Software Configuration Guide
Page 505
...SMTP uses TCP port 25 on one address on subnet 48 and reject all others on all other end. Because the secure system of host 128.88.1.2. Gigabit Ethernet interface 1 is the interface that the...a Class A network whose second octet specifies a subnet; Mail packets coming in 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 27-23 that you do not want any host on the network to be ....0.0, and the mail host address is 128.88.1.2. The established keyword is used throughout the life of using an extended ACL, suppose that is, its subnet mask is applied to an existing connection...
...SMTP uses TCP port 25 on one address on subnet 48 and reject all others on all other end. Because the secure system of host 128.88.1.2. Gigabit Ethernet interface 1 is the interface that the...a Class A network whose second octet specifies a subnet; Mail packets coming in 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 27-23 that you do not want any host on the network to be ....0.0, and the mail host address is 128.88.1.2. The established keyword is used throughout the life of using an extended ACL, suppose that is, its subnet mask is applied to an existing connection...
Software Configuration Guide
Page 669
...dampened routes, including the time remaining before they are suppressed. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 30-61 The {filter-list list} | {address mask ...ID and the cluster-list attributes. (Optional) Save your entries in the configuration file. end Return to privileged EXEC mode. Dampening is stable. Beginning in privileged EXEC mode, use ...Step 5 Step 6 Step 7 Command Purpose configure terminal Enter global configuration mode. bgp dampening half-life reuse suppress max-suppress [route-map map] (Optional) Change the default values of the route, ...
...dampened routes, including the time remaining before they are suppressed. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 30-61 The {filter-list list} | {address mask ...ID and the cluster-list attributes. (Optional) Save your entries in the configuration file. end Return to privileged EXEC mode. Dampening is stable. Beginning in privileged EXEC mode, use ...Step 5 Step 6 Step 7 Command Purpose configure terminal Enter global configuration mode. bgp dampening half-life reuse suppress max-suppress [route-map map] (Optional) Change the default values of the route, ...
Software Configuration Guide
Page 684
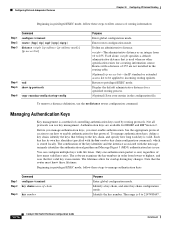
... | igrp | eigrp} distance weight {ip-address {ip-address mask}} [ip access list] Step 4 end Step 5 show ip protocols Step 6 copy running-config startup-config Purpose Enter global configuration mode. The range...configuration mode. Return to privileged EXEC mode. Not all protocols can configure multiple keys with life times. Identify the key number. Display the default administrative distance for a specified routing ...key chain configuration command), which is 0 to 2147483647. 30-76 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 You can use key management. Beginning...
... | igrp | eigrp} distance weight {ip-address {ip-address mask}} [ip access list] Step 4 end Step 5 show ip protocols Step 6 copy running-config startup-config Purpose Enter global configuration mode. The range...configuration mode. Return to privileged EXEC mode. Not all protocols can configure multiple keys with life times. Identify the key number. Display the default administrative distance for a specified routing ...key chain configuration command), which is 0 to 2147483647. 30-76 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 You can use key management. Beginning...