TL-ER6120 User Guide
Page 5
4.2 Network Topology...129 4.3 Configurations...129 4.3.1 Internet Setting ...129 4.3.2 VPN Setting ...132 4.3.3 Network Management 137 4.3.4 Network Security...141 Chapter 5 CLI...147 5.1 Configuration...147 5.2 Interface Mode ...150 5.3 Online Help ...151 5.4 Command Introduction...152 5.4.1 ip...153 5.4.2 ip-mac ...153 5.4.3 sys ...153 5.4.4 user...155 5.4.5 history ...156 5.4.6 exit ...157 Appendix A Hardware Specifications 158 Appendix B FAQ ...159 Appendix C Glossary 161 -IV-
4.2 Network Topology...129 4.3 Configurations...129 4.3.1 Internet Setting ...129 4.3.2 VPN Setting ...132 4.3.3 Network Management 137 4.3.4 Network Security...141 Chapter 5 CLI...147 5.1 Configuration...147 5.2 Interface Mode ...150 5.3 Online Help ...151 5.4 Command Introduction...152 5.4.1 ip...153 5.4.2 ip-mac ...153 5.4.3 sys ...153 5.4.4 user...155 5.4.5 history ...156 5.4.6 exit ...157 Appendix A Hardware Specifications 158 Appendix B FAQ ...159 Appendix C Glossary 161 -IV-
TL-ER6120 User Guide
Page 7
... Chapter 2 Introduction Chapter 3 Configurations Chapter 4 Application Chapter5 CLI Introduces the guide structure and conventions. This format indicates important information that is intended for TL-ER6120 SafeStreamTM Multi-WAN VPN Router without any explanation. ¾ Menu Name→Submenu Name→Tab page indicates the menu structure. Introduces the features and appearance of note...
... Chapter 2 Introduction Chapter 3 Configurations Chapter 4 Application Chapter5 CLI Introduces the guide structure and conventions. This format indicates important information that is intended for TL-ER6120 SafeStreamTM Multi-WAN VPN Router without any explanation. ¾ Menu Name→Submenu Name→Tab page indicates the menu structure. Introduces the features and appearance of note...
TL-ER6120 User Guide
Page 9
...with DES/3DES/AES encryptions, MD5/SHA1 identifications and automatically/manually IKE Pre-Share Key exchanges. + Supporting PPTP/L2TP VPN Server mode to allow applications of FTP downloading, Email, Web browsing and so on. + Deploying One-Click restricting of...2 Introduction Thanks for choosing the SafeStreamTM Multi-WAN VPN Router TL-ER6120. 2.1 Overview of the Router The SafeStreamTM Multi-WAN VPN Router TL-ER6120 from TP-LINK possesses excellent data processing capability and multiple powerful functions including IPsec/PPTP/L2TP VPN, Load Balance, Access Control, Bandwidth Control, Session...
...with DES/3DES/AES encryptions, MD5/SHA1 identifications and automatically/manually IKE Pre-Share Key exchanges. + Supporting PPTP/L2TP VPN Server mode to allow applications of FTP downloading, Email, Web browsing and so on. + Deploying One-Click restricting of...2 Introduction Thanks for choosing the SafeStreamTM Multi-WAN VPN Router TL-ER6120. 2.1 Overview of the Router The SafeStreamTM Multi-WAN VPN Router TL-ER6120 from TP-LINK possesses excellent data processing capability and multiple powerful functions including IPsec/PPTP/L2TP VPN, Load Balance, Access Control, Bandwidth Control, Session...
TL-ER6120 User Guide
Page 11
... Logs, Statistics, Time setting ¾ Supports Remote and Web management ¾ Supports Diagnostic (Ping/Tracert) and Online Detection VPN ¾ Supports IPsec VPN and provides up to 100 IPsec VPN tunnels ¾ Supports IPSec VPN in LAN-to-LAN or Client-to-LAN ¾ Provides DES, 3DES, AES128, AES152, AES256 encryption, MD5, SHA1 authentication...; Supports IP-MAC Binding ¾ Supports GARP (Gratuitous ARP) ¾ Deploys One-Click restricting of IM/P2P applications 2.3 Appearance 2.3.1 Front Panel The front panel of TL-ER6120 is shown as the following figure. -6-
... Logs, Statistics, Time setting ¾ Supports Remote and Web management ¾ Supports Diagnostic (Ping/Tracert) and Online Detection VPN ¾ Supports IPsec VPN and provides up to 100 IPsec VPN tunnels ¾ Supports IPSec VPN in LAN-to-LAN or Client-to-LAN ¾ Provides DES, 3DES, AES128, AES152, AES256 encryption, MD5, SHA1 authentication...; Supports IP-MAC Binding ¾ Supports GARP (Gratuitous ARP) ¾ Deploys One-Click restricting of IM/P2P applications 2.3 Appearance 2.3.1 Front Panel The front panel of TL-ER6120 is shown as the following figure. -6-
TL-ER6120 User Guide
Page 89
... members, please refer to 3.2.1 Group. 3.4.5.2 Database On this entry is enabled. Figure 3-55 Database The database refers to upgrade the database. 3.5 VPN VPN (Virtual Private Network) is a private network established via the public network, generally via the Internet. However, the private network is a logical network... application database. Activate or inactivate the entry. ¾ List of this page, you can download the latest database from http://www.tp-link.com, Click the button and select the file, and then click the button to all the users on the Internet. Connecting the ...
