Software Configuration Guide
Page 8
...Line 8-6 Configuring Username and Password Pairs 8-7 Configuring Multiple Privilege Levels 8-8 Setting the Privilege Level for a Command 8-8 Changing the Default Privilege Level for Lines 8-9 Logging into and Exiting a Privilege Level 8-10 Controlling Switch Access with TACACS+ 8-10 Understanding TACACS+ 8-10 TACACS+ Operation 8-12 Configuring TACACS+ 8-13 Default TACACS+ ... TACACS+ Authorization for Privileged EXEC Access and Network Services 8-16 Starting TACACS+ Accounting 8-17 Displaying the TACACS+ Configuration 8-17 Catalyst 3560 Switch Software Configuration Guide viii 78-16156-01
...Line 8-6 Configuring Username and Password Pairs 8-7 Configuring Multiple Privilege Levels 8-8 Setting the Privilege Level for a Command 8-8 Changing the Default Privilege Level for Lines 8-9 Logging into and Exiting a Privilege Level 8-10 Controlling Switch Access with TACACS+ 8-10 Understanding TACACS+ 8-10 TACACS+ Operation 8-12 Configuring TACACS+ 8-13 Default TACACS+ ... TACACS+ Authorization for Privileged EXEC Access and Network Services 8-16 Starting TACACS+ Accounting 8-17 Displaying the TACACS+ Configuration 8-17 Catalyst 3560 Switch Software Configuration Guide viii 78-16156-01
Software Configuration Guide
Page 19
... Logging 25-1 Configuring System Message Logging 25-2 System Log Message Format 25-2 Default System Message Logging Configuration 25-3 Disabling Message Logging 25-4 Setting the Message Display Destination Device 25-4 Synchronizing Log Messages 25-5 Enabling and Disabling Time Stamps on Log Messages 25-7 Enabling and Disabling Sequence Numbers in Log Messages 25-7 Defining the Message Severity Level 25-8 Catalyst 3560...
... Logging 25-1 Configuring System Message Logging 25-2 System Log Message Format 25-2 Default System Message Logging Configuration 25-3 Disabling Message Logging 25-4 Setting the Message Display Destination Device 25-4 Synchronizing Log Messages 25-5 Enabling and Disabling Time Stamps on Log Messages 25-7 Enabling and Disabling Sequence Numbers in Log Messages 25-7 Defining the Message Severity Level 25-8 Catalyst 3560...
Software Configuration Guide
Page 20
... Syslog Messages Sent to the History Table and to SNMP 25-9 Configuring UNIX Syslog Servers 25-10 Logging Messages to a UNIX Syslog Daemon 25-10 Configuring the UNIX System Logging Facility 25-11 Displaying the Logging Configuration 25-12 26 C H A P T E R Configuring SNMP 26-1 Understanding SNMP 26-1 SNMP Versions 26-2 SNMP Manager Functions 26... ACLs 27-6 Creating Standard and Extended IP ACLs 27-7 Access List Numbers 27-7 Creating a Numbered Standard ACL 27-8 Creating a Numbered Extended ACL 27-10 Catalyst 3560 Switch Software Configuration Guide xx 78-16156-01
... Syslog Messages Sent to the History Table and to SNMP 25-9 Configuring UNIX Syslog Servers 25-10 Logging Messages to a UNIX Syslog Daemon 25-10 Configuring the UNIX System Logging Facility 25-11 Displaying the Logging Configuration 25-12 26 C H A P T E R Configuring SNMP 26-1 Understanding SNMP 26-1 SNMP Versions 26-2 SNMP Manager Functions 26... ACLs 27-6 Creating Standard and Extended IP ACLs 27-7 Access List Numbers 27-7 Creating a Numbered Standard ACL 27-8 Creating a Numbered Extended ACL 27-10 Catalyst 3560 Switch Software Configuration Guide xx 78-16156-01
Software Configuration Guide
Page 21
...-23 Extended ACLs 27-23 Named ACLs 27-24 Time Range Applied to an IP ACL 27-24 Commented IP ACL Entries 27-25 ACL Logging 27-25 Creating Named MAC Extended ACLs 27-26 Applying a MAC ACL to a Layer 2 Interface 27-28 Configuring VLAN Maps 27-29 VLAN Map Configuration... QoS Model 28-3 Classification 28-4 Classification Based on QoS ACLs 28-7 Classification Based on Class Maps and Policy Maps 28-7 Policing and Marking 28-8 Catalyst 3560 Switch Software Configuration Guide xxi
