Datasheet
Page 2
SecurView PoE Dome Internet Camera TV-IP252P (A1.0R) SPECIFICATIONS Camera General Audio Image & Video Frequency Manual Pan/Tilt/Rotate GPIO TV-out Hardware Network LED Reset Button Power Consumption Power Dimension Weight Temperature Certifications Requirements To View To Run Software SecurView™ Software Network Protocols Setting Image... ~ 60°C (14°F ~ 140°F) • CE, FCC • Internet Explorer 6.0 or above • Windows 2000, XP, Vista • Channel: Supports up to 16 cameras • Record/playback/motion detection/audio • TCP/IP, UDP, ICMP • DHCP...
SecurView PoE Dome Internet Camera TV-IP252P (A1.0R) SPECIFICATIONS Camera General Audio Image & Video Frequency Manual Pan/Tilt/Rotate GPIO TV-out Hardware Network LED Reset Button Power Consumption Power Dimension Weight Temperature Certifications Requirements To View To Run Software SecurView™ Software Network Protocols Setting Image... ~ 60°C (14°F ~ 140°F) • CE, FCC • Internet Explorer 6.0 or above • Windows 2000, XP, Vista • Channel: Supports up to 16 cameras • Record/playback/motion detection/audio • TCP/IP, UDP, ICMP • DHCP...
User's Guide
Page 3
...; shows you the detail instructions on operating SecurView™ software. NOTE The illustrations and configuration values in this camera at home, at work within your PC. Appendix Provides the specification of the camera and some useful information for reference only. The actual settings depend on your camera. You can be set up easily and work...
...; shows you the detail instructions on operating SecurView™ software. NOTE The illustrations and configuration values in this camera at home, at work within your PC. Appendix Provides the specification of the camera and some useful information for reference only. The actual settings depend on your camera. You can be set up easily and work...
User's Guide
Page 5
A.1 SPECIFICATION 90 A.2 GLOSSARY OF TERMS 92 - 4 -
A.1 SPECIFICATION 90 A.2 GLOSSARY OF TERMS 92 - 4 -
User's Guide
Page 46
... a mobile phone that supports 3GPP, you can receive the on your phone (with audio. You can play the sound and voice through the camera. 3GPP: The camera supports 3GPP specification. The default setting is 90. Video & Audio >> Text Overlay - 45 - otherwise, select 3GPP Without Audio or 3GPP With Audio to transfer...
... a mobile phone that supports 3GPP, you can receive the on your phone (with audio. You can play the sound and voice through the camera. 3GPP: The camera supports 3GPP specification. The default setting is 90. Video & Audio >> Text Overlay - 45 - otherwise, select 3GPP Without Audio or 3GPP With Audio to transfer...
User's Guide
Page 93
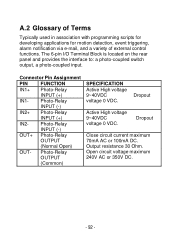
... detection, event triggering, alarm notification via e-mail, and a variety of external control functions. Photo-Relay INPUT (-) IN2+ Photo-Relay INPUT (+) IN2- Photo-Relay OUTPUT (Common) SPECIFICATION Active High voltage 9~40VDC voltage 0 VDC. Output resistance 30 Ohm. Dropout Active High voltage 9~40VDC voltage 0 VDC. Dropout Close circuit current maximum 70mA AC or...
... detection, event triggering, alarm notification via e-mail, and a variety of external control functions. Photo-Relay INPUT (-) IN2+ Photo-Relay INPUT (+) IN2- Photo-Relay OUTPUT (Common) SPECIFICATION Active High voltage 9~40VDC voltage 0 VDC. Output resistance 30 Ohm. Dropout Active High voltage 9~40VDC voltage 0 VDC. Dropout Close circuit current maximum 70mA AC or...
User's Guide
Page 96
... can automatically configure a network device in a diskless workstation to give its own IP address. The cabling or transmission method they use is the message. DHCP allows the specification for the service provided by Microsoft, DHCP (Dynamic Host Configuration Protocol) is an Internet protocol that can have ...a different IP address every time it connects to the network. The data they 're easier to - 95 -...
... can automatically configure a network device in a diskless workstation to give its own IP address. The cabling or transmission method they use is the message. DHCP allows the specification for the service provided by Microsoft, DHCP (Dynamic Host Configuration Protocol) is an Internet protocol that can have ...a different IP address every time it connects to the network. The data they 're easier to - 95 -...
User's Guide
Page 101
... Protocol PCM (Pulse Code Modulation) is primarily used to determine whether a specific IP address is governed by sending a packet to the specified address and waits for a reply. Common network protocols responsible for the presentation and formatting of data for transferors the medium include...file server's net work adapter Others are the Internetwork Packet Exchange (IPX) protocol or the Internet Protocol (IP). It functions by sets of the Transmission Control Protocol/Internet Protocol (TCP/IP) suite, forwards packets from file server memory to communicate with Collision ...
... Protocol PCM (Pulse Code Modulation) is primarily used to determine whether a specific IP address is governed by sending a packet to the specified address and waits for a reply. Common network protocols responsible for the presentation and formatting of data for transferors the medium include...file server's net work adapter Others are the Internetwork Packet Exchange (IPX) protocol or the Internet Protocol (IP). It functions by sets of the Transmission Control Protocol/Internet Protocol (TCP/IP) suite, forwards packets from file server memory to communicate with Collision ...
User's Guide
Page 103
... used transport protocol that are separated by all access methods. Transceivers can be used to join a segment that performs a specific task. A wide-area network consists of groups of interconnected computers that connects diverse computers of various transmission methods. T (TCP/IP) Transceiver U UDP User... Name Utility UTP W WAN WEP Transmission Control Protocol/Internet Protocol is a widely used as the basic security protocol in Wi-Fi networks, which secures data transmissions using 64-bit or 128-bit encryption. - 102 - It was developed...
... used transport protocol that are separated by all access methods. Transceivers can be used to join a segment that performs a specific task. A wide-area network consists of groups of interconnected computers that connects diverse computers of various transmission methods. T (TCP/IP) Transceiver U UDP User... Name Utility UTP W WAN WEP Transmission Control Protocol/Internet Protocol is a widely used as the basic security protocol in Wi-Fi networks, which secures data transmissions using 64-bit or 128-bit encryption. - 102 - It was developed...
User's Guide
Page 104
... and IEEE 802.1X-based authentication, which are required to improve the security of Wi-Fi networks, replacing the current WEP standard. Wi-Fi Protected Access 2, the latest security specification that provides greater data protection and network access control for workstations that use DOS. WPA (Wi-Fi Protected Access ) is a graphical user interface...
... and IEEE 802.1X-based authentication, which are required to improve the security of Wi-Fi networks, replacing the current WEP standard. Wi-Fi Protected Access 2, the latest security specification that provides greater data protection and network access control for workstations that use DOS. WPA (Wi-Fi Protected Access ) is a graphical user interface...
User's Guide
Page 108
... General Public License ("GPL") or GNU Lesser General Public License ("LGPL"). TRENDnet does not provide technical support for specific terms of the developers. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for the desired TRENDnet product to access to http://www.gnu.org/licenses/gpl.txt or...
... General Public License ("GPL") or GNU Lesser General Public License ("LGPL"). TRENDnet does not provide technical support for specific terms of the developers. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for the desired TRENDnet product to access to http://www.gnu.org/licenses/gpl.txt or...