User Manual
Page 2
...Changing LAN Settings 53 Viewing the DHCP Client List Page 55 Configuring the Wireless Network Settings 56 Securing your Wi-Fi Network 61 WEP Setup 66 WPA Setup 68 Using the Access Point Mode 76 Wireless Range Extension and Bridging 77 Configuring the Firewall 81 Setting MAC Address ...Filtering 84 Enabling the Demilitarized Zone (DMZ 85 Utilities Tab 87 Restarting the Router 88 Updating ...
...Changing LAN Settings 53 Viewing the DHCP Client List Page 55 Configuring the Wireless Network Settings 56 Securing your Wi-Fi Network 61 WEP Setup 66 WPA Setup 68 Using the Access Point Mode 76 Wireless Range Extension and Bridging 77 Configuring the Firewall 81 Setting MAC Address ...Filtering 84 Enabling the Demilitarized Zone (DMZ 85 Utilities Tab 87 Restarting the Router 88 Updating ...
User Manual
Page 6
Should you to cover the maximum possible area with your Wireless Router or Access Point. Secure connections include: • Virtual Private Network (VPN) connections, often used where security is to simply reconnect by re-running the VPN or AOL software, or by a computer's power management setting, ... channels, in order to change your power management setting under Windows, see the "Power Options" item in your User Guide. For Belkin wireless networking products, use AOL through broadband provided by another cable or DSL service • Most on-line banking websites • Many ...
Should you to cover the maximum possible area with your Wireless Router or Access Point. Secure connections include: • Virtual Private Network (VPN) connections, often used where security is to simply reconnect by re-running the VPN or AOL software, or by a computer's power management setting, ... channels, in order to change your power management setting under Windows, see the "Power Options" item in your User Guide. For Belkin wireless networking products, use AOL through broadband provided by another cable or DSL service • Most on-line banking websites • Many ...
User Manual
Page 10
...an actual throughput of up your network. MAC Address Filtering For added security, you to block unwanted or offensive web content before it makes it to use the trial. Simply enter these MAC addresses into the Belkin Wireless Router, so there is compatible at a signaling rate of neighboring networks, and...Manual for 802.11g-capable networks in this unique feature. If you will never be modified to your network. *When operating in 54G Mode, nearly five times faster than 34.1Mbps, which is the equivalent throughput of a system following 802.11g protocol and operating at high ...
...an actual throughput of up your network. MAC Address Filtering For added security, you to block unwanted or offensive web content before it makes it to use the trial. Simply enter these MAC addresses into the Belkin Wireless Router, so there is compatible at a signaling rate of neighboring networks, and...Manual for 802.11g-capable networks in this unique feature. If you will never be modified to your network. *When operating in 54G Mode, nearly five times faster than 34.1Mbps, which is the equivalent throughput of a system following 802.11g protocol and operating at high ...
User Manual
Page 36
...such as the Internal IP address, the IP address pool, DHCP settings and more. • Set the Router's firewall to work with specific applications (port forwarding). • Set up security features such as client restrictions, MAC address filtering, WEP and WPA. • Enable the DMZ feature for... a single computer on the back of the Router labeled "Connection to Modem". 1.4 Connect the new blue network cable...
...such as the Internal IP address, the IP address pool, DHCP settings and more. • Set the Router's firewall to work with specific applications (port forwarding). • Set up security features such as client restrictions, MAC address filtering, WEP and WPA. • Enable the DMZ feature for... a single computer on the back of the Router labeled "Connection to Modem". 1.4 Connect the new blue network cable...
User Manual
Page 58
... to make changes to or you can make a change the SSID, type in the SSID that of another wireless network in your new network name. The default SSID of the Router is used as an access point. The change . (1) (2) 56 To change to be used . Changing...called the SSID (Service Set Identifier) is "belkin54g". If there are other wireless networks operating in the area). If you make changes to the wireless network name (SSID), operating channel, encryption security settings, and configure the Router to be reconfigured to connect to your area, you can leave it unchanged....
... to make changes to or you can make a change the SSID, type in the SSID that of another wireless network in your new network name. The default SSID of the Router is used as an access point. The change . (1) (2) 56 To change to be used . Changing...called the SSID (Service Set Identifier) is "belkin54g". If there are other wireless networks operating in the area). If you make changes to the wireless network name (SSID), operating channel, encryption security settings, and configure the Router to be reconfigured to connect to your area, you can leave it unchanged....
