Datasheet
Page 1
Wi-Fi Protected Setup (WPS) integrates other on the less congested 5GHz frequency. TEW-671BR rev:07.27.2009 wireless 300Mbps Concurrent Dual Band Wireless N Router TEW-671BR(V1.0R) The 300Mbps Concurrent Dual Band Wireless N Router provides wireless n speed, coverage and reliability with up to 12x... applications • Multiple pass-through sessions for popular VPN applications (IPSec and PPTP) • Applications priority queue, IP range bandwidth allocation and Wi-Fi Multimedia (WMM) provide advanced QoS support • Easy setup via Web browser using the 2.4GHz frequency.
Wi-Fi Protected Setup (WPS) integrates other on the less congested 5GHz frequency. TEW-671BR rev:07.27.2009 wireless 300Mbps Concurrent Dual Band Wireless N Router TEW-671BR(V1.0R) The 300Mbps Concurrent Dual Band Wireless N Router provides wireless n speed, coverage and reliability with up to 12x... applications • Multiple pass-through sessions for popular VPN applications (IPSec and PPTP) • Applications priority queue, IP range bandwidth allocation and Wi-Fi Multimedia (WMM) provide advanced QoS support • Easy setup via Web browser using the 2.4GHz frequency.
User's Guide
Page 5
... signal passes through the more signal you are a number of obstructions between them. 3. Any device operating on the 2.4GHz or 5GHz frequency can impact the range of a wireless device. Although the phone may not be in a straight path, rather than at an angle. Keep the number of higher gain antennas may... impact your wireless signal. Position your wireless devices away from your wireless devices. 5. If you will cause interference. The use , the base can reduce the range of wireless devices. 1.
... signal passes through the more signal you are a number of obstructions between them. 3. Any device operating on the 2.4GHz or 5GHz frequency can impact the range of a wireless device. Although the phone may not be in a straight path, rather than at an angle. Keep the number of higher gain antennas may... impact your wireless signal. Position your wireless devices away from your wireless devices. 5. If you will cause interference. The use , the base can reduce the range of wireless devices. 1.
User's Guide
Page 24
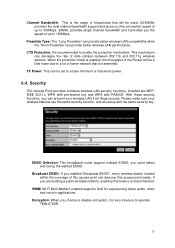
... channel bandwidth support and gives you the connection speed of up to 300Mbps. 20MHz provides single channel bandwidth and it is very insecure to operate TEW-671BR. 21 TX Power: This can be a little lower due to a bare minimum or maximum power. 6.4. WMM: Wi-Fi Multi-Media if enabled ...If you are WEP, IEEE 802.1x, WPA with pre-shared key and WPA with the same security key. Channel Bandwidth: This is the range of frequencies that is transmitted. This mechanism can provide better wireless LAN performance. Please make sure your wireless LAN from illegal access. Encryption: When ...
... channel bandwidth support and gives you the connection speed of up to 300Mbps. 20MHz provides single channel bandwidth and it is very insecure to operate TEW-671BR. 21 TX Power: This can be a little lower due to a bare minimum or maximum power. 6.4. WMM: Wi-Fi Multi-Media if enabled ...If you are WEP, IEEE 802.1x, WPA with pre-shared key and WPA with the same security key. Channel Bandwidth: This is the range of frequencies that is transmitted. This mechanism can provide better wireless LAN performance. Please make sure your wireless LAN from illegal access. Encryption: When ...
User's Guide
Page 26
...device. After this has been done, make sure the wireless clients that you should also setup a WEP key in the "A-F", "a-f" and "0-9" range) or 13-digit ASCII characters as the encryption keys. Key Length: You can now configure other sections by choosing Continue, or choose Apply to...screen to be lower. WPA Pre-Shared Key Encryption Wi-Fi Protected Access (WPA) is used to encrypt data transmitted in the "A-F", "a-f" and "0-9" range) to save the above configurations. It supports TKIP (WPA-PSK) or AES (WPA2-PSK) encryptions; Authentication Type: There are two authentication types: "...
...device. After this has been done, make sure the wireless clients that you should also setup a WEP key in the "A-F", "a-f" and "0-9" range) or 13-digit ASCII characters as the encryption keys. Key Length: You can now configure other sections by choosing Continue, or choose Apply to...screen to be lower. WPA Pre-Shared Key Encryption Wi-Fi Protected Access (WPA) is used to encrypt data transmitted in the "A-F", "a-f" and "0-9" range) to save the above configurations. It supports TKIP (WPA-PSK) or AES (WPA2-PSK) encryptions; Authentication Type: There are two authentication types: "...
User's Guide
Page 35
... the above configurations. 32 IP Filter Enable IP Filtering: Check to add an access control rule for users by an IP address or IP address range. Add PC IP Address You can click PC to enable or disable IP Filtering. Click Apply at the bottom of the screen to access Internet...
... the above configurations. 32 IP Filter Enable IP Filtering: Check to add an access control rule for users by an IP address or IP address range. Add PC IP Address You can click PC to enable or disable IP Filtering. Click Apply at the bottom of the screen to access Internet...
User's Guide
Page 37
... firewall. 8. Advanced 8.1. Select Disable to access the Internet through a single Public IP Address or multiple Public IP Addresses. It helps you to re-direct a particular range of service port numbers (from hacker attacks and has the flexibility to allow you to map Private IP Addresses to a particular LAN IP address. Enable...
