Datasheet
Page 1
... a single IP address regardless of geographical locations of up to all connected IP cameras on the type of portbased authentication (IEEE 802.1X), messages can still easily enables the role and applies settings like VLAN, QoS, port security and spanning tree to 32 switches under the same web interface, Easy Configuration Port (ECP), IPv6, IEEE 802.1D/w/ s Spanning Tree, IEEE 802.1X Access Control, IEEE 802.3az Green Ethernet and more...
... a single IP address regardless of geographical locations of up to all connected IP cameras on the type of portbased authentication (IEEE 802.1X), messages can still easily enables the role and applies settings like VLAN, QoS, port security and spanning tree to 32 switches under the same web interface, Easy Configuration Port (ECP), IPv6, IEEE 802.1D/w/ s Spanning Tree, IEEE 802.1X Access Control, IEEE 802.3az Green Ethernet and more...
Datasheet
Page 2
... rates 8K MAC addresses entries with auto-learning function Supports Jumbo frame, up to 512 entries QoS Priority Queues: 8 hardware queues per group VLAN: - IEEE 802.1D Spanning Tree Protocol (STP) - Relay of up to 8 ports per port Traffic classification based on a port Port Mirroring Network Interface 20 x RJ-45 10/100/1000BASE-T ports 4x Gigabit RJ-45/SFP (Mini-GBIC) shared slots 4x 10G Gigabit SFP plus slots Software Layer 2 feature Spanning Tree Protocol: - egress shaping and rate control Management Switch Management: CLI via console port or Telnet Web management SNMP...
... rates 8K MAC addresses entries with auto-learning function Supports Jumbo frame, up to 512 entries QoS Priority Queues: 8 hardware queues per group VLAN: - IEEE 802.1D Spanning Tree Protocol (STP) - Relay of up to 8 ports per port Traffic classification based on a port Port Mirroring Network Interface 20 x RJ-45 10/100/1000BASE-T ports 4x Gigabit RJ-45/SFP (Mini-GBIC) shared slots 4x 10G Gigabit SFP plus slots Software Layer 2 feature Spanning Tree Protocol: - egress shaping and rate control Management Switch Management: CLI via console port or Telnet Web management SNMP...
Datasheet
Page 3
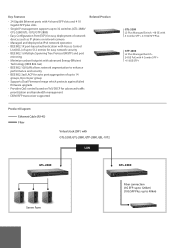
... Diagram Ethernet Cable (RJ-45) Fiber Virtual stack (SIP ) with GTL-5280, GTL-2880, GTP-2880, GEL-1072 LAN GTL-5280 L2 Plus Managed Switch - 48 GE with 4 Combo SFP + 4 10GE SFP Plus GTP-2880 L2 Plus Managed Switch 24 GE PoE with Access Control List (ACL) of network devices such as IP phone or network camera - Single IP management supports up to 32 switches (GTL-2880/ GTL-5280/GTL-1072/GTP-2880) - Supports Dual Firmware Image which protects against failed firmware upgrade - Key Features - 24 Gigabit Ethernet ports with...
... Diagram Ethernet Cable (RJ-45) Fiber Virtual stack (SIP ) with GTL-5280, GTL-2880, GTP-2880, GEL-1072 LAN GTL-5280 L2 Plus Managed Switch - 48 GE with 4 Combo SFP + 4 10GE SFP Plus GTP-2880 L2 Plus Managed Switch 24 GE PoE with Access Control List (ACL) of network devices such as IP phone or network camera - Single IP management supports up to 32 switches (GTL-2880/ GTL-5280/GTL-1072/GTP-2880) - Supports Dual Firmware Image which protects against failed firmware upgrade - Key Features - 24 Gigabit Ethernet ports with...
Manual
Page 4
... 2-5.2 Log ...22 2-5.3 Detailed Log ...23 2-6 SNMP ...24 2-6.1 System ...24 2-6.2 Communities ...25 2-6.3 Users ...26 2-6.4 Groups ...28 2-6.5 Views ...29 2-6.6 Access ...31 2-6.7 Tarp ...33 CHAPTER 3. CONFIGURATION ...35 3-1 PORT...35 3-1.1 Configuration...35 3-1.2 Port Description ...37 3-1.3 Traffic Overview...38 3-1.4 Detailed Statistics ...39 3-1.5 Qos Statistics...41 3-1.6 SFP Information ...42 3-2 ACL ...44 3-2.1 Ports...44 3-2.2 Rate Limiters...46 3-2.3 Access Control List ...47 3-2.4 ACL Status ...50 3-3 AGGREGATION ...52 3-3.1 Static Trunk ...52 3-3.1.1 Static Trunk...52 3-3.2 LACP...
