User Guide
Page 25
... terminal emulation program. 2) Set terminal parameters as follows: z Bits per second: 38,400 z Data bits: 8 z Parity: None z Stop bits: 1 z Flow control: None z Emulation: VT100 The specific procedure is as shown below. Figure 3-3 Connection description of the HyperTerminal Step2 Type the name of the HyperTerminal, refer to enter the HyperTerminal window. The...
... terminal emulation program. 2) Set terminal parameters as follows: z Bits per second: 38,400 z Data bits: 8 z Parity: None z Stop bits: 1 z Flow control: None z Emulation: VT100 The specific procedure is as shown below. Figure 3-3 Connection description of the HyperTerminal Step2 Type the name of the HyperTerminal, refer to enter the HyperTerminal window. The...
User Guide
Page 116
... traffic. For details, refer to enter the page shown in an Ethernet. With storm constrain enabled on a port, you can specify the system to control a specific type of traffic. z Shutdown: Shut down below the lower threshold. As the storm suppression function and the storm constrain function are mutually exclusive, do not...
... traffic. For details, refer to enter the page shown in an Ethernet. With storm constrain enabled on a port, you can specify the system to control a specific type of traffic. z Shutdown: Shut down below the lower threshold. As the storm suppression function and the storm constrain function are mutually exclusive, do not...
User Guide
Page 117
... configuration, as shown in Figure 1-1. z For network stability sake, set here is the interval used for measuring the average traffic sending and receiving rates over a specific interval. Configuring Storm Constrain Select Device > Storm Constrain from the interval set in the flow interval module, which is different from the navigation tree to...
... configuration, as shown in Figure 1-1. z For network stability sake, set here is the interval used for measuring the average traffic sending and receiving rates over a specific interval. Configuring Storm Constrain Select Device > Storm Constrain from the interval set in the flow interval module, which is different from the navigation tree to...
User Guide
Page 122
... notify the occurrence of packets. Event group The event group defines event indexes and controls the generation and notifications of the events triggered by RMON specifications (RFC 2819), the realized public MIB of the monitored variable is greater than or equal to collect traffic statistics on . It provides statistics about network...
... notify the occurrence of packets. Event group The event group defines event indexes and controls the generation and notifications of the events triggered by RMON specifications (RFC 2819), the realized public MIB of the monitored variable is greater than or equal to collect traffic statistics on . It provides statistics about network...
User Guide
Page 151
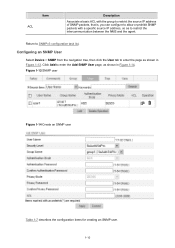
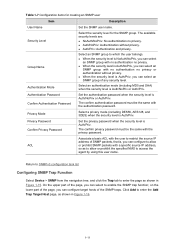
... Table 1-7 describes the configuration items for creating an SNMP user. 1-10 Item ACL Description Associate a basic ACL with the group to restrict the source IP address of SNMP packets, that is, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as shown in Figure 1-13. Click...
... Table 1-7 describes the configuration items for creating an SNMP user. 1-10 Item ACL Description Associate a basic ACL with the group to restrict the source IP address of SNMP packets, that is, you can configure to allow or prohibit SNMP packets with a specific source IP address, so as shown in Figure 1-13. Click...
User Guide
Page 152
.... Return to which the user belongs. The available security levels are: z NoAuth/NoPriv: No authentication no privacy or authentication without privacy. Associate a basic ACL with a specific source IP address, so as shown in Figure 1-16. 1-11 Select an authentication mode (including MD5 and SHA) when the security level is Auth/Priv...
.... Return to which the user belongs. The available security levels are: z NoAuth/NoPriv: No authentication no privacy or authentication without privacy. Associate a basic ACL with a specific source IP address, so as shown in Figure 1-16. 1-11 Select an authentication mode (including MD5 and SHA) when the security level is Auth/Priv...
User Guide
Page 225
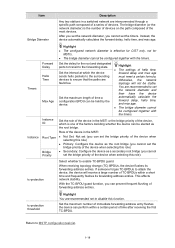
... threshold You are recommended not to the surrounding must meet a certain formula. Item Bridge Diameter Description Any two stations in a switched network are interconnected through a specific path composed of a series of time after receiving the first TC-BPDU. Set the delay for MSTIs. This affects network stability. automatically calculate the forward...
... threshold You are recommended not to the surrounding must meet a certain formula. Item Bridge Diameter Description Any two stations in a switched network are interconnected through a specific path composed of a series of time after receiving the first TC-BPDU. Set the delay for MSTIs. This affects network stability. automatically calculate the forward...
User Guide
Page 254
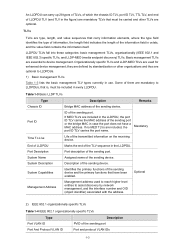
...Management address used for enhanced device management; Basic management TLVs are included, the port ID TLV carries the port name. Organizationally specific TLVs and LLDP-MED TLVs are optional. ID of the transmitted information on the receiving device. Mandatory Life of the sending port... enabled. Description of the sending device. LLDPDU TLVs fall into these categories: basic management TLVs, organizationally (IEEE 802.1 and IEEE 802.3) specific TLVs, and LLDP-MED (media endpoint discovery) TLVs. Some of them are type, length, and value sequences that have a MAC address...
