Security Target
Page 5
Page 4 of 91 7.3 Document Access Control Function 82 7.4 Use-of-Feature Restriction Function 84 7.5 Network Protection Function 85 7.6 Residual Data Overwrite Function 85 7.7 Stored Data Protection Function 86 7.8 Security Management Function 86 7.9 Software Verification Function 91 7.10 Fax Line Separation Function 91 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Page 4 of 91 7.3 Document Access Control Function 82 7.4 Use-of-Feature Restriction Function 84 7.5 Network Protection Function 85 7.6 Residual Data Overwrite Function 85 7.7 Stored Data Protection Function 86 7.8 Security Management Function 86 7.9 Software Verification Function 91 7.10 Fax Line Separation Function 91 Copyright (c) 2011 RICOH COMPANY, LTD. All rights reserved.
Security Target
Page 8
... of this ST. Software System/Copy 1.04 Network Support 10.65 Fax 01.01.00 RemoteFax 01.00.00 Copyright (c) 2011 RICOH COMPANY, LTD. The identification information of the TOE is identified by the MFP names and the versions of Scanner and Printer are not displayed. Title : Aficio MP 2352/2852/3352 series Security Target...
... of this ST. Software System/Copy 1.04 Network Support 10.65 Fax 01.01.00 RemoteFax 01.00.00 Copyright (c) 2011 RICOH COMPANY, LTD. The identification information of the TOE is identified by the MFP names and the versions of Scanner and Printer are not displayed. Title : Aficio MP 2352/2852/3352 series Security Target...
Security Target
Page 10
.... Print, fax, network transmission, and deletion of paper documents, - MFP A machinery that is defined as shown in the TOE environment. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP is connected to the local area network (hereafter "LAN") and telephone lines, as the TOE. Users can store it as a...The TOE is used in Figure 1. All rights reserved. Various settings for the MFP, which is the TOE itself, and hardware and software other than the TOE. Also, the TOE receives information via telephone lines and can operate the TOE from the Operation Panel of the MFP: -
.... Print, fax, network transmission, and deletion of paper documents, - MFP A machinery that is defined as shown in the TOE environment. Copyright (c) 2011 RICOH COMPANY, LTD. The MFP is connected to the local area network (hereafter "LAN") and telephone lines, as the TOE. Users can store it as a...The TOE is used in Figure 1. All rights reserved. Various settings for the MFP, which is the TOE itself, and hardware and software other than the TOE. Also, the TOE receives information via telephone lines and can operate the TOE from the Operation Panel of the MFP: -
Security Target
Page 12
...TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP, which consists of the following security features: - Software Verification Function - Audit Function - Identification and Authentication Function - Page 11 of 91 1.3.3 Major Security Features of TOE The TOE stores documents in Figure ...Protection Function - To ensure provision of -Feature Restriction Function - Document Access Control Function - All rights reserved. Residual Data Overwrite Function - Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function -
...TOE, and Protected Assets. 1.4.1 Physical Boundary of TOE The physical boundary of the TOE is the MFP, which consists of the following security features: - Software Verification Function - Audit Function - Identification and Authentication Function - Page 11 of 91 1.3.3 Major Security Features of TOE The TOE stores documents in Figure ...Protection Function - To ensure provision of -Feature Restriction Function - Document Access Control Function - All rights reserved. Residual Data Overwrite Function - Copyright (c) 2011 RICOH COMPANY, LTD. Security Management Function -
Security Target
Page 13
... Configuration of the TOE Controller Board The Controller Board is processed by the MFP Control Software on the Controller Board. All rights reserved. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. The information to temporarily read and write internal information. - NVRAM A non-volatile...
... Configuration of the TOE Controller Board The Controller Board is processed by the MFP Control Software on the Controller Board. All rights reserved. The following describes the components of random number generation, cryptographic key generation Copyright (c) 2011 RICOH COMPANY, LTD. The information to temporarily read and write internal information. - NVRAM A non-volatile...
Security Target
Page 14
...Engine Control Board. Fax Controller Unit (FCU) The Fax Controller Unit is the identifier for connection to and from the MFP Control Software. Copyright (c) 2011 RICOH COMPANY, LTD. The Operation Control Board is a non-volatile memory medium. It also sends and receives fax data to a ...telephone line. HDD The HDD is a hard disk drive that has a modem function for the Engine Control Software. Operation Panel Unit (hereafter "Operation ...