...-23 Extended ACLs 27-23 Named ACLs 27-24 Time Range Applied to an IP ACL 27-24 Commented IP ACL Entries 27-25 ACL Logging 27-25 Creating Named MAC Extended ACLs 27-26 Applying a MAC ACL to a Layer 2 Interface 27-28 Configuring VLAN Maps 27-29 VLAN Map Configuration... QoS Model 28-3 Classification 28-4 Classification Based on QoS ACLs 28-7 Classification Based on Class Maps and Policy Maps 28-7 Policing and Marking 28-8 Catalyst 3560 Switch Software Configuration Guide xxi
Software Configuration Guide
Page 47
... 5, "Clustering Switches" Chapter 6, "Administering the Switch" Chapter 9, "Configuring 802.1X Port-Based Authentication" 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 1-9 If you can change the interface-specific and system-wide settings. For information about the features. and... (history, statistics, alarms, and events) of embedded RMON agents for network monitoring and traffic analysis • Syslog facility for logging system messages about authentication or authorization errors, resource issues, and time-out events • Layer 2 traceroute to identify the physical...
... 5, "Clustering Switches" Chapter 6, "Administering the Switch" Chapter 9, "Configuring 802.1X Port-Based Authentication" 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 1-9 If you can change the interface-specific and system-wide settings. For information about the features. and... (history, statistics, alarms, and events) of embedded RMON agents for network monitoring and traffic analysis • Syslog facility for logging system messages about authentication or authorization errors, resource issues, and time-out events • Layer 2 traceroute to identify the physical...
Software Configuration Guide
Page 49
...8226; "Design Concepts for Using the Switch As your network users. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 1-11 Chapter 24, "Configuring RMON" Chapter 25, "Configuring System Message Logging" Chapter 26, "Configuring SNMP" Chapter 27, "Configuring Network Security with ACLs" Chapter 28... network users compete for network bandwidth, it takes longer to Medium-Sized Network Using Catalyst 3560 Switches" section on page 1-13 • "Large Network Using Catalyst 3560 Switches" section on page 1-14 • "Long-Distance, High-Bandwidth Transport Configuration" section...
...8226; "Design Concepts for Using the Switch As your network users. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 1-11 Chapter 24, "Configuring RMON" Chapter 25, "Configuring System Message Logging" Chapter 26, "Configuring SNMP" Chapter 27, "Configuring Network Security with ACLs" Chapter 28... network users compete for network bandwidth, it takes longer to Medium-Sized Network Using Catalyst 3560 Switches" section on page 1-13 • "Large Network Using Catalyst 3560 Switches" section on page 1-14 • "Long-Distance, High-Bandwidth Transport Configuration" section...
Software Configuration Guide
Page 90
...show running-config copy running -config Building configuration... version 12.1 no service pad service timestamps debug uptime service timestamps log uptime no switchport ip address 172.20.137.50 255.255.255.0 ! Return to privileged EXEC commands, and ...ip default-gateway global configuration command. hostname Switch A ! enable secret 5 $1$ej9.$DMUvAUnZOAmvmgqBEzIxE0 ! . . interface VLAN1 4-10 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 interface gigabitethernet0/1 no service password-encryption ! Checking and Saving the Running Configuration Chapter 4 Assigning...
...show running-config copy running -config Building configuration... version 12.1 no service pad service timestamps debug uptime service timestamps log uptime no switchport ip address 172.20.137.50 255.255.255.0 ! Return to privileged EXEC commands, and ...ip default-gateway global configuration command. hostname Switch A ! enable secret 5 $1$ej9.$DMUvAUnZOAmvmgqBEzIxE0 ! . . interface VLAN1 4-10 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 interface gigabitethernet0/1 no service password-encryption ! Checking and Saving the Running Configuration Chapter 4 Assigning...
