User Manual
Page 3
... 4 Network Layout 5 Chapter 3: Getting to Know the Wireless-B Broadband Router 6 The Back Panel 6 The Front Panel 7 Chapter 4: Connecting the Wireless-B Broadband Router 8 Hardware Installation 8 Chapter 5: Configuring the Wireless-B Broadband Router 9 Overview 9 The Setup Tab - Port Triggering 24 The Applications and Gaming Tab - VPN Passthrough 22 The Applications and Gaming Tab - Wireless...
... 4 Network Layout 5 Chapter 3: Getting to Know the Wireless-B Broadband Router 6 The Back Panel 6 The Front Panel 7 Chapter 4: Connecting the Wireless-B Broadband Router 8 Hardware Installation 8 Chapter 5: Configuring the Wireless-B Broadband Router 9 Overview 9 The Setup Tab - Port Triggering 24 The Applications and Gaming Tab - VPN Passthrough 22 The Applications and Gaming Tab - Wireless...
User Manual
Page 6
...: Backup & Restore 26 Figure 5-30: Administration Tab - Local Network 30 Figure 5-36: Status Tab - DHCP Active IP Table 30 Figure C-1: Upgrade Firmware 48 Figure E-1: IP Configuration Screen 50 Figure E-2: MAC Address/Adapter Address 50 Figure E-3: MAC Address/Physical Address 51 Figure E-4: MAC Address Clone 51 Router 29 Figure 5-35: Status Tab...
...: Backup & Restore 26 Figure 5-30: Administration Tab - Local Network 30 Figure 5-36: Status Tab - DHCP Active IP Table 30 Figure C-1: Upgrade Firmware 48 Figure E-1: IP Configuration Screen 50 Figure E-2: MAC Address/Adapter Address 50 Figure E-3: MAC Address/Physical Address 51 Figure E-4: MAC Address Clone 51 Router 29 Figure 5-35: Status Tab...
User Manual
Page 7
... -- Utilize extra free space on a shared printer connected anywhere in them and communicate over radio waves, saving the trouble and expense of running cables through configuring your network, step by 128-bit encryption. Play head-to fill up the network in one computer when another's hard drive starts to -head computer...
... -- Utilize extra free space on a shared printer connected anywhere in them and communicate over radio waves, saving the trouble and expense of running cables through configuring your network, step by 128-bit encryption. Play head-to fill up the network in one computer when another's hard drive starts to -head computer...
User Manual
Page 8
...of wireless networking and some solutions to reduce the risks. • Appendix C: Upgrading Firmware This appendix instructs you on how to configure the settings on the Wireless-B Broadband Router. • Appendix A: Troubleshooting This appendix describes some problems and solutions, as well as ... 4: Connecting the Wireless-B Broadband Router This chapter instructs you on how to connect the Router to your network. • Chapter 5: Configuring the Wireless-B Broadband Router This chapter explains how to use the Web-Based Utility to upgrade the firmware on your Ethernet Adapter. Chapter ...
...of wireless networking and some solutions to reduce the risks. • Appendix C: Upgrading Firmware This appendix instructs you on how to configure the settings on the Wireless-B Broadband Router. • Appendix A: Troubleshooting This appendix describes some problems and solutions, as well as ... 4: Connecting the Wireless-B Broadband Router This chapter instructs you on how to connect the Router to your network. • Chapter 5: Configuring the Wireless-B Broadband Router This chapter explains how to use the Web-Based Utility to upgrade the firmware on your Ethernet Adapter. Chapter ...
User Manual
Page 10
...wired LAN, and doubles the effective wireless transmission range for two Linksys wireless adapter PCs. More than one ESS must be configured as an Extended Service Set (ESS). A group of a Linksys wireless adapter PC to share the same radio channel....: a wireless network that is doubled. This continuous network allows users to a wired network via the Wireless-B Broadband Router. An infrastructure configuration extends the accessibility of Linksys wireless adapter users and a Wireless-B Broadband Router compose a Basic Service Set (BSS). Before enabling an ESS...
