MR814v2 Reference Manual
Page 11
... your purchase of the NETGEAR® MR814v2 Cable/DSL Wireless Router. The MR814v2 router provides connection for multiple personal computers (PCs) to the Internet through an external broadband access device (such as a cable modem or DSL modem) that the reader has basic to intermediate computer and Internet skills. About This Manual xi Audience This reference manual assumes that is provided...
... your purchase of the NETGEAR® MR814v2 Cable/DSL Wireless Router. The MR814v2 router provides connection for multiple personal computers (PCs) to the Internet through an external broadband access device (such as a cable modem or DSL modem) that the reader has basic to intermediate computer and Internet skills. About This Manual xi Audience This reference manual assumes that is provided...
MR814v2 Reference Manual
Page 15
... are discarded, preventing users outside the LAN are autosensing and capable of ports. The router incorporates Auto UplinkTM technology. Extensive Protocol Support The MR814v2 router supports the Transmission Control...Cable/DSL Wireless Router Security The MR814v2 router is equipped with several networked PCs to share an Internet account using only a single IP address, which may be statically or dynamically assigned by NAT The MR814v2 router allows several features designed to maintain security, as NAT, allows the use of cable to one designated "DMZ" host computer. Reference Manual...
... are discarded, preventing users outside the LAN are autosensing and capable of ports. The router incorporates Auto UplinkTM technology. Extensive Protocol Support The MR814v2 router supports the Transmission Control...Cable/DSL Wireless Router Security The MR814v2 router is equipped with several networked PCs to share an Internet account using only a single IP address, which may be statically or dynamically assigned by NAT The MR814v2 router allows several features designed to maintain security, as NAT, allows the use of cable to one designated "DMZ" host computer. Reference Manual...
MR814v2 Reference Manual
Page 16
... on the LAN using the Dynamic Host Configuration Protocol (DHCP). Reference Manual for the MR814v2 Cable/DSL Wireless Router • Automatic Configuration of Attached PCs by simulating a dial-up connection. Maintenance and Support NETGEAR offers the following features simplify installation and management tasks: • Browser...configuration of PCs on your use of ISP account. • Visual monitoring The MR814v2 router's front panel LEDs provide an easy way to the attached PCs. A user-friendly Setup Wizard is provided and online help you only for the information required for ...
... on the LAN using the Dynamic Host Configuration Protocol (DHCP). Reference Manual for the MR814v2 Cable/DSL Wireless Router • Automatic Configuration of Attached PCs by simulating a dial-up connection. Maintenance and Support NETGEAR offers the following features simplify installation and management tasks: • Browser...configuration of PCs on your use of ISP account. • Visual monitoring The MR814v2 router's front panel LEDs provide an easy way to the attached PCs. A user-friendly Setup Wizard is provided and online help you only for the information required for ...
MR814v2 Reference Manual
Page 23
...Server IP Address Host and Domain Names: Some ISPs use the following : Wireless Network Name (SSID Encryption (circle one): WEP 64, WEP 128, or IPSec WEP passphrase or key Connecting the Router to the Internet 2-3 Fixed or Static Internet IP Address Gateway IP Address ... as the domain name. For example, 169.254.141.148 could be entered exactly as your ISP. Reference Manual for the MR814v2 Cable/DSL Wireless Router Record Your Internet Connection Information Print this your account, user, host, computer, or system name. • If your Internet Service Provider (ISP).
...Server IP Address Host and Domain Names: Some ISPs use the following : Wireless Network Name (SSID Encryption (circle one): WEP 64, WEP 128, or IPSec WEP passphrase or key Connecting the Router to the Internet 2-3 Fixed or Static Internet IP Address Gateway IP Address ... as the domain name. For example, 169.254.141.148 could be entered exactly as your ISP. Reference Manual for the MR814v2 Cable/DSL Wireless Router Record Your Internet Connection Information Print this your account, user, host, computer, or system name. • If your Internet Service Provider (ISP).
MR814v2 Reference Manual
Page 26
... automatically via DHCP. For security reasons, the router has its own user name and password. When prompted, enter admin for the router user name and password for the MR814v2 Cable/DSL Wireless Router f. If you may use to log in to your Internet connection. 2-6 Connecting the Router to the router. a. Reference Manual for the router password, both in the address filed of...
... automatically via DHCP. For security reasons, the router has its own user name and password. When prompted, enter admin for the router user name and password for the MR814v2 Cable/DSL Wireless Router f. If you may use to log in to your Internet connection. 2-6 Connecting the Router to the router. a. Reference Manual for the router password, both in the address filed of...
