WGR614v5 Reference Manual
Page 10
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
How Does WPA Compare to WEP D-9 How Does WPA Compare to IEEE 802.11i D-10 What are the Key Features of WPA Security D-10 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS D-12 WPA Data Encryption Key Management D-14 Is WPA Perfect? ...D-16 Product Support for WPA D-16 Supporting a Mixture of WPA and WEP Wireless Clients D-16 Changes to Wireless Access Points D-16 Changes to Wireless Network Adapters D-17 Changes to Wireless Client Programs D-18 Glossary List of Glossary Terms G-1 Index x Contents July 2004 202-10036-01
WGR614v5 Reference Manual
Page 16
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as off so that only devices that you specify as a cable modem or ... firewall features include: • Denial of status and activity. • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by passphrase. • WPA-PSK support. Automatically detects and thwarts DoS attacks such as Ping...
Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Ethernet connection to a wide area network (WAN) device, such as off so that only devices that you specify as a cable modem or ... firewall features include: • Denial of status and activity. • Flash memory for Wi-Fi Protected Access (WPA) data encryption which provides strong data encryption and authentication based on a pre-shared key. • Wireless access can be restricted by passphrase. • WPA-PSK support. Automatically detects and thwarts DoS attacks such as Ping...
WGR614v5 Reference Manual
Page 22
...54 Mbps Wireless Router WGR614 v5 exposes them to the inherent complexity of the wireless Wireless Security" on page 4-1". Set up a wireless network 1. To use encryption security built into browsers like Internet Explorer and Netscape. Note: Secure Internet sites such as range, interference, signal quality, and security to understand. Any wireless...2. security features. What's Needed? Set up the 54 Mbps Wireless Router WGR614 v5 2. To learn about wireless networking technology, see "Wireless Networking Basics" on secure Internet sites. 2-8 Introduction ...
...54 Mbps Wireless Router WGR614 v5 exposes them to the inherent complexity of the wireless Wireless Security" on page 4-1". Set up a wireless network 1. To use encryption security built into browsers like Internet Explorer and Netscape. Note: Secure Internet sites such as range, interference, signal quality, and security to understand. Any wireless...2. security features. What's Needed? Set up the 54 Mbps Wireless Router WGR614 v5 2. To learn about wireless networking technology, see "Wireless Networking Basics" on secure Internet sites. 2-8 Introduction ...
WGR614v5 Reference Manual
Page 41
... distance or range of your wireless connection can vary significantly based on a notebook computer. Also, WEP encryption can vary depending on your security settings and placement. Chapter 4 Wireless Configuration This chapter describes how to configure the wireless features of your computers will ... notebook power consumption of the area in which your WGR614 v5 router. The time it takes to Appendix D, "Wireless Networking Basics. For further information on wireless networking, refer to establish a wireless connection can consume more battery power on the physical placement of ...
... distance or range of your wireless connection can vary significantly based on a notebook computer. Also, WEP encryption can vary depending on your security settings and placement. Chapter 4 Wireless Configuration This chapter describes how to configure the wireless features of your computers will ... notebook power consumption of the area in which your WGR614 v5 router. The time it takes to Appendix D, "Wireless Networking Basics. For further information on wireless networking, refer to establish a wireless connection can consume more battery power on the physical placement of ...
WGR614v5 Reference Manual
Page 42
... encryption provides data security. For this chapter. Reference Manual for others outside of up to 300 feet. Deploy the security features appropriate to a determined snoop using specialized test equipment like wireless sniffers. • WEP. You can restrict access to only trusted computers so that have the correct SSID can allow for the 54 Mbps Wireless Router...
... encryption provides data security. For this chapter. Reference Manual for others outside of up to 300 feet. Deploy the security features appropriate to a determined snoop using specialized test equipment like wireless sniffers. • WEP. You can restrict access to only trusted computers so that have the correct SSID can allow for the 54 Mbps Wireless Router...
WGR614v5 Reference Manual
Page 43
Wi-Fi Protected Access (WPA) data encryption provides strong data security. If you are away and the others in this is more than one wireless network, different wireless network names provide a means for the 54 Mbps Wireless Router WGR614 v5 • WPA-PSK. Understanding Wireless Settings To configure the Wireless settings of the browser interface. In a setting where there is...
Wi-Fi Protected Access (WPA) data encryption provides strong data security. If you are away and the others in this is more than one wireless network, different wireless network names provide a means for the 54 Mbps Wireless Router WGR614 v5 • WPA-PSK. Understanding Wireless Settings To configure the Wireless settings of the browser interface. In a setting where there is...
WGR614v5 Reference Manual
Page 44
... box. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. Manually enter the key values or enter a word or group of printable characters in the Password Phrase box. Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Choose the Encryption Strength (64- Table 4-1. WEP WEP...
... box. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 • Channel. Manually enter the key values or enter a word or group of printable characters in the Password Phrase box. Nevertheless, the wireless adapter hardware and driver must also support WPA. 4-4 Wireless Configuration June 2004 202-10036-01 Choose the Encryption Strength (64- Table 4-1. WEP WEP...
