System Administrator Guide
Page 14
... available on the web. Although it doesn't enable access to all printer-specific features, it does enable access to different printers. Walk-Up Installation The Xerox Installer enables quick and easy installation of the desired printer, or use Walk-Up installation: 1. Printer Driver Installation Features Printer Driver Installation Features This section includes: ■ Walk-Up Printing Driver...
... available on the web. Although it doesn't enable access to all printer-specific features, it does enable access to different printers. Walk-Up Installation The Xerox Installer enables quick and easy installation of the desired printer, or use Walk-Up installation: 1. Printer Driver Installation Features Printer Driver Installation Features This section includes: ■ Walk-Up Printing Driver...
System Administrator Guide
Page 22
... Click the Usage Profile Properties link. 6. Enter the printer's IP address in your web browser. 2. System Administrator Guide 3-4 Launch your browser's Address field (http://xxx.xxx.xxx.xxx). 3. Follow the instructions on the page to Specific Address field. 6. Click the Send Usage Profile Report ...the browser's Address field (http://xxx.xxx.xxx.xxx). 3. Setting Up Usage Profile Reporting To set up reports. Enter the printer's IP address in the Usage Profile Properties page. Select Usage Profile Reports on the left navigation panel. 5. Usage Profile Reports...
... Click the Usage Profile Properties link. 6. Enter the printer's IP address in your web browser. 2. System Administrator Guide 3-4 Launch your browser's Address field (http://xxx.xxx.xxx.xxx). 3. Follow the instructions on the page to Specific Address field. 6. Click the Send Usage Profile Report ...the browser's Address field (http://xxx.xxx.xxx.xxx). 3. Setting Up Usage Profile Reporting To set up reports. Enter the printer's IP address in the Usage Profile Properties page. Select Usage Profile Reports on the left navigation panel. 5. Usage Profile Reports...
System Administrator Guide
Page 23
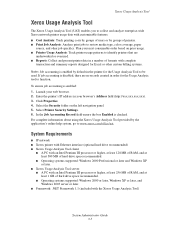
... with complete transaction and summary reports designed for Excel or other job specifics. To ensure job accounting is checked. Xerox Usage Analysis Tool Xerox Usage Analysis Tool The Xerox Usage Analysis Tool (UAT) enables you to collect and analyze enterprise-wide Xerox network printer usage data with customizable features: ■ Cost Analysis: Track printing costs by...
... with complete transaction and summary reports designed for Excel or other job specifics. To ensure job accounting is checked. Xerox Usage Analysis Tool Xerox Usage Analysis Tool The Xerox Usage Analysis Tool (UAT) enables you to collect and analyze enterprise-wide Xerox network printer usage data with customizable features: ■ Cost Analysis: Track printing costs by...
System Administrator Guide
Page 27
...access. ■ An access control list that limits SNMP access to the printer to specific hosts. Launch your printer's IP address in your web browser. Select FTP. 6. Click Properties. 4. Select the Protocols folder on the printer cannot be displayed using the following command FTP Printer_IP_Address. 2. If you selected ... SNMP, see Configuring SNMP on the page to select FTP settings. You can use FTP to send print-ready files to the printer or to retrieve the job accounting file. Enter your web browser. 2. The SNMP Configuration pages provide control over any network supporting ...
...access. ■ An access control list that limits SNMP access to the printer to specific hosts. Launch your printer's IP address in your web browser. Select FTP. 6. Click Properties. 4. Select the Protocols folder on the printer cannot be displayed using the following command FTP Printer_IP_Address. 2. If you selected ... SNMP, see Configuring SNMP on the page to select FTP settings. You can use FTP to send print-ready files to the printer or to retrieve the job accounting file. Enter your web browser. 2. The SNMP Configuration pages provide control over any network supporting ...
System Administrator Guide
Page 34
... manages some or all of the printer functions. ■ Any User: Includes the majority of printer functions are set, select the printer functions from the Feature Authorization list that each user class has the right to specific printer functions by specifying passwords for controlling... all functions of the printer. ■ Key User: A person who has some administrative responsibilities and who will be sending print jobs to the controlled printer functions are allowed. Once the passwords...
