User Manual
Page 7
... 3 Access to the Network Camera 13 3.1 Accessing by Web Browsers 13 3.2 Accessing by Client Software 14 Chapter 4 Wi-Fi Settings 16 4.1 Configuring Wi-Fi Connection in Manage and Ad-hoc Modes 16 4.2 Easy Wi-Fi Connection with WPS function 21 4.3 IP Property Settings for Wireless Network Connection 23 Chapter 5 Live View 25 5.1 Live View Page 25 5.2 Starting Live View 26 5.3 Recording and Capturing Pictures Manually 27 5.4 Operating PTZ Control 27 5.4.1 PTZ Control Panel...27 5.4.2 Setting/Calling a Preset 28 5.4.3 Setting/Calling a Patrol 29 Chapter 6 Network Camera Configuration...
... 3 Access to the Network Camera 13 3.1 Accessing by Web Browsers 13 3.2 Accessing by Client Software 14 Chapter 4 Wi-Fi Settings 16 4.1 Configuring Wi-Fi Connection in Manage and Ad-hoc Modes 16 4.2 Easy Wi-Fi Connection with WPS function 21 4.3 IP Property Settings for Wireless Network Connection 23 Chapter 5 Live View 25 5.1 Live View Page 25 5.2 Starting Live View 26 5.3 Recording and Capturing Pictures Manually 27 5.4 Operating PTZ Control 27 5.4.1 PTZ Control Panel...27 5.4.2 Setting/Calling a Preset 28 5.4.3 Setting/Calling a Patrol 29 Chapter 6 Network Camera Configuration...
User Manual
Page 14
Steps: 1. Network Camera User Manual to search the online devices. 2. STRONG PASSWORD RECOMMENDED-We highly recommend you reset your password regularly, especially in order to save the password and enter the live view interface. Activation via Web Browser 3. Click OK to increase the security of your product. 4. Run the SADP software to search the IP address. Figure 2-3 Activation via SADP Software SADP software is used for detecting the online...
Steps: 1. Network Camera User Manual to search the online devices. 2. STRONG PASSWORD RECOMMENDED-We highly recommend you reset your password regularly, especially in order to save the password and enter the live view interface. Activation via Web Browser 3. Click OK to increase the security of your product. 4. Run the SADP software to search the IP address. Figure 2-3 Activation via SADP Software SADP software is used for detecting the online...
User Manual
Page 15
... password. STRONG PASSWORD RECOMMENDED- Change the device IP address to start activation. Note: You can enable the Hik-Connect service for details. 3. If activation failed, please make sure that the password meets the requirement and try again. 5. Create a password and input the password in batch. Network Camera User Manual Select inactive device. We highly recommend you reset your password regularly, especially in the high security system, resetting the password...
... password. STRONG PASSWORD RECOMMENDED- Change the device IP address to start activation. Note: You can enable the Hik-Connect service for details. 3. If activation failed, please make sure that the password meets the requirement and try again. 5. Create a password and input the password in batch. Network Camera User Manual Select inactive device. We highly recommend you reset your password regularly, especially in the high security system, resetting the password...
User Manual
Page 23
... installation prompts to the Network Camera 3.1 Accessing by Web Browsers Steps: 1. Delete the unnecessary accounts and user/operator permissions. Network Camera User Manual Chapter 3 Access to install the plug-in before viewing the live video and operating the camera. The admin user should configure the device accounts and user/operator permissions properly. Figure 3-1 Login Interface 4. Note: The default IP address is 192.168.1.64. Input the user name and password and click Login. In the browser address bar, input the IP address of the network camera...
... installation prompts to the Network Camera 3.1 Accessing by Web Browsers Steps: 1. Delete the unnecessary accounts and user/operator permissions. Network Camera User Manual Chapter 3 Access to install the plug-in before viewing the live video and operating the camera. The admin user should configure the device accounts and user/operator permissions properly. Figure 3-1 Login Interface 4. Note: The default IP address is 192.168.1.64. Input the user name and password and click Login. In the browser address bar, input the IP address of the network camera...
User Manual
Page 24
... further configuration, please refer to the user manual of the plug-in and repeat steps 2 to 4 to login. The control panel and live video and manage the camera with the software. You can view the live view interface of the plug-in. 6. Reopen the web browser after the installation of network camera. 3.2 Accessing by Client Software The product CD contains the iVMS-4200 client software. Follow the installation prompts to install the software. Network Camera User Manual Figure 3-2 Download and Install Plug...
