Security Target
Page 4
...4.3.2 Tracing Validity ...32 5 Extended Components Definition 35 6 Security Requirements...36 6.1 Security Functional Requirements 36 6.1.1 Class FAU: Security audit 36 6.1.2 Class FCS: Cryptographic support 41 6.1.3 Class FDP: User data protection 42 6.1.4 Class FIA: Identification and authentication 45 6.1.5 Class FMT: Security management 48 6.1.6 Class FPT: Protection of the... Function 69 7.1.2.1 User Identification and Authentication 69 7.1.2.2 Action in case of Identification and Authentication Failure 69 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
...4.3.2 Tracing Validity ...32 5 Extended Components Definition 35 6 Security Requirements...36 6.1 Security Functional Requirements 36 6.1.1 Class FAU: Security audit 36 6.1.2 Class FCS: Cryptographic support 41 6.1.3 Class FDP: User data protection 42 6.1.4 Class FIA: Identification and authentication 45 6.1.5 Class FMT: Security management 48 6.1.6 Class FPT: Protection of the... Function 69 7.1.2.1 User Identification and Authentication 69 7.1.2.2 Action in case of Identification and Authentication Failure 69 Copyright (c) 2009,2010 RICOH COMPANY, LTD. All Rights Reserved.
Security Target
Page 8
..., LTD. ST Title : imagio MP 2550/3350 series, Aficio MP 2550/3350 series Security Target ST Version : 1.05 Date : 2010-02-08 Authors : RICOH COMPANY, LTD., Yoshihiko KAMEKURA, Yasushi FUNAKI, Fumi TAKITA 1.2 TOE Reference The following software and hardware. All Rights Reserved. Software System/Copy Network Support Scanner Printer Fax Web Support Web Uapl Network Doc...
..., LTD. ST Title : imagio MP 2550/3350 series, Aficio MP 2550/3350 series Security Target ST Version : 1.05 Date : 2010-02-08 Authors : RICOH COMPANY, LTD., Yoshihiko KAMEKURA, Yasushi FUNAKI, Fumi TAKITA 1.2 TOE Reference The following software and hardware. All Rights Reserved. Software System/Copy Network Support Scanner Printer Fax Web Support Web Uapl Network Doc...
Security Target
Page 18
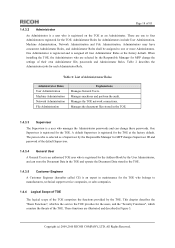
... passwords and Administrator Roles. Administrators may have concurrent Administrator Roles, and Administrator Roles shall be assigned to manufacturers, technical support service companies, or sales companies. 1.4.4 Logical Scope of TOE The logical scope of the TOE. One Administrator is ...Machine Administration, Network Administration and File Administration. Manages the TOE network connections. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. This chapter describes the "Basic Functions", which counters the threats of the TOE comprises the functions provided ...
... passwords and Administrator Roles. Administrators may have concurrent Administrator Roles, and Administrator Roles shall be assigned to manufacturers, technical support service companies, or sales companies. 1.4.4 Logical Scope of TOE The logical scope of the TOE. One Administrator is ...Machine Administration, Network Administration and File Administration. Manages the TOE network connections. All Rights Reserved. Copyright (c) 2009,2010 RICOH COMPANY, LTD. This chapter describes the "Basic Functions", which counters the threats of the TOE comprises the functions provided ...
Security Target
Page 41
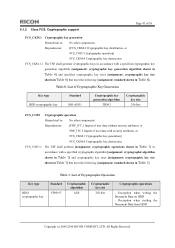
...[FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction. 6.1.2 Class FCS: Cryptographic support Page 41 of 83 FCS_CKM.1 Cryptographic key generation Hierarchical to : No other components. FCS_COP.1.1 The TSF shall ... meet the following : [assignment: standard shown in Table 6]. Decryption when reading the Document Data from HDD Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 6: List of Cryptographic Key Generation Key type HDD cryptographic key Standard BSI-AIS31 Cryptographic key generation algorithm TRNG...
...[FCS_CKM.2 Cryptographic key distribution, or FCS_COP.1 Cryptographic operation] FCS_CKM.4 Cryptographic key destruction. 6.1.2 Class FCS: Cryptographic support Page 41 of 83 FCS_CKM.1 Cryptographic key generation Hierarchical to : No other components. FCS_COP.1.1 The TSF shall ... meet the following : [assignment: standard shown in Table 6]. Decryption when reading the Document Data from HDD Copyright (c) 2009,2010 RICOH COMPANY, LTD. Table 6: List of Cryptographic Key Generation Key type HDD cryptographic key Standard BSI-AIS31 Cryptographic key generation algorithm TRNG...
