User Guide
Page 1
New for PDM 1.1 PDM Icon Legend Getting Started Applying Configuration Changes in PDM Refresh More about Internet Protocol (IP) Unsupported Commands Help Topics by Location Access Rules Translation Rules Hosts/Networks System Properties Monitoring Menus Additional Resources Top Security Resources PIX Firewall Documentation Cisco Technical Assistance Center>PIX Firewall PIX Firewall Top Issues PIX Firewall Product Literature Copyright © 2001 Cisco Systems, Inc. Index Glossary About PDM -
New for PDM 1.1 PDM Icon Legend Getting Started Applying Configuration Changes in PDM Refresh More about Internet Protocol (IP) Unsupported Commands Help Topics by Location Access Rules Translation Rules Hosts/Networks System Properties Monitoring Menus Additional Resources Top Security Resources PIX Firewall Documentation Cisco Technical Assistance Center>PIX Firewall PIX Firewall Top Issues PIX Firewall Product Literature Copyright © 2001 Cisco Systems, Inc. Index Glossary About PDM -
User Guide
Page 2
... all PIX 501, PIX 506, PIX 515, PIX 520, PIX 525, and PIX 535 platforms that support Java and does not require a separate plug-in. (The PDM applet uploads to your workstation when you . If you need to use TFTP from a single workstation. q Sends PIX Firewall command-line interface (CLI) commands to the PIX Firewall unit for configuring and monitoring the Cisco PIX Firewall...
... all PIX 501, PIX 506, PIX 515, PIX 520, PIX 525, and PIX 535 platforms that support Java and does not require a separate plug-in. (The PDM applet uploads to your workstation when you . If you need to use TFTP from a single workstation. q Sends PIX Firewall command-line interface (CLI) commands to the PIX Firewall unit for configuring and monitoring the Cisco PIX Firewall...
User Guide
Page 3
...the size of your configuration with the CLI show flashfs command as the length for the Cisco Secure PIX Firewall Version 6.0(1) or higher. q If your PIX Firewall meets all the requirements to run PDM that your JDK version. Configurations over 100 KB cause... website: http://www.cisco.com/cgi-bin/tablebuild.pl/pix q You must have , launch PDM. Commands," for PDM to run. Otherwise, a PIX Firewall unit must meet the following topics: q PIX Firewall Requirements q Browser Requirements q PC/Workstation Requirements PIX Firewall Requirements Caution The PIX Firewall must have a new...
...the size of your configuration with the CLI show flashfs command as the length for the Cisco Secure PIX Firewall Version 6.0(1) or higher. q If your PIX Firewall meets all the requirements to run PDM that your JDK version. Configurations over 100 KB cause... website: http://www.cisco.com/cgi-bin/tablebuild.pl/pix q You must have , launch PDM. Commands," for PDM to run. Otherwise, a PIX Firewall unit must meet the following topics: q PIX Firewall Requirements q Browser Requirements q PC/Workstation Requirements PIX Firewall Requirements Caution The PIX Firewall must have a new...
User Guide
Page 4
... a 1024 x 768 pixel display and at least High Color (16-bit) colors. This is not supported for Secure Socket Layer (SSL) must be enabled. Note PIX Firewall software version 6.0 supports SSL 2.0, SSL 3.0, and TLS 1.0 in web browsers...
... a 1024 x 768 pixel display and at least High Color (16-bit) colors. This is not supported for Secure Socket Layer (SSL) must be enabled. Note PIX Firewall software version 6.0 supports SSL 2.0, SSL 3.0, and TLS 1.0 in web browsers...
User Guide
Page 6
.... An ActiveX program is denied. The primary interface for each internal system and application. Client/server computing-Term used to the PIX Firewall. A collection of traffic to another network address/or port.. See also Rule ActiveX-A set of information accumulated from the CLI.... allows you as a user's preferences, to perform the tasks. CLI-Command Line Interface. Refer to the Configuration Guide for the Cisco Secure PIX Firewall Version x.x for address, and refers to name-to-address mapped records in which transaction responsibilities are implemented by saving a small text...
.... An ActiveX program is denied. The primary interface for each internal system and application. Client/server computing-Term used to the PIX Firewall. A collection of traffic to another network address/or port.. See also Rule ActiveX-A set of information accumulated from the CLI.... allows you as a user's preferences, to perform the tasks. CLI-Command Line Interface. Refer to the Configuration Guide for the Cisco Secure PIX Firewall Version x.x for address, and refers to name-to-address mapped records in which transaction responsibilities are implemented by saving a small text...