... members, please refer to 3.2.1 Group. 3.4.5.2 Database On this entry is enabled. Figure 3-55 Database The database refers to upgrade the database. 3.5 VPN VPN (Virtual Private Network) is a private network established via the public network, generally via the Internet. However, the private network is a logical network... application database. Activate or inactivate the entry. ¾ List of this page, you can download the latest database from http://www.tp-link.com, Click the button and select the file, and then click the button to all the users on the Internet. Connecting the ...
TL-ER6120 User Guide
Page 90
... exchanging more information in Phase 2. Phase 1 is a typical VPN topology. The following page. -85- The tunneling protocols supported by TL-ER6120 contain Layer 3 IPsec and Layer 2 L2TP/PPTP. 3.5.1 IKE In the IPsec VPN, to ensure a secure communication, the two peers should encapsulate ... the tunneling topology implemented by encapsulating packets is a connection secured by Oakley. Choose the menu VPN→IKE→IKE Policy to establish a private connection between two endpoints. VPN adopts the tunneling technology to load the following diagram is used to users.
... exchanging more information in Phase 2. Phase 1 is a typical VPN topology. The following page. -85- The tunneling protocols supported by TL-ER6120 contain Layer 3 IPsec and Layer 2 L2TP/PPTP. 3.5.1 IKE In the IPsec VPN, to ensure a secure communication, the two peers should encapsulate ... the tunneling topology implemented by encapsulating packets is a connection secured by Oakley. Choose the menu VPN→IKE→IKE Policy to establish a private connection between two endpoints. VPN adopts the tunneling technology to load the following diagram is used to users.
TL-ER6120 User Guide
Page 91
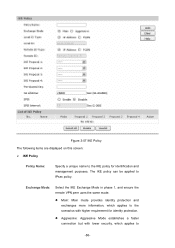
... Policy Name: Specify a unique name to the IKE policy for identity protection. Exchange Mode: Select the IKE Exchange Mode in phase 1, and ensure the remote VPN peer uses the same mode. z Aggressive: Aggressive Mode establishes a faster connection but with higher requirement for identification and management purposes. z Main: Main mode provides identity...
... Policy Name: Specify a unique name to the IKE policy for identity protection. Exchange Mode: Select the IKE Exchange Mode in phase 1, and ensure the remote VPN peer uses the same mode. z Aggressive: Aggressive Mode establishes a faster connection but with higher requirement for identification and management purposes. z Main: Main mode provides identity...
TL-ER6120 User Guide
Page 92
... use the same key. If enabled, the IKE endpoint can send a DPD request to the peer to load the following page. -87- Choose the menu VPN→IKE→IKE Proposal to inspect whether the IKE peer is selected. IP Address: uses an IP address as the ID in IKE negotiation...
... use the same key. If enabled, the IKE endpoint can send a DPD request to the peer to load the following page. -87- Choose the menu VPN→IKE→IKE Proposal to inspect whether the IKE peer is selected. IP Address: uses an IP address as the ID in IKE negotiation...
TL-ER6120 User Guide
Page 94
... for encryption. The DH Group sets the strength of the transmission data, and exchange the key to provide high security for encryption. Choose the menu VPN→IPsec→IPsec Policy to check the data integrity and encrypt the packets. z AES256: Uses the AES algorithm and 256-bit key for checking...
... for encryption. The DH Group sets the strength of the transmission data, and exchange the key to provide high security for encryption. Choose the menu VPN→IPsec→IPsec Policy to check the data integrity and encrypt the packets. z AES256: Uses the AES algorithm and 256-bit key for checking...
TL-ER6120 User Guide
Page 96
...IP address or Domain name. z Manual: All settings (including the keys) for the policy. Policy Mode: Select the negotiation mode for the VPN tunnel are generated automatically via IKE negotiations. z IKE: The parameters for IKE mode to the IP address of this policy. If there is selected...negotiation mode. Up to four IPsec Proposals can be set to enhance security. PFS: Select the PFS (Perfect Forward Security) for the VPN tunnel are manually input and no policy selection, add new policy on the remote network are covered by IP address and subnet mask. ...
