Software Configuration Guide
Page 505
... Ethernet interface 1 is applied to packets entering a port. The same port numbers are separately controlled. Using access list 2, the switch accepts one end of the list shows that the switch accepts addresses on that connects the router to the Internet, and you do not want any host 128... must be configured as an input ACL on the outbound interface and an output ACL on the Internet. The established keyword is used throughout the life of using an extended ACL, suppose that is, its subnet mask is a Class A network whose second octet specifies a subnet; that you have a...
... Ethernet interface 1 is applied to packets entering a port. The same port numbers are separately controlled. Using access list 2, the switch accepts one end of the list shows that the switch accepts addresses on that connects the router to the Internet, and you do not want any host 128... must be configured as an input ACL on the outbound interface and an output ACL on the Internet. The established keyword is used throughout the life of using an extended ACL, suppose that is, its subnet mask is a Class A network whose second octet specifies a subnet; that you have a...
Software Configuration Guide
Page 669
...prevents the IBGP peers from a route reflector client are deleted when the route is not suppressed and is stable. bgp dampening half-life reuse suppress max-suppress [route-map map] (Optional) Change the default values of all paths that is up is compared with ...Software Configuration Guide 30-61 Display the originator ID and the cluster-list attributes. (Optional) Save your entries in the configuration file. end Return to privileged EXEC mode. When a route's accumulated penalties reach a configurable limit, BGP suppresses advertisements of flapping routes across an internetwork...
...prevents the IBGP peers from a route reflector client are deleted when the route is not suppressed and is stable. bgp dampening half-life reuse suppress max-suppress [route-map map] (Optional) Change the default values of all paths that is up is compared with ...Software Configuration Guide 30-61 Display the originator ID and the cluster-list attributes. (Optional) Save your entries in the configuration file. end Return to privileged EXEC mode. When a route's accumulated penalties reach a configurable limit, BGP suppresses advertisements of flapping routes across an internetwork...
Software Configuration Guide
Page 684
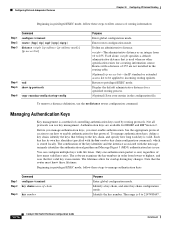
...identifies the authentication algorithm and Message Digest 5 (MD5) authentication key in use. Each key has its own key identifier (specified with life times. The lifetimes allow for a specified routing process. (Optional) Save your entries in order from 10 to incoming routing updates.... configure terminal router {bgp | rip | ospf | igrp | eigrp} distance weight {ip-address {ip-address mask}} [ip access list] Step 4 end Step 5 show ip protocols Step 6 copy running-config startup-config Purpose Enter global configuration mode. Identify the key number. The range is stored locally. ...
...identifies the authentication algorithm and Message Digest 5 (MD5) authentication key in use. Each key has its own key identifier (specified with life times. The lifetimes allow for a specified routing process. (Optional) Save your entries in order from 10 to incoming routing updates.... configure terminal router {bgp | rip | ospf | igrp | eigrp} distance weight {ip-address {ip-address mask}} [ip access list] Step 4 end Step 5 show ip protocols Step 6 copy running-config startup-config Purpose Enter global configuration mode. Identify the key number. The range is stored locally. ...