MR814v2 Reference Manual
Page 44
... of your changes. 3-8 Wireless Configuration Reference Manual for the wireless network name (SSID). Note: The SSID of any other wireless networks within several hundred feet of password, or using whatever LAN address and password you notice interference problems with another nearby wireless router or access point. Choose a suitable descriptive name for the MR814v2 Cable/DSL Wireless Router How to Set...
... of your changes. 3-8 Wireless Configuration Reference Manual for the wireless network name (SSID). Note: The SSID of any other wireless networks within several hundred feet of password, or using whatever LAN address and password you notice interference problems with another nearby wireless router or access point. Choose a suitable descriptive name for the MR814v2 Cable/DSL Wireless Router How to Set...
MR814v2 Reference Manual
Page 45
Reference Manual for wireless connectivity. Configure and test your PC to Restrict Wireless Access by DHCP from a wireless PC and you change the wireless settings of your PCs for the MR814v2 Cable/DSL Wireless Router Note: If you are able to have set up.... 2. How to match the firewall's new settings. 8. Log in to the MR814v2 firewall at its default LAN address of http://192.168.0.1 with its default user...
Reference Manual for wireless connectivity. Configure and test your PC to Restrict Wireless Access by DHCP from a wireless PC and you change the wireless settings of your PCs for the MR814v2 Cable/DSL Wireless Router Note: If you are able to have set up.... 2. How to match the firewall's new settings. 8. Log in to the MR814v2 firewall at its default LAN address of http://192.168.0.1 with its default user...
MR814v2 Reference Manual
Page 47
... page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Be sure you have set in the MR814v2. 5. In the Security Encryption menu, select the authentication and encryption strength Please refer to save your wireless adapter. Enter ten hexadecimal digits (any further changes. Click Apply to "Overview of these options, as defined by the IEEE 802.11b wireless communication standard.
... page D-5 for the MR814v2 Cable/DSL Wireless Router 1. Be sure you have set in the MR814v2. 5. In the Security Encryption menu, select the authentication and encryption strength Please refer to save your wireless adapter. Enter ten hexadecimal digits (any further changes. Click Apply to "Overview of these options, as defined by the IEEE 802.11b wireless communication standard.
MR814v2 Reference Manual
Page 51
... If you to block the use of certain Internet services by server computers at the request of client computers. Since the Trusted User will be identified by an IP address, you wish to block all Internet browsing access during a scheduled period, enter the keyword "."... 4-3 Reference Manual for service to a server computer on the Internet, the requested service is identified by a service or port number. This is shown below: Figure 4-2: Block Services menu Services are functions performed by PCs on your network sends a request for the MR814v2 Cable/DSL Wireless Router • ...
... If you to block the use of certain Internet services by server computers at the request of client computers. Since the Trusted User will be identified by an IP address, you wish to block all Internet browsing access during a scheduled period, enter the keyword "."... 4-3 Reference Manual for service to a server computer on the Internet, the requested service is identified by a service or port number. This is shown below: Figure 4-2: Block Services menu Services are functions performed by PCs on your network sends a request for the MR814v2 Cable/DSL Wireless Router • ...
MR814v2 Reference Manual
Page 52
... service numbers for blocking, click Add. If the application uses a single port number, enter that do not already appear, select User Defined. The list already displays several common services, but you know that the application uses either TCP or UDP, select the appropriate... the Service Type list, select the application or service to be determined by contacting the publisher of the application. Reference Manual for the MR814v2 Cable/DSL Wireless Router To specify a service for many common protocols are defined by the Internet Engineering Task Force (IETF) and published in both...
... service numbers for blocking, click Add. If the application uses a single port number, enter that do not already appear, select User Defined. The list already displays several common services, but you know that the application uses either TCP or UDP, select the appropriate... the Service Type list, select the application or service to be determined by contacting the publisher of the application. Reference Manual for the MR814v2 Cable/DSL Wireless Router To specify a service for many common protocols are defined by the Internet Engineering Task Force (IETF) and published in both...
MR814v2 Reference Manual
Page 54
... be made for the Trusted User. This field displays whether the access was recorded. The date and time the log entry was blocked or allowed. An example is a detailed record of what websites you have accessed or attempted to access. 4-6 Content Filtering Reference Manual for the MR814v2 Cable/DSL Wireless Router Viewing Logs of Web Access...
