Software Guide
Page 4
... Opening the CLI with Secure Shell 2-2 Obtaining and Assigning an IP Address 2-3 Assigning an IP Address By Using the Exec 2-3 Protecting Your Wireless LAN 2-4 Configuring Basic Security Settings 2-4 Using VLANs 2-4 Express Security Types 2-5 CLI Security Configuration Examples 2-6 Example: No ... Bridging 3-4 Redundant Bridging 3-5 Workgroup Bridge Role 3-6 Universal Workgroup Bridge (2.4-GHz Radios Only) 3-8 Configuring Universal Workgroup Bridge on a Cisco 3200 3-11 Assigning Dynamic MAC address for Universal Workgroup Bridge 3-12 World Mode (2.4 GHz Radio Only) 3-12 Supported Country Codes ...
... Opening the CLI with Secure Shell 2-2 Obtaining and Assigning an IP Address 2-3 Assigning an IP Address By Using the Exec 2-3 Protecting Your Wireless LAN 2-4 Configuring Basic Security Settings 2-4 Using VLANs 2-4 Express Security Types 2-5 CLI Security Configuration Examples 2-6 Example: No ... Bridging 3-4 Redundant Bridging 3-5 Workgroup Bridge Role 3-6 Universal Workgroup Bridge (2.4-GHz Radios Only) 3-8 Configuring Universal Workgroup Bridge on a Cisco 3200 3-11 Assigning Dynamic MAC address for Universal Workgroup Bridge 3-12 World Mode (2.4 GHz Radio Only) 3-12 Supported Country Codes ...
Software Guide
Page 5
... Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation...the RADIUS Configuration 4-31 Controlling WMIC Access with TACACS+ 4-32 Understanding TACACS+ 4-32 TACACS+ Operation 4-33 Default TACACS+ Configuration 4-33 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide v
... Username and Password Pairs 4-9 Configuring Multiple Privilege Levels 4-10 Setting the Privilege Level for a Command 4-10 Logging Into and Exiting a Privilege Level 4-11 Protecting the Wireless LAN 4-11 Using VLANs 4-11 Express Security Types 4-12 Security Configuration Examples 4-14 Configuring and Enabling RADIUS 4-19 Understanding RADIUS 4-19 RADIUS Operation...the RADIUS Configuration 4-31 Controlling WMIC Access with TACACS+ 4-32 Understanding TACACS+ 4-32 TACACS+ Operation 4-33 Default TACACS+ Configuration 4-33 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide v
Software Guide
Page 13
GLOSSARY INDEX Using CLI Commands to Enable Roaming 14-12 Management Frame Protection 15-1 Understanding Management Frame Protection 15-1 Protection of Unicast Management Frames 15-2 Protection of Broadcast Management Frames 15-2 Client MFP For Access Points in Root mode 15-2 Configuring Client MFP 15-2 Configuring Infrastructure MFP 15-3 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xiii
GLOSSARY INDEX Using CLI Commands to Enable Roaming 14-12 Management Frame Protection 15-1 Understanding Management Frame Protection 15-1 Protection of Unicast Management Frames 15-2 Protection of Broadcast Management Frames 15-2 Client MFP For Access Points in Root mode 15-2 Configuring Client MFP 15-2 Configuring Infrastructure MFP 15-3 OL-6415-04 Cisco 3200 Series Wireless MIC Software Configuration Guide xiii
Software Guide
Page 31
....1x supplicant provides a secure method for Wi-Fi Protected Access (WPA) with Cipher Block Chaining Message Authentication Code Protocol (AES-CCMP). Cisco 3200 Series Wireless MIC Software Configuration Guide 7 AES-CCMP is required for Wi-Fi Protected Access 2 (WPA2) and IEEE 802.11i wireless .... The supplicant refers to any root device as long the encrption and authentication settings match. • Management Frame Protection (MFP)-Support management frame protection version 1 and 2. May associate to the client software that supports the 802.1x and EAP protocols. After a...
