User Guide
Page 4
... the Wireless Client Utility 2 Working with Profiles ...3 Creating a Profile ...3 Modifying Profiles ...6 Checking for Available Access Points 10 Disabling the Wireless Client Utility 11 HotSpot Detector Hardware 13 Charging TEW-429UB 13 Identifying Components 13 LCD Icons ...13 Finding a HotSpot 14 Accessing a HotSpot 14 Exploring the Wireless Client Utility Screens 15 The Network Screen 15 Wireless...
... the Wireless Client Utility 2 Working with Profiles ...3 Creating a Profile ...3 Modifying Profiles ...6 Checking for Available Access Points 10 Disabling the Wireless Client Utility 11 HotSpot Detector Hardware 13 Charging TEW-429UB 13 Identifying Components 13 LCD Icons ...13 Finding a HotSpot 14 Accessing a HotSpot 14 Exploring the Wireless Client Utility Screens 15 The Network Screen 15 Wireless...
User Guide
Page 9
...record of your home you use to connect to access your home network and your current connection. Then when you go from the office to reconfigure the TEW-429UB each time you can configure the TEW-429UB to a particular access point. NOTE YOU CAN CHANGE PROFILES WITHOUT REBOOTING YOUR COMPUTER.... (PERHAPS WHEN WALKING FROM ONE ACCESS POINT TO ANOTHER WITHIN YOUR OFFICE.) IF YOU USE WINDOWS...
...record of your home you use to connect to access your home network and your current connection. Then when you go from the office to reconfigure the TEW-429UB each time you can configure the TEW-429UB to a particular access point. NOTE YOU CAN CHANGE PROFILES WITHOUT REBOOTING YOUR COMPUTER.... (PERHAPS WHEN WALKING FROM ONE ACCESS POINT TO ANOTHER WITHIN YOUR OFFICE.) IF YOU USE WINDOWS...
User Guide
Page 10
... or Ad-Hoc. You can type anything for the profile such as the same SSID is used on the computer you are connecting to an access point or wireless router. All devices must use this case-sensitive name, which is the name assigned to communicate. 4 You will need to another... computer without using an access point. In the SSID pane click Browse. Type a descriptive name for the SSID as long as Office or CoffeeShop. 4. The utility performs a site survey ...
... or Ad-Hoc. You can type anything for the profile such as the same SSID is used on the computer you are connecting to an access point or wireless router. All devices must use this case-sensitive name, which is the name assigned to communicate. 4 You will need to another... computer without using an access point. In the SSID pane click Browse. Type a descriptive name for the SSID as long as Office or CoffeeShop. 4. The utility performs a site survey ...
User Guide
Page 11
6. Security settings vary in the access point you want to connect to and click Add to consult your network administrator for this information. See "Configuring Wireless Security" for the security mode. 5 The WLAN Security Configuration screen appears. This screen reflects the security settings detected in complexity and you want to connect to. Select the Security Mode from the drop-down list and then select the appropriate settings for more information. 8. Select the SSID you may have to Profile. 7. Click Next.
6. Security settings vary in the access point you want to connect to and click Add to consult your network administrator for this information. See "Configuring Wireless Security" for the security mode. 5 The WLAN Security Configuration screen appears. This screen reflects the security settings detected in complexity and you want to connect to. Select the Security Mode from the drop-down list and then select the appropriate settings for more information. 8. Select the SSID you may have to Profile. 7. Click Next.
User Guide
Page 14
...WPA-PSK/WPA2-PSK WHENEVER POSSIBLE. WPA2 PROVIDES EVEN STRONGER ENCRYPTION, AUTHENTICATION AND KEY MANAGEMENT. 8 When using WEP encryption, only access points and PCs using the same WEP Key can communicate with each client must have in order to choose from the following settings:... Disabled (No Encryption) All data sent between the access point and the client is a compromise between the access point and the client using their own unique username, password, and security certificate. WEP (Wired Equivalent Privacy) ...
...WPA-PSK/WPA2-PSK WHENEVER POSSIBLE. WPA2 PROVIDES EVEN STRONGER ENCRYPTION, AUTHENTICATION AND KEY MANAGEMENT. 8 When using WEP encryption, only access points and PCs using the same WEP Key can communicate with each client must have in order to choose from the following settings:... Disabled (No Encryption) All data sent between the access point and the client is a compromise between the access point and the client using their own unique username, password, and security certificate. WEP (Wired Equivalent Privacy) ...