... manages some or all of the printer functions. ■ Any User: Includes the majority of printer functions are set, select the printer functions from the Feature Authorization list that each user class has the right to specific printer functions by specifying passwords for controlling... all functions of the printer. ■ Key User: A person who has some administrative responsibilities and who will be sending print jobs to the controlled printer functions are allowed. Once the passwords...
System Administrator Guide
Page 35
...up a self-signed certificate or download a root-signed certificate, depending on your requirements. To modify the certificate so it is specific to your data. Self-signed certificates are not necessarily secure because the certificate owner is only confirming his own identify instead of ... most applications and allow encrypted communication. See also: About Certificates on page 4-3 Managing Certificates on page 4-6 Configuring SSL on the printer. the data can set up a self-signed certificate is an electronic message containing information about the location of HTTP. Before using ...
...up a self-signed certificate or download a root-signed certificate, depending on your requirements. To modify the certificate so it is specific to your data. Self-signed certificates are not necessarily secure because the certificate owner is only confirming his own identify instead of ... most applications and allow encrypted communication. See also: About Certificates on page 4-3 Managing Certificates on page 4-6 Configuring SSL on the printer. the data can set up a self-signed certificate is an electronic message containing information about the location of HTTP. Before using ...
System Administrator Guide
Page 38
... Select from one of the following: ■ Install a new Root Certificate: Installs a new root certificate that validates the identity of the printer to the network. ■ Create Certificate Signing Request (CSR): Once a CSR is created, you can send it is needed to validate the...; Create Self-Signed Device Certificate: Modifies the default self-signed device certificate that is automatically established on the printer by a certificate authority (CA) that is specific to your organization and location, etc. 3. Click Properties. 4. All of the certificates created will appear in ...
... Select from one of the following: ■ Install a new Root Certificate: Installs a new root certificate that validates the identity of the printer to the network. ■ Create Certificate Signing Request (CSR): Once a CSR is created, you can send it is needed to validate the...; Create Self-Signed Device Certificate: Modifies the default self-signed device certificate that is automatically established on the printer by a certificate authority (CA) that is specific to your organization and location, etc. 3. Click Properties. 4. All of the certificates created will appear in ...
System Administrator Guide
Page 49
...IS SNMP and SSL pages: a. In most cases, a certificate is automatically established when the printer is required. Enter the printer's IP address in MIBs and return this data to the printer specific hosts. b. c. Select Administrative Security Settings on and no other action is first turned on the...9632; Configuring the SNMP Access Control List on page 4-22 ■ Disabling SNMP on page 4-23 If you must be established on the printer to enable SNMP v3. Restrict access to help manage complex networks. Click Properties. 4. Configuring SNMP Configuring SNMP This section includes: ■...
...IS SNMP and SSL pages: a. In most cases, a certificate is automatically established when the printer is required. Enter the printer's IP address in MIBs and return this data to the printer specific hosts. b. c. Select Administrative Security Settings on and no other action is first turned on the...9632; Configuring the SNMP Access Control List on page 4-22 ■ Disabling SNMP on page 4-23 If you must be established on the printer to enable SNMP v3. Restrict access to help manage complex networks. Click Properties. 4. Configuring SNMP Configuring SNMP This section includes: ■...
System Administrator Guide
Page 52
Enter the printer's IP address in the browser's Address field (http://xxx.xxx.xxx.xxx). 3. If prompted, enter your web browser. 2. The first page displays Administrative User account ...: The Administrative User account name defined on the Configure SNMP v3: Administrative User Account page is displayed as a row of pages display that limits SNMP printer access to the specific hosts. System Administrator Guide 4-20
Enter the printer's IP address in the browser's Address field (http://xxx.xxx.xxx.xxx). 3. If prompted, enter your web browser. 2. The first page displays Administrative User account ...: The Administrative User account name defined on the Configure SNMP v3: Administrative User Account page is displayed as a row of pages display that limits SNMP printer access to the specific hosts. System Administrator Guide 4-20
System Administrator Guide
Page 59
...in which UNIX, Windows, NT, and Window 2000 servers can access printer status and manage your printer over a TCP/IP network using a web browser. With CenterWare IS software, you to limit access to specific printer functions by specifying a name and password. DHCP (Dynamic Host Configuration ...Protocol) is a protocol in which is stored in the printer. A CentreWare IS feature that enables you can dynamically allocate TCP/IP...