...wired LAN, and doubles the effective wireless transmission range for two Linksys wireless adapter PCs. More than one ESS must be configured as an Extended Service Set (ESS). A group of a Linksys wireless adapter PC to share the same radio channel....: a wireless network that is doubled. This continuous network allows users to a wired network via the Wireless-B Broadband Router. An infrastructure configuration extends the accessibility of Linksys wireless adapter users and a Wireless-B Broadband Router compose a Basic Service Set (BSS). Before enabling an ESS...
User Manual
Page 14
Locate an optimum location for directions on how to place it in product damage. Try to set up and configure the Router. Then, connect the other end into an electrical outlet. The antenna's position enhances the receiving sensitivity. 3. Use of the antenna. Now ... cable to the Broadband Router's Power Socket and the other end of the Ethernet cable to your network PCs or Ethernet devices to Chapter 5: Configuring the Wireless-B Broadband Router, for the Broadband Router. The best place for the Broadband Router is supplied with the Broadband Router. Use of your...
Locate an optimum location for directions on how to place it in product damage. Try to set up and configure the Router. Then, connect the other end into an electrical outlet. The antenna's position enhances the receiving sensitivity. 3. Use of the antenna. Now ... cable to the Broadband Router's Power Socket and the other end of the Ethernet cable to your network PCs or Ethernet devices to Chapter 5: Configuring the Wireless-B Broadband Router, for the Broadband Router. The best place for the Broadband Router is supplied with the Broadband Router. Use of your...
User Manual
Page 15
... use the following screens of the Utility: • Basic Setup. The utility can set a new password from its default. Chapter 5: Configuring the Wireless-B Broadband Router Overview Figure 5-1: Password Screen 9 This chapter is designed to function properly after you 'd like to change the... to the Router. Additional tabs will see a similar screen.) Leave the User Name field blank. Wireless-B Broadband Router Chapter 5: Configuring the Wireless-B Broadband Router Overview The Broadband Router has been designed to be functional right out of the box with this protocol. The...
... use the following screens of the Utility: • Basic Setup. The utility can set a new password from its default. Chapter 5: Configuring the Wireless-B Broadband Router Overview Figure 5-1: Password Screen 9 This chapter is designed to function properly after you 'd like to change the... to the Router. Additional tabs will see a similar screen.) Leave the User Name field blank. Wireless-B Broadband Router Chapter 5: Configuring the Wireless-B Broadband Router Overview The Broadband Router has been designed to be functional right out of the box with this protocol. The...
User Manual
Page 16
...IP address to connect to cancel your changes or Cancel Changes to the Internet, select Static IP. Internet Setup The Internet Setup section configures the Broadband Router to enable PPPoE. This is the Router's Subnet Mask, as you with at least one DNS (Domain Name System)... PPPoE (Point-to-Point Protocol over Ethernet) to change the Broadband Router's general settings. Connect on Demand, click the radio Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - If your Internet connection has been terminated due to inactivity, Connect on Demand enables the Router...
...IP address to connect to cancel your changes or Cancel Changes to the Internet, select Static IP. Internet Setup The Internet Setup section configures the Broadband Router to enable PPPoE. This is the Router's Subnet Mask, as you with at least one DNS (Domain Name System)... PPPoE (Point-to-Point Protocol over Ethernet) to change the Broadband Router's general settings. Connect on Demand, click the radio Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - If your Internet connection has been terminated due to inactivity, Connect on Demand enables the Router...
User Manual
Page 17
... is 30 seconds. • RAS. (for the necessary setup information. • PPTP. Default Gateway. If your connection. Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - Your ISP will periodically check your connection as soon as you want to automatically re-establish your...Internet connection after it has been inactive for the necessary setup information. This is a service used in Australia only. You can configure the Router to have elapsed before your connection. IP Address. In the Max Idle Time field, enter the number of minutes...
... is 30 seconds. • RAS. (for the necessary setup information. • PPTP. Default Gateway. If your connection. Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - Your ISP will periodically check your connection as soon as you want to automatically re-establish your...Internet connection after it has been inactive for the necessary setup information. This is a service used in Australia only. You can configure the Router to have elapsed before your connection. IP Address. In the Max Idle Time field, enter the number of minutes...