User Guide
Page 16
... Guide for access points using the TEW-429UB, refer to the following Web sites for updated information for public use is constantly increasing in the vicinity of an access point, you do not have to turn on the locations of hot spots. Click Refresh anytime to find access points. To scan...spot finder functionality of the WHF-432/230 to locate access points while you are in major cities. Open the Wireless Client Utility and click SiteSurvey. 2. Check the following . 1. Checking for Available Access Points The number of access points or hot spots for your computer to update the ...
... Guide for access points using the TEW-429UB, refer to the following Web sites for updated information for public use is constantly increasing in the vicinity of an access point, you do not have to turn on the locations of hot spots. Click Refresh anytime to find access points. To scan...spot finder functionality of the WHF-432/230 to locate access points while you are in major cities. Open the Wireless Client Utility and click SiteSurvey. 2. Check the following . 1. Checking for Available Access Points The number of access points or hot spots for your computer to update the ...
User Guide
Page 17
...screen. Open the Wireless Client Utility and click Options. 11 3. Select the network you want to the following screen. (You can also double-click an access point to have Windows manage your wireless network settings. In that case, you want and click Connect. For details about any of the listed... access points, select it from the list and click Detailed Info to see the following . 1. To disable the Wireless Client Utility refer to connect later. Or ...
...screen. Open the Wireless Client Utility and click Options. 11 3. Select the network you want to the following screen. (You can also double-click an access point to have Windows manage your wireless network settings. In that case, you want and click Connect. For details about any of the listed... access points, select it from the list and click Detailed Info to see the following . 1. To disable the Wireless Client Utility refer to connect later. Or ...
User Guide
Page 22
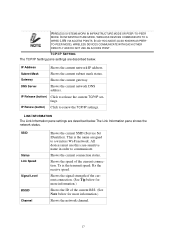
... are for more information.) Security Shows the security status. Reconnect (button) Press to reconnect to select another profile. Click the dropdown arrow to the current access point. Network Mode Shows the current network mode. The settings shown in the Network screen are described below for the current profile. Infrastructure or ad-hoc...
... are for more information.) Security Shows the security status. Reconnect (button) Press to reconnect to select another profile. Click the dropdown arrow to the current access point. Network Mode Shows the current network mode. The settings shown in the Network screen are described below for the current profile. Infrastructure or ad-hoc...
User Guide
Page 23
... current connection status. IN AD-HOC MODE (ALSO KNOWN AS PEERTO-PEER MODE), WIRELESS DEVICES COMMUNICATE WITH EACH OTHER DIRECTLY AND DO NOT USE AN ACCESS POINT. SSID Status Link Speed Signal Level BSSID Channel Shows the current SSID (Service Set IDentifier). Shows the speed of the current BSS. (See Note ...below for more information.) Shows the ID of the current connection. Rx the receive speed. IN INFRASTRUCTURE MODE, WIRELESS DEVICES COMMUNICATE TO A WIRED LAN VIA ACCESS POINTS. DNS Server Shows the current network DNS address. Shows the current subnet mask status.
... current connection status. IN AD-HOC MODE (ALSO KNOWN AS PEERTO-PEER MODE), WIRELESS DEVICES COMMUNICATE WITH EACH OTHER DIRECTLY AND DO NOT USE AN ACCESS POINT. SSID Status Link Speed Signal Level BSSID Channel Shows the current SSID (Service Set IDentifier). Shows the speed of the current BSS. (See Note ...below for more information.) Shows the ID of the current connection. Rx the receive speed. IN INFRASTRUCTURE MODE, WIRELESS DEVICES COMMUNICATE TO A WIRED LAN VIA ACCESS POINTS. DNS Server Shows the current network DNS address. Shows the current subnet mask status.
User Guide
Page 24
... (ALSO KNOWN AS PEER-TO-PEER MODE), WIRELESS DEVICES COMMUNICATE WITH EACH OTHER DIRECTLY AND DO NOT USE AN ACCESS POINT. Without profiles, you would have to reconfigure the TEW-429UB each time you use to connect to attain a suitable signal. THIS IS AN INDEPENDENT BSS (IBSS). Using the... Profile screen you can configure the TEW-429UB to access you move around to a particular access point. THE LINK INFORMATION PANEL IS SHOWN IN ALL SCREENS SO YOU CAN ALWAYS SEE THE STATUS OF YOUR CURRENT CONNECTION. ...
... (ALSO KNOWN AS PEER-TO-PEER MODE), WIRELESS DEVICES COMMUNICATE WITH EACH OTHER DIRECTLY AND DO NOT USE AN ACCESS POINT. Without profiles, you would have to reconfigure the TEW-429UB each time you use to connect to attain a suitable signal. THIS IS AN INDEPENDENT BSS (IBSS). Using the... Profile screen you can configure the TEW-429UB to access you move around to a particular access point. THE LINK INFORMATION PANEL IS SHOWN IN ALL SCREENS SO YOU CAN ALWAYS SEE THE STATUS OF YOUR CURRENT CONNECTION. ...