User Manual
Page 62
For security, you are scanning for the presence of wireless networks. To turn off the broadcast of the SSID, remove the check mark from computers that are in environments with Protected mode OFF. 60 an SSID of "ANY" will keep your best performance will be accepted. Therefore,... interference achieves best performance results. The change . Refer to your wireless network adapter for other wireless network traffic, your network name hidden from the box next to broadcast your network's SSID. When Protected mode is heavy 802.11b traffic in the operating environment. Doing so ...
For security, you are scanning for the presence of wireless networks. To turn off the broadcast of the SSID, remove the check mark from computers that are in environments with Protected mode OFF. 60 an SSID of "ANY" will keep your best performance will be accepted. Therefore,... interference achieves best performance results. The change . Refer to your wireless network adapter for other wireless network traffic, your network name hidden from the box next to broadcast your network's SSID. When Protected mode is heavy 802.11b traffic in the operating environment. Doing so ...
User Manual
Page 63
... level of your wireless network and protect your Wi-Fi® Network 1 Here are three encryption methods available. 3 4 Name 64-bit Wired 128-bit Wired Wi-Fi Protected With Protected Equivalent Equivalent Access-TKIP Access Privacy Privacy 5 Acronym 64-bit WEP 128-bit WEP WPA-TKIP WPA-AES Security Good Better Best... was introduced, researchers found that 64-bit encryption was first introduced with 64-bit encryption, which includes a key length of 40 bits plus that adds security to all Wi-Fi-compliant wireless products.
... level of your wireless network and protect your Wi-Fi® Network 1 Here are three encryption methods available. 3 4 Name 64-bit Wired 128-bit Wired Wi-Fi Protected With Protected Equivalent Equivalent Access-TKIP Access Privacy Privacy 5 Acronym 64-bit WEP 128-bit WEP WPA-TKIP WPA-AES Security Good Better Best... was introduced, researchers found that 64-bit encryption was first introduced with 64-bit encryption, which includes a key length of 40 bits plus that adds security to all Wi-Fi-compliant wireless products.
User Manual
Page 64
...Belkin wireless products will support both 64-bit and 128-bit WEP encryption, but different hardware manufacturers might have older equipment that you will be able to use the hex WEP key from A-F and 0-9. If the encryption key is not consistent throughout the entire wireless network, your wireless... mode, it manually into the hex WEP key table in your WEP keys, but you might have multiple vendors' equipments in your Router or...128-Bit WEP As a result of 64-bit WEP's potential security weaknesses, a more secure method of 128-bit encryption was developed. 128-bit encryption includes...
...Belkin wireless products will support both 64-bit and 128-bit WEP encryption, but different hardware manufacturers might have older equipment that you will be able to use the hex WEP key from A-F and 0-9. If the encryption key is not consistent throughout the entire wireless network, your wireless... mode, it manually into the hex WEP key table in your WEP keys, but you might have multiple vendors' equipments in your Router or...128-Bit WEP As a result of 64-bit WEP's potential security weaknesses, a more secure method of 128-bit encryption was developed. 128-bit encryption includes...
User Manual
Page 65
.... 9 For a list of Belkin wireless products that will be a combination of WEP. Typically, this is known as a Pre-Shared key as the Network key. To use WPA 2 security, the drivers and software of WPA security, WPA- 3 PSK (no server) uses what is the 6 mode that support WPA, please visit ...our website at www.belkin.com/networking. 10 11 12 13 section 63
.... 9 For a list of Belkin wireless products that will be a combination of WEP. Typically, this is known as a Pre-Shared key as the Network key. To use WPA 2 security, the drivers and software of WPA security, WPA- 3 PSK (no server) uses what is the 6 mode that support WPA, please visit ...our website at www.belkin.com/networking. 10 11 12 13 section 63
User Manual
Page 66
... User Interface Sharing the Same Network Keys Most Wi-Fi products ship with security turned off. Network key= MyPassword Wireless G Notebook Network Card Network key= MyPassword Wireless G Router Network key= MyPassword Wireless G Desktop Network Card Network key= WRONG Password Wireless G Desktop Network Card The Wireless G Desktop Network Card cannot access the network because it is using a different...