...Management address used for enhanced device management; Basic management TLVs are included, the port ID TLV carries the port name. Organizationally specific TLVs and LLDP-MED TLVs are optional. ID of the transmitted information on the receiving device. Mandatory Life of the sending port... enabled. Description of the sending device. LLDPDU TLVs fall into these categories: basic management TLVs, organizationally (IEEE 802.1 and IEEE 802.3) specific TLVs, and LLDP-MED (media endpoint discovery) TLVs. Some of them are type, length, and value sequences that have a MAC address...
User Guide
Page 255
... name on the port Protocols supported on the port Currently, 3Com Switch 2900 supports receiving but not sending protocol identity TLVs. 3) IEEE 802.3 organizationally specific TLVs Table 1-5 IEEE 802.3 organizationally specific TLVs Type MAC/PHY Configuration/Status Power Via MDI Link Aggregation Maximum ...Firmware Revision Allows a MED endpoint to IEEE 802.3AF). LLDP-MED TLVs LLDP-MED TLVs provide multiple advanced applications for a specific set of the specific port, and the Layer 2 and Layer 3 priorities for voice over IP (VoIP), such as basic configuration, network policy ...
... name on the port Protocols supported on the port Currently, 3Com Switch 2900 supports receiving but not sending protocol identity TLVs. 3) IEEE 802.3 organizationally specific TLVs Table 1-5 IEEE 802.3 organizationally specific TLVs Type MAC/PHY Configuration/Status Power Via MDI Link Aggregation Maximum ...Firmware Revision Allows a MED endpoint to IEEE 802.3AF). LLDP-MED TLVs LLDP-MED TLVs provide multiple advanced applications for a specific set of the specific port, and the Layer 2 and Layer 3 priorities for voice over IP (VoIP), such as basic configuration, network policy ...
User Guide
Page 257
... can cause a requesting Cisco IP phone to send voice traffic untagged to your device, disabling your device to be transmitted and received. With this mechanism, a specific number of LLDP.
... can cause a requesting Cisco IP phone to send voice traffic untagged to your device, disabling your device to be transmitted and received. With this mechanism, a specific number of LLDP.
User Guide
Page 286
... on a member port, it to any port. z If the forwarding table entry exists and its aging timer expires. Upon hearing the IGMP group-specific query, the switch forwards it is receiving or expecting to receive multicast data for that group address. z If no hosts attached to the port are... for that multicast group, and performs the following to the port (in case it through the port that port. When the switch receives a group-specific IGMP leave group message on a member port before its aging timer expires, this means that the host just left the multicast group. Table 1-1 IGMP...
... on a member port, it to any port. z If the forwarding table entry exists and its aging timer expires. Upon hearing the IGMP group-specific query, the switch forwards it is receiving or expecting to receive multicast data for that group address. z If no hosts attached to the port are... for that multicast group, and performs the following to the port (in case it through the port that port. When the switch receives a group-specific IGMP leave group message on a member port before its aging timer expires, this means that the host just left the multicast group. Table 1-1 IGMP...
User Guide
Page 290
... traffic on the port. features configured on a member port of the aggregate group will not take effect for the port. Then, when receiving IGMP group-specific queries for that multicast group, the switch will fail to receive multicast data. If fast leave is attached to the entry. Click the plus sign...
... traffic on the port. features configured on a member port of the aggregate group will not take effect for the port. Then, when receiving IGMP group-specific queries for that multicast group, the switch will fail to receive multicast data. If fast leave is attached to the entry. Click the plus sign...
User Guide
Page 317
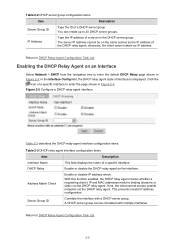
...the DHCP relay agent. Return to enter the page shown in Figure 2-5. In the Interface Config field, the DHCP relay agent state of a specific interface. Correlate the interface with multiple interfaces. Return to 20 DHCP server groups. Enable or disable the DHCP relay agent on the DHCP relay agent... check. Type the IP address of a DHCP server group. Enabling the DHCP Relay Agent on the same subnet as the IP address of a specific interface to DHCP Relay Agent Configuration Task List. 2-5 You can be on an Interface Select Network > DHCP from the navigation tree to enter the...
...the DHCP relay agent. Return to enter the page shown in Figure 2-5. In the Interface Config field, the DHCP relay agent state of a specific interface. Correlate the interface with multiple interfaces. Return to 20 DHCP server groups. Enable or disable the DHCP relay agent on the DHCP relay agent... check. Type the IP address of a DHCP server group. Enabling the DHCP Relay Agent on the same subnet as the IP address of a specific interface to DHCP Relay Agent Configuration Task List. 2-5 You can be on an Interface Select Network > DHCP from the navigation tree to enter the...