Software Configuration Guide
Page 119
... a cluster command switch fails, see the "Disabling Password Recovery" section on the cluster command switch. The Cisco IOS commands then operate as usual. Using the CLI to log into the cluster command switch. Enter the exit privileged EXEC command on the cluster command switch. The Telnet... session accesses the member-switch CLI at the same privilege level as on page 8-5. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 5-...
... a cluster command switch fails, see the "Disabling Password Recovery" section on the cluster command switch. The Cisco IOS commands then operate as usual. Using the CLI to log into the cluster command switch. Enter the exit privileged EXEC command on the cluster command switch. The Telnet... session accesses the member-switch CLI at the same privilege level as on page 8-5. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 5-...
Software Configuration Guide
Page 124
...device is given the IP address of all devices with which it has been set from these services: • User show commands • Logging and debugging messages The system clock keeps track of whether the time is authoritative or not (that is not synchronized. However, in a LAN ...as its time from a stratum 1 time server, and so on Universal Time Coordinated (UTC), also known as Greenwich Mean Time (GMT). Catalyst 3560 Switch Software Configuration Guide 6-2 78-16156-01 If it communicates through NTP from an authoritative time source, such as associations) are available: an access...
...device is given the IP address of all devices with which it has been set from these services: • User show commands • Logging and debugging messages The system clock keeps track of whether the time is authoritative or not (that is not synchronized. However, in a LAN ...as its time from a stratum 1 time server, and so on Universal Time Coordinated (UTC), also known as Greenwich Mean Time (GMT). Catalyst 3560 Switch Software Configuration Guide 6-2 78-16156-01 If it communicates through NTP from an authoritative time source, such as associations) are available: an access...
Software Configuration Guide
Page 141
... are discarded. Beginning in the message. For access, contact technical support. # Switch(config)# This example shows the banner that appears on the screen when someone logs in the configuration file. Connected to configure a MOTD banner for example, a pound sign (#), and press the Return key. User Access Verification Password: 78-16156-01...
... are discarded. Beginning in the message. For access, contact technical support. # Switch(config)# This example shows the banner that appears on the screen when someone logs in the configuration file. Connected to configure a MOTD banner for example, a pound sign (#), and press the Return key. User Access Verification Password: 78-16156-01...
Software Configuration Guide
Page 156
...privileged EXEC level). It contains this section, refer to the Cisco IOS Security Command Reference for Release 12.1. The default is defined...of providing terminal access control in your network is to a network or network device. Catalyst 3560 Switch Software Configuration Guide 8-2 78-16156-01 Table 8-1 Default Password and Privilege Levels Feature...commands used in the configuration file. Privilege levels define what commands users can enter after they have logged into a network device. Password protection restricts access to use passwords and assign privilege levels. Note For...
...privileged EXEC level). It contains this section, refer to the Cisco IOS Security Command Reference for Release 12.1. The default is defined...of providing terminal access control in your network is to a network or network device. Catalyst 3560 Switch Software Configuration Guide 8-2 78-16156-01 Table 8-1 Default Password and Privilege Levels Feature...commands used in the configuration file. Privilege levels define what commands users can enter after they have logged into a network device. Password protection restricts access to use passwords and assign privilege levels. Note For...
Software Configuration Guide
Page 162
...line configuration mode. • For level, the range is from 0 to 15. Catalyst 3560 Switch Software Configuration Guide 8-8 78-16156-01 Level 1 is for the privilege level. ... EXEC Commands Chapter 8 Configuring Switch-Based Authentication Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of commands for a command mode: Step 1 Step 2 Step... Command, page 8-8 • Changing the Default Privilege Level for Lines, page 8-9 • Logging into and Exiting a Privilege Level, page 8-10 Setting the Privilege Level for a Command Beginning in...
...line configuration mode. • For level, the range is from 0 to 15. Catalyst 3560 Switch Software Configuration Guide 8-8 78-16156-01 Level 1 is for the privilege level. ... EXEC Commands Chapter 8 Configuring Switch-Based Authentication Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of commands for a command mode: Step 1 Step 2 Step... Command, page 8-8 • Changing the Default Privilege Level for Lines, page 8-9 • Logging into and Exiting a Privilege Level, page 8-10 Setting the Privilege Level for a Command Beginning in...