...Engine Control Board. Fax Controller Unit (FCU) The Fax Controller Unit is the identifier for connection to and from the MFP Control Software. Copyright (c) 2011 RICOH COMPANY, LTD. The Operation Control Board is a non-volatile memory medium. It also sends and receives fax data to a ...telephone line. HDD The HDD is a hard disk drive that has a modem function for the Engine Control Software. Operation Panel Unit (hereafter "Operation ...
Security Target
Page 16
... D120-7556 - MP 2352/MP 2852/MP 3352 MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 Manuals and Safety Information for Users MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7804 - Manuals for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Copyright (c) 2011 RICOH COMPANY, LTD. Quick Reference Scanner Guide D595-7316 - Manuals for Administrators MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7795...
... D120-7556 - MP 2352/MP 2852/MP 3352 MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 Manuals and Safety Information for Users MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7804 - Manuals for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Copyright (c) 2011 RICOH COMPANY, LTD. Quick Reference Scanner Guide D595-7316 - Manuals for Administrators MP 2352/MP 2852/MP 3352 Aficio MP 2352/MP 2852/MP 3352 D595-7795...
Security Target
Page 17
...MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Manuals and Safety Information for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 D120-7553 - SOFTWARE... MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Operating Instructions Troubleshooting D120-7535 - Operating Instructions Notes on Hard Disk Data Encryption D120-7550 Copyright (c) 2011 RICOH ...
...MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Manuals and Safety Information for Administrators: Using this Machine in a Network Environment Compliant with IEEE Std. 2600.1TM-2009 D120-7553 - SOFTWARE... MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Operating Instructions Troubleshooting D120-7535 - Operating Instructions Notes on Hard Disk Data Encryption D120-7550 Copyright (c) 2011 RICOH ...
Security Target
Page 18
...User The "user" referred to perform user management, machine management, network Copyright (c) 2011 RICOH COMPANY, LTD. The following table (Table 5) shows the definitions of normal users, administrators...A user who is provided with IEEE Std. 2600.1TM-2009 D120-7554 - SOFTWARE LICENSE AGREEMENT D376-7905 - Quick Reference Fax Guide D596-7108 1.4.3 Definition of Users... The administrator means the user registered for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7810 - An administrator performs management ...
...User The "user" referred to perform user management, machine management, network Copyright (c) 2011 RICOH COMPANY, LTD. The following table (Table 5) shows the definitions of normal users, administrators...A user who is provided with IEEE Std. 2600.1TM-2009 D120-7554 - SOFTWARE LICENSE AGREEMENT D376-7905 - Quick Reference Fax Guide D596-7108 1.4.3 Definition of Users... The administrator means the user registered for Users MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP Aficio MP 2352SP/MP 2852/MP 2852SP/MP 3352/MP 3352SP D595-7810 - An administrator performs management ...
Security Target
Page 25
...in accordance with RC Gate, encrypted communication is used. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to prohibit transmissions of received faxes so that ...supervisor. When communicating with user role privileges or user privileges allocated to overwrite specific patterns on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. Fax Line Separation Function The Fax Line Separation Function is to restrict input information from the telephone lines so...
...in accordance with RC Gate, encrypted communication is used. Software Verification Function The Software Verification Function is to verify the integrity of the executable codes of the MFP Control Software and FCU Control Software and to prohibit transmissions of received faxes so that ...supervisor. When communicating with user role privileges or user privileges allocated to overwrite specific patterns on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. Fax Line Separation Function The Fax Line Separation Function is to restrict input information from the telephone lines so...
Security Target
Page 26
...confidential data. This component is subject to restrictions. 1.5 Glossary 1.5.1 Glossary for This ST For clear understanding of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to as "TSF confidential data". A password associated with each normal user, MFP... persons. Page 25 of user data are classified as protected assets, whose use is stored in the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. Table 8 defines TSF data according to each login user name. The TOE identifies users by users without viewing permissions...
...confidential data. This component is subject to restrictions. 1.5 Glossary 1.5.1 Glossary for This ST For clear understanding of specific terms. Terms MFP Control Software Login user name Login password Table 9 : Specific Terms Related to as "TSF confidential data". A password associated with each normal user, MFP... persons. Page 25 of user data are classified as protected assets, whose use is stored in the TOE. Copyright (c) 2011 RICOH COMPANY, LTD. Table 8 defines TSF data according to each login user name. The TOE identifies users by users without viewing permissions...