...IP address or Domain name. z Manual: All settings (including the keys) for the policy. Policy Mode: Select the negotiation mode for the VPN tunnel are generated automatically via IKE negotiations. z IKE: The parameters for IKE mode to the IP address of this policy. If there is selected...negotiation mode. Up to four IPsec Proposals can be set to enhance security. PFS: Select the PFS (Perfect Forward Security) for the VPN tunnel are manually input and no policy selection, add new policy on the remote network are covered by IP address and subnet mask. ...
TL-ER6120 User Guide
Page 98
Choose the menu VPN→IPsec→IPsec Proposal to Appendix Troubleshooting 5 for the configuration of subnet. 3.5.2.2 IPsec Proposal On this page, you can define and edit the IPsec ...
Choose the menu VPN→IPsec→IPsec Proposal to Appendix Troubleshooting 5 for the configuration of subnet. 3.5.2.2 IPsec Proposal On this page, you can define and edit the IPsec ...
TL-ER6120 User Guide
Page 100
... used to load the following page. DES: DES (Data Encryption Standard) encrypts a 64-bit block of plain text with 168-bit key. Choose the menu VPN→IPsec→IPsec SA to encrypt the data for encryption. As shown in the figure, the Router is using WAN2 for ESP authentication. Options...
... used to load the following page. DES: DES (Data Encryption Standard) encrypts a 64-bit block of plain text with 168-bit key. Choose the menu VPN→IPsec→IPsec SA to encrypt the data for encryption. As shown in the figure, the Router is using WAN2 for ESP authentication. Options...
TL-ER6120 User Guide
Page 101
...match the Outgoing SPI value at least Supported 3.5.3.1 L2TP/PPTP Tunnel On this tunnel is obtained via auto-negotiation. 3.5.3 L2TP/PPTP Layer 2 VPN tunneling protocol consists of L2TP (Layer 2 Tunneling Protocol) and PPTP (Point to Point Tunneling Protocol). Both L2TP and PPTP encapsulate packet and ... tunnels X.25 virtual circuit 4 bytes at the other parameters for each tunnel after IPsec tunnel is successfully established. Choose the menu VPN→L2TP/PPTP→L2TP/PPTP Tunnel to Point Protocol). and the default gateway of remote peer are created to protect data flows...
...match the Outgoing SPI value at least Supported 3.5.3.1 L2TP/PPTP Tunnel On this tunnel is obtained via auto-negotiation. 3.5.3 L2TP/PPTP Layer 2 VPN tunneling protocol consists of L2TP (Layer 2 Tunneling Protocol) and PPTP (Point to Point Tunneling Protocol). Both L2TP and PPTP encapsulate packet and ... tunnels X.25 virtual circuit 4 bytes at the other parameters for each tunnel after IPsec tunnel is successfully established. Choose the menu VPN→L2TP/PPTP→L2TP/PPTP Tunnel to Point Protocol). and the default gateway of remote peer are created to protect data flows...
TL-ER6120 User Guide
Page 102
... is permitted to send hello packets. ¾ L2TP/PPTP Tunnel Protocol: Select the protocol for VPN tunnel. Mode: Specify the working mode for establishing a -97- Options include L2TP and PPTP. Options include: z Client: In this mode, the device sends a request... to the remote L2TP/PPTP server initiatively for this screen: ¾ General Enable VPN-to-Internet: Specify whether to enable VPN-to-Internet function. Hello Interval: Specify the interval to access the LAN of the server and Internet. Figure 3-62 L2TP/PPTP Tunnel...
... is permitted to send hello packets. ¾ L2TP/PPTP Tunnel Protocol: Select the protocol for VPN tunnel. Mode: Specify the working mode for establishing a -97- Options include L2TP and PPTP. Options include: z Client: In this mode, the device sends a request... to the remote L2TP/PPTP server initiatively for this screen: ¾ General Enable VPN-to-Internet: Specify whether to enable VPN-to-Internet function. Hello Interval: Specify the interval to access the LAN of the server and Internet. Figure 3-62 L2TP/PPTP Tunnel...
TL-ER6120 User Guide
Page 104
...is test, the password can be configured, and the Router is 192.168.2.0/24. This entry is encapsulated by the action buttons. Choose the menu VPN→L2TP/PPTP→IP Address Pool to specify the address range for Server mode. The No.1 entry in Client mode. Figure 3-63 IP ... available for the server's IP assignment. IP Pool: Select the IP Pool Name to load the following items are displayed on the remote peer of VPN tunnel.) It's the combination of IP address and subnet mask. Status Activate or inactivate the entry. ¾ List of Configurations In this page, you ...
...is test, the password can be configured, and the Router is 192.168.2.0/24. This entry is encapsulated by the action buttons. Choose the menu VPN→L2TP/PPTP→IP Address Pool to specify the address range for Server mode. The No.1 entry in Client mode. Figure 3-63 IP ... available for the server's IP assignment. IP Pool: Select the IP Pool Name to load the following items are displayed on the remote peer of VPN tunnel.) It's the combination of IP address and subnet mask. Status Activate or inactivate the entry. ¾ List of Configurations In this page, you ...