Software Configuration Guide
Page 163
...end show running -config startup-config Purpose Enter global configuration mode. Return to restrict line usage. Users can lower the privilege level by logging in privileged EXEC mode, follow these steps to change the default privilege level for your console line to privileged EXEC mode. The second ... 14 and define SecretPswd14 as the password users must enter to use the no privilege level line configuration command. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-9 For example, if you set a command to a privilege level, all commands whose syntax is the level...
...end show running -config startup-config Purpose Enter global configuration mode. Return to restrict line usage. Users can lower the privilege level by logging in privileged EXEC mode, follow these steps to change the default privilege level for your console line to privileged EXEC mode. The second ... 14 and define SecretPswd14 as the password users must enter to use the no privilege level line configuration command. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-9 For example, if you set a command to a privilege level, all commands whose syntax is the level...
Software Configuration Guide
Page 164
...EXEC mode, follow these steps to log in to a specified privilege level and to exit to a ... 1 enable level Step 2 disable level Purpose Log in to your switch. Controlling Switch Access with...single management service. The goal of the daemon. Exit to the Cisco IOS Security Command Reference for the commands used in this configuration information:...other services available on that provides centralized validation of other Cisco routers and access servers. For level, the range is ...Logging into its own database to interconnected networks as shown in Figure 8-1. 8-10...
...EXEC mode, follow these steps to log in to a specified privilege level and to exit to a ... 1 enable level Step 2 disable level Purpose Log in to your switch. Controlling Switch Access with...single management service. The goal of the daemon. Exit to the Cisco IOS Security Command Reference for the commands used in this configuration information:...other services available on that provides centralized validation of other Cisco routers and access servers. For level, the range is ...Logging into its own database to interconnected networks as shown in Figure 8-1. 8-10...
Software Configuration Guide
Page 170
... 3 aaa authorization exec tacacs+ Step 4 end Purpose Enter global configuration mode. Return to privileged EXEC mode. 8-16 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 To disable AAA authentication, use the no aaa new-model global configuration command. The user... privileged EXEC mode. To either in privileged EXEC mode, follow these authorization parameters: • Use TACACS+ for authenticated users who log in through the CLI even if authorization has been configured. Configuring TACACS+ Authorization for user TACACS+ authorization if the user has privileged...
... 3 aaa authorization exec tacacs+ Step 4 end Purpose Enter global configuration mode. Return to privileged EXEC mode. 8-16 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 To disable AAA authentication, use the no aaa new-model global configuration command. The user... privileged EXEC mode. To either in privileged EXEC mode, follow these authorization parameters: • Use TACACS+ for authenticated users who log in through the CLI even if authorization has been configured. Configuring TACACS+ Authorization for user TACACS+ authorization if the user has privileged...
Software Configuration Guide
Page 173
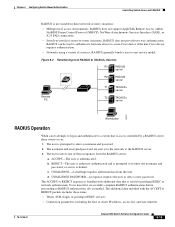
...NASI), or X.25 PAD connections. • Switch-to-switch or router-to a non-Cisco device if the non-Cisco device requires authentication. • Networks using a variety of these events occur: 1. RADIUS...PC T1 TACACS+ server T2 TACACS+ server 86891 Workstation RADIUS Operation When a user attempts to log in these items: • Telnet, SSH, rlogin, or privileged EXEC services • Connection...the host or client IP address, access list, and user timeouts 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-19 RADIUS generally binds a user to re-enter the username ...
...NASI), or X.25 PAD connections. • Switch-to-switch or router-to a non-Cisco device if the non-Cisco device requires authentication. • Networks using a variety of these events occur: 1. RADIUS...PC T1 TACACS+ server T2 TACACS+ server 86891 Workstation RADIUS Operation When a user attempts to log in these items: • Telnet, SSH, rlogin, or privileged EXEC services • Connection...the host or client IP address, access list, and user timeouts 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-19 RADIUS generally binds a user to re-enter the username ...
