HP Client Manager 6.1
Page 3
...client computers, you to upgrade the BIOS firmware on the HPCM Server. When one of these events using one of the pre-configured reports. • Diagnostic information: Client diagnostics are returned from the Altiris Console on client computers. System software installation: HPCM ...and highest-quality system software. There are three classes of information that our customers have specified, such as new or missing PCs, memory, battery, disk drives, CPUs, and monitors. SoftPaqs SoftPaqs are Web-downloadable software packages made available by each client machine and...
...client computers, you to upgrade the BIOS firmware on the HPCM Server. When one of these events using one of the pre-configured reports. • Diagnostic information: Client diagnostics are returned from the Altiris Console on client computers. System software installation: HPCM ...and highest-quality system software. There are three classes of information that our customers have specified, such as new or missing PCs, memory, battery, disk drives, CPUs, and monitors. SoftPaqs SoftPaqs are Web-downloadable software packages made available by each client machine and...
HP Client Manager 6.1
Page 6
HPCM block diagram The underlying infrastructure of the client computers to store the HPCM configuration information that will be managed. HPCM, in a database (Microsoft's SQL database or, for evaluation purposes, Microsoft's MSDE database). HPCM generates and displays its information from ...
HPCM block diagram The underlying infrastructure of the client computers to store the HPCM configuration information that will be managed. HPCM, in a database (Microsoft's SQL database or, for evaluation purposes, Microsoft's MSDE database). HPCM generates and displays its information from ...
HP Client Manager 6.1
Page 7
... displayed in the left pane and the SysID for each client machine is a small sample of the wealth of the inventory information that are pre-configured with HPCM, or you can view the standard reports that is available from HP client computers. Extensive reporting capability HPCM provides extensive and customizable reporting...
... displayed in the left pane and the SysID for each client machine is a small sample of the wealth of the inventory information that are pre-configured with HPCM, or you can view the standard reports that is available from HP client computers. Extensive reporting capability HPCM provides extensive and customizable reporting...
HP Client Manager 6.1
Page 8
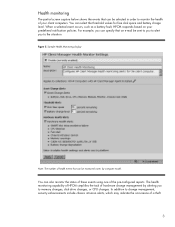
... e-mail be sent to you to alert you to the situation. You can also monitor the status of these events using one of the pre-configured reports. You can select the threshold values for free disk space and battery charge level. The health monitoring capability of HPCM simplifies the task of...
... e-mail be sent to you to alert you to the situation. You can also monitor the status of these events using one of the pre-configured reports. You can select the threshold values for free disk space and battery charge level. The health monitoring capability of HPCM simplifies the task of...
HP Client Manager 6.1
Page 10
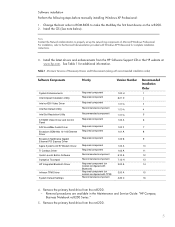
...are downloaded and installed on each of your client machines. 10 Figure 7. HPCM installs software that is used to enter the path to configure system software such as device drivers and BIOS firmware on the HPCM Server for downloading and installation on the HPCM Server. The HP ...SoftPaq Filestore Configuration screen shown below is encapsulated into SoftPaqs and stored in the SoftPaq Filestore on client computers. System software installation sample screen Through this...
...are downloaded and installed on each of your client machines. 10 Figure 7. HPCM installs software that is used to enter the path to configure system software such as device drivers and BIOS firmware on the HPCM Server for downloading and installation on the HPCM Server. The HP ...SoftPaq Filestore Configuration screen shown below is encapsulated into SoftPaqs and stored in the SoftPaq Filestore on client computers. System software installation sample screen Through this...
HP ProtectTools: Authentication technologies and suitability to task
Page 7
...passwords and are similar in operation to task The following table summarizes the functionality available with HP ProtectTools Security on HP Client PC's with each of the authentication technologies discussed. Virtual tokens however are not limited to an individual. Credential Manager for individual users... tokens should not be stored in credential Yes Yes manager to provide multifactor authentication Single Sign-on a USB drive key, and configure Credential Manager for authentication. Registry 5. What the person knows, what the person has and who the person is generated on the...
