User Manual
Page 9
... network, when emails are sent to their destination, or when you have to connect to your company's network when you are called the DHCP client. With this flexibility, however, comes an increased risk in "Chapter 6: The Router's Web-based Utility." DHCP frees you from having to assign... IP addresses manually every time a new user is your Wireless Network 5 Why do I need a VPN? But what do you do I need a VPN? How is added to a device on the network or another network device, such as PCs and print servers. Wireless...
... network, when emails are sent to their destination, or when you have to connect to your company's network when you are called the DHCP client. With this flexibility, however, comes an increased risk in "Chapter 6: The Router's Web-based Utility." DHCP frees you from having to assign... IP addresses manually every time a new user is your Wireless Network 5 Why do I need a VPN? But what do you do I need a VPN? How is added to a device on the network or another network device, such as PCs and print servers. Wireless...
User Manual
Page 11
...were physically connected. His router is configured with the built-in effect, operates as if you must have a second VPN Router or a computer with VPN client software that supports IPSec. Virtual Private Networking can be used to "Appendix C: Configuring IPSec between a Windows 2000 or... XP PC and the VPN Router"). A computer with VPN client software that supports IPSec can connect to a VPN Router using IPSec (refer to create secure networks linking a central office with branch offices, telecommuters, ...
...were physically connected. His router is configured with the built-in effect, operates as if you must have a second VPN Router or a computer with VPN client software that supports IPSec. Virtual Private Networking can be used to "Appendix C: Configuring IPSec between a Windows 2000 or... XP PC and the VPN Router"). A computer with VPN client software that supports IPSec can connect to a VPN Router using IPSec (refer to create secure networks linking a central office with branch offices, telecommuters, ...
User Manual
Page 12
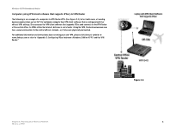
... Figure 2-3.) In her hotel room, a traveling businesswoman dials up her office's VPN settings. Wireless-G VPN Broadband Router Computer (using VPN client software that supports IPSec) to VPN Router The following is not a factor. She accesses the VPN client software that supports IPSec and connects to the VPN Router at www.linksys.com or refer to "Appendix C: Configuring IPSec...
... Figure 2-3.) In her hotel room, a traveling businesswoman dials up her office's VPN settings. Wireless-G VPN Broadband Router Computer (using VPN client software that supports IPSec) to VPN Router The following is not a factor. She accesses the VPN client software that supports IPSec and connects to the VPN Router at www.linksys.com or refer to "Appendix C: Configuring IPSec...
User Manual
Page 18
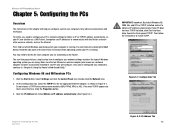
... by clicking the Start button. Click the Properties button. 3. Configuring Windows 98 and Millennium PCs 1. You can function as a DHCP client. Figure 5-1: Configuration Tab Chapter 5: Configuring the PCs Overview Figure 5-2: IP Address Tab 14 Make sure that line. If your network ...IP addresses to the Router. Double-click the Network icon. 2. Search for the applicable Ethernet adapter, as the Internet. Wireless-G VPN Broadband Router Chapter 5: Configuring the PCs Overview The instructions in this chapter will configure. Click the IP Address tab. Then follow ...
... by clicking the Start button. Click the Properties button. 3. Configuring Windows 98 and Millennium PCs 1. You can function as a DHCP client. Figure 5-1: Configuration Tab Chapter 5: Configuring the PCs Overview Figure 5-2: IP Address Tab 14 Make sure that line. If your network ...IP addresses to the Router. Double-click the Network icon. 2. Search for the applicable Ethernet adapter, as the Internet. Wireless-G VPN Broadband Router Chapter 5: Configuring the PCs Overview The instructions in this chapter will configure. Click the IP Address tab. Then follow ...
User Manual
Page 31
... wireless products, enter the WEP key manually on the non-Linksys wireless products.) After you are using the same key. • WEP Encryption. When wireless clients survey the local area for every data transmission. To broadcast the Router's SSID, keep the default setting, Disabled. If you want to use an identical... characters are not using 64-bit WEP encryption, then the key must use , 64-bit 10 hex digits or 128-bit 26 hex digits. Wireless-G VPN Broadband Router Wireless Security • Wireless SSID Broadcast.
... wireless products, enter the WEP key manually on the non-Linksys wireless products.) After you are using the same key. • WEP Encryption. When wireless clients survey the local area for every data transmission. To broadcast the Router's SSID, keep the default setting, Disabled. If you want to use an identical... characters are not using 64-bit WEP encryption, then the key must use , 64-bit 10 hex digits or 128-bit 26 hex digits. Wireless-G VPN Broadband Router Wireless Security • Wireless SSID Broadcast.