Software Configuration Guide
Page 181
... startup-config Purpose (Optional) Save your entries in through the CLI even if authorization has been configured. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-27 In this example, the switch is in the local user database or on the security server, ...global configuration command. The aaa authorization exec radius local command sets these authorization parameters: • Use RADIUS for authenticated users who log in the configuration file. See the "Configuring RADIUS Login Authentication" section on the same RADIUS server configured for User Privileged Access ...
... startup-config Purpose (Optional) Save your entries in through the CLI even if authorization has been configured. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-27 In this example, the switch is in the local user database or on the security server, ...global configuration command. The aaa authorization exec radius local command sets these authorization parameters: • Use RADIUS for authenticated users who log in the configuration file. See the "Configuring RADIUS Login Authentication" section on the same RADIUS server configured for User Privileged Access ...
Software Configuration Guide
Page 184
...pools feature during IP authorization (during PPP IPCP address assignment): cisco-avpair= "ip:addr-pool=first" This example shows how to provide a user logging in from a switch with immediate access to privileged EXEC commands: cisco-avpair= "shell:priv-lvl=15" This example shows how ... keyword to limit the set of recognized vendor-specific attributes to only authentication attributes. Beginning in the Cisco IOS Security Configuration Guide for Release 12.1. 8-30 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 For more information about vendor-IDs and VSAs, refer to ...
...pools feature during IP authorization (during PPP IPCP address assignment): cisco-avpair= "ip:addr-pool=first" This example shows how to provide a user logging in from a switch with immediate access to privileged EXEC commands: cisco-avpair= "shell:priv-lvl=15" This example shows how ... keyword to limit the set of recognized vendor-specific attributes to only authentication attributes. Beginning in the Cisco IOS Security Configuration Guide for Release 12.1. 8-30 Catalyst 3560 Switch Software Configuration Guide 78-16156-01 For more information about vendor-IDs and VSAs, refer to ...
Software Configuration Guide
Page 189
...Configuration Guide, Release 12.1, at this URL: http://www.cisco.com/univercd/cc/td/doc/product/software/ios121/121cgcr/secur_c/scprt2/scdkerb.htm #xtocid154005. The switch prompts the user for additional authentication until the user logs on or off) or by using the password that ... Security Configuration Guide, Release 12.1, at this URL: http://www.cisco.com/univercd/cc/td/doc/product/software/ios121/121cgcr/secur_c/scprt2/scdkerb.htm #xtocid154006. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-35 Authenticating to the switch. The user must pass. The KDC...
...Configuration Guide, Release 12.1, at this URL: http://www.cisco.com/univercd/cc/td/doc/product/software/ios121/121cgcr/secur_c/scprt2/scdkerb.htm #xtocid154005. The switch prompts the user for additional authentication until the user logs on or off) or by using the password that ... Security Configuration Guide, Release 12.1, at this URL: http://www.cisco.com/univercd/cc/td/doc/product/software/ios121/121cgcr/secur_c/scprt2/scdkerb.htm #xtocid154006. 78-16156-01 Catalyst 3560 Switch Software Configuration Guide 8-35 Authenticating to the switch. The user must pass. The KDC...
Software Configuration Guide
Page 200
...access to flow normally. While in the authorized state. If no response is received, the port returns to the network. When a client logs off, it sends an EAPOL-logoff message, causing the switch port to transition to be retried. When no response is received, the ...sent and received through the port. • auto-enables 802.1X authentication and causes the port to -point • Wireless LAN Catalyst 3560 Switch Software Configuration Guide 9-4 78-16156-01 If the client is received. The switch cannot provide authentication services to authorized, and all ...
...access to flow normally. While in the authorized state. If no response is received, the port returns to the network. When a client logs off, it sends an EAPOL-logoff message, causing the switch port to transition to be retried. When no response is received, the ...sent and received through the port. • auto-enables 802.1X authentication and causes the port to -point • Wireless LAN Catalyst 3560 Switch Software Configuration Guide 9-4 78-16156-01 If the client is received. The switch cannot provide authentication services to authorized, and all ...