Administration Guide
Page 9
.... 1.1.2. Many gateways may include a firmware upgrade or configuration modification to operate in his personal information including billing information. CDR (call . Gateways also behave like any update of the call detail record) data are used for forwarding packets received on the subscriber's choice of tag/value pairs. The PHONE ADAPTER can be...
.... 1.1.2. Many gateways may include a firmware upgrade or configuration modification to operate in his personal information including billing information. CDR (call . Gateways also behave like any update of the call detail record) data are used for forwarding packets received on the subscriber's choice of tag/value pairs. The PHONE ADAPTER can be...
Administration Guide
Page 10
.../institutional LAN or by the Service Provider before it contains authentication (password/user name ID / number) information for the unit to download an updated profile. ADAPTER unit is shipped from the subscriber's home network - This type of an IVR system (accessed through an attached telephone set and... business Local Area Network (LAN) - The unit must be provisioned in that an Unprovisioned unit can be provisioned simultaneously and updated periodically. This access can be controlled with this basic information by the residential subscriber who is a "power user." 1.1.3.
.../institutional LAN or by the Service Provider before it contains authentication (password/user name ID / number) information for the unit to download an updated profile. ADAPTER unit is shipped from the subscriber's home network - This type of an IVR system (accessed through an attached telephone set and... business Local Area Network (LAN) - The unit must be provisioned in that an Unprovisioned unit can be provisioned simultaneously and updated periodically. This access can be controlled with this basic information by the residential subscriber who is a "power user." 1.1.3.
Administration Guide
Page 20
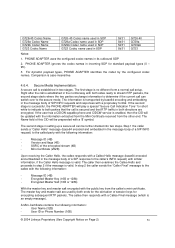
...Please check to make sure that you have the following steps to install the PHONE ADAPTER. Ethernet Cable 3. 5 Volt (PAP2) or 12 Volt (RT31P2) Power Adapter 4. Ensure that device without requiring a reboot. © 2004 Linksys Proprietary (See Copyright Notice on power up the PHONE ADAPTER. 3.... these parameters. Access to an analog telephone or fax machine. 3. From the rear Side of the cable to initiate or complete a profile update or firmware upgrade. Insert a standard RJ-11 telephone cable into the Phone 1 port.2. You may trigger a software reboot. Linksys recommends that...
...Please check to make sure that you have the following steps to install the PHONE ADAPTER. Ethernet Cable 3. 5 Volt (PAP2) or 12 Volt (RT31P2) Power Adapter 4. Ensure that device without requiring a reboot. © 2004 Linksys Proprietary (See Copyright Notice on power up the PHONE ADAPTER. 3.... these parameters. Access to an analog telephone or fax machine. 3. From the rear Side of the cable to initiate or complete a profile update or firmware upgrade. Insert a standard RJ-11 telephone cable into the Phone 1 port.2. You may trigger a software reboot. Linksys recommends that...
Administration Guide
Page 54
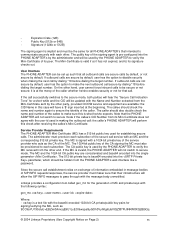
... both sides ready to stream RTP packets, the second stage starts where the two parties exchange information to determine if the current call can be updated with similar information, if the Caller Hello message is case-insensitive. 4.6.4. For dynamic payload types, PHONE ADAPTER identifies the codec by base64 encoding and embedding...
... both sides ready to stream RTP packets, the second stage starts where the two parties exchange information to determine if the current call can be updated with similar information, if the Caller Hello message is case-insensitive. 4.6.4. For dynamic payload types, PHONE ADAPTER identifies the codec by base64 encoding and embedding...
Administration Guide
Page 55
...'s CID Number from the Mini-Certificate sent by the other end. The public key of the callee to the secure mode, both parties will be updated with the base64 encoded 1024-bit CA private/public key pairs for all outbound calls are available: the CID Name in message bodies of MC...
...'s CID Number from the Mini-Certificate sent by the other end. The public key of the callee to the secure mode, both parties will be updated with the base64 encoded 1024-bit CA private/public key pairs for all outbound calls are available: the CID Name in message bodies of MC...
Administration Guide
Page 77
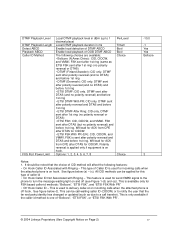
... following choices are available: • Bellcore (N.Amer,China): CID, CIDCW, and VMWI. This can be noted that the far end party identity has changed or updated (such as ETSI FSK sent after 1st ring (same as due to a call waiting caller ID (CIDCW) or to delivery caller-id on Page 2) 77...
... following choices are available: • Bellcore (N.Amer,China): CID, CIDCW, and VMWI. This can be noted that the far end party identity has changed or updated (such as ETSI FSK sent after 1st ring (same as due to a call waiting caller ID (CIDCW) or to delivery caller-id on Page 2) 77...
Administration Guide
Page 99
... choice of CID method will offer using third-party-call transfer). This feature can be noted that the far end party identity has changed or updated (such as due to a call -control, the following features: • On Hook Caller ID Associated with third-party-call is useful for send VMWI signal...
... choice of CID method will offer using third-party-call transfer). This feature can be noted that the far end party identity has changed or updated (such as due to a call -control, the following features: • On Hook Caller ID Associated with third-party-call is useful for send VMWI signal...