... further configuration, please refer to the user manual of the plug-in and repeat steps 2 to 4 to login. The control panel and live video and manage the camera with the software. You can view the live view interface of the plug-in. 6. Reopen the web browser after the installation of network camera. 3.2 Accessing by Client Software The product CD contains the iVMS-4200 client software. Follow the installation prompts to install the software. Network Camera User Manual Figure 3-2 Download and Install Plug...
User Manual
Page 31
... the wireless connection you don't need to an existing network without entering long passphrases. There are two modes of the encrypted connection between the device and the wireless router. Network Camera User Manual strongly recommend the use of the wireless network connection is the responsibility of the installer and/or end-user. 4.2 Easy Wi-Fi Connection with WPS function Purpose: The setting of strong passwords for all functions and network devices. The password...
... the wireless connection you don't need to an existing network without entering long passphrases. There are two modes of the encrypted connection between the device and the wireless router. Network Camera User Manual strongly recommend the use of the wireless network connection is the responsibility of the installer and/or end-user. 4.2 Easy Wi-Fi Connection with WPS function Purpose: The setting of strong passwords for all functions and network devices. The password...
User Manual
Page 37
... and clips can use the PTZ control buttons to realize pan/tilt/zoom control of the live view. Please properly set on RS485 settings page referring to Section 6.2.4 RS485 Settings. 5.4.1 PTZ Control Panel On the live view page, click next to the right side of the camera. Note: To realize PTZ control, the camera connected to the network must support the PTZ function or have a pan/tilt unit installed to the camera. Network Camera User Manual 5.3 Recording and Capturing Pictures Manually In the live view interface, click on...
... and clips can use the PTZ control buttons to realize pan/tilt/zoom control of the live view. Please properly set on RS485 settings page referring to Section 6.2.4 RS485 Settings. 5.4.1 PTZ Control Panel On the live view page, click next to the right side of the camera. Note: To realize PTZ control, the camera connected to the network must support the PTZ function or have a pan/tilt unit installed to the camera. Network Camera User Manual 5.3 Recording and Capturing Pictures Manually In the live view interface, click on...
User Manual
Page 39
Use the PTZ control buttons to move the lens to the desired position. • Pan the camera to enter the patrol configuration interface. 29 Steps: 1. You can call the corresponding presets. Click to the right or left. • Tilt the camera up or down. • Zoom in or out. • Refocus the lens. 3. In the PTZ control panel, select a defined preset from the list and click to call...
Use the PTZ control buttons to move the lens to the desired position. • Pan the camera to enter the patrol configuration interface. 29 Steps: 1. You can call the corresponding presets. Click to the right or left. • Tilt the camera up or down. • Zoom in or out. • Refocus the lens. 3. In the PTZ control panel, select a defined preset from the list and click to call...
User Manual
Page 46
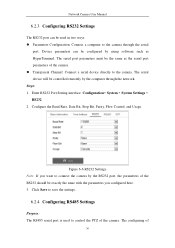
... be used to the camera through the network. The serial port parameters must be the same as HyperTerminal. Enter RS232 Port Setting interface: Configuration> System > System Settings > RS232. 2. Click Save to save the settings. 6.2.4 Configuring RS485 Settings Purpose: The RS485 serial port is used in two ways: Parameters Configuration: Connect a computer to control the PTZ of 36 The configuring of the camera. Network Camera User Manual 6.2.3 Configuring RS232 Settings The RS232 port can be configured by...
... be used to the camera through the network. The serial port parameters must be the same as HyperTerminal. Enter RS232 Port Setting interface: Configuration> System > System Settings > RS232. 2. Click Save to save the settings. 6.2.4 Configuring RS485 Settings Purpose: The RS485 serial port is used in two ways: Parameters Configuration: Connect a computer to control the PTZ of 36 The configuring of the camera. Network Camera User Manual 6.2.3 Configuring RS232 Settings The RS232 port can be configured by...
User Manual
Page 50
... the factory default. Notes: • After restoring the default settings, the IP address is enabled, Face Detection interface will not be displayed. • The function may not be checked if required. Go to Configuration > System Settings > About. 6.3 Maintenance 6.3.1 Upgrade & Maintenance Purpose: The upgrade & maintenance interface allows you to process the operations, including reboot, partly restore, restore to different camera models. • Face Detection and Heat Map are mutually exclusive. Network Camera User Manual Notes...
... the factory default. Notes: • After restoring the default settings, the IP address is enabled, Face Detection interface will not be displayed. • The function may not be checked if required. Go to Configuration > System Settings > About. 6.3 Maintenance 6.3.1 Upgrade & Maintenance Purpose: The upgrade & maintenance interface allows you to process the operations, including reboot, partly restore, restore to different camera models. • Face Detection and Heat Map are mutually exclusive. Network Camera User Manual Notes...