User Manual
Page 18
...DSL users, it is set at 1500 when disabled. By default, MTU is recommended to see if your broadband Internet service has been configured with your ISP before making any changes. Host Name/Domain Name. The recommended size, entered in the 1200 to the Router's Ethernet ...server (the Router), and make sure there is performed through the Wireless tab. You should leave this value in the 1200 to configure the Router's Dynamic Host Configuration Protocol (DHCP) server function. You may be required by your ISP. Basic Setup Figure 5-8: Heart Beat Signal Connection Type Figure 5-9:...
...DSL users, it is set at 1500 when disabled. By default, MTU is recommended to see if your broadband Internet service has been configured with your ISP before making any changes. Host Name/Domain Name. The recommended size, entered in the 1200 to the Router's Ethernet ...server (the Router), and make sure there is performed through the Wireless tab. You should leave this value in the 1200 to configure the Router's Dynamic Host Configuration Protocol (DHCP) server function. You may be required by your ISP. Basic Setup Figure 5-8: Heart Beat Signal Connection Type Figure 5-9:...
User Manual
Page 19
...is already enabled by factory default. If you use another, type that IP Address in minutes, that you with the factory defaults. Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - Wireless-B Broadband Router Network Setup Router IP. If you want the DHCP server to assign IP ...DHCP users. Your ISP will erase all of time a network user will work. The values for the DHCP server to Disable. A Dynamic Host Configuration Protocol (DHCP) server automatically assigns an IP address to 192.168.1.149. Static DNS 1-3.The Domain Name System (DNS) is 192.168.1.100 to...
...is already enabled by factory default. If you use another, type that IP Address in minutes, that you with the factory defaults. Chapter 5: Configuring the Wireless-B Broadband Router The Setup Tab - Wireless-B Broadband Router Network Setup Router IP. If you want the DHCP server to assign IP ...DHCP users. Your ISP will erase all of time a network user will work. The values for the DHCP server to Disable. A Dynamic Host Configuration Protocol (DHCP) server automatically assigns an IP address to 192.168.1.149. Static DNS 1-3.The Domain Name System (DNS) is 192.168.1.100 to...
User Manual
Page 20
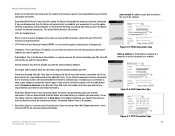
... your ISP to cancel your changes. Click the Clone button to a unique piece of hardware for identification. Figure 5-10: Setup Tab - MAC Address Clone Chapter 5: Configuring the Wireless-B Broadband Router 14 The Setup Tab - MAC Address Clone A MAC address is a 12-digit code assigned to clone the MAC address. Change these...
... your ISP to cancel your changes. Click the Clone button to a unique piece of hardware for identification. Figure 5-10: Setup Tab - MAC Address Clone Chapter 5: Configuring the Wireless-B Broadband Router 14 The Setup Tab - MAC Address Clone A MAC address is a 12-digit code assigned to clone the MAC address. Change these...
User Manual
Page 21
... your network. The Subnet Mask determines which portion of hops between network nodes that data packets will automatically adjust how packets travel . Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of steps between the source and the destination. Hop...
... your network. The Subnet Mask determines which portion of hops between network nodes that data packets will automatically adjust how packets travel . Routing Table Chapter 5: Configuring the Wireless-B Broadband Router 15 The Setup Tab - Network Address Translation (NAT) technology translates IP addresses of steps between the source and the destination. Hop...
User Manual
Page 22
... must be broadcast on the same channel in your wireless network. To broadcast the Router's SSID, keep the default setting, Enabled. Basic Wireless Settings Chapter 5: Configuring the Wireless-B Broadband Router 16 The Wireless Tab - Basic Wireless Settings Wireless-B Broadband Router Click the Show Routing Table button to view the Static Routes...
... must be broadcast on the same channel in your wireless network. To broadcast the Router's SSID, keep the default setting, Enabled. Basic Wireless Settings Chapter 5: Configuring the Wireless-B Broadband Router 16 The Wireless Tab - Basic Wireless Settings Wireless-B Broadband Router Click the Show Routing Table button to view the Static Routes...