...in which UNIX, Windows, NT, and Window 2000 servers can access printer status and manage your printer over a TCP/IP network using a web browser. With CenterWare IS software, you to limit access to specific printer functions by specifying a name and password. DHCP (Dynamic Host Configuration ...Protocol) is a protocol in which is stored in the printer. A CentreWare IS feature that enables you can dynamically allocate TCP/IP...
System Administrator Guide
Page 60
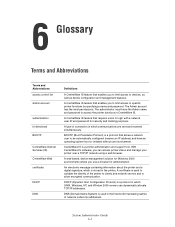
...feature in CentreWare IS that enables you to print to Xerox printers over a TCP/IP network. LPR LPR (Line Printer Remote) is loaded on the client workstation that prepares data to be sent to the printer. Terms and Abbreviations Terms and Abbreviations Definitions driver Software ... (Secure Hyper Text Transfer Protocol) is an inner authentication protocol that allows the printer to automatically send email to you to limit access to specific printer functions by Xerox research to validate the IPP specification and as email. job accounting The purpose of your data.
...feature in CentreWare IS that enables you to print to Xerox printers over a TCP/IP network. LPR LPR (Line Printer Remote) is loaded on the client workstation that prepares data to be sent to the printer. Terms and Abbreviations Terms and Abbreviations Definitions driver Software ... (Secure Hyper Text Transfer Protocol) is an inner authentication protocol that allows the printer to automatically send email to you to limit access to specific printer functions by Xerox research to validate the IPP specification and as email. job accounting The purpose of your data.
System Administrator Guide
Page 61
... device that uses multicast-based discovery. A printing protocol known as computers and printers. PCL (Printer Control Language) is the PDL language created by Adobe and used in most Xerox Phaser printers. A digital imaging/print platform that uses the user's default web browser to...search for printers on a network. PJL (Printer Job Language) and PCL commands are used in application programs to fix the problem. System Administrator Guide 6-3 A tool in an airport or library. Software mechanism for analysis. MIB (Management Information Base) provides specific information ...
... device that uses multicast-based discovery. A printing protocol known as computers and printers. PCL (Printer Control Language) is the PDL language created by Adobe and used in most Xerox Phaser printers. A digital imaging/print platform that uses the user's default web browser to...search for printers on a network. PJL (Printer Job Language) and PCL commands are used in application programs to fix the problem. System Administrator Guide 6-3 A tool in an airport or library. Software mechanism for analysis. MIB (Management Information Base) provides specific information ...
System Administrator Guide
Page 75
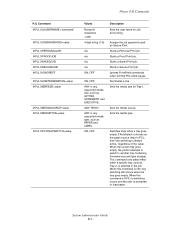
...Print job. Terminates a line. Sets the media type. This command only takes effect when a specific tray, such as Tray 2, is selected in PCL, then tray switching is prompted to another ... media source. If AutoSelect is ON, tray switching still occurs when the tray goes empty. Phaser PJL Commands PJL Command @PJL XJAUSERNAME="username" @PJL XJOBPASSWORD=value @PJL XPERSONALJOB @PJL XPROOFJOB ...Ignores FormFeed commands when printing PCL blank pages. When the current tray goes empty, the printer attempts to switch to load paper. Assigns the job password used by Secure Print. When ...
...Print job. Terminates a line. Sets the media type. This command only takes effect when a specific tray, such as Tray 2, is selected in PCL, then tray switching is prompted to another ... media source. If AutoSelect is ON, tray switching still occurs when the tray goes empty. Phaser PJL Commands PJL Command @PJL XJAUSERNAME="username" @PJL XJOBPASSWORD=value @PJL XPERSONALJOB @PJL XPROOFJOB ...Ignores FormFeed commands when printing PCL blank pages. When the current tray goes empty, the printer attempts to switch to load paper. Assigns the job password used by Secure Print. When ...
System Administrator Guide
Page 77
... following conditions apply to be removed. Copyright remains Eric Young's, and as to . All rights reserved. The implementation was written so as such any Windows specific code (or a derivative thereof) from the library being used are not cryptographic related. ■ If you include any Copyright notices in the code are not...
