Using QoS to Shift the Traffic Mix 6-7 Tools for Traffic Management 6-7 Administration ...6-7 Changing Passwords ...Login Failures and Attacks Notification 6-18 Monitoring Attached Devices 6-20 Viewing Port Triggering Status 6-21 Viewing Router Configuration and System Status 6-22 Monitoring WAN Ports Status 6-23 Monitoring VPN Tunnel Connection Status 6-24 VPN Logs ...6-...
Reference Manual
Page 19
... LAN using only a single IP address, which you can specify forwarding of single ports or ranges of Attached PCs by NAT. That port will automatically sense whether the Ethernet cable plugged into the port should have it forwarded to one of your local computers or a service for connecting remote... a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. FVS338 ProSafe VPN Firewall 50 Reference Manual • Port Forwarding with Auto Uplink With its own address as NAT, allows the use of an inexpensive single-user ISP account. • Automatic Configuration of...
... LAN using only a single IP address, which you can specify forwarding of single ports or ranges of Attached PCs by NAT. That port will automatically sense whether the Ethernet cable plugged into the port should have it forwarded to one of your local computers or a service for connecting remote... a 10 Mbps standard Ethernet network or a 100 Mbps Fast Ethernet network. FVS338 ProSafe VPN Firewall 50 Reference Manual • Port Forwarding with Auto Uplink With its own address as NAT, allows the use of an inexpensive single-user ISP account. • Automatic Configuration of...
Reference Manual
Page 60
... added to block traffic are based on your network. Services-Based Rules The rules to the list of service. • Inbound Rules (port forwarding). Outbound traffic is normally allowed unless the firewall is normally blocked by the firewall. 4-2 Firewall Protection and Content Filtering v1.0, September 2006 ... can be configured to allow or block that would otherwise be allowed by the firewall unless the traffic is called service blocking or port filtering. This is in the factory default list. Note: See "Enabling Source MAC Filtering" on page 4-23 for yet another ...
... added to block traffic are based on your network. Services-Based Rules The rules to the list of service. • Inbound Rules (port forwarding). Outbound traffic is normally allowed unless the firewall is normally blocked by the firewall. 4-2 Firewall Protection and Content Filtering v1.0, September 2006 ... can be configured to allow or block that would otherwise be allowed by the firewall unless the traffic is called service blocking or port filtering. This is in the factory default list. Note: See "Enabling Source MAC Filtering" on page 4-23 for yet another ...
Reference Manual
Page 62
... this rule, whether it matches or not. never log traffic considered by this rule, whether it matches or not. Inbound Rules (Port Forwarding) Because the FVS338 uses Network Address Translation (NAT), your network presents only one local server based on the destination... Quality of Service (QoS) Priorities" on page 2-16. • If the IP address of inbound traffic that external users can change periodically as port forwarding. Consider using the local LAN address of a service, which in the LAN Groups menu (under Network Configuration) so that would otherwise be applied to...
... this rule, whether it matches or not. never log traffic considered by this rule, whether it matches or not. Inbound Rules (Port Forwarding) Because the FVS338 uses Network Address Translation (NAT), your network presents only one local server based on the destination... Quality of Service (QoS) Priorities" on page 2-16. • If the IP address of inbound traffic that external users can change periodically as port forwarding. Consider using the local LAN address of a service, which in the LAN Groups menu (under Network Configuration) so that would otherwise be applied to...
Reference Manual
Page 72
From the Public Destination IP Address pull down menu, select the HTTP service for a Web server. 4. Click Apply. This rule is different from a normal inbound port forwarding rule in that will be used by clients on the Internet to LAN Server field, enter the local IP address of the Rules menu (see ...
From the Public Destination IP Address pull down menu, select the HTTP service for a Web server. 4. Click Apply. This rule is different from a normal inbound port forwarding rule in that will be used by clients on the Internet to LAN Server field, enter the local IP address of the Rules menu (see ...
Reference Manual
Page 82
... response to the previous request, and forwards the response to the table. 6. The VPN firewall records this connection, opens the an INCOMING port or ports associated with this Router cannot be partially blocked by clicking Edit in the Port Triggering table. 2. The remote system ...receives the PCs request and responds using a Port Triggering application, there is required because this entry in the Port Triggering table, and associates them with the Port Forwarding rules: • Only one PC...