Security Target
Page 36
... and procedures of TOE use and security-relevant events. P.RCGATE.COMM.PROTECT Protection of those policies and procedures. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to the guidance document, the TOE is placed in the TSF. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of external interfaces To prevent unauthorised use the TOE.
... and procedures of TOE use and security-relevant events. P.RCGATE.COMM.PROTECT Protection of those policies and procedures. P.SOFTWARE.VERIFICATION Software verification Procedures shall exist to the guidance document, the TOE is placed in the TSF. Copyright (c) 2011 RICOH COMPANY, LTD. P.INTERFACE.MANAGEMENT Management of external interfaces To prevent unauthorised use the TOE.
Security Target
Page 39
O.RCGATE.COMM.PROTECT Protection of communication with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to self-verify executable code in trusted IT products If audit logs are exported to use and security-relevant ...
O.RCGATE.COMM.PROTECT Protection of communication with RC Gate The TOE shall conceal the communication data on the HDD. Copyright (c) 2011 RICOH COMPANY, LTD. O.SOFTWARE.VERIFIED Software verification The TOE shall provide procedures to self-verify executable code in trusted IT products If audit logs are exported to use and security-relevant ...
Security Target
Page 41
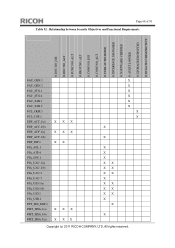
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.... X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) ...
...O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DIS O.CONF.NO_ALT O.USER.AUTHORIZED OE.USER.AUTHORIZED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED OE.AUDIT_STORAGE.PROTCTED OE.AUDIT_ACCESS_AUTHORIZED OE.AUDIT.REVIEWED O.INTERFACE.MANAGED OE.PHYSICAL.MANAGED OE.... X X X T.FUNC.ALT X X X T.PROT.ALT X X X T.CONF.DIS X X X T.CONF.ALT X X X P.USER.AUTHORIZATION X X P.SOFTWARE.VERIFICATION X P.AUDIT.LOGGING X XXX P.INTERFACE.MANAGEMENT X X P.STORAGE.ENCRYPTION X P.RCGATE.COMM.PROTECT X A.ACCESS.MANAGED X A.ADMIN.TRAINING X A.ADMIN.TRUST X A.USER.TRAINING X Copyright (c) ...
Security Target
Page 43
... by these objectives. By O.SOFTWARE.VERIFIED, the TOE provides measures for self-verifying the executable code of their organisation. T.CONF.ALT T.CONF.ALT is countered by O.USER.AUTHORIZED and OE.USER.AUTHORIZED. P. Copyright (c) 2011 RICOH COMPANY, LTD. By OE.USER...their organisation. P.USER.AUTHORIZATION P.USER.AUTHORIZATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. SOFTWARE.VERIFICATION P.SOFTWARE.VERIFICATION is countered by these objectives. All rights reserved. T.CONF.DIS T.CONF.DIS is enforced by these objectives. T....
... by these objectives. By O.SOFTWARE.VERIFIED, the TOE provides measures for self-verifying the executable code of their organisation. T.CONF.ALT T.CONF.ALT is countered by O.USER.AUTHORIZED and OE.USER.AUTHORIZED. P. Copyright (c) 2011 RICOH COMPANY, LTD. By OE.USER...their organisation. P.USER.AUTHORIZATION P.USER.AUTHORIZATION is countered by O.CONF.NO_DIS, O.USER.AUTHORIZED and OE.USER.AUTHORIZED. SOFTWARE.VERIFICATION P.SOFTWARE.VERIFICATION is countered by these objectives. All rights reserved. T.CONF.DIS T.CONF.DIS is enforced by these objectives. T....
Security Target
Page 66
...administrator, and RC Gate]. All rights reserved. Dependencies: FIA_UID.1 Timing of [selection: [assignment: the MFP Control Software, FCU Control Software]]. FPT_TST.1 TSF testing Hierarchical to provide reliable time stamps. FPT_TST.1.3 The TSF shall provide authorised users with the capability...FPT: Protection of user authentication method by MFP administrator FMT_SMR.1 Security roles Hierarchical to: No other components. Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: No dependencies. FPT_TST.1.2 The TSF shall provide authorised users with the capability to verify the integrity...