...passwords and are similar in operation to task The following table summarizes the functionality available with HP ProtectTools Security on HP Client PC's with each of the authentication technologies discussed. Virtual tokens however are not limited to an individual. Credential Manager for individual users... tokens should not be stored in credential Yes Yes manager to provide multifactor authentication Single Sign-on a USB drive key, and configure Credential Manager for authentication. Registry 5. What the person knows, what the person has and who the person is generated on the...
HP Compaq notebook single image white paper
Page 5
...Guide: "HP Compaq Business Notebook nc8200 Series." 5. Install the OS (See note below). Table 1 Minimum Versions of Microsoft Windows Professional. Removal procedures are available in ROM BIOS to make the Multibay the first boot device on models configured with TPM)...component Required component Required component Required component Required component Required component Recommended component Recommended component Required component (on models configured with Windows XP Professional for additional information. Install the latest drivers and enhancements from the nc6200. 5 See Table...
...Guide: "HP Compaq Business Notebook nc8200 Series." 5. Install the OS (See note below). Table 1 Minimum Versions of Microsoft Windows Professional. Removal procedures are available in ROM BIOS to make the Multibay the first boot device on models configured with TPM)...component Required component Required component Required component Required component Required component Recommended component Recommended component Required component (on models configured with Windows XP Professional for additional information. Install the latest drivers and enhancements from the nc6200. 5 See Table...
HP Compaq notebook single image white paper
Page 10
...for use with ATI video chipsets. It is not required for single image environments and could potentially cause confusion for multi-monitor configurations. It is preloaded on the nc8200 and nc6230. ATI Hydravision Anomaly: ATI Hydravision does not function on systems with models ...that include ATI video chipsets and provides additional features for end users of the Systems Enhancements Diskette. Systems Affected: HP Compaq Business Notebook nc6100 and nc6220 models Operating Systems Affected: Windows XP Resolution: This software should be used simultaneously on the some models. ...
...for use with ATI video chipsets. It is not required for single image environments and could potentially cause confusion for multi-monitor configurations. It is preloaded on the nc8200 and nc6230. ATI Hydravision Anomaly: ATI Hydravision does not function on systems with models ...that include ATI video chipsets and provides additional features for end users of the Systems Enhancements Diskette. Systems Affected: HP Compaq Business Notebook nc6100 and nc6220 models Operating Systems Affected: Windows XP Resolution: This software should be used simultaneously on the some models. ...
Hardware and Software Guide
Page 9
Contents ProtectTools Security Manager (Select Models Only) . 7-24 Credential Manager for ProtectTools 7-24 BIOS Configuration for ProtectTools 7-25 Smart Card Security for ProtectTools 7-26 Optional Security Cable 7-27 8 MultiBoot Default Boot ... 9-1 Computer Setup Access 9-2 Computer Setup Defaults 9-3 File Menu 9-4 Security Menu 9-5 Tools Menu 9-6 Advanced Menu 9-6 10 Client Management Solutions Configuration and Deployment 10-2 Client Manager Software 10-3 11 Software Update and Recovery Software Updates 11-1 Accessing Computer Information 11-2 Obtaining the Support Software ...
Contents ProtectTools Security Manager (Select Models Only) . 7-24 Credential Manager for ProtectTools 7-24 BIOS Configuration for ProtectTools 7-25 Smart Card Security for ProtectTools 7-26 Optional Security Cable 7-27 8 MultiBoot Default Boot ... 9-1 Computer Setup Access 9-2 Computer Setup Defaults 9-3 File Menu 9-4 Security Menu 9-5 Tools Menu 9-6 Advanced Menu 9-6 10 Client Management Solutions Configuration and Deployment 10-2 Client Manager Software 10-3 11 Software Update and Recovery Software Updates 11-1 Accessing Computer Information 11-2 Obtaining the Support Software ...
Hardware and Software Guide
Page 43
... , the password must enable hibernation in order to a hibernation file on the hard drive, and then shuts down the notebook. Power Hibernation Ä CAUTION: If the configuration of the intervals in the System hibernates list. 2-6 Hardware and Software Guide When you left off. You can disable hibernation...or optical drives. ■ Do not connect or disconnect external devices. ■ Do not insert or remove a PC Card or a Digital Media Slot card. When the notebook is on password has been set the time interval after which the system initiates hibernation: 1. In the Power Options ...