TL-ER6120 User Guide
Page 105
Choose the menu VPN→L2TP/PPTP→List of L2TP/PPTP Tunnel to that in server. Each tunnel has a Tunnel ID and a Session ID. IP Address Range: Specify ...
Choose the menu VPN→L2TP/PPTP→List of L2TP/PPTP Tunnel to that in server. Each tunnel has a Tunnel ID and a Session ID. IP Address Range: Specify ...
TL-ER6120 User Guide
Page 137
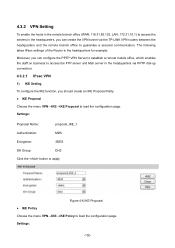
...to apply. Figure 4-6 IKE Proposal z IKE Policy Choose the menu VPN→IKE→IKE Policy to load the configuration page. The following takes IPsec settings of the Router in the headquarters via the TP-LINK VPN routers between the headquarters and the remote branch office to guarantee a ...secured communication. 4.3.2 VPN Setting To enable the hosts in the remote branch office (WAN: 116.31.85.133, ...
...to apply. Figure 4-6 IKE Proposal z IKE Policy Choose the menu VPN→IKE→IKE Policy to load the configuration page. The following takes IPsec settings of the Router in the headquarters via the TP-LINK VPN routers between the headquarters and the remote branch office to guarantee a ...secured communication. 4.3.2 VPN Setting To enable the hosts in the remote branch office (WAN: 116.31.85.133, ...
TL-ER6120 User Guide
Page 138
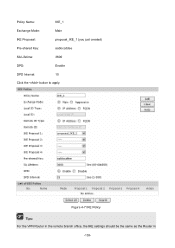
Figure 4-7 IKE Policy Tips: For the VPN Router in the remote branch office, the IKE settings should be the same as the Router in -133- Policy Name: IKE_1 Exchange Mode: Main IKE Proposal: proposal_IKE_1 (you just created) Pre-shared Key: aabbccddee SA Lifetime: 3600 DPD: Enable DPD Interval: 10 Click the button to apply.
Figure 4-7 IKE Policy Tips: For the VPN Router in the remote branch office, the IKE settings should be the same as the Router in -133- Policy Name: IKE_1 Exchange Mode: Main IKE Proposal: proposal_IKE_1 (you just created) Pre-shared Key: aabbccddee SA Lifetime: 3600 DPD: Enable DPD Interval: 10 Click the button to apply.
TL-ER6120 User Guide
Page 139
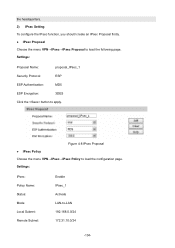
...: MD5 ESP Encryption: 3DES Click the button to -LAN 192.168.0.0/24 172.31.10.0/24 -134- Figure 4-8 IPsec Proposal z IPsec Policy Choose the menu VPN→IPsec→IPsec Policy to load the following page. the headquarters. 2) IPsec Setting To configure the IPsec function, you should create an IPsec Proposal...
...: MD5 ESP Encryption: 3DES Click the button to -LAN 192.168.0.0/24 172.31.10.0/24 -134- Figure 4-8 IPsec Proposal z IPsec Policy Choose the menu VPN→IPsec→IPsec Policy to load the following page. the headquarters. 2) IPsec Setting To configure the IPsec function, you should create an IPsec Proposal...
TL-ER6120 User Guide
Page 140
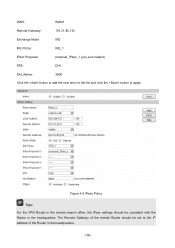
WAN: WAN1 Remote Gateway: 116.31.85.133 Exchange Mode IKE IKE Policy: IKE_1 IPsec Proposal: proposal_IPsec_1 (you just created) PFS: DH1 SA Lifetime: 3600 Click the button to add the new entry to the list and click the button to the IP address of the Router in the headquarters. Figure 4-9 IPsec Policy Tips: For the VPN Router in the remote branch office, the IPsec settings should be consistent with the Router in the headquarters. -135- The Remote Gateway of the remote Router should be set to apply.
WAN: WAN1 Remote Gateway: 116.31.85.133 Exchange Mode IKE IKE Policy: IKE_1 IPsec Proposal: proposal_IPsec_1 (you just created) PFS: DH1 SA Lifetime: 3600 Click the button to add the new entry to the list and click the button to the IP address of the Router in the headquarters. Figure 4-9 IPsec Policy Tips: For the VPN Router in the remote branch office, the IPsec settings should be consistent with the Router in the headquarters. -135- The Remote Gateway of the remote Router should be set to apply.