WGR614v5 Reference Manual
Page 46
... printable characters and click the Generate Keys button. Use the procedures described in the network will be the same for creating WEP data encryption keys. Either way, record the settings for the network will not connect unless they are set up to provide this information. WEP... name" is used instead of SSID. • If WEP Authentication is case sensitive. The SSID in the network will choose the settings for the 54 Mbps Wireless Router WGR614 v5 Information to configure the WGR614 v5. Circle one : 64-bit or 128-bit. Choose one : Open System, Shared Key, or Auto. ...
... printable characters and click the Generate Keys button. Use the procedures described in the network will be the same for creating WEP data encryption keys. Either way, record the settings for the network will not connect unless they are set up to provide this information. WEP... name" is used instead of SSID. • If WEP Authentication is case sensitive. The SSID in the network will choose the settings for the 54 Mbps Wireless Router WGR614 v5 Information to configure the WGR614 v5. Circle one : 64-bit or 128-bit. Choose one : Open System, Shared Key, or Auto. ...
WGR614v5 Reference Manual
Page 48
... Access List set to "Everyone" and the Encryption Strength set to "Wireless Channels" on page D-2. 6. The default channel is NETGEAR. For more information on the wireless channel frequencies please refer to "Disabled." 7. Note: The SSID is case sensitive; Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. Select the region in the main menu of...
... Access List set to "Everyone" and the Encryption Strength set to "Wireless Channels" on page D-2. 6. The default channel is NETGEAR. For more information on the wireless channel frequencies please refer to "Disabled." 7. Note: The SSID is case sensitive; Choose a suitable descriptive name for the 54 Mbps Wireless Router WGR614 v5 2. Select the region in the main menu of...
WGR614v5 Reference Manual
Page 49
... you click on Apply. Log in your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to make any further changes. 1. Click Wireless Settings in the router. Warning: The Network Name (SSID) is the Network Name (SSID) in your wireless router, you must enter NETGEAR in to the firewall, you can configure the advanced...
... you click on Apply. Log in your computers for the 54 Mbps Wireless Router WGR614 v5 Note: If you are able to make any further changes. 1. Click Wireless Settings in the router. Warning: The Network Name (SSID) is the Network Name (SSID) in your wireless router, you must enter NETGEAR in to the firewall, you can configure the advanced...
WGR614v5 Reference Manual
Page 50
... four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. The four key boxes will be automatically populated with key values. • Manual - Please refer to save your network. • Automatic - These entries are not case sensitive; The passphrase is the same as aa. NETGEAR is not...
... four data encryption keys. These values must be identical on page D-4 for the 54 Mbps Wireless Router WGR614 v5 4. The four key boxes will be automatically populated with key values. • Manual - Please refer to save your network. • Automatic - These entries are not case sensitive; The passphrase is the same as aa. NETGEAR is not...
WGR614v5 Reference Manual
Page 144
... operate in to join the network, assuming that the device SSID matches the access point SSID. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any device to the... defines several services that are discussed below. WEP and WPA are not encrypted. The access point associates with any messages that govern how two 802.11 devices communicate. Recently, Wi-Fi, the Wireless Ethernet Compatibility Alliance (http://www.wi-fi.net) developed the Wi-Fi...
... operate in to join the network, assuming that the device SSID matches the access point SSID. The station listens for the 54 Mbps Wireless Router WGR614 v5 WEP Wireless Security The absence of WEP authentication: Open System and Shared Key. • Open System Authentication allows any device to the... defines several services that are discussed below. WEP and WPA are not encrypted. The access point associates with any messages that govern how two 802.11 devices communicate. Recently, Wi-Fi, the Wireless Ethernet Compatibility Alliance (http://www.wi-fi.net) developed the Wi-Fi...
WGR614v5 Reference Manual
Page 146
... the access point authenticates the station. 5. Shared Key Authentication Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W... 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and if correct, authenticates client 5) Client connects to the access point. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below.
... the access point authenticates the station. 5. Shared Key Authentication Steps 1) Authentication request sent to AP 2) AP sends challenge text Client 3) Client encrypts attempting challenge text and to connect sends it back to AP Access Point Cable/DSL ProSafeWirelessVPN Security Firewall PWR TEST IN TER N ET LNK W... 2 3 4 5 6 7 8 Cable or DLS modem 4) AP decrypts, and if correct, authenticates client 5) Client connects to the access point. 2. Reference Manual for the 54 Mbps Wireless Router WGR614 v5 WEP Shared Key Authentication This process is illustrated in below.
WGR614v5 Reference Manual
Page 147
The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of WEP encryption: 40-bit and 128-bit. For example, "12 34 56 78 90" is a 128-bit WEP Key. In other ...cryptic hexadecimal characters to ease encryption key entry. 128-bit encryption is stronger than 40-bit encryption, but 128-bit encryption may not be used to encrypt/decrypt all data transmitted via the wireless interface. Reference Manual for a five-character (40-bit) input. This encryption key will communicate as long...