... be made for the Trusted User. This field displays whether the access was recorded. The date and time the log entry was blocked or allowed. An example is a detailed record of what websites you have accessed or attempted to access. 4-6 Content Filtering Reference Manual for the MR814v2 Cable/DSL Wireless Router Viewing Logs of Web Access...
MR814v2 Reference Manual
Page 62
... to display the menu shown below. This file can be saved (backed up) to a user's PC, retrieved (restored) from NETGEAR. 2. Reference Manual for the MR814v2 Cable/DSL Wireless Router From the Main Menu of the browser interface, under the Maintenance heading, select the Router Upgrade heading to interrupt the Web browser by closing the window, clicking a link, or...
... to display the menu shown below. This file can be saved (backed up) to a user's PC, retrieved (restored) from NETGEAR. 2. Reference Manual for the MR814v2 Cable/DSL Wireless Router From the Main Menu of the browser interface, under the Maintenance heading, select the Router Upgrade heading to interrupt the Web browser by closing the window, clicking a link, or...
MR814v2 Reference Manual
Page 67
...23 in the table. 2. Type the IP address of an unused port in this address is 172.16.1.23, for example, an Internet user can manually configure the PC to use the supplied number in the default listing and add +1 for each additional computer. Some considerations for this example). Click... fixed address. • Local PCs must know the IP address that you 've already configured one computer to http://172.16.1.23. Reference Manual for the MR814v2 Cable/DSL Wireless Router Local Web and FTP Server Example If a local PC with a private IP address of 192.168.0.33 acts as a Web and FTP server...
...23 in the table. 2. Type the IP address of an unused port in this address is 172.16.1.23, for example, an Internet user can manually configure the PC to use the supplied number in the default listing and add +1 for each additional computer. Some considerations for this example). Click... fixed address. • Local PCs must know the IP address that you 've already configured one computer to http://172.16.1.23. Reference Manual for the MR814v2 Cable/DSL Wireless Router Local Web and FTP Server Example If a local PC with a private IP address of 192.168.0.33 acts as a Web and FTP server...
MR814v2 Reference Manual
Page 73
Reference Manual for the MR814v2 Cable/DSL Wireless Router Note: The reserved address will not be routed on Dynamic ...service providers whose names appear in to your account, and register your frequently-changing IP address. Type the User Name for your dynamic DNS account. 6. Click Edit or Delete. In this case, you can register ...account uses a dynamically assigned IP address, you to register your IP address by public Domain Name Servers (DNS). The router contains a client that can change frequently. Then, whenever your ISP-assigned IP address changes, your dynamic DNS Service ...
Reference Manual for the MR814v2 Cable/DSL Wireless Router Note: The reserved address will not be routed on Dynamic ...service providers whose names appear in to your account, and register your frequently-changing IP address. Type the User Name for your dynamic DNS account. 6. Click Edit or Delete. In this case, you can register ...account uses a dynamically assigned IP address, you to register your IP address by public Domain Name Servers (DNS). The router contains a client that can change frequently. Then, whenever your ISP-assigned IP address changes, your dynamic DNS Service ...
MR814v2 Reference Manual
Page 76
...few external IP addresses as practical. To allow a user or users on the Internet, select Everyone. 6-12 Advanced Configuration of 1 will work since the ISDN router is on the 134.177.0.0 network, your router will be up to your local network for all ...'s firewall. To configure your request to access the router's remote management. a. Note: For enhanced security, restrict access to a very secure password. Reference Manual for the MR814v2 Cable/DSL Wireless Router When you first configured your MR814v2 router. Enabling Remote Management Access Using the Remote Management page...
...few external IP addresses as practical. To allow a user or users on the Internet, select Everyone. 6-12 Advanced Configuration of 1 will work since the ISDN router is on the 134.177.0.0 network, your router will be up to your local network for all ...'s firewall. To configure your request to access the router's remote management. a. Note: For enhanced security, restrict access to a very secure password. Reference Manual for the MR814v2 Cable/DSL Wireless Router When you first configured your MR814v2 router. Enabling Remote Management Access Using the Remote Management page...
MR814v2 Reference Manual
Page 92
...and exchanging information with other improvements, RIP-2 supports subnet and multicast protocols. Among other routers in the data and on routing tables maintained by the router. Individual users and small organizations may obtain their addresses either from the IANA or from an Internet service... (IANA). IP Addresses and the Internet Because TCP/IP networks are assigned to the routing table. Reference Manual for the MR814v2 Cable/DSL Wireless Router What is the Routing Information Protocol (RIP). The Internet Protocol (IP) uses a 32-bit address structure. In ...