... User Interface Sharing the Same Network Keys Most Wi-Fi products ship with security turned off. Network key= MyPassword Wireless G Notebook Network Card Network key= MyPassword Wireless G Router Network key= MyPassword Wireless G Desktop Network Card Network key= WRONG Password Wireless G Desktop Network Card The Wireless G Desktop Network Card cannot access the network because it is using a different...
User Manual
Page 68
...key 3. WARNING: If you are configuring the Wireless Router or Access Point from a computer with a wireless client, you will now need to be configured with the same security settings. Each of numbers and letters from the...that security is not done, you will lose your key by typing in the hex key manually, or you can type in a passphrase in the Router is a mixture of your computers on your wireless ...network will need to create a key. If this is turned ON for this wireless client. For 64-bit WEP...
...key 3. WARNING: If you are configuring the Wireless Router or Access Point from a computer with a wireless client, you will now need to be configured with the same security settings. Each of numbers and letters from the...that security is not done, you will lose your key by typing in the hex key manually, or you can type in a passphrase in the Router is a mixture of your computers on your wireless ...network will need to create a key. If this is turned ON for this wireless client. For 64-bit WEP...
User Manual
Page 69
...encryption for this is a mixture of your computers on your wireless connection. 67 For 128-bit WEP, you will need to ensure that security is turned ON for your Mac computer, 2 set the encryption using the manual method described in the Router is now set. Click "Apply Changes" to finish. ...After selecting your WEP encryption mode, you can enter your 4 key manually by typing...
...encryption for this is a mixture of your computers on your wireless connection. 67 For 128-bit WEP, you will need to ensure that security is turned ON for your Mac computer, 2 set the encryption using the manual method described in the Router is now set. Click "Apply Changes" to finish. ...After selecting your WEP encryption mode, you can enter your 4 key manually by typing...
User Manual
Page 70
...be used in a business environment. From the "Security Mode" drop-down menu, select "WPA-PSK (no server) and WPA (with radius server). This can be from the Belkin support site. WPA (with WPA (Wireless Protected Access), the latest wireless security standard. For example, your clients must be ... network. To enable security, you must first determine which standard you set up . Each client uses the same key to download the latest driver for free, from Microsoft. Using the Web-Based Advanced User Interface Changing the Wireless Security Settings Your Router is typically used in...
...be used in a business environment. From the "Security Mode" drop-down menu, select "WPA-PSK (no server) and WPA (with radius server). This can be from the Belkin support site. WPA (with WPA (Wireless Protected Access), the latest wireless security standard. For example, your clients must be ... network. To enable security, you must first determine which standard you set up . Each client uses the same key to download the latest driver for free, from Microsoft. Using the Web-Based Advanced User Interface Changing the Wireless Security Settings Your Router is typically used in...
User Manual
Page 71
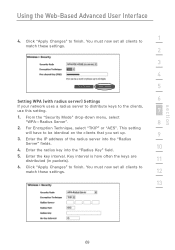
For Encryption Technique, select "TKIP" or "AES". Enter the IP address of the radius server into the "Radius Key" field. 10 5. From the "Security Mode" drop-down menu, select "WPA-Radius Server". 8 2. You must now set up. 9 3. Enter the radius key into the "Radius Server" fields. 4. You must now set ...
For Encryption Technique, select "TKIP" or "AES". Enter the IP address of the radius server into the "Radius Key" field. 10 5. From the "Security Mode" drop-down menu, select "WPA-Radius Server". 8 2. You must now set up. 9 3. Enter the radius key into the "Radius Server" fields. 4. You must now set ...
User Manual
Page 72
... to connect to a corporate network, please consult your WEP key in the "Network key" box. Using the Web-Based Advanced User Interface Configuring your Belkin Wireless G Network Cards to Use Security Please Note: This section is to provide you with the information on how to configure your Wireless Router or Access Point set your card. 2.
... to connect to a corporate network, please consult your WEP key in the "Network key" box. Using the Web-Based Advanced User Interface Configuring your Belkin Wireless G Network Cards to Use Security Please Note: This section is to provide you with the information on how to configure your Wireless Router or Access Point set your card. 2.
User Manual
Page 84
...settings you to route external (Internet) calls for services such as a web server (port 80), FTP server (Port 21), or other applications through your Router to your network (over the Internet) cannot get to the next available space in your application from the drop-down list. Opening ports in the..., the port(s) required to the maximum of the row that allows a start and end port range, e.g. [xxxxx]-[xxxxx]. For each entry, you can pose a security risk. You can only pass one port per field that you must use multiple entries up to pass, select the port type (TCP or UDP...