....1x supplicant provides a secure method for Wi-Fi Protected Access (WPA) with Cipher Block Chaining Message Authentication Code Protocol (AES-CCMP). Cisco 3200 Series Wireless MIC Software Configuration Guide 7 AES-CCMP is required for Wi-Fi Protected Access 2 (WPA2) and IEEE 802.11i wireless .... The supplicant refers to any root device as long the encrption and authentication settings match. • Management Frame Protection (MFP)-Support management frame protection version 1 and 2. May associate to the client software that supports the 802.1x and EAP protocols. After a...
Software Guide
Page 36
...a DB-9-to-RJ-45 serial cable. When the terminal emulator establishes communications, a router prompt displays. The default username is Cisco. The default password is Cisco. Note In Windows 2000, the Telnet window does not contain drop-down menus. See the "Administering the WMIC" document for...baud, 8 data bits, no parity, 1 stop bit, and no flow control. SSH features strong cryptographic authentication, strong encryption, and integrity protection. Connecting to the WMIC Configuring the WMIC for the First Time Using the Console Port to Access the Privileged Exec Mode Connect a PC to...
...a DB-9-to-RJ-45 serial cable. When the terminal emulator establishes communications, a router prompt displays. The default username is Cisco. The default password is Cisco. Note In Windows 2000, the Telnet window does not contain drop-down menus. See the "Administering the WMIC" document for...baud, 8 data bits, no parity, 1 stop bit, and no flow control. SSH features strong cryptographic authentication, strong encryption, and integrity protection. Connecting to the WMIC Configuring the WMIC for the First Time Using the Console Port to Access the Privileged Exec Mode Connect a PC to...
Software Guide
Page 38
... VLANs disabled, you need to configure security settings to prevent unauthorized access to your network. Protecting Your Wireless LAN Configuring the WMIC for the First Time Protecting Your Wireless LAN After you assign basic settings to your WMIC, you cannot create additional SSIDs... Settings After you assign basic settings to your access point, you must configure security settings to prevent unauthorized access to your network. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Without VLANs, encryption settings (WEP and ciphers) apply to an interface, such as ...
... VLANs disabled, you need to configure security settings to prevent unauthorized access to your network. Protecting Your Wireless LAN Configuring the WMIC for the First Time Protecting Your Wireless LAN After you assign basic settings to your WMIC, you cannot create additional SSIDs... Settings After you assign basic settings to your access point, you must configure security settings to prevent unauthorized access to your network. Cisco 3200 Series Wireless MIC Software Configuration Guide 4 Without VLANs, encryption settings (WEP and ciphers) apply to an interface, such as ...
Software Guide
Page 39
...open authentication. Mandatory WEP encryption, no security. This option enables 802.1x extensible authentication protocol (EAP) types, including Lightweight EAP (LEAP), Protected EAP (PEAP), EAP-Transport Layer Security (EAP-TLS), and EAP-GTC, and requires you can assign to an SSID. In Root ...be WPA-capable. You should consider limiting association to your network. This option is the least secure option. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 Wi-Fi Protected Access (WPA) permits wireless access to enter a WEP key. Assign this setting, you must perform 802....
...open authentication. Mandatory WEP encryption, no security. This option enables 802.1x extensible authentication protocol (EAP) types, including Lightweight EAP (LEAP), Protected EAP (PEAP), EAP-Transport Layer Security (EAP-TLS), and EAP-GTC, and requires you can assign to an SSID. In Root ...be WPA-capable. You should consider limiting association to your network. This option is the least secure option. Cisco 3200 Series Wireless MIC Software Configuration Guide 5 Wi-Fi Protected Access (WPA) permits wireless access to enter a WEP key. Assign this setting, you must perform 802....