...and exchanging information with other improvements, RIP-2 supports subnet and multicast protocols. Among other routers in the data and on routing tables maintained by the router. Individual users and small organizations may obtain their addresses either from the IANA or from an Internet service... (IANA). IP Addresses and the Internet Because TCP/IP networks are assigned to the routing table. Reference Manual for the MR814v2 Cable/DSL Wireless Router What is the Routing Information Protocol (RIP). The Internet Protocol (IP) uses a 32-bit address structure. In ...
MR814v2 Reference Manual
Page 98
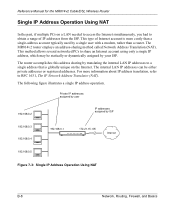
Reference Manual for the MR814v2 Cable/DSL Wireless Router Single IP Address Operation Using NAT In the past, if multiple PCs on a LAN needed to access the Internet simultaneously, you had to obtain a range ... using only a single IP address, which may be either private addresses or registered addresses. Private IP addresses assigned by user 192.168.0.2 IP addresses assigned by a single user with a modem, rather than a router. The internal LAN IP addresses can be statically or dynamically assigned by your ISP. This method allows several networked PCs...
Reference Manual for the MR814v2 Cable/DSL Wireless Router Single IP Address Operation Using NAT In the past, if multiple PCs on a LAN needed to access the Internet simultaneously, you had to obtain a range ... using only a single IP address, which may be either private addresses or registered addresses. Private IP addresses assigned by user 192.168.0.2 IP addresses assigned by a single user with a modem, rather than a router. The internal LAN IP addresses can be statically or dynamically assigned by your ISP. This method allows several networked PCs...
MR814v2 Reference Manual
Page 99
... to deliver data from one PC (for example, a Web server) on the network receive and read the request. Reference Manual for the MR814v2 Cable/DSL Wireless Router This scheme offers the additional benefit of firewall-like protection because the internal LAN addresses are filtered out by the manufacturer. This... data and MAC address data for Management of the destination device to its own MAC address directly to outside users. For more information about IP address translation, refer to the Internet through the translated connection. Network, Routing, Firewall, and Basics B-9
... to deliver data from one PC (for example, a Web server) on the network receive and read the request. Reference Manual for the MR814v2 Cable/DSL Wireless Router This scheme offers the additional benefit of firewall-like protection because the internal LAN addresses are filtered out by the manufacturer. This... data and MAC address data for Management of the destination device to its own MAC address directly to outside users. For more information about IP address translation, refer to the Internet through the translated connection. Network, Routing, Firewall, and Basics B-9
MR814v2 Reference Manual
Page 100
... PC accesses a resource by which each PC must be translated to an IP address in order for a user to look up addresses. If the PCs need to act as www.NETGEAR.com. The firewall can automatically obtain an IP address, subnet mask, DNS server addresses, and a gateway address... the servers to actually contact the resource. The MR814v2 router has the capacity to access the Internet, they should also be configured with a gateway address and one or more DNS server addresses. Reference Manual for the MR814v2 Cable/DSL Wireless Router Domain Name Server Many of the resources on the Internet...
... PC accesses a resource by which each PC must be translated to an IP address in order for a user to look up addresses. If the PCs need to act as www.NETGEAR.com. The firewall can automatically obtain an IP address, subnet mask, DNS server addresses, and a gateway address... the servers to actually contact the resource. The MR814v2 router has the capacity to access the Internet, they should also be configured with a gateway address and one or more DNS server addresses. Reference Manual for the MR814v2 Cable/DSL Wireless Router Domain Name Server Many of the resources on the Internet...
MR814v2 Reference Manual
Page 101
...through or rejected. When an incident is a device that protects one network from another, while allowing communication between the two. Since user-level applications such as merely flooding your site with more sophisticated attack may be able to determine whether or not it can handle. ... will be allowed to protect your network from operating or communicating by launching a Denial of Service (DoS) attack. Reference Manual for the MR814v2 Cable/DSL Wireless Router What is analyzed against the state of these connections in the operating system used for such an attack can be as simple...
...through or rejected. When an incident is a device that protects one network from another, while allowing communication between the two. Since user-level applications such as merely flooding your site with more sophisticated attack may be able to determine whether or not it can handle. ... will be allowed to protect your network from operating or communicating by launching a Denial of Service (DoS) attack. Reference Manual for the MR814v2 Cable/DSL Wireless Router What is analyzed against the state of these connections in the operating system used for such an attack can be as simple...