...settings you to route external (Internet) calls for services such as a web server (port 80), FTP server (Port 21), or other applications through your Router to your network (over the Internet) cannot get to the next available space in your application from the drop-down list. Opening ports in the..., the port(s) required to the maximum of the row that allows a start and end port range, e.g. [xxxxx]-[xxxxx]. For each entry, you can pose a security risk. You can only pass one port per field that you must use multiple entries up to pass, select the port type (TCP or UDP...
User Manual
Page 86
... able to delete the MAC address of each . Using the Web-Based Advanced User Interface Setting MAC Address Filtering The MAC address filter is a powerful security feature that is not specified in the space provided (2) and entering the MAC address of the computer you want to add to the list. To... delete a MAC address from the list. (1) (2) (3) To enable this feature, you must enter the MAC address of the computer you are using to access the Router's administrative functions (the computer you turn on the network. The "Block" feature lets you are using now). 84
... able to delete the MAC address of each . Using the Web-Based Advanced User Interface Setting MAC Address Filtering The MAC address filter is a powerful security feature that is not specified in the space provided (2) and entering the MAC address of the computer you want to add to the list. To... delete a MAC address from the list. (1) (2) (3) To enable this feature, you must enter the MAC address of the computer you are using to access the Router's administrative functions (the computer you turn on the network. The "Block" feature lets you are using now). 84
User Manual
Page 88
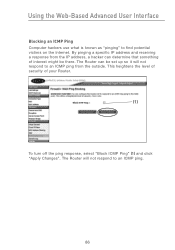
The Router will not respond to an ICMP ping from the IP address, a hacker can be there. This heightens the level of security of interest might be set up so it will not respond to find potential victims on the Internet. By pinging a specific IP address and receiving a response from the outside. The Router can determine that something of your Router. (1) To turn off the ping response, select "Block ICMP Ping" (1) and click "Apply Changes". Using the Web-Based Advanced User Interface Blocking an ICMP Ping Computer hackers use what is known as "pinging" to an ICMP ping. 86
The Router will not respond to an ICMP ping from the IP address, a hacker can be there. This heightens the level of security of interest might be set up so it will not respond to find potential victims on the Internet. By pinging a specific IP address and receiving a response from the outside. The Router can determine that something of your Router. (1) To turn off the ping response, select "Block ICMP Ping" (1) and click "Apply Changes". Using the Web-Based Advanced User Interface Blocking an ICMP Ping Computer hackers use what is known as "pinging" to an ICMP ping. 86
User Manual
Page 99
...left your computer alone without clicking "Logout". The login timeout option is for greater security, you have to login to the Router again to make any more changes. If you wish to add a password for security purposes and the default is where you will have made some changes in the ...future. section 97 The timer starts when 10 there has been no activity. Write down your Router. 6 7 8 9 Changing the Login Timeout Setting The ...
...left your computer alone without clicking "Logout". The login timeout option is for greater security, you have to login to the Router again to make any more changes. If you wish to add a password for security purposes and the default is where you will have made some changes in the ...future. section 97 The timer starts when 10 there has been no activity. Write down your Router. 6 7 8 9 Changing the Login Timeout Setting The ...
User Manual
Page 100
...Internet by connecting to record the security log and control client filtering. The second method is used to a Simple Network Time Protocol (SNTP) server. There are two methods of your Router to your Router's settings from in the space ...Belkin Router, MAKE SURE YOU HAVE SET THE ADMINISTRATOR PASSWORD. Using the Web-Based Advanced User Interface Setting the Time and Time Zone The Router keeps time by selecting "Any IP address can remotely manage the Router". This allows the Router to synchronize the system clock to remotely manage the Router. The first is more secure...
...Internet by connecting to record the security log and control client filtering. The second method is used to a Simple Network Time Protocol (SNTP) server. There are two methods of your Router to your Router's settings from in the space ...Belkin Router, MAKE SURE YOU HAVE SET THE ADMINISTRATOR PASSWORD. Using the Web-Based Advanced User Interface Setting the Time and Time Zone The Router keeps time by selecting "Any IP address can remotely manage the Router". This allows the Router to synchronize the system clock to remotely manage the Router. The first is more secure...