Software Guide
Page 40
...key: encryption vlan 20 key 3 size 128bit 7 4E78330C1A841439656A9323F25A transmit-ke y encryption vlan 20 mode wep mandatory ! ssid no_security-ssid Cisco 3200 Series Wireless MIC Software Configuration Guide 6 interface FastEthernet0.10 encapsulation dot1Q 10 no ip address no ip route-cache duplex auto... authentication open interface Dot11Radio0 no ip address no ip route-cache bridge-group 10 bridge-group 10 spanning-disabled ! Protecting Your Wireless LAN Configuring the WMIC for the First Time CLI Security Configuration Examples This section provides example configurations for creating...
...key: encryption vlan 20 key 3 size 128bit 7 4E78330C1A841439656A9323F25A transmit-ke y encryption vlan 20 mode wep mandatory ! ssid no_security-ssid Cisco 3200 Series Wireless MIC Software Configuration Guide 6 interface FastEthernet0.10 encapsulation dot1Q 10 no ip address no ip route-cache duplex auto... authentication open interface Dot11Radio0 no ip address no ip route-cache bridge-group 10 bridge-group 10 spanning-disabled ! Protecting Your Wireless LAN Configuring the WMIC for the First Time CLI Security Configuration Examples This section provides example configurations for creating...
Software Guide
Page 41
... 1 block-unknown-source no bridge-group 1 source-learning no bridge-group 1 unicast-flooding bridge-group 1 spanning-disabled ! Cisco 3200 Series Wireless MIC Software Configuration Guide 7 ssid no_security-ssid ! Configuring the WMIC for the First Time Protecting Your Wireless LAN ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts...
... 1 block-unknown-source no bridge-group 1 source-learning no bridge-group 1 unicast-flooding bridge-group 1 spanning-disabled ! Cisco 3200 Series Wireless MIC Software Configuration Guide 7 ssid no_security-ssid ! Configuring the WMIC for the First Time Protecting Your Wireless LAN ! speed basic-1.0 basic-2.0 basic-5.5 6.0 9.0 basic-11.0 12.0 18.0 24.0 36.0 48.0 54.0 rts...
Software Guide
Page 42
... auto speed auto bridge-group 1 no bridge-group 30 unicast-flooding bridge-group 30 spanning-disabled ! aaa group server radius dummy ! Cisco 3200 Series Wireless MIC Software Configuration Guide 8 Protecting Your Wireless LAN Configuring the WMIC for the First Time interface Dot11Radio0.30 encapsulation dot1Q 30 no ip route-cache bridge-group...
... auto speed auto bridge-group 1 no bridge-group 30 unicast-flooding bridge-group 30 spanning-disabled ! aaa group server radius dummy ! Cisco 3200 Series Wireless MIC Software Configuration Guide 8 Protecting Your Wireless LAN Configuring the WMIC for the First Time interface Dot11Radio0.30 encapsulation dot1Q 30 no ip route-cache bridge-group...
Software Guide
Page 43
... wpa interface Dot11Radio0 no ip address no ip route-cache bridge-group 40 ! ip http server ip http help-path http://www.cisco.com/warp/public/779/smbiz/prodconfig/help/eag /122-15.JA/1100 ip radius source-interface BVI1 radius-server attribute 32 include-in...135445415F59 radius-server authorization permit missing Service-Type radius-server vsa send accounting bridge 1 route ip ! Configuring the WMIC for the First Time Protecting Your Wireless LAN encryption vlan 40 mode ciphers tkip ! interface FastEthernet0.40 encapsulation dot1Q 40 no ip route-cache duplex auto speed auto bridge...
... wpa interface Dot11Radio0 no ip address no ip route-cache bridge-group 40 ! ip http server ip http help-path http://www.cisco.com/warp/public/779/smbiz/prodconfig/help/eag /122-15.JA/1100 ip radius source-interface BVI1 radius-server attribute 32 include-in...135445415F59 radius-server authorization permit missing Service-Type radius-server vsa send accounting bridge 1 route ip ! Configuring the WMIC for the First Time Protecting Your Wireless LAN encryption vlan 40 mode ciphers tkip ! interface FastEthernet0.40 encapsulation dot1Q 40 no ip route-cache duplex auto speed auto bridge...