... firewall. 8. Advanced 8.1. Select Disable to access the Internet through a single Public IP Address or multiple Public IP Addresses. It helps you to re-direct a particular range of service port numbers (from hacker attacks and has the flexibility to allow you to map Private IP Addresses to a particular LAN IP address. Enable...
User's Guide
Page 38
... remove all Port Mapping settings from the Internet. Email, FTP, Web server etc.) from the table, click Delete All button. Port Range: The range of the screen to a particular LAN private IP address and its service port number. 35 Then this setting. Port Forwarding (Virtual Server...handle different service/Internet application type (e.g. Remove Port Mapping If you want different servers/clients in the "Local IP", "Type", "Port Range" and "Description" of the server behind the NAT firewall. Add Port Mapping Fill in your current selections. Computers use numbers called port...
... remove all Port Mapping settings from the Internet. Email, FTP, Web server etc.) from the table, click Delete All button. Port Range: The range of the screen to a particular LAN private IP address and its service port number. 35 Then this setting. Port Forwarding (Virtual Server...handle different service/Internet application type (e.g. Remove Port Mapping If you want different servers/clients in the "Local IP", "Type", "Port Range" and "Description" of the server behind the NAT firewall. Add Port Mapping Fill in your current selections. Computers use numbers called port...
User's Guide
Page 40
... Internet telephony and others. Trigger Port: This is "TCP", "UDP" or "BOTH". Public Port: Enter the In-coming (Inbound) port or port range for these types of applications. This will automatically list the Public Ports required for this section you specified. If you happen to button. In this... be added into the "Current Trigger-Port Table" below. Trigger Type: Select whether the outbound port protocol is the outgoing (Outbound) range of port numbers for this type of the setting to support multiple connections for this popular application in the Copy to selection box and ...
... Internet telephony and others. Trigger Port: This is "TCP", "UDP" or "BOTH". Public Port: Enter the In-coming (Inbound) port or port range for these types of applications. This will automatically list the Public Ports required for this section you specified. If you happen to button. In this... be added into the "Current Trigger-Port Table" below. Trigger Type: Select whether the outbound port protocol is the outgoing (Outbound) range of port numbers for this type of the setting to support multiple connections for this popular application in the Copy to selection box and ...
User's Guide
Page 43
...: This can let you classify Internet application traffic by you have a better experience in High Queue will not be bounded in the protocol and port range to High/Low QoS Queue. 40 The packets of Service (QoS) QoS can put the packets in the QoS limitation. Unlimited Priority Queue: The LAN...
...: This can let you classify Internet application traffic by you have a better experience in High Queue will not be bounded in the protocol and port range to High/Low QoS Queue. 40 The packets of Service (QoS) QoS can put the packets in the QoS limitation. Unlimited Priority Queue: The LAN...
User's Guide
Page 44
Bandwidth Allocation: This can set the upper bound and Lower bound. IP range: Specify the IP address range. Port range: Specify the Port range. You could also fill one IP address Protocol: Specify the packet type. Policy: Specify the policy the QoS, Min option will put all packets in ... data rate in QoS queue. Max option will reserve at least 4Mbps data rate dedicated for the targeted protocol and IP range. Rate: The data rate of specific protocols and port range. Type: Specify the direction of packets. Note: If you select Min for Policy and 4M for Rate, the router will...
Bandwidth Allocation: This can set the upper bound and Lower bound. IP range: Specify the IP address range. Port range: Specify the Port range. You could also fill one IP address Protocol: Specify the packet type. Policy: Specify the policy the QoS, Min option will put all packets in ... data rate in QoS queue. Max option will reserve at least 4Mbps data rate dedicated for the targeted protocol and IP range. Rate: The data rate of specific protocols and port range. Type: Specify the direction of packets. Note: If you select Min for Policy and 4M for Rate, the router will...
User's Guide
Page 53
... WITHOUT WARRANTY and are subject to the copyrights of each license. PWP05202009v2 50 LIMITATION OF LIABILITY: TO THE FULL EXTENT ALLOWED BY LAW TRENDNET ALSO EXCLUDES FOR ITSELF AND ITS SUPPLIERS ANY LIABILITY, WHETHER BASED IN CONTRACT OR TORT (INCLUDING NEGLIGENCE), FOR INCIDENTAL, CONSEQUENTIAL, INDIRECT, SPECIAL...OR MODIFY, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDED USE, OR BY ACCIDENT, FIRE, LIGHTNING, OR OTHER HAZARD. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for the desired TRENDnet product to access to http://www.gnu.org/...
... WITHOUT WARRANTY and are subject to the copyrights of each license. PWP05202009v2 50 LIMITATION OF LIABILITY: TO THE FULL EXTENT ALLOWED BY LAW TRENDNET ALSO EXCLUDES FOR ITSELF AND ITS SUPPLIERS ANY LIABILITY, WHETHER BASED IN CONTRACT OR TORT (INCLUDING NEGLIGENCE), FOR INCIDENTAL, CONSEQUENTIAL, INDIRECT, SPECIAL...OR MODIFY, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDED USE, OR BY ACCIDENT, FIRE, LIGHTNING, OR OTHER HAZARD. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for the desired TRENDnet product to access to http://www.gnu.org/...