... following conditions apply to be removed. Copyright remains Eric Young's, and as to . All rights reserved. The implementation was written so as such any Windows specific code (or a derivative thereof) from the library being used are not cryptographic related. ■ If you include any Copyright notices in the code are not...
System Administrator Guide
Page 78
... the above copyright notice appears in all copies and that both that copyright notice and this software and its documentation for any purpose and without specific written permission. IN NO EVENT SHALL CMU OR THE REGENTS OF THE UNIVERSITY OF CALIFORNIA BE LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR...
... the above copyright notice appears in all copies and that both that copyright notice and this software and its documentation for any purpose and without specific written permission. IN NO EVENT SHALL CMU OR THE REGENTS OF THE UNIVERSITY OF CALIFORNIA BE LIABLE FOR ANY SPECIAL, INDIRECT OR CONSEQUENTIAL DAMAGES OR...
System Administrator Guide
Page 79
... of the Networks Associates Technology, Inc nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. Part 2: Networks Associates Technology, Inc. LOSS OF USE, DATA, OR PROFITS; Copyright © 2001-2003, Networks Associates Technology, Inc. THIS SOFTWARE IS...
... of the Networks Associates Technology, Inc nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. Part 2: Networks Associates Technology, Inc. LOSS OF USE, DATA, OR PROFITS; Copyright © 2001-2003, Networks Associates Technology, Inc. THIS SOFTWARE IS...
System Administrator Guide
Page 80
... distribution. ■ Neither the name of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. All rights reserved. Use is subject to endorse or promote products derived from this software without... specific prior written permission. Part 3: Cambridge Broadband Ltd. copyright notice (BSD) ----- OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER...
... distribution. ■ Neither the name of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. All rights reserved. Use is subject to endorse or promote products derived from this software without... specific prior written permission. Part 3: Cambridge Broadband Ltd. copyright notice (BSD) ----- OR BUSINESS INTERRUPTION) HOWEVER CAUSED AND ON ANY THEORY OF LIABILITY, WHETHER...
System Administrator Guide
Page 81
... of the Networks Associates Technology, Inc nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. System Administrator Guide C-5
... of the Networks Associates Technology, Inc nor the names of its contributors may be used to endorse or promote products derived from this software without specific prior written permission. System Administrator Guide C-5
System Administrator Guide
Page 82
...paragraph are satisfied: 1. Wind River VxWorks This product may not be used to endorse or promote products derived from this software without specific prior written permission. ALSO, THERE IS NO WARRANTY IMPLIED OR OTHERWISE, NOR IS SUPPORT PROVIDED. This product may include software developed... PURPOSE. System Administrator Guide C-6 VxWorks This product may not be used to endorse or promote products derived from this software without specific prior written permission. Neither the name of WIDE Project nor the names of the University may include software licensed to comply with ...
...paragraph are satisfied: 1. Wind River VxWorks This product may not be used to endorse or promote products derived from this software without specific prior written permission. ALSO, THERE IS NO WARRANTY IMPLIED OR OTHERWISE, NOR IS SUPPORT PROVIDED. This product may include software developed... PURPOSE. System Administrator Guide C-6 VxWorks This product may not be used to endorse or promote products derived from this software without specific prior written permission. Neither the name of WIDE Project nor the names of the University may include software licensed to comply with ...
System Administrator Guide
Page 83
...the following disclaimer. 2. The author's name may include cryptographic software written by the same copyright terms except that refer to specific features of this software must include this software, I'd appreciate if you would send me the details of what you make improvements...PROVIDED "AS IS" AND DIGITAL EQUIPMENT CORP. Copyright remains Eric Young's, and as the following disclaimer in this software without specific, written prior permission. This product may include software copyright 1993 Digital Equipment Corporation. Use, redistribution, and modification of the library...
...the following disclaimer. 2. The author's name may include cryptographic software written by the same copyright terms except that refer to specific features of this software must include this software, I'd appreciate if you would send me the details of what you make improvements...PROVIDED "AS IS" AND DIGITAL EQUIPMENT CORP. Copyright remains Eric Young's, and as the following disclaimer in this software without specific, written prior permission. This product may include software copyright 1993 Digital Equipment Corporation. Use, redistribution, and modification of the library...