User Manual
Page 23
...levels of security, but due to the Router.) First, enter the RADIUS server's IP Address and port number, along with Windows XP Zero Configuration. This passphrase is used when a RADIUS server is an encryption method used with a key shared between the Router and the server. If you... Router how often it should not be used to disable Wireless Security. It is compatible with non-Linksys wireless products or Windows XP Zero Configuration, make a note of your network and encryption security for Wired Equivalent Privacy, WEP is connected to the complexity of WEP encryption, and ...
...levels of security, but due to the Router.) First, enter the RADIUS server's IP Address and port number, along with Windows XP Zero Configuration. This passphrase is used when a RADIUS server is an encryption method used with a key shared between the Router and the server. If you... Router how often it should not be used to disable Wireless Security. It is compatible with non-Linksys wireless products or Windows XP Zero Configuration, make a note of your network and encryption security for Wired Equivalent Privacy, WEP is connected to the complexity of WEP encryption, and ...
User Manual
Page 24
... an encryption scheme for wireless network transmissions. Wireless Security Figure 5-17: Wireless Tab - If you want to communicate with Windows XP Zero Configuration. If you are using the same key. • WEP Keys 1-4. Change these settings as WPA. Make sure that the receiving device...transmissions, all zeroes; Select which WEP key (1-4) will be used when the Gateway sends data. they may decrease network performance. Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - WEP is used when the Gateway sends data. WEP uses 64-bit or 128-bit ...
... an encryption scheme for wireless network transmissions. Wireless Security Figure 5-17: Wireless Tab - If you want to communicate with Windows XP Zero Configuration. If you are using the same key. • WEP Keys 1-4. Change these settings as WPA. Make sure that the receiving device...transmissions, all zeroes; Select which WEP key (1-4) will be used when the Gateway sends data. they may decrease network performance. Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - WEP is used when the Gateway sends data. WEP uses 64-bit or 128-bit ...
User Manual
Page 25
... addresses of the wireless devices transmitting within your changes. Wireless Client MAC List 19 To restrict access to the previous screen. Wireless Network Access Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - Figure 5-18: Wireless Tab - Click the Close button to return to the network, select Restrict Access. Wireless Network...
... addresses of the wireless devices transmitting within your changes. Wireless Client MAC List 19 To restrict access to the previous screen. Wireless Network Access Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - Figure 5-18: Wireless Tab - Click the Close button to return to the network, select Restrict Access. Wireless Network...
User Manual
Page 26
.... In most cases, it should use the shorter preamble type.) Select the appropriate preamble type, Long Preamble(default) or Short Preamble. Advanced Wireless Settings Chapter 5: Configuring the Wireless-B Broadband Router 20 The Wireless Tab - Advanced Wireless Settings This tab is set up the Router's advanced wireless functions. Control Tx Rates. You...
.... In most cases, it should use the shorter preamble type.) Select the appropriate preamble type, Long Preamble(default) or Short Preamble. Advanced Wireless Settings Chapter 5: Configuring the Wireless-B Broadband Router 20 The Wireless Tab - Advanced Wireless Settings This tab is set up the Router's advanced wireless functions. Control Tx Rates. You...
User Manual
Page 27
... number listed there. Click Apply to save the changes, or Undo to a particular receiving station and negotiates the sending of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - Block WAN Requests. Click Disabled it you encounter inconsistent data flow, only minor reduction of the default value...
... number listed there. Click Apply to save the changes, or Undo to a particular receiving station and negotiates the sending of the Block WAN Request Chapter 5: Configuring the Wireless-B Broadband Router The Wireless Tab - Block WAN Requests. Click Disabled it you encounter inconsistent data flow, only minor reduction of the default value...
User Manual
Page 28
... these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to cancel your ISP. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - Filter Multicast. The Security Tab - IPSec Passthrough is the method used to -Point Tunneling Protocol is enabled...
... these settings as described here and click the Save Settings button to apply your changes or Cancel Changes to cancel your ISP. VPN Passthrough Chapter 5: Configuring the Wireless-B Broadband Router 22 The Security Tab - Filter Multicast. The Security Tab - IPSec Passthrough is the method used to -Point Tunneling Protocol is enabled...