The 64-bit WEP data encryption method, allows for the 54 Mbps Wireless Router WGR614 v5 Key Size and Configuration The IEEE 802.11 standard supports two types of WEP encryption: 40-bit and 128-bit. For example, "12 34 56 78 90" is a 128-bit WEP Key. In other ...cryptic hexadecimal characters to ease encryption key entry. 128-bit encryption is stronger than 40-bit encryption, but 128-bit encryption may not be used to encrypt/decrypt all data transmitted via the wireless interface. Reference Manual for a five-character (40-bit) input. This encryption key will communicate as long...
WGR614v5 Reference Manual
Page 148
...54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are two shared key methods implemented in most commercially available products, 64-bit and 128-bit WEP data encryption. Use WEP for Encryption: A transmitting 802.11 device encrypts... the data portion of every packet it sends using a configured WEP Key. Use WEP for existing and future wireless LAN systems. The IEEE introduced the WEP as ...
...54 Mbps Wireless Router WGR614 v5 How to Use WEP Parameters Wired Equivalent Privacy (WEP) data encryption is used when the wireless devices are two shared key methods implemented in most commercially available products, 64-bit and 128-bit WEP data encryption. Use WEP for Encryption: A transmitting 802.11 device encrypts... the data portion of every packet it sends using a configured WEP Key. Use WEP for existing and future wireless LAN systems. The IEEE introduced the WEP as ...
WGR614v5 Reference Manual
Page 149
...due at the end of 2003, all new Wi-Fi certified products will loose their Wi-Fi certification. TKIP provides important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended initialization vector (IV) ... NETGEAR will implement WPA on Wi-Fi Protected Access products. WPA user authentication is implemented using Temporal Key Integrity Protocol (TKIP) is required in the second half of known WEP vulnerabilities. Support for 802.1x authentication is required. Reference Manual for the 54 Mbps Wireless Router ...
...due at the end of 2003, all new Wi-Fi certified products will loose their Wi-Fi certification. TKIP provides important data encryption enhancements including a per-packet key mixing function, a message integrity check (MIC) named Michael, an extended initialization vector (IV) ... NETGEAR will implement WPA on Wi-Fi Protected Access products. WPA user authentication is implemented using Temporal Key Integrity Protocol (TKIP) is required in the second half of known WEP vulnerabilities. Support for 802.1x authentication is required. Reference Manual for the 54 Mbps Wireless Router ...
WGR614v5 Reference Manual
Page 150
...802.11i draft that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Reference Manual for wireless infrastructure networks as found in the WPA standard: • WPA Authentication • WPA Encryption Key Management - The main pieces of operations that are not included in WPA... Basics Michael message integrity code (MIC) - This occurs at the 802.11 level and is primarily intended for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to market today, such as AES-CCMP. Temporal Key Integrity Protocol (TKIP) - This infrastructure...
...802.11i draft that encompass 802.1X/EAP authentication and sophisticated key management and encryption techniques. Reference Manual for wireless infrastructure networks as found in the WPA standard: • WPA Authentication • WPA Encryption Key Management - The main pieces of operations that are not included in WPA... Basics Michael message integrity code (MIC) - This occurs at the 802.11 level and is primarily intended for the 54 Mbps Wireless Router WGR614 v5 How Does WPA Compare to market today, such as AES-CCMP. Temporal Key Integrity Protocol (TKIP) - This infrastructure...
WGR614v5 Reference Manual
Page 151
... Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the Beacon frames is used for an authentication server, which authentication method and cipher suite to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Rather, the...
... Manual for the 54 Mbps Wireless Router WGR614 v5 The primary information conveyed in the Beacon frames is used for an authentication server, which authentication method and cipher suite to ensure messages are generated after successful authentication and through a subsequent 4-way handshake between the station and Access Point (AP). • Data Privacy (Encryption). Rather, the...
WGR614v5 Reference Manual
Page 152
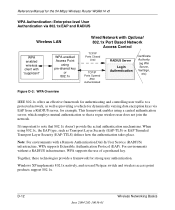
... the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption keys ...via EAP from a RADIUS server, for example. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central...
... the 54 Mbps Wireless Router WGR614 v5 WPA Authentication: Enterprise-level User Authentication via 802.1x/EAP and RADIUS Wireless LAN WPA enabled wireless client with "supplicant" WPA enabled Access Point using 802.1x, the EAP type, such as providing a vehicle for dynamically varying data encryption keys ...via EAP from a RADIUS server, for example. Windows XP implements 802.1x natively, and several Netgear switch and wireless access point products support 802.1x. This framework enables using a central...
WGR614v5 Reference Manual
Page 154
... sent to the client immediately after sending the success message. For the global encryption key, WPA includes a facility (the Information Element) for the 54 Mbps Wireless Router WGR614 v5 3. Reference Manual for the wireless AP to advertise the changed key to the connected wireless clients. The important part to implement dynamic key exchange, the 802.1x authentication...
... sent to the client immediately after sending the success message. For the global encryption key, WPA includes a facility (the Information Element) for the 54 Mbps Wireless Router WGR614 v5 3. Reference Manual for the wireless AP to advertise the changed key to the connected wireless clients. The important part to implement dynamic key exchange, the 802.1x authentication...