User Manual
Page 33
...System or Shared Key authentication to synchronize the wireless network. • DTIM Interval The default value is a countdown field informing clients of a data frame. The Beacon Interval value indicates the frequency interval of this screen you encounter inconsistent data flow, only ...broadcast and multicast messages. • RTS Threshold This value should remain at its default setting of your wireless network. Wireless-G VPN Broadband Router Advanced Wireless Settings (See Figure 6-15.) On this value are recommended. The default transmission rate is fragmented into...
...System or Shared Key authentication to synchronize the wireless network. • DTIM Interval The default value is a countdown field informing clients of a data frame. The Beacon Interval value indicates the frequency interval of this screen you encounter inconsistent data flow, only ...broadcast and multicast messages. • RTS Threshold This value should remain at its default setting of your wireless network. Wireless-G VPN Broadband Router Advanced Wireless Settings (See Figure 6-15.) On this value are recommended. The default transmission rate is fragmented into...
User Manual
Page 35
...(s) on the remote end of the tunnel that the data or information between two remote locations. The IP Address may either be another VPN Router, a VPN Server, or a computer with VPN client software that basically creates a secure connection between these endpoints is a suite of protocols used by to -Point Tunneling Protocol Passthrough is the...
...(s) on the remote end of the tunnel that the data or information between two remote locations. The IP Address may either be another VPN Router, a VPN Server, or a computer with VPN client software that basically creates a secure connection between these endpoints is a suite of protocols used by to -Point Tunneling Protocol Passthrough is the...
User Manual
Page 41
Any PC whose port is being forwarded must have its DHCP client function disabled and must have a new static IP address assigned to it because its IP address may not require any applications that use for each ....) When users send this tab, click the Save Settings button to save these changes, or click the Cancel Changes button to undo your changes. Wireless-G VPN Broadband Router The Applications and Gaming Tab Port Range Forwarding The Port Forwarding screen sets up public services on this type of request to your...
Any PC whose port is being forwarded must have its DHCP client function disabled and must have a new static IP address assigned to it because its IP address may not require any applications that use for each ....) When users send this tab, click the Save Settings button to save these changes, or click the Cancel Changes button to undo your changes. Wireless-G VPN Broadband Router The Applications and Gaming Tab Port Range Forwarding The Port Forwarding screen sets up public services on this type of request to your...
User Manual
Page 50
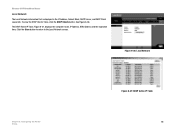
Click the Close button to return to the Local Network screen. The DHCP Active IP Table, Figure 6-37, displays the computer name, IP Address, MAC Address and the expiration time. To view the DHCP Clients Table, click the DHCP Clients button. Figure 6-36: Local Network Chapter 6: Configuring the Router Status Figure 6-37: DHCP Active IP Table 46 See Figure 6-36. Wireless-G VPN Broadband Router Local Network The Local Network information that is displayed is the IP Address, Subnet Mask, DHCP Server, and DHCP Client Lease Info.
Click the Close button to return to the Local Network screen. The DHCP Active IP Table, Figure 6-37, displays the computer name, IP Address, MAC Address and the expiration time. To view the DHCP Clients Table, click the DHCP Clients button. Figure 6-36: Local Network Chapter 6: Configuring the Router Status Figure 6-37: DHCP Active IP Table 46 See Figure 6-36. Wireless-G VPN Broadband Router Local Network The Local Network information that is displayed is the IP Address, Subnet Mask, DHCP Server, and DHCP Client Lease Info.
User Manual
Page 61
... key connect at this single address provided by the ISP. What do I am behind the Router. How do ? The default client port for setup, configuration or troubleshooting of the Router. Wireless-G VPN Broadband Router Does the Internet connection of your broadband connection. The Router also supports 100Mbps over the auto-sensing Fast...
... key connect at this single address provided by the ISP. What do I am behind the Router. How do ? The default client port for setup, configuration or troubleshooting of the Router. Wireless-G VPN Broadband Router Does the Internet connection of your broadband connection. The Router also supports 100Mbps over the auto-sensing Fast...
User Manual
Page 62
...a connection. downloads are corrupt, or nothing but the Router's setup pages are experiencing corrupted files when you download a file with your FTP client, try using another FTP program. Reset the Router by powering the unit off . Reset your cable or DSL modem by holding down the ...com for Macintosh. To upgrade the Router's firmware, use . Check with 1.0.1.3). For Netscape Navigator, click Edit, Preferences, Advanced, and Proxy. Wireless-G VPN Broadband Router the same time, even if on the same LAN (not a problem with your browser documentation, and make sure that your browser is ...
...a connection. downloads are corrupt, or nothing but the Router's setup pages are experiencing corrupted files when you download a file with your FTP client, try using another FTP program. Reset the Router by powering the unit off . Reset your cable or DSL modem by holding down the ...com for Macintosh. To upgrade the Router's firmware, use . Check with 1.0.1.3). For Netscape Navigator, click Edit, Preferences, Advanced, and Proxy. Wireless-G VPN Broadband Router the same time, even if on the same LAN (not a problem with your browser documentation, and make sure that your browser is ...