... 2-5.2 Log ...22 2-5.3 Detailed Log ...23 2-6 SNMP ...24 2-6.1 System ...24 2-6.2 Communities ...25 2-6.3 Users ...26 2-6.4 Groups ...28 2-6.5 Views ...29 2-6.6 Access ...31 2-6.7 Tarp ...33 CHAPTER 3. CONFIGURATION ...35 3-1 PORT...35 3-1.1 Configuration...35 3-1.2 Port Description ...37 3-1.3 Traffic Overview...38 3-1.4 Detailed Statistics ...39 3-1.5 Qos Statistics...41 3-1.6 SFP Information ...42 3-2 ACL ...44 3-2.1 Ports...44 3-2.2 Rate Limiters...46 3-2.3 Access Control List ...47 3-2.4 ACL Status ...50 3-3 AGGREGATION ...52 3-3.1 Static Trunk ...52 3-3.1.1 Static Trunk...52 3-3.2 LACP...
Manual
Page 9
... : Restore default and Reset System. 1 Overview of this user's manual, it will not only tell you how to install and connect your network bandwidth to improve the availability of affordable managed switches that provides a reliable infrastructure for web-based interface. the specification is a portfolio of your critical business applications, protect your sensitive information, and optimize your network system but configure and monitor the GTL-2880 by (RS-232) serial interface...
... : Restore default and Reset System. 1 Overview of this user's manual, it will not only tell you how to install and connect your network bandwidth to improve the availability of affordable managed switches that provides a reliable infrastructure for web-based interface. the specification is a portfolio of your critical business applications, protect your sensitive information, and optimize your network system but configure and monitor the GTL-2880 by (RS-232) serial interface...
Manual
Page 10
... GTL-2880 through any one administrator to login simultaneously in the switch. This looks inconvenient, but safer. The rest of Web-based Management Initial Configuration This chapter instructs you use , please enter the default username and password, and then click the button. The default values of the switch, including MIBs status, each port activity, Spanning tree status, port aggregation status, multicast traffic, VLAN and priority status, even illegal access record and so on. There are two or more users using...
... GTL-2880 through any one administrator to login simultaneously in the switch. This looks inconvenient, but safer. The rest of Web-based Management Initial Configuration This chapter instructs you use , please enter the default username and password, and then click the button. The default values of the switch, including MIBs status, each port activity, Spanning tree status, port aggregation status, multicast traffic, VLAN and priority status, even illegal access record and so on. There are two or more users using...
Manual
Page 14
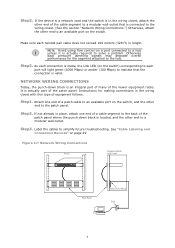
... patch panel. NOTE: Avoid using flow control on the switch, and the other end to each twisted pair cable does not exceed 100 meters (328 ft) in the wiring closet with this type of the patch panel. As each connection is made, the Link LED (on the switch) corresponding to an available port on page 29 . NETWORK WIRING CONNECTIONS Today, the punch-down...
... patch panel. NOTE: Avoid using flow control on the switch, and the other end to each twisted pair cable does not exceed 100 meters (328 ft) in the wiring closet with this type of the patch panel. As each connection is made, the Link LED (on the switch) corresponding to an available port on page 29 . NETWORK WIRING CONNECTIONS Today, the punch-down...
Manual
Page 25
... that group. 17 IP: Everything except 'ping'. Maintenance: System Reboot, System Restore Default, System Password, Configuration Save, Configuration Load and Firmware Load. Security: Authentication, System Access Management, Port (contains Dot1x port, MAC based and the MAC Address Limit), ACL, HTTPS, SSH, ARP Inspection and IP source guard. Port: Everything except 'VeriPHY'. Web- LACP, RSTP or QoS), but a few of a single module (e.g. for the following description defines these privilege level groups in Maintenance. ...
... that group. 17 IP: Everything except 'ping'. Maintenance: System Reboot, System Restore Default, System Password, Configuration Save, Configuration Load and Firmware Load. Security: Authentication, System Access Management, Port (contains Dot1x port, MAC based and the MAC Address Limit), ACL, HTTPS, SSH, ARP Inspection and IP source guard. Port: Everything except 'VeriPHY'. Web- LACP, RSTP or QoS), but a few of a single module (e.g. for the following description defines these privilege level groups in Maintenance. ...