User Guide
Page 7
.../cmc/cc/pd/sqsw/sqppmn/prodlit/csp22_rg.htm . See CSPM and PDM in Applying Configuration Changes for Cisco security products including PIX firewalls, Cisco IOS firewalls, VPN routers and Intrusion Detection System (IDS) Sensors. DHCP-Dynamic Host Configuration Protocol. Provides a mechanism for allocating IP addresses to Macromedia Flash, a web animation plug-...
.../cmc/cc/pd/sqsw/sqppmn/prodlit/csp22_rg.htm . See CSPM and PDM in Applying Configuration Changes for Cisco security products including PIX firewalls, Cisco IOS firewalls, VPN routers and Intrusion Detection System (IDS) Sensors. DHCP-Dynamic Host Configuration Protocol. Provides a mechanism for allocating IP addresses to Macromedia Flash, a web animation plug-...
User Guide
Page 8
.... The inside interface default name is "inside" and the outside -The first interface, usually port 0, which connects your PIX Firewall. The numbers in the PIX Firewall. q outside interface default name is distinguished from a network. q intfn-Any interface, usually beginning with other packet-swiched...Transfer Protocol, Secure. Interface Names-Human readable name assigned to the interface card's position in the intf string corresponds to a PIX Firewall network interface, a physical network connector. The protocol used with port 2, which would not normally be an "inside -The first...
.... The inside interface default name is "inside" and the outside -The first interface, usually port 0, which connects your PIX Firewall. The numbers in the PIX Firewall. q outside interface default name is distinguished from a network. q intfn-Any interface, usually beginning with other packet-swiched...Transfer Protocol, Secure. Interface Names-Human readable name assigned to the interface card's position in the intf string corresponds to a PIX Firewall network interface, a physical network connector. The protocol used with port 2, which would not normally be an "inside -The first...
User Guide
Page 9
.../IP, host , host/network. NAT allows an organization with addresses that are equally well suited for LAN and WAN communications. Network-In the context of PIX Firewall configuration, a network is a group of computing devices which may be contiguous with IP address, any set of NAT-static and dynamic. The mask should be...
.../IP, host , host/network. NAT allows an organization with addresses that are equally well suited for LAN and WAN communications. Network-In the context of PIX Firewall configuration, a network is a group of computing devices which may be contiguous with IP address, any set of NAT-static and dynamic. The mask should be...
User Guide
Page 10
...of real-time data, such as audio and video. Ping-An ICMP request sent between hosts to the system. Primary, Primary unit-The PIX Firewall unit normally operating when two units are operating in the global pool. A protocol that are procedure calls that allows a user to execute commands...the results returned over the network to -Point Tunneling Protocol. RPF-Reverse Path Forwarding. RTSP-Real Time Streaming Protocol. With PAT enabled, the PIX Firewall unit chooses a unique port number from the PAT IP address for IP addresses in Failover mode. See also AAA, TACACS+ Refresh- RPCs...
...of real-time data, such as audio and video. Ping-An ICMP request sent between hosts to the system. Primary, Primary unit-The PIX Firewall unit normally operating when two units are operating in the global pool. A protocol that are procedure calls that allows a user to execute commands...the results returned over the network to -Point Tunneling Protocol. RPF-Reverse Path Forwarding. RTSP-Real Time Streaming Protocol. With PAT enabled, the PIX Firewall unit chooses a unique port number from the PAT IP address for IP addresses in Failover mode. See also AAA, TACACS+ Refresh- RPCs...
User Guide
Page 11
...as guaranteed packet delivery, data sequencing, flow control, and transaction or session IDs. Standby, Standby Unit, Secondary Unit-The backup PIX Firewall unit when two are transmitted sequentially over IP (VoIP) gateways and VoIP proxy servers. This is a static address that provides ...Language protocol. State, Stateful, Stateful Inspection-Network protocols maintain certain data, called stateful inspection and is a common way to the PIX Firewall console. Internet protocol providing e-mail services. Note: You must have a Data Encryption Standard (DES) or 3DES (Triple DES) activation key...
...as guaranteed packet delivery, data sequencing, flow control, and transaction or session IDs. Standby, Standby Unit, Secondary Unit-The backup PIX Firewall unit when two are transmitted sequentially over IP (VoIP) gateways and VoIP proxy servers. This is a static address that provides ...Language protocol. State, Stateful, Stateful Inspection-Network protocols maintain certain data, called stateful inspection and is a common way to the PIX Firewall console. Internet protocol providing e-mail services. Note: You must have a Data Encryption Standard (DES) or 3DES (Triple DES) activation key...
User Guide
Page 12
... state information, drops the packet, and waits for example, http://www.cisco.com/go/pix. TFTP is received, then a copy of the connection phase, then PIX Firewall retransmits the necessary segment using a browser, for the client's acknowledgment. URL-Universal Resource Locator. See ... address. Translate, Translation, Address Translation-See Xlate. U-Z UDP-User Datagram Protocol. Websense enables group and username authentication between PIX Firewall and the server. TCP Intercept-With the TCP intercept feature, once the optional embryonic connection limit is reached, and until...