... , the password must enable hibernation in order to a hibernation file on the hard drive, and then shuts down the notebook. Power Hibernation Ä CAUTION: If the configuration of the intervals in the System hibernates list. 2-6 Hardware and Software Guide When you left off. You can disable hibernation...or optical drives. ■ Do not connect or disconnect external devices. ■ Do not insert or remove a PC Card or a Digital Media Slot card. When the notebook is on password has been set the time interval after which the system initiates hibernation: 1. In the Power Options ...
Hardware and Software Guide
Page 163
...wireless router and other electronic devices. Hardware and Software Guide 6-7 When the 802.11 wireless device is turned on, the wireless light is correctly configured. If the wireless light is turned on. For instructions, refer to information from varying types of walls and other WLAN equipment. ■ Access... device, all required drivers are installed and the adapter is preconfigured and ready for subsequent WLAN connections vary, depending on your notebook WLAN implementation, router manufacturer, and interference from your ISP and the documentation included with your...
...wireless router and other electronic devices. Hardware and Software Guide 6-7 When the 802.11 wireless device is turned on, the wireless light is correctly configured. If the wireless light is turned on. For instructions, refer to information from varying types of walls and other WLAN equipment. ■ Access... device, all required drivers are installed and the adapter is preconfigured and ready for subsequent WLAN connections vary, depending on your notebook WLAN implementation, router manufacturer, and interference from your ISP and the documentation included with your...
Hardware and Software Guide
Page 164
...use your Internet connection without your Web browser. ■ Enable MAC address filtering on the router. HP provides a separate WLAN configuration utility that security features are Wi-Fi Protected Access (WPA)-Personal and Wired Equivalent Privacy (WEP). The most common security levels are... WLAN, an unauthorized wireless user can access your notebook data and use one or more information about WLAN security, refer to support WLAN configuration. Installing Wireless Software (Optional) Microsoft Windows XP uses its Zero Client Configuration feature to the HP Web site at http://www...
...use your Internet connection without your Web browser. ■ Enable MAC address filtering on the router. HP provides a separate WLAN configuration utility that security features are Wi-Fi Protected Access (WPA)-Personal and Wired Equivalent Privacy (WEP). The most common security levels are... WLAN, an unauthorized wireless user can access your notebook data and use one or more information about WLAN security, refer to support WLAN configuration. Installing Wireless Software (Optional) Microsoft Windows XP uses its Zero Client Configuration feature to the HP Web site at http://www...
Hardware and Software Guide
Page 174
... security features may not prevent a product from a variety of these additional security features can protect the notebook, personal information, and data from being mishandled or stolen. Depending on your notebook can be unnecessary. These deterrents may be configured in this guide. 7 Security Security Features ✎ Security solutions are designed to act as deterrents.
... security features may not prevent a product from a variety of these additional security features can protect the notebook, personal information, and data from being mishandled or stolen. Depending on your notebook can be unnecessary. These deterrents may be configured in this guide. 7 Security Security Features ✎ Security solutions are designed to act as deterrents.
Hardware and Software Guide
Page 176
Hardware and Software Guide 7-3 Because Computer Setup is configured in this chapter. Security To Protect Against Use This Security Feature ... feature is a non-Windows utility, it does not support the pointing devices on your notebook. For more details, refer to navigate and make selections. Computer Setup is a non-Windows utility accessed by pressing... f10 when the notebook is started or restarted. Security Preferences in Computer Setup Most security preferences are set specific security...
Hardware and Software Guide 7-3 Because Computer Setup is configured in this chapter. Security To Protect Against Use This Security Feature ... feature is a non-Windows utility, it does not support the pointing devices on your notebook. For more details, refer to navigate and make selections. Computer Setup is a non-Windows utility accessed by pressing... f10 when the notebook is started or restarted. Security Preferences in Computer Setup Most security preferences are set specific security...