Security Target
Page 54
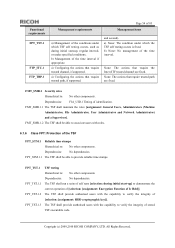
... shall provide authorised users with the capability to verify the integrity of stored TSF executable code.㩷 Copyright (c) 2009,2010 RICOH COMPANY, LTD. FMT_SMR.1 Security roles Hierarchical to : No other components. b) None: No management of the time interval if... appropriate. a) Configuring the actions that require trusted channel, if supported. a) None: The condition under specified conditions; FMT_SMR.1.1 The TSF shall maintain the roles [assignment: General Users, Administrators (Machine Administrator...
... shall provide authorised users with the capability to verify the integrity of stored TSF executable code.㩷 Copyright (c) 2009,2010 RICOH COMPANY, LTD. FMT_SMR.1 Security roles Hierarchical to : No other components. b) None: No management of the time interval if... appropriate. a) Configuring the actions that require trusted channel, if supported. a) None: The condition under specified conditions; FMT_SMR.1.1 The TSF shall maintain the roles [assignment: General Users, Administrators (Machine Administrator...
Security Target
Page 56
... and other requirements are shown in Table 22. Table 22: TOE Security Assurance Requirements (EAL3) Assurance classes ADV: Development AGD: Guidance documents ALC: Life-cycle support ASE: Security Target evaluation ATE: Tests AVA: Vulnerability assessment ADV_ARC.1 ADV_FSP.3 summary ADV_TDS.2 AGD_OPE.1 AGD_PRE.1 ALC_CMC.3 ALC_CMS.3 ALC_DEL.1 ALC_DVS.1 ALC_LCD.1 ASE_CCL.1 ASE_ECD.1 ...objectives Derived security requirements Security problem definition TOE summary specification Analysis of this TOE is EAL3. sample Vulnerability analysis Copyright (c) 2009,2010 RICOH COMPANY, LTD.
... and other requirements are shown in Table 22. Table 22: TOE Security Assurance Requirements (EAL3) Assurance classes ADV: Development AGD: Guidance documents ALC: Life-cycle support ASE: Security Target evaluation ATE: Tests AVA: Vulnerability assessment ADV_ARC.1 ADV_FSP.3 summary ADV_TDS.2 AGD_OPE.1 AGD_PRE.1 ALC_CMC.3 ALC_CMS.3 ALC_DEL.1 ALC_DVS.1 ALC_LCD.1 ASE_CCL.1 ASE_ECD.1 ...objectives Derived security requirements Security problem definition TOE summary specification Analysis of this TOE is EAL3. sample Vulnerability analysis Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 79
... MFP. An abbreviation for S/MIME use. A chip that contains a microprocessor for a set of parameters that identify the TOE such as System/Copy, Network Support, Scanner, Printer, Fax, Web Support, Web Uapl and Network Doc Box. A function that sends and receives document files between two faxes that encrypts the data to be written... this function. A generic term for encryption processing and EEPROM that comprise the MFP and controls their operation. Information about each General User. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
... MFP. An abbreviation for S/MIME use. A chip that contains a microprocessor for a set of parameters that identify the TOE such as System/Copy, Network Support, Scanner, Printer, Fax, Web Support, Web Uapl and Network Doc Box. A function that sends and receives document files between two faxes that encrypts the data to be written... this function. A generic term for encryption processing and EEPROM that comprise the MFP and controls their operation. Information about each General User. Copyright (c) 2009,2010 RICOH COMPANY, LTD.
Security Target
Page 80
... Software on Fax Unit. A function that stores the scanned data of the original in that user's Lockout. Copyright (c) 2009,2010 RICOH COMPANY, LTD. One of the authorised TOE users who has the user management role. The password to networks. Indicates the Supervisor's login... Administration Network Control Data Minimum Password Length Password Complexity Setting Fax Process on Fax Unit Deliver to Folder Sending by manufacturers, technical support service companies, or sales companies. A person who has the network management role. MFP Control Software that sends the Document Data...
... Software on Fax Unit. A function that stores the scanned data of the original in that user's Lockout. Copyright (c) 2009,2010 RICOH COMPANY, LTD. One of the authorised TOE users who has the user management role. The password to networks. Indicates the Supervisor's login... Administration Network Control Data Minimum Password Length Password Complexity Setting Fax Process on Fax Unit Deliver to Folder Sending by manufacturers, technical support service companies, or sales companies. A person who has the network management role. MFP Control Software that sends the Document Data...