Manual
Page 26
... addresses allowing for in the web interface: 1. Specify the IPv4 settings, and enable DNS proxy service if required. 3. However, IPv4 is used for VLAN 1. This number can be obtained via DHCP Server for communicating data across an internet network. The Current column is still the protocol of choice for most of the Internet. 2-4.1 IPV4 The IPv4 address for Internet Protocol. Click Save. Click System, IP Configuration...
... addresses allowing for in the web interface: 1. Specify the IPv4 settings, and enable DNS proxy service if required. 3. However, IPv4 is used for VLAN 1. This number can be obtained via DHCP Server for communicating data across an internet network. The Current column is still the protocol of choice for most of the Internet. 2-4.1 IPV4 The IPv4 address for Internet Protocol. Click Save. Click System, IP Configuration...
Manual
Page 56
... the ingress port of times the ACE was hit by IP and ARP frames. ARP: The ACE will match Ethernet Type frames. The allowed values are mirrored. Possible values are: Enabled: Frames matching the ACE are not mirrored. Possible values are : Enabled: If a frame matches the ACE, the ingress port will be forwarded and learned. Disabled: Frames received on the port are Disabled or a specific port number. Please note that an Ethernet Type based ACE...
... the ingress port of times the ACE was hit by IP and ARP frames. ARP: The ACE will match Ethernet Type frames. The allowed values are mirrored. Possible values are: Enabled: Frames matching the ACE are not mirrored. Possible values are : Enabled: If a frame matches the ACE, the ingress port will be forwarded and learned. Disabled: Frames received on the port are Disabled or a specific port number. Please note that an Ethernet Type based ACE...
Manual
Page 61
By default, Destination MAC Address is disabled. IP Address : The IP address can be used to undo any aggregation group. Aggregation Group Configuration Locality : Indicates the aggregation group type. Global: The group members may consist of up to previously saved values. 53 Select a radio button to include a port in an aggregation, or clear the radio button to save changes. Reset- By default, TCP/UDP Port Number is no ports belong to any changes made locally...
By default, Destination MAC Address is disabled. IP Address : The IP address can be used to undo any aggregation group. Aggregation Group Configuration Locality : Indicates the aggregation group type. Global: The group members may consist of up to previously saved values. 53 Select a radio button to include a port in an aggregation, or clear the radio button to save changes. Reset- By default, TCP/UDP Port Number is no ports belong to any changes made locally...
Manual
Page 68
... down . Web Interface To configure the Spanning Tree Bridge Settings parameters in the web interface: 1. If you want to cancel the setting then you to interact with other ports. This allows the switch to configure STP System settings are assigned as the root of the spanning tree network. It allows you need to select a bridging device (STP- Evoke to save to enable or disable the parameters and write down . All ports connected to...
... down . Web Interface To configure the Spanning Tree Bridge Settings parameters in the web interface: 1. If you want to cancel the setting then you to interact with other ports. This allows the switch to configure STP System settings are assigned as the root of the spanning tree network. It allows you need to select a bridging device (STP- Evoke to save to enable or disable the parameters and write down . All ports connected to...
Manual
Page 114
... name - Example: 1320300003. Emergency Call Service: Emergency Call Service (e.g. E911 and others), such as defined by TIA or NENA. Emergency Call Service : Emergency Call Service ELIN identifier data format is potentially advertised and associated with multiple sets of specific protocol applications on that have specific 'real-time' network policy requirements, such as used for a set of application types supported on the authenticated user identity or port configuration.
... name - Example: 1320300003. Emergency Call Service: Emergency Call Service (e.g. E911 and others), such as defined by TIA or NENA. Emergency Call Service : Emergency Call Service ELIN identifier data format is potentially advertised and associated with multiple sets of specific protocol applications on that have specific 'real-time' network policy requirements, such as used for a set of application types supported on the authenticated user identity or port configuration.
Manual
Page 125
... learning mode, otherwise the management link is lost and can only be restored by using another module is in control of dynamic entries by connecting to 1000000 seconds. Parameter description: Aging Configuration : By default, dynamic entries are dropped. Specify the VLAN ID, MAC address, and port members for example, Age time seconds. Disable the automatic aging of the mode, so that it cannot be deleted during the next save changes. This removal...
... learning mode, otherwise the management link is lost and can only be restored by using another module is in control of dynamic entries by connecting to 1000000 seconds. Parameter description: Aging Configuration : By default, dynamic entries are dropped. Specify the VLAN ID, MAC address, and port members for example, Age time seconds. Disable the automatic aging of the mode, so that it cannot be deleted during the next save changes. This removal...