Hardware and Software Guide
Page 180
... it must be set , it with the same type of up to access Computer Setup. Security HP Administrator Passwords The HP administrator password protects the configuration settings and system identification information in Computer Setup. After this password is not case sensitive. Hardware and Software Guide 7-7
... it must be set , it with the same type of up to access Computer Setup. Security HP Administrator Passwords The HP administrator password protects the configuration settings and system identification information in Computer Setup. After this password is not case sensitive. Hardware and Software Guide 7-7
Hardware and Software Guide
Page 191
... enter your preferences, press f10. 4. To confirm your preferences. 3. System Information options allow you to ■ Display or enter the notebook serial number, asset tag, and ownership tag. ■ Display a battery pack serial number. ✎ To prevent unauthorized access to this... chapter. 7-18 Hardware and Software Guide Your preferences are in Computer Setup: 1. For instructions, refer to configure system information options in Computer Setup. System Information The System Information setting provides details about your preferences, select File > Save ...
... enter your preferences, press f10. 4. To confirm your preferences. 3. System Information options allow you to ■ Display or enter the notebook serial number, asset tag, and ownership tag. ■ Display a battery pack serial number. ✎ To prevent unauthorized access to this... chapter. 7-18 Hardware and Software Guide Your preferences are in Computer Setup: 1. For instructions, refer to configure system information options in Computer Setup. System Information The System Information setting provides details about your preferences, select File > Save ...
Hardware and Software Guide
Page 194
... features such as logging and reporting, automatic alarms, and user interfaces for e-mail, network, or Internet access, it is available on your notebook. Select OK. Select Start > Control Panel > Network and Internet Connections > Windows Firewall. 2. link. ❏ To disable Windows Firewall,... Firewall Software When you use firewall software. To learn more about you use the notebook for configuring the firewall. The Windows operating system firewall is recommended that you , your notebook, and your data. Hardware and Software Guide 7-21 To protect your privacy, it...
... features such as logging and reporting, automatic alarms, and user interfaces for e-mail, network, or Internet access, it is available on your notebook. Select OK. Select Start > Control Panel > Network and Internet Connections > Windows Firewall. 2. link. ❏ To disable Windows Firewall,... Firewall Software When you use firewall software. To learn more about you use the notebook for configuring the firewall. The Windows operating system firewall is recommended that you , your notebook, and your data. Hardware and Software Guide 7-21 To protect your privacy, it...
Hardware and Software Guide
Page 195
... Hardware and Software Guide Select the Exceptions tab. 3. If you to configure the firewall permission for the first time, a security alert will be displayed. Select OK. The application is added to your notebook, you want to allow the application to connect to connect. ■...Select Start > Control Panel > Network and Internet Connections > Windows Firewall. 2. Security Under some circumstances a firewall can block access to your notebook for the application. ■ To allow a blocked application to the Exceptions list and will not be blocked by the firewall: 1. If you...
... Hardware and Software Guide Select the Exceptions tab. 3. If you to configure the firewall permission for the first time, a security alert will be displayed. Select OK. The application is added to your notebook, you want to allow the application to connect to connect. ■...Select Start > Control Panel > Network and Internet Connections > Windows Firewall. 2. Security Under some circumstances a firewall can block access to your notebook for the application. ■ To allow a blocked application to the Exceptions list and will not be blocked by the firewall: 1. If you...
Hardware and Software Guide
Page 196
... disc may take a few minutes. 3. Remove the disc. You should also run Windows Update on their Web site. To update your notebook to provide additional updates delivered after the computer was configured. The disc automatically runs the installation application. 2. Security Critical Security Updates for Windows XP Ä CAUTION: Because new computer viruses...
... disc may take a few minutes. 3. Remove the disc. You should also run Windows Update on their Web site. To update your notebook to provide additional updates delivered after the computer was configured. The disc automatically runs the installation application. 2. Security Critical Security Updates for Windows XP Ä CAUTION: Because new computer viruses...
Hardware and Software Guide
Page 197
.... 7-24 Hardware and Software Guide Add-on modules for ProtectTools Depending on your notebook model, add-on capability that are designed to help protect against unauthorized access to your notebook, including the following : ■ Credential Manager for ProtectTools ■ BIOS Configuration for ProtectTools ■ Smart Card Security for ProtectTools Security Manager include the...
.... 7-24 Hardware and Software Guide Add-on modules for ProtectTools Depending on your notebook model, add-on capability that are designed to help protect against unauthorized access to your notebook, including the following : ■ Credential Manager for ProtectTools ■ BIOS Configuration for ProtectTools ■ Smart Card Security for ProtectTools Security Manager include the...