User Guide
Page 326
...interface configuration items Item Interface Name Interface State Option 82 Support Option 82 Strategy Description This field displays the name of a specific interface to DHCP Snooping Configuration Task List. Figure 3-5 DHCP snooping user information Table 3-3 describes DHCP snooping user information configuration items... and untrusted ports in Figure 3-4. Select the handling strategy for DHCP requests containing Option 82. Click the icon of a specific interface. z Keep: The message is forwarded without its original Option 82 is discarded if it contains Option 82. Return to...
...interface configuration items Item Interface Name Interface State Option 82 Support Option 82 Strategy Description This field displays the name of a specific interface to DHCP Snooping Configuration Task List. Figure 3-5 DHCP snooping user information Table 3-3 describes DHCP snooping user information configuration items... and untrusted ports in Figure 3-4. Select the handling strategy for DHCP requests containing Option 82. Click the icon of a specific interface. z Keep: The message is forwarded without its original Option 82 is discarded if it contains Option 82. Return to...
User Guide
Page 342
... the sender IP and MAC addresses in the received ARP reply are the same as those in Figure 1-3. After a static ARP entry is specified, only a specific MAC address is manually configured and maintained. It cannot get aged or be forwarded, the device sends an ARP request first. Usually ARP dynamically resolves...
... the sender IP and MAC addresses in the received ARP reply are the same as those in Figure 1-3. After a static ARP entry is specified, only a specific MAC address is manually configured and maintained. It cannot get aged or be forwarded, the device sends an ARP request first. Usually ARP dynamically resolves...
User Guide
Page 350
... attack Switch Host A IP_ A MAC_ A Host C IP_C MAC_C Forged ARP reply Forged ARP reply Host B IP_B MAC_B ARP detection mechanism With ARP detection enabled for a specific VLAN, ARP messages arrived on any interface in the VLAN are consistent, the ARP packet passes the check;
... attack Switch Host A IP_ A MAC_ A Host C IP_C MAC_C Forged ARP reply Forged ARP reply Host B IP_B MAC_B ARP detection mechanism With ARP detection enabled for a specific VLAN, ARP messages arrived on any interface in the VLAN are consistent, the ARP packet passes the check;
User Guide
Page 383
...the configuration on username format on the device does not take effect only after both global 802.1X and 802.1X on the specific port are mutually exclusive on an access port if the connected client sends untagged traffic. 1-28 For details about username format .... z From the navigation tree, select Network > Diagnostic Tools. z Figure 1-36 shows the ping operation summary. z Enter the destination IP address 10.0.0.1. Perform the following configurations as shown in some special network environment. 3) A port enabled with 802.1X cannot be added to an aggregation group. ...
...the configuration on username format on the device does not take effect only after both global 802.1X and 802.1X on the specific port are mutually exclusive on an access port if the connected client sends untagged traffic. 1-28 For details about username format .... z From the navigation tree, select Network > Diagnostic Tools. z Figure 1-36 shows the ping operation summary. z Enter the destination IP address 10.0.0.1. Perform the following configurations as shown in some special network environment. 3) A port enabled with 802.1X cannot be added to an aggregation group. ...
User Guide
Page 385
The three security functions are two RADIUS servers. For example, a user logging into the server can be authenticated before they access specific resources, you can use RADIUS server 1 for authentication and authorization, and RADIUS server 2 for the AAA servers, as follows: z Authentication: Identifies remote users and judges ...
The three security functions are two RADIUS servers. For example, a user logging into the server can be authenticated before they access specific resources, you can use RADIUS server 1 for authentication and authorization, and RADIUS server 2 for the AAA servers, as follows: z Authentication: Identifies remote users and judges ...
User Guide
Page 386
... the user belongs to configure AAA. 1-2 As the AAA framework allows for authentication and the isp-name part the ISP domain name. Introduction to access specific resources and records operations of the entities. Refer to User Configuration for the ISP domains. Configuration Task List Perform the tasks in Table 1-1 to the...
... the user belongs to configure AAA. 1-2 As the AAA framework allows for authentication and the isp-name part the ISP domain name. Introduction to access specific resources and records operations of the entities. Refer to User Configuration for the ISP domains. Configuration Task List Perform the tasks in Table 1-1 to the...
User Guide
Page 401
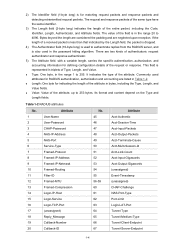
... and are two kinds of authenticators: request authenticator and response authenticator. 5) The Attribute field, with a variable length, carries the specific authentication, authorization, and accounting information for RADIUS authentication, authorization and accounting are listed in triplets of a received packet is less than... byte, in the range 1 to 253 bytes. z Value: Value of the request or response. Table 1-2 RADIUS attributes No. 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 Attribute User-Name User-Password CHAP-Password NAS-IP-Address NAS-Port Service-Type Framed...
... and are two kinds of authenticators: request authenticator and response authenticator. 5) The Attribute field, with a variable length, carries the specific authentication, authorization, and accounting information for RADIUS authentication, authorization and accounting are listed in triplets of a received packet is less than... byte, in the range 1 to 253 bytes. z Value: Value of the request or response. Table 1-2 RADIUS attributes No. 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 17 18 19 20 Attribute User-Name User-Password CHAP-Password NAS-IP-Address NAS-Port Service-Type Framed...