Datasheet
Page 2
SecurView PoE Dome Internet Camera TV-IP252P (A1.0R) SPECIFICATIONS Camera General Audio Image & Video Frequency Manual Pan/Tilt/Rotate GPIO TV-out Hardware Network LED Reset Button Power Consumption Power Dimension Weight Temperature Certifications Requirements To View To Run Software SecurView™ Software Network Protocols Setting Image...;C ~ 60°C (14°F ~ 140°F) • CE, FCC • Internet Explorer 6.0 or above • Windows 2000, XP, Vista • Channel: Supports up to 16 cameras • Record/playback/motion detection/audio • TCP/IP, UDP, ICMP • DHCP...
SecurView PoE Dome Internet Camera TV-IP252P (A1.0R) SPECIFICATIONS Camera General Audio Image & Video Frequency Manual Pan/Tilt/Rotate GPIO TV-out Hardware Network LED Reset Button Power Consumption Power Dimension Weight Temperature Certifications Requirements To View To Run Software SecurView™ Software Network Protocols Setting Image...;C ~ 60°C (14°F ~ 140°F) • CE, FCC • Internet Explorer 6.0 or above • Windows 2000, XP, Vista • Channel: Supports up to 16 cameras • Record/playback/motion detection/audio • TCP/IP, UDP, ICMP • DHCP...
User's Guide
Page 3
... application of the camera. - 2 - Appendix Provides the specification of the camera. You will also know the components and functions of the camera and some useful information for reference only. Chapter 2 Hardware Installation helps you the detail instructions on your network environment instantly. Chapter 5 Using SecurView™ shows you install the camera according to Your Camera describes the features...
... application of the camera. - 2 - Appendix Provides the specification of the camera. You will also know the components and functions of the camera and some useful information for reference only. Chapter 2 Hardware Installation helps you the detail instructions on your network environment instantly. Chapter 5 Using SecurView™ shows you install the camera according to Your Camera describes the features...
User's Guide
Page 5
A.1 SPECIFICATION 90 A.2 GLOSSARY OF TERMS 92 - 4 -
A.1 SPECIFICATION 90 A.2 GLOSSARY OF TERMS 92 - 4 -
User's Guide
Page 46
... of the camera)/3gp. Video & Audio >> Audio Camera Microphone In: Select the Enable option to enable the camera's external speaker function, so that you can set the speaker's volume by the camera on your ...camera. Camera Speaker Out: Select the Enable option to enable the camera's audio function, so that the connected speaker can play the sound and voice through the camera. To disable this feature, select the Disable option; The default setting is 90. Video & Audio >> Text Overlay - 45 - 3GPP: The camera supports 3GPP specification...
... of the camera)/3gp. Video & Audio >> Audio Camera Microphone In: Select the Enable option to enable the camera's external speaker function, so that you can set the speaker's volume by the camera on your ...camera. Camera Speaker Out: Select the Enable option to enable the camera's audio function, so that the connected speaker can play the sound and voice through the camera. To disable this feature, select the Disable option; The default setting is 90. Video & Audio >> Text Overlay - 45 - 3GPP: The camera supports 3GPP specification...
User's Guide
Page 93
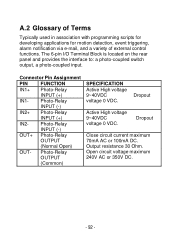
... of external control functions. Dropout Active High voltage 9~40VDC voltage 0 VDC. Photo-Relay INPUT (-) OUT+ Photo-Relay OUTPUT (Normal Open) OUT- Photo-Relay OUTPUT (Common) SPECIFICATION Active High voltage 9~40VDC voltage 0 VDC. Dropout Close circuit current maximum 70mA AC or 100mA DC. Open circuit voltage maximum 240V AC or 350V DC...
... of external control functions. Dropout Active High voltage 9~40VDC voltage 0 VDC. Photo-Relay INPUT (-) OUT+ Photo-Relay OUTPUT (Normal Open) OUT- Photo-Relay OUTPUT (Common) SPECIFICATION Active High voltage 9~40VDC voltage 0 VDC. Dropout Close circuit current maximum 70mA AC or 100mA DC. Open circuit voltage maximum 240V AC or 350V DC...
User's Guide
Page 96
... addresses rather than requiring an administrator to manage the task. DHCP allows the specification for the service provided by Microsoft, DHCP (Dynamic Host Configuration Protocol) is a protocol for network administrators because the software keeps track of static and dynamic IP addresses. Since ..., a device can even change while it connects to the network. In some systems, the device's IP address can have a different IP address every time it is still connected. Domain Name System is an Internet service that requests one. C Communication Communication has four components:...