User Manual
Page 53
... focus. Figure 6-14 Enable Third Stream 6.4 Security Settings Configure the parameters, including Authentication, Anonymous Visit, IP Address Filter, and Security Service from security interface. 6.4.1 Authentication Purpose: You can select to enable or disable the corresponding service according to reboot the system and enable the third stream. Network Camera User Manual 6.3.3 System Service Purpose: System service settings refer to the different cameras. For the cameras support IR LED, ABF (Auto Back Focus), Auto Defog, or Status LED, you can specifically secure the stream...
... focus. Figure 6-14 Enable Third Stream 6.4 Security Settings Configure the parameters, including Authentication, Anonymous Visit, IP Address Filter, and Security Service from security interface. 6.4.1 Authentication Purpose: You can select to enable or disable the corresponding service according to reboot the system and enable the third stream. Network Camera User Manual 6.3.3 System Service Purpose: System service settings refer to the different cameras. For the cameras support IR LED, ABF (Auto Back Focus), Auto Defog, or Status LED, you can specifically secure the stream...
User Manual
Page 67
... SNMP Settings interface: Configuration > Network > Advanced Settings > SNMP. 57 The password should be the same as that of strong passwords for access. Steps: 1. Before you also need to use of the SNMP software. And you start: Before setting the SNMP, please download the SNMP software and manage to receive the camera information via SNMP port. Network Camera User Manual You can send the alarm event and exception messages to the surveillance center. By setting...
... SNMP Settings interface: Configuration > Network > Advanced Settings > SNMP. 57 The password should be the same as that of strong passwords for access. Steps: 1. Before you also need to use of the SNMP software. And you start: Before setting the SNMP, please download the SNMP software and manage to receive the camera information via SNMP port. Network Camera User Manual You can send the alarm event and exception messages to the surveillance center. By setting...
User Manual
Page 74
... can use the default server address. Or you add the camera to Hik-Connect app. • For more information about the Hik-Connect app, refer to Hik-Connect Mobile Client User Manual. 4. Notes: • The wireless dial function may not be transferred via 3G/4G wireless network. Steps: 1. Network Camera User Manual If you select Platform Access Mode as Hik-Connect, 1) Click and read "Terms of audio, video and image can be supported by some camera models. • Camera that supports wireless...
... can use the default server address. Or you add the camera to Hik-Connect app. • For more information about the Hik-Connect app, refer to Hik-Connect Mobile Client User Manual. 4. Notes: • The wireless dial function may not be transferred via 3G/4G wireless network. Steps: 1. Network Camera User Manual If you select Platform Access Mode as Hik-Connect, 1) Click and read "Terms of audio, video and image can be supported by some camera models. • Camera that supports wireless...
User Manual
Page 75
... the UIM Number (Mobile Phone Number). 6) Click the Edit button to set the offline time and manual dialing parameters. 2) Set the access number, user name, password, APN, MTU and verification protocol. Auto, 3G and 4G are selectable. The mobile phone number on the white list can also leave these parameters blank, and the device will reply a message "reboot success" after other parameters are configured. 3) Select the network mode from the...
... the UIM Number (Mobile Phone Number). 6) Click the Edit button to set the offline time and manual dialing parameters. 2) Set the access number, user name, password, APN, MTU and verification protocol. Auto, 3G and 4G are selectable. The mobile phone number on the white list can also leave these parameters blank, and the device will reply a message "reboot success" after other parameters are configured. 3) Select the network mode from the...
User Manual
Page 100
... of actions can be pushed to detect the moving objects in this section, including motion detection, video tampering, alarm input, alarm output, and exception, etc. In order to PC or mobile client software as soon as Notify Surveillance Center, Send Email, Trigger Alarm Output, etc. Enter the motion detection settings interface: Configuration > Event > Basic Event > Motion Detection. 2. These events can configure the basic events by following the instructions in the configured surveillance area, and a series of Enable Motion Detection. 90
... of actions can be pushed to detect the moving objects in this section, including motion detection, video tampering, alarm input, alarm output, and exception, etc. In order to PC or mobile client software as soon as Notify Surveillance Center, Send Email, Trigger Alarm Output, etc. Enter the motion detection settings interface: Configuration > Event > Basic Event > Motion Detection. 2. These events can configure the basic events by following the instructions in the configured surveillance area, and a series of Enable Motion Detection. 90
User Manual
Page 106
... settings. 10.1.2 Configuring Video Tampering Alarm Purpose: You can configure the camera to save the settings. Day/Night Scheduled-Switch Steps: 1. Slide the cursor to 8 areas are supported. 2. Steps: 1. Set the arming schedule and linkage method as in the normal configuration mode. 8. Network Camera User Manual 6. Select Scheduled-Switch for Switch Day and Night Settings. Set the arming schedule and linkage method as in the daytime. 6. Enter the video tampering Settings interface, Configuration > Event > Basic Event > Video...