Software Guide
Page 44
Protecting Your Wireless LAN Configuring the WMIC for the First Time Cisco 3200 Series Wireless MIC Software Configuration Guide 10
Protecting Your Wireless LAN Configuring the WMIC for the First Time Cisco 3200 Series Wireless MIC Software Configuration Guide 10
Software Guide
Page 54
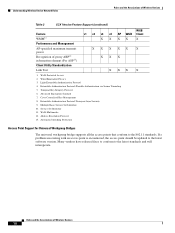
...Secure Tunneling 5. Temporal Key Integrity Protocol 6. Extensible Authentication Protocol-Transport layer Security 9. Address Resolution Protocol 13. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal Workgroup Bridges The universal workgroup bridge supports ...Wired Equivalent Privacy 3. Light Extensible Authentication Protocol 4. Cisco Centralized Key Management 8. Wi-Fi Multimedia 12. Many vendors have released fixes to conform to the 802.11 standards. Wi-Fi Protected Access 2. Multiple Basic Service Set Identifier 10. ...
...Secure Tunneling 5. Temporal Key Integrity Protocol 6. Extensible Authentication Protocol-Transport layer Security 9. Address Resolution Protocol 13. Automatic Switching Protection WGB X X X WGB Client X X X Access Point Support for Universal Workgroup Bridges The universal workgroup bridge supports ...Wired Equivalent Privacy 3. Light Extensible Authentication Protocol 4. Cisco Centralized Key Management 8. Wi-Fi Multimedia 12. Many vendors have released fixes to conform to the 802.11 standards. Wi-Fi Protected Access 2. Multiple Basic Service Set Identifier 10. ...
Software Guide
Page 69
... username and password. $ bridge(config)# Protecting Access to Privileged EXEC Commands A simple way of the banner text. Specifies the login message. To configure a login banner, follow these steps, beginning in this section, see the Cisco IOS Security Command Reference for the commands ...login prompt. Privilege levels define what commands users can configure a login banner to appear on all connected terminals. Administering the WMIC Protecting Access to Privileged EXEC Commands Configuring a Login Banner You can issue after they have logged into a network device. Verifies your ...
... username and password. $ bridge(config)# Protecting Access to Privileged EXEC Commands A simple way of the banner text. Specifies the login message. To configure a login banner, follow these steps, beginning in this section, see the Cisco IOS Security Command Reference for the commands ...login prompt. Privilege levels define what commands users can configure a login banner to appear on all connected terminals. Administering the WMIC Protecting Access to Privileged EXEC Commands Configuring a Login Banner You can issue after they have logged into a network device. Verifies your ...
Software Guide
Page 70
... global configuration command removes the enable password, but you are locked out of the EXEC mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 Default password is level 15 (privileged EXEC level). The default is Cisco. Protecting Access to Privileged EXEC Commands Administering the WMIC This section describes how to control access to...
... global configuration command removes the enable password, but you are locked out of the EXEC mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 6 Default password is level 15 (privileged EXEC level). The default is Cisco. Protecting Access to Privileged EXEC Commands Administering the WMIC This section describes how to control access to...
Software Guide
Page 71
...; If you configure the enable secret command, it allows spaces but ignores leading spaces. Enter abc. 2. Administering the WMIC Protecting Access to Privileged EXEC Commands To set or change a static enable password, follow these steps, beginning in the configuration file... Step 5 end show running-config copy running-config startup-config Purpose Enters global configuration mode. The password is Cisco. bridge(config)# enable password l1u2c3k4y5 Protecting Enable and Enable Secret Passwords with the Ctrl-V; that are stored on a Trivial File Transfer Protocol (TFTP) server...