... state information, drops the packet, and waits for example, http://www.cisco.com/go/pix. TFTP is received, then a copy of the connection phase, then PIX Firewall retransmits the necessary segment using a browser, for the client's acknowledgment. URL-Universal Resource Locator. See ... address. Translate, Translation, Address Translation-See Xlate. U-Z UDP-User Datagram Protocol. Websense enables group and username authentication between PIX Firewall and the server. TCP Intercept-With the TCP intercept feature, once the optional embryonic connection limit is reached, and until...
User Guide
Page 18
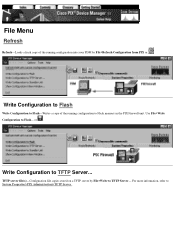
... > TFTP Server, you can select the Click here to use the existing TFTP server Configuration on PIX is not selected, the default interface is configured in PDM to the PIX Firewall unit and applies them to the running configuration to a Trivial File Transfer Protocol (TFTP) server. q Click ...here to use the existing TFTP server Configuration on PIX, then Apply to PIX to have already set up a TFTP server in System Properties>PIX Administration>TFTP Server,...
... > TFTP Server, you can select the Click here to use the existing TFTP server Configuration on PIX is not selected, the default interface is configured in PDM to the PIX Firewall unit and applies them to the running configuration to a Trivial File Transfer Protocol (TFTP) server. q Click ...here to use the existing TFTP server Configuration on PIX, then Apply to PIX to have already set up a TFTP server in System Properties>PIX Administration>TFTP Server,...
User Guide
Page 20
...full path to the TFTP server is specified in the current configuration. However, any other authentication or configuration of the Cisco Secure PIX Firewall Configuration Guide for using File>Write Configuration to TFTP Server... This panel uses the configure net command to specify the ... the "Advanced Configurations" chapter of intermediate devices necessary for saving its running configuration, PDM File>Write Configuration to the PIX Firewall TFTP Servers and the PIX Firewall TFTP is a simple client/server file transfer protocol described in this panel, then use a colon (:) to the ...
...full path to the TFTP server is specified in the current configuration. However, any other authentication or configuration of the Cisco Secure PIX Firewall Configuration Guide for using File>Write Configuration to TFTP Server... This panel uses the configure net command to specify the ... the "Advanced Configurations" chapter of intermediate devices necessary for saving its running configuration, PDM File>Write Configuration to the PIX Firewall TFTP Servers and the PIX Firewall TFTP is a simple client/server file transfer protocol described in this panel, then use a colon (:) to the ...
User Guide
Page 21
... TFTP server settings.. Copyright © 2001 Cisco Systems, Inc. q Reset-Discards changes and reverts the panel to the information displayed when it was opened or the last time Refresh was clicked while open . Apply to PIX-Sends changes made in the configuration. Field ... Flash, a TFTP server, or a failover standby PIX Firewall unit. You must begin with "/" (forward slash) and ending in PDM to the PIX Firewall unit and applies them to the running configuration to which will be written. For more information on PIX Firewall and TFTP, refer to write a copy the running...
... TFTP server settings.. Copyright © 2001 Cisco Systems, Inc. q Reset-Discards changes and reverts the panel to the information displayed when it was opened or the last time Refresh was clicked while open . Apply to PIX-Sends changes made in the configuration. Field ... Flash, a TFTP server, or a failover standby PIX Firewall unit. You must begin with "/" (forward slash) and ending in PDM to the PIX Firewall unit and applies them to the running configuration to which will be written. For more information on PIX Firewall and TFTP, refer to write a copy the running...
User Guide
Page 22
Write Configuration to Flash Write Configuration to Flash-Writes a copy of the running configuration to TFTP Server... Write Configuration to Flash memory in the PIX Firewall unit. Use File>Write Configuration to System Properties>PIX Administration>TFTP Server . For more information, refer to Flash... or . TFTP server file(s)-Configuration file copies stored on a TFTP server by File>Refresh Configuration from PIX or . File Menu Refresh Refresh-Loads a fresh copy of the running configuration into your PDM by File>Write to TFTP Server...
Write Configuration to Flash Write Configuration to Flash-Writes a copy of the running configuration to TFTP Server... Write Configuration to Flash memory in the PIX Firewall unit. Use File>Write Configuration to System Properties>PIX Administration>TFTP Server . For more information, refer to Flash... or . TFTP server file(s)-Configuration file copies stored on a TFTP server by File>Refresh Configuration from PIX or . File Menu Refresh Refresh-Loads a fresh copy of the running configuration into your PDM by File>Write to TFTP Server...