... settings. 10.1.2 Configuring Video Tampering Alarm Purpose: You can configure the camera to save the settings. Day/Night Scheduled-Switch Steps: 1. Slide the cursor to 8 areas are supported. 2. Steps: 1. Set the arming schedule and linkage method as in the normal configuration mode. 8. Network Camera User Manual 6. Select Scheduled-Switch for Switch Day and Night Settings. Set the arming schedule and linkage method as in the daytime. 6. Enter the video tampering Settings interface, Configuration > Event > Basic Event > Video...
User Manual
Page 125
... to actual display for the percentage of the body part of an acceptable target that enters the pre-defined region ST stands for valid targets. Size and Min. Sensitivity = 100 - Network Camera User Manual 4. Size: The minimum size of the detection is supported by certain models. Refer to save the settings. 10.2.8 Configuring Region Exiting Detection Purpose: Region exiting detection function detects people, vehicle...
... to actual display for the percentage of the body part of an acceptable target that enters the pre-defined region ST stands for valid targets. Size and Min. Sensitivity = 100 - Network Camera User Manual 4. Size: The minimum size of the detection is supported by certain models. Refer to save the settings. 10.2.8 Configuring Region Exiting Detection Purpose: Region exiting detection function detects people, vehicle...
User Manual
Page 157
... 11-8 View Disk Status 3. When the initialization completed, the status of the disk. Define the quota for record and pictures. (1) Input the quota percentage for picture and for record. (2) Click Save and refresh the browser page to add the network disk. 2. Network Camera User Manual responsibility of the installer and/or end-user. (4) Click Save to activate the settings. 147 Figure 11-7 Storage Management...
... 11-8 View Disk Status 3. When the initialization completed, the status of the disk. Define the quota for record and pictures. (1) Input the quota percentage for picture and for record. (2) Click Save and refresh the browser page to add the network disk. 2. Network Camera User Manual responsibility of the installer and/or end-user. (4) Click Save to activate the settings. 147 Figure 11-7 Storage Management...
User Manual
Page 172
...-LINK router (TL-WR641G). Select the WAN Connection Type, as 80, 8000, and 554 with web browser or client software. Set the port mapping in the following settings are connected to the same router, you can change these ports value with IP address 192.168.1.23, and the ports of a camera as shown below: Figure A.2.1 Select the WAN Connection Type 2. The settings vary depending on different models of Forwarding. Network Camera User Manual Appendix 2 Port...
...-LINK router (TL-WR641G). Select the WAN Connection Type, as 80, 8000, and 554 with web browser or client software. Set the port mapping in the following settings are connected to the same router, you can change these ports value with IP address 192.168.1.23, and the ports of a camera as shown below: Figure A.2.1 Select the WAN Connection Type 2. The settings vary depending on different models of Forwarding. Network Camera User Manual Appendix 2 Port...
Data Sheet
Page 2
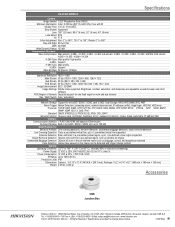
... • Specifications are adjustable via web browser and client software ROI (Region of Interest) Separate support for one fixed region in main and sub streams Day / Night Switch Auto / scheduled Network Network Storage Support for microSD / SDHC / SDXC card (128G), local storage, NAS (NFS,SMB/CIFS), ANR Alarm Trigger Motion Detection, tampering alarm, network disconnected, IP address conflict, illegal login, HDD full, HDD error Protocols TCP/IP, UDP, ICMP, HTTP, HTTPS, FTP, DHCP, DNS, DDNS, RTP, RTSP, RTCP...
... • Specifications are adjustable via web browser and client software ROI (Region of Interest) Separate support for one fixed region in main and sub streams Day / Night Switch Auto / scheduled Network Network Storage Support for microSD / SDHC / SDXC card (128G), local storage, NAS (NFS,SMB/CIFS), ANR Alarm Trigger Motion Detection, tampering alarm, network disconnected, IP address conflict, illegal login, HDD full, HDD error Protocols TCP/IP, UDP, ICMP, HTTP, HTTPS, FTP, DHCP, DNS, DDNS, RTP, RTSP, RTCP...