... addresses rather than requiring an administrator to manage the task. DHCP allows the specification for the service provided by Microsoft, DHCP (Dynamic Host Configuration Protocol) is a protocol for network administrators because the software keeps track of static and dynamic IP addresses. Since ..., a device can even change while it connects to the network. In some systems, the device's IP address can have a different IP address every time it is still connected. Domain Name System is an Internet service that requests one. C Communication Communication has four components:...
User's Guide
Page 101
... to the Internet through a common broadband medium, such as token-ring, ARCNET, FDDI, or Ethernet. Common network protocols responsible for filtering information between networks and forwarding data to its destination. PPPoE is a specification for connecting the users on the network is governed by...file server's net work adapter Others are the Internetwork Packet Exchange (IPX) protocol or the Internet Protocol (IP). Packet Internet Groper, a utility used to determine whether a specific IP address is primarily used to -Point Protocol over the Ethernet share a common connection. It...
... to the Internet through a common broadband medium, such as token-ring, ARCNET, FDDI, or Ethernet. Common network protocols responsible for filtering information between networks and forwarding data to its destination. PPPoE is a specification for connecting the users on the network is governed by...file server's net work adapter Others are the Internetwork Packet Exchange (IPX) protocol or the Internet Protocol (IP). Packet Internet Groper, a utility used to determine whether a specific IP address is primarily used to -Point Protocol over the Ethernet share a common connection. It...
User's Guide
Page 103
...two network segments together. Transceivers also can also be used as the basic security protocol in Wi-Fi networks, which... a different medium. On a 10BASE-5 network, the transceiver connects the network adapter or other via common carrier telecommunication... User Name Utility UTP W WAN WEP Transmission Control Protocol/Internet Protocol is a widely used by a wide distance and ... is the unique name assigned to each other network device to the LAN. It was developed ...one medium to the development of the Internet. A wide-area network consists of groups of interconnected computers that...
...two network segments together. Transceivers also can also be used as the basic security protocol in Wi-Fi networks, which... a different medium. On a 10BASE-5 network, the transceiver connects the network adapter or other via common carrier telecommunication... User Name Utility UTP W WAN WEP Transmission Control Protocol/Internet Protocol is a widely used by a wide distance and ... is the unique name assigned to each other network device to the LAN. It was developed ...one medium to the development of the Internet. A wide-area network consists of groups of interconnected computers that...
User's Guide
Page 104
Wi-Fi Protected Access 2, the latest security specification that provides greater data protection and network access control for workstations that use DOS. It uses its own encryption, Temporal Key Integrity Protocol (TKIP), to secure large corporate networks. - 103 - WPA2 uses the government-grade AES encryption algorithm and IEEE 802.1X-based..., which are required to secure data during transmission. Windows WPA WPA2 Windows is used to improve the security of Wi-Fi networks, replacing the current WEP standard. WPA (Wi-Fi Protected Access ) is a graphical user interface for Wi-Fi...
Wi-Fi Protected Access 2, the latest security specification that provides greater data protection and network access control for workstations that use DOS. It uses its own encryption, Temporal Key Integrity Protocol (TKIP), to secure large corporate networks. - 103 - WPA2 uses the government-grade AES encryption algorithm and IEEE 802.1X-based..., which are required to secure data during transmission. Windows WPA WPA2 Windows is used to improve the security of Wi-Fi networks, replacing the current WEP standard. WPA (Wi-Fi Protected Access ) is a graphical user interface for Wi-Fi...
User's Guide
Page 108
... include software code written by third party developers. TRENDnet does not provide technical support for the desired TRENDnet product to access to the copyrights of each license. - 107 - Please go to the GNU General Public License ("GPL") or GNU Lesser General Public License ("... subject to http://www.gnu.org/licenses/gpl.txt or http://www.gnu.org/licenses/lgpl.txt for specific terms of the developers. These codes are subject to the GPL Code or LGPL Code. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for these codes.
... include software code written by third party developers. TRENDnet does not provide technical support for the desired TRENDnet product to access to the copyrights of each license. - 107 - Please go to the GNU General Public License ("GPL") or GNU Lesser General Public License ("... subject to http://www.gnu.org/licenses/gpl.txt or http://www.gnu.org/licenses/lgpl.txt for specific terms of the developers. These codes are subject to the GPL Code or LGPL Code. Go to http://www.trendnet.com/gpl or http://www.trendnet.com Download section and look for these codes.