User Guide
Page 27
DETAILED INFO. Use this screen to view the Detailed Info screen. SCREEN For details about any of the listed access points, select it from the list and click Detailed Info to see the following screen. (You can also double-click an access point to disable the Wireless Client Utility. 21 The Options Screen By default, the Wireless Client Utility configures your wireless settings.
DETAILED INFO. Use this screen to view the Detailed Info screen. SCREEN For details about any of the listed access points, select it from the list and click Detailed Info to see the following screen. (You can also double-click an access point to disable the Wireless Client Utility. 21 The Options Screen By default, the Wireless Client Utility configures your wireless settings.
User Guide
Page 31
.... Generate your own WEP Key (4 keys maximum) using PassPhrase Manual Input (ASCII) Manual Input (HEX) Select the encryption to generate your WEP key on your access point. The WEP Configuration screen appears. 4. WEP Method Authentication Make Key using ASCII characters (5 characters for 64-bit, 13 characters for 128-bit). 25 A WEP Key... generated as you have used by your own WEP Key using hexadecimal characters (10 characters for 64-bit, 26 characters for 128-bit) Generate your access point. Use this feature when you type in any PassPhrase of your...
.... Generate your own WEP Key (4 keys maximum) using PassPhrase Manual Input (ASCII) Manual Input (HEX) Select the encryption to generate your WEP key on your access point. The WEP Configuration screen appears. 4. WEP Method Authentication Make Key using ASCII characters (5 characters for 64-bit, 13 characters for 128-bit). 25 A WEP Key... generated as you have used by your own WEP Key using hexadecimal characters (10 characters for 64-bit, 26 characters for 128-bit) Generate your access point. Use this feature when you type in any PassPhrase of your...
User Guide
Page 33
CONFIGURING 802.1 X - PEAP Refer to the following to know if your access point. CONFIGURING 802.1 X You need to configure PEAP. 27 Options for WPA-PSK & WPA2-PSK.) 3. 1. Click the drop-down arrow at Security Mode and choose WPA-...PSK or WPA2-PSK. 2. Click the drop-down arrow at Encryption Method and choose TKIP or AES. (Most access points use TKIP for User Information depend on your access point supports 802.1x and then apply the configuration here. 1. Choose the EAP method under Authentication protocol. 2. At PSK Pass Phrase enter...
CONFIGURING 802.1 X - PEAP Refer to the following to know if your access point. CONFIGURING 802.1 X You need to configure PEAP. 27 Options for WPA-PSK & WPA2-PSK.) 3. 1. Click the drop-down arrow at Security Mode and choose WPA-...PSK or WPA2-PSK. 2. Click the drop-down arrow at Encryption Method and choose TKIP or AES. (Most access points use TKIP for User Information depend on your access point supports 802.1x and then apply the configuration here. 1. Choose the EAP method under Authentication protocol. 2. At PSK Pass Phrase enter...
User Guide
Page 37
...As the wireless station moves from one or more wireless stations communicate directly to interact with an EAP-compatible RADIUS server, an access point helps a wireless station and a RADIUS server perform authentication. C HANNEL A radio frequency used below, look for both the ...is an authentication protocol that transmits wireless from the original to a difficult-to computer without the use of a base station (access point). During this period, the wireless stations maintain uninterrupted connection to support multiple types of user authentication. E NCRYPTION The reversible ...
...As the wireless station moves from one or more wireless stations communicate directly to interact with an EAP-compatible RADIUS server, an access point helps a wireless station and a RADIUS server perform authentication. C HANNEL A radio frequency used below, look for both the ...is an authentication protocol that transmits wireless from the original to a difficult-to computer without the use of a base station (access point). During this period, the wireless stations maintain uninterrupted connection to support multiple types of user authentication. E NCRYPTION The reversible ...
User Guide
Page 38
... that are user authentication and improved data encryption. Key differences between the TEW-429UB and the AP or other . If you do not have the same SSID to communicate with each access point, wireless gateway and wireless client. WPA/WPA2 Wi-Fi Protected Access (WPA) and WPA2 (future upgrade) is a unique name shared among all...
... that are user authentication and improved data encryption. Key differences between the TEW-429UB and the AP or other . If you do not have the same SSID to communicate with each access point, wireless gateway and wireless client. WPA/WPA2 Wi-Fi Protected Access (WPA) and WPA2 (future upgrade) is a unique name shared among all...