...; If you configure the enable secret command, it allows spaces but ignores leading spaces. Enter abc. 2. Administering the WMIC Protecting Access to Privileged EXEC Commands To set or change a static enable password, follow these steps, beginning in the configuration file... Step 5 end show running-config copy running-config startup-config Purpose Enters global configuration mode. The password is Cisco. bridge(config)# enable password l1u2c3k4y5 Protecting Enable and Enable Secret Passwords with the Ctrl-V; that are stored on a Trivial File Transfer Protocol (TFTP) server...
Software Guide
Page 72
...that you can not reenter privileged EXEC mode. For more information, see the "Configuring Multiple Privilege Levels" section on page 10. Cisco 3200 Series Wireless MIC Software Configuration Guide 8 or Defines a secret password, which is saved using a nonreversible encryption method. •...configuration. By default, no password is defined. • (Optional) For encryption-type, only type 5, a Cisco proprietary encryption algorithm, is normal user EXEC mode privileges. Protecting Access to 15. To specify commands accessible at this level. The string cannot start with a number, it...
...that you can not reenter privileged EXEC mode. For more information, see the "Configuring Multiple Privilege Levels" section on page 10. Cisco 3200 Series Wireless MIC Software Configuration Guide 8 or Defines a secret password, which is saved using a nonreversible encryption method. •...configuration. By default, no password is defined. • (Optional) For encryption-type, only type 5, a Cisco proprietary encryption algorithm, is normal user EXEC mode privileges. Protecting Access to 15. To specify commands accessible at this level. The string cannot start with a number, it...
Software Guide
Page 73
...Note You must have defined privilege levels, you can also assign a specific privilege level (with associated rights and privileges) to 15. Cisco 3200 Series Wireless MIC Software Configuration Guide 9 To establish a username-based authentication system that a hidden password will follow. Enter 7 to...the last option specified in Step 2. The range is based on the WMIC. If you have at login time. Administering the WMIC Protecting Access to Privileged EXEC Commands This example shows how to lines or interfaces, and they authenticate each user. • For name, specify...
...Note You must have defined privilege levels, you can also assign a specific privilege level (with associated rights and privileges) to 15. Cisco 3200 Series Wireless MIC Software Configuration Guide 9 To establish a username-based authentication system that a hidden password will follow. Enter 7 to...the last option specified in Step 2. The range is based on the WMIC. If you have at login time. Administering the WMIC Protecting Access to Privileged EXEC Commands This example shows how to lines or interfaces, and they authenticate each user. • For name, specify...
Software Guide
Page 74
... spaces but ignores leading spaces. Verifies your entries in global configuration mode. Protecting Access to Privileged EXEC Commands Administering the WMIC Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of that command are automatically set to privilege level... specify the command to which you want to restrict access. The show running -config startup-config Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 10 Level 1 is from 0 to the configure command, you set them individually to...
... spaces but ignores leading spaces. Verifies your entries in global configuration mode. Protecting Access to Privileged EXEC Commands Administering the WMIC Configuring Multiple Privilege Levels By default, the Cisco IOS software has two modes of that command are automatically set to privilege level... specify the command to which you want to restrict access. The show running -config startup-config Purpose Enters global configuration mode. Cisco 3200 Series Wireless MIC Software Configuration Guide 10 Level 1 is from 0 to the configure command, you set them individually to...
Software Guide
Page 75
Protecting the Wireless LAN Configure security settings to prevent unauthorized access to your building. For level, the range is from 0 to 15. Without VLANs, encryption settings (... (WPA) authentication cannot be created because of your network. You can be used on the wireless LAN. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 Administering the WMIC Protecting the Wireless LAN This example shows how to set identifiers (SSIDs) that are not broadcast in to a specified privilege level. Because it...
Protecting the Wireless LAN Configure security settings to prevent unauthorized access to your building. For level, the range is from 0 to 15. Without VLANs, encryption settings (... (WPA) authentication cannot be created because of your network. You can be used on the wireless LAN. Cisco 3200 Series Wireless MIC Software Configuration Guide 11 Administering the WMIC Protecting the Wireless LAN This example shows how to set identifiers (SSIDs) that are not broadcast in to a specified privilege level. Because it...