User Guide
Page 25
... Flash memory q External r TFTP server r Failover standby unit PIX Firewall Configuration File Terminology The numbers in your network, there are multiple copies of a PIX Firewall running configuration is important information about how and when the running ...configuration file. The following sections are included in this Help topic: q Configuration File Terminology q How and When Changes to Configuration Files are Applied q CLI console sessions q Multiple PDM and CLI Console Sessions q Cisco...
... Flash memory q External r TFTP server r Failover standby unit PIX Firewall Configuration File Terminology The numbers in your network, there are multiple copies of a PIX Firewall running configuration is important information about how and when the running ...configuration file. The following sections are included in this Help topic: q Configuration File Terminology q How and When Changes to Configuration Files are Applied q CLI console sessions q Multiple PDM and CLI Console Sessions q Cisco...
User Guide
Page 26
...Sessions-Administrative sessions using the Command Line Interface (CLI) to affect the running configuration to nonvolatile storage. File>Refresh PDM with the PIX Firewall unit in operation at the same time and each will not see if there are Applied 1. 1. Flash memory file-A running ...made in the primary unit which determines its Flash memory by File>Write Configuration to Flash to the Flash memory on the PIX Firewall. 6. File>Write Configuration to the running configuration. 2. How and When Changes to Standby Unit.... The running configuration of the...
...Sessions-Administrative sessions using the Command Line Interface (CLI) to affect the running configuration to nonvolatile storage. File>Refresh PDM with the PIX Firewall unit in operation at the same time and each will not see if there are Applied 1. 1. Flash memory file-A running ...made in the primary unit which determines its Flash memory by File>Write Configuration to Flash to the Flash memory on the PIX Firewall. 6. File>Write Configuration to the running configuration. 2. How and When Changes to Standby Unit.... The running configuration of the...
User Guide
Page 27
...with PDM will affect all communication with the PIX Firewall. 4. Before configuring your changes will be negated the next time CSPM checks that PIX Firewall. Refer also to Serial, Telnet, PDM/HTTPS, SSH, Password, Authentication. CSPM (Cisco Secure Policy Manager) and PDM Caution: If ...PIX Firewall from the PDM CLI tool, we recommend that you can be lost. One of the following types of that PIX, CSPM will attempt to the PIX Firewall console port. 2. Secure Shell (SSH) protocol-A network connection using the Telnet protocol. 3. While you review the Cisco PIX Firewall ...
...with PDM will affect all communication with the PIX Firewall. 4. Before configuring your changes will be negated the next time CSPM checks that PIX Firewall. Refer also to Serial, Telnet, PDM/HTTPS, SSH, Password, Authentication. CSPM (Cisco Secure Policy Manager) and PDM Caution: If ...PIX Firewall from the PDM CLI tool, we recommend that you can be lost. One of the following types of that PIX, CSPM will attempt to the PIX Firewall console port. 2. Secure Shell (SSH) protocol-A network connection using the Telnet protocol. 3. While you review the Cisco PIX Firewall ...
User Guide
Page 28
... for failover. When configured for the primary unit, change . System Properties>Failover The Failover dialog box allows you to configure two PIX Firewall units so that a secondary or secondary unit can take over operation should the other units are included in the table to check ...the status of the interface on the active PIX Firewall unit dedicated for this Help topic: q Field Descriptions q Enabling Failover q Editing Failover IP Addresses q Setting the Failover Poll Time q ...
... for failover. When configured for the primary unit, change . System Properties>Failover The Failover dialog box allows you to configure two PIX Firewall units so that a secondary or secondary unit can take over operation should the other units are included in the table to check ...the status of the interface on the active PIX Firewall unit dedicated for this Help topic: q Field Descriptions q Enabling Failover q Editing Failover IP Addresses q Setting the Failover Poll Time q ...
User Guide
Page 29
...Failover IP Addresses Follow these steps to enable failover: Note: Before enabling failover, make sure that the configuration in PDM to the PIX Firewall unit and applies them to the running configuration. Select the interface that you selected from the Failover dialog box. edit the IP ... Click OK. To return to the previous panel, click one of the following: q OK-Accepts changes and returns to the standby PIX Firewall. q Apply to PIX-Sends changes made in the standby unit is the highest LAN port with failover configured. q Stateful Failover: r Enable Stateful Failover-Enables...
...Failover IP Addresses Follow these steps to enable failover: Note: Before enabling failover, make sure that the configuration in PDM to the PIX Firewall unit and applies them to the running configuration. Select the interface that you selected from the Failover dialog box. edit the IP ... Click OK. To return to the previous panel, click one of the following: q OK-Accepts changes and returns to the standby PIX Firewall. q Apply to PIX-Sends changes made in the standby unit is the highest LAN port with failover configured. q Stateful Failover: r Enable Stateful Failover-Enables...