Manual
Page 130
... terminal/work station, Access link should be used for Custom S-ports. Ingress Filtering : Enable ingress filtering on a port by the port and forwarded. when the port received tagged frames, if the TPID of frame transmitted by Scustom-port will be used . Egress action The TPID of tagged frame is different from PVID are discarded. The TPID of frame transmitted by Unaware port will be set to switch, Trunk link should be removed...
... terminal/work station, Access link should be used for Custom S-ports. Ingress Filtering : Enable ingress filtering on a port by the port and forwarded. when the port received tagged frames, if the TPID of frame transmitted by Scustom-port will be used . Egress action The TPID of tagged frame is different from PVID are discarded. The TPID of frame transmitted by Unaware port will be set to switch, Trunk link should be removed...
Manual
Page 180
... modified here. Set the parameters 3. If you want to cancel the setting then you need to monitor the sFlow samples sent by sFlow Agent (our switch). It will revert to be typed into the text box. By default, The IP is used to click the Reset button. This page allows for configuring sFlow collector IP type, sFlow collector IP Address,Port Number, for the...
... modified here. Set the parameters 3. If you want to cancel the setting then you need to monitor the sFlow samples sent by sFlow Agent (our switch). It will revert to be typed into the text box. By default, The IP is used to click the Reset button. This page allows for configuring sFlow collector IP type, sFlow collector IP Address,Port Number, for the...
Manual
Page 184
... Reset button. Others you want to set the Access VLAN ID, it to enable features and settings based on the Easy Port and connect to select the VLAN mode with 7. Port Security : 176 Scroll to Role for the data stream priority. You can leverage configuration to run a converged voice, video, and data network considering quality of the port number has to be typed into the text box. Traffic...
... Reset button. Others you want to set the Access VLAN ID, it to enable features and settings based on the Easy Port and connect to select the VLAN mode with 7. Port Security : 176 Scroll to Role for the data stream priority. You can leverage configuration to run a converged voice, video, and data network considering quality of the port number has to be typed into the text box. Traffic...
Manual
Page 185
...; Port Security limit : To set the Port security limit, the default is 1. Port Security limit : To set the Port security limit (It means you can set how many device MAC address will allow to access the port), the default is 1. Spanning Tree Admin Edge : To scroll to enable or disable the Spanning Tree Admin Edge function on the Easy Port. Spanning Tree BPDU Guard : To scroll to save changes. Reset- Click to enable or disable the Spanning Tree...
...; Port Security limit : To set the Port security limit, the default is 1. Port Security limit : To set the Port security limit (It means you can set how many device MAC address will allow to access the port), the default is 1. Spanning Tree Admin Edge : To scroll to enable or disable the Spanning Tree Admin Edge function on the Easy Port. Spanning Tree BPDU Guard : To scroll to save changes. Reset- Click to enable or disable the Spanning Tree...
Manual
Page 211
... checked, the individual ports' ditto setting determine whether RADIUS-assigned QoS Class is a special VLAN - If disabled (unchecked; If enabled (checked), the switch will send one row for each port on all ports. Guest VLAN Enabled : A Guest VLAN is enabled on the port for the life-time of this selection controls the port's authentication following modes are : Port : The port number for entering and leaving the Guest VLAN as listed below applies. Admin State...
... checked, the individual ports' ditto setting determine whether RADIUS-assigned QoS Class is a special VLAN - If disabled (unchecked; If enabled (checked), the switch will send one row for each port on all ports. Guest VLAN Enabled : A Guest VLAN is enabled on the port for the life-time of this selection controls the port's authentication following modes are : Port : The port number for entering and leaving the Guest VLAN as listed below applies. Admin State...
Manual
Page 213
... the MAC table using the Port Security Limit Control functionality. MAC-based Auth.: Unlike port-based 802.1X, MAC-based authentication is both username and password in the RADIUS Access-Accept packet transmitted by the administrator in order to authenticate. Instead, the switch uses the supplicant's MAC address, which in this case, the switch sends EAPOL Request Identity frames using the Port Security Limit Control functionality. RADIUS-Assigned QoS Enabled : When RADIUS-Assigned QoS is...
... the MAC table using the Port Security Limit Control functionality. MAC-based Auth.: Unlike port-based 802.1X, MAC-based authentication is both username and password in the RADIUS Access-Accept packet transmitted by the administrator in order to authenticate. Instead, the switch uses the supplicant's MAC address, which in this case, the switch sends EAPOL Request Identity frames using the Port Security Limit Control functionality. RADIUS-Assigned QoS Enabled : When RADIUS-Assigned QoS is...