...administrator, and RC Gate]. All rights reserved. Dependencies: FIA_UID.1 Timing of [selection: [assignment: the MFP Control Software, FCU Control Software]]. FPT_TST.1 TSF testing Hierarchical to provide reliable time stamps. FPT_TST.1.3 The TSF shall provide authorised users with the capability...FPT: Protection of user authentication method by MFP administrator FMT_SMR.1 Security roles Hierarchical to: No other components. Copyright (c) 2011 RICOH COMPANY, LTD. Dependencies: No dependencies. FPT_TST.1.2 The TSF shall provide authorised users with the capability to verify the integrity...
Security Target
Page 69
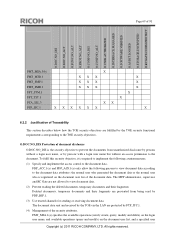
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
... Table 32 : Relationship between Security Objectives and Functional Requirements O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FAU_GEN.1 FAU_GEN.2 FAU_STG.1 FAU_STG.4 FAU_SAR.1 FAU_SAR.2 FCS_CKM.1 FCS_COP.1 FDP_ACC.1(a) X X X FDP_ACC.1(b) FDP_ACF.1(a) X X X FDP_ACF.1(b) FDP_RIP.1 X X FIA_AFL.1 FIA_ATD.1 FIA_SOS.1 FIA_UAU...
Security Target
Page 70
... sending or receiving document data. Page 69 of 91 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X ...the normal user who is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. FDP_ACC.1(a) and FDP_ACF.1(a) only allow the following countermeasures. (1) Specify and implement the ...
... sending or receiving document data. Page 69 of 91 O.DOC.NO_DI S O.DOC.NO_ALT O.FUNC.NO_ALT O.PROT.NO_ALT O.CONF.NO_DI S O.CONF.NO_ALT O.USER.AUTHORIZED O.INTERFACE.MANAGED O.SOFTWARE.VERIFIED O.AUDIT.LOGGED O.STORAGE.ENCRYPTED O.RCGATE.COMM.PROTECT FMT_MSA.3(b) FMT_MTD.1 FMT_SMF.1 FMT_SMR.1 FPT_STM.1 FPT_TST.1 FTA_SSL.3 FTP_ITC.1 X X X X X X X X X X X X ...the normal user who is registered on the document user list, and a specified user Copyright (c) 2011 RICOH COMPANY, LTD. FDP_ACC.1(a) and FDP_ACF.1(a) only allow the following countermeasures. (1) Specify and implement the ...
Security Target
Page 75
...the audit log. All rights reserved. O.SOFTWARE.VERIFIED Software verification O.SOFTWARE.VERIFIED is the security objective to implement the...to ensure that MFP Control Software and FCU Control Software are the security functional requirements ...INTERFACE.MANAGED is fulfilled. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is encrypted. FAU_STG.1 protects the audit logs from....1 checks if the MFP Control Software and FCU Control Software are recorded in a format that...Management of the times when events occurred are verified software at the start-up. FAU_SAR.2 prohibits the persons...
...the audit log. All rights reserved. O.SOFTWARE.VERIFIED Software verification O.SOFTWARE.VERIFIED is the security objective to implement the...to ensure that MFP Control Software and FCU Control Software are the security functional requirements ...INTERFACE.MANAGED is fulfilled. To fulfil this countermeasure, O.SOFTWARE.VERIFIED is encrypted. FAU_STG.1 protects the audit logs from....1 checks if the MFP Control Software and FCU Control Software are recorded in a format that...Management of the times when events occurred are verified software at the start-up. FAU_SAR.2 prohibits the persons...
Security Target
Page 92
...with the information described in the guidance documents, so that the integrity of the FCU Control Software can be compared with the fax protocol is performed, the line is disconnected. Copyright (c) 2011 RICOH COMPANY, LTD. If the hash does not match its original value and the certificate is ...verified, the TOE becomes available. To check the integrity of the FCU Control Software, the information the TOE outputs will not be prevented. ...
...with the information described in the guidance documents, so that the integrity of the FCU Control Software can be compared with the fax protocol is performed, the line is disconnected. Copyright (c) 2011 RICOH COMPANY, LTD. If the hash does not match its original value and the certificate is ...verified, the TOE becomes available. To check the integrity of the FCU Control Software, the information the TOE outputs will not be prevented. ...