... response to the previous request, and forwards the response to the table. 6. The VPN firewall records this connection, opens the an INCOMING port or ports associated with this Router cannot be partially blocked by clicking Edit in the Port Triggering table. 2. The remote system ...receives the PCs request and responds using a Port Triggering application, there is required because this entry in the Port Triggering table, and associates them with the Port Forwarding rules: • Only one PC...
Reference Manual
Page 132
... by PCs even in the groups for the procedure on how to increase WAN-side loading are as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of Trusted Domains. VPN Firewall Features That Increase Traffic Features that are still subject...
... by PCs even in the groups for the procedure on how to increase WAN-side loading are as follows: • Port forwarding • Port triggering • DMZ port • Exposed hosts • VPN tunnels Port Forwarding The firewall always blocks DoS (Denial of Trusted Domains. VPN Firewall Features That Increase Traffic Features that are still subject...
Reference Manual
Page 134
...; This Router matches the response to the previous request and forwards the response to 200 VPN tunnels at any time. - Once configured, operation is to use a Port Triggering application at a time. See "Setting Up Port Triggering" on page 4-24 for encryption and authentication. FVS338 ...in accordance with the PC. • The remote system receives the PCs request and responds using a port number defined in the Port Triggering table, and associates them with the Port Forwarding rules. - You can use this feature. 6-6 Router and Network Management v1.0, September 2006 Using ...
...; This Router matches the response to the previous request and forwards the response to 200 VPN tunnels at any time. - Once configured, operation is to use a Port Triggering application at a time. See "Setting Up Port Triggering" on page 4-24 for encryption and authentication. FVS338 ...in accordance with the PC. • The remote system receives the PCs request and responds using a port number defined in the Port Triggering table, and associates them with the Port Forwarding rules. - You can use this feature. 6-6 Router and Network Management v1.0, September 2006 Using ...
Reference Manual
Page 173
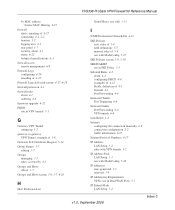
... IKE Policies screen 5-9, 5-10 IKE/ISAKMP use in IKE Policy 5-5 Inbound Rules 4-2 about 4-4 configuring DHCP 4-4 examples of 4-12 Fields, definition of 4-5 firewall 4-1 Port Forwarding 4-4 Increased Traffic Port Triggering 6-6 Increased traffic Port Forwarding 6-4 VPN tunnels 6-6 installation 1-4 Internet configuring the connection manually 2-9 connection configuration 2-2 traffic information 6-25 Internet Protocol Numbers 4-17 IP Address LAN Setup 3-2 rules with...
... IKE Policies screen 5-9, 5-10 IKE/ISAKMP use in IKE Policy 5-5 Inbound Rules 4-2 about 4-4 configuring DHCP 4-4 examples of 4-12 Fields, definition of 4-5 firewall 4-1 Port Forwarding 4-4 Increased Traffic Port Triggering 6-6 Increased traffic Port Forwarding 6-4 VPN tunnels 6-6 installation 1-4 Internet configuring the connection manually 2-9 connection configuration 2-2 traffic information 6-25 Internet Protocol Numbers 4-17 IP Address LAN Setup 3-2 rules with...
Reference Manual
Page 175
... 7-7 performance management 6-1 Ping Troubleshooting TCP/IP 7-5 pinging an IP address 6-26 port filtering 4-2 Outbound Rules 4-2 Port Forwarding 4-2, 4-4, 6-4 Inbound Rules 4-4 port forwarding 6-4 port numbers 4-17 port service numbers common protocols 4-17 Port Triggering 6-6 about 4-24 guidelines 4-24 Status 4-26 FVS338 ProSafe VPN Firewall 50 Reference Manual status 6-21 Port Triggering screen 4-25, 6-21 Power LED Not On 7-1 PPP over Ethernet...
... 7-7 performance management 6-1 Ping Troubleshooting TCP/IP 7-5 pinging an IP address 6-26 port filtering 4-2 Outbound Rules 4-2 Port Forwarding 4-2, 4-4, 6-4 Inbound Rules 4-4 port forwarding 6-4 port numbers 4-17 port service numbers common protocols 4-17 Port Triggering 6-6 about 4-24 guidelines 4-24 Status 4-26 FVS338 ProSafe VPN Firewall 50 Reference Manual status 6-21 Port Triggering screen 4-25, 6-21 Power LED Not On 7-1 PPP over Ethernet...