Design Guide
Page 6
Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of 86 For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to as the information security of the hardware (e.g. Page 6 of the hardware and software for the specific machine in question. The...
Print Controller Design Guide for Information Security Overview This document describes the structural layout and functional operations of 86 For these details, please refer to the Operating Instructions for the multi-functional products and laser printers listed below (herein referred to as the information security of the hardware (e.g. Page 6 of the hardware and software for the specific machine in question. The...
Design Guide
Page 8
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
... coin/card-operated devices. • External controller I/F board: Acts as the interface between the MFP and external controller. • File Format Converter: Converts the file format of image files. • RC Gate: Intermediary device connected to the MFP/LP via an Ethernet connection for performing remote diagnostic operations including firmware updates and settings changes. • SD card I/F: Used for performing service maintenance and as an interface for firmware storage media. • RAM, HDD: Image data...
Design Guide
Page 12
... Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages the status of all non-FAX transmission/reception of e-mail as well ass the forwarding of image data to servers and folders. Print Controller Design Guide for access control, is handled from the operation panel. counters). Receives image data through the host interface, which then sends the data to a PC via a telecommunications line. Secondary data...
... Report Service) UCS (User Control Service) CCS (Certification Control Service) NRS (New Remote Service) LCS (Log Control Service) DESS (Data Encryption Security Service) Manages the status of all non-FAX transmission/reception of e-mail as well ass the forwarding of image data to servers and folders. Print Controller Design Guide for access control, is handled from the operation panel. counters). Receives image data through the host interface, which then sends the data to a PC via a telecommunications line. Secondary data...
Design Guide
Page 13
... designed to be peformed on models capable of supporting an external controller. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as a client to external Web services, including transferring the machine log data to specific log data collection utilities A Web application that standardizes the meanings of simplified commands used by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS...
... designed to be peformed on models capable of supporting an external controller. The EAC allows the external controller to initiate MFP operations such as print jobs and scan jobs, as well as a client to external Web services, including transferring the machine log data to specific log data collection utilities A Web application that standardizes the meanings of simplified commands used by Ricoh. Print Controller Design Guide for Information Security Netfile (GWWS...
Design Guide
Page 14
All image data stored on the UNIX operating system as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I/F (IC card, Pictbridge) 1-3-2 Protection of Program Data from Illegal Access via an...
All image data stored on the UNIX operating system as a two-way parallel interface when using a USB cable. • Standard IEEE 1394 I/F • 100BASE-TX and 10BASE-T compatible network I/F (Host I/F) • Gigabit Ethernet-compatible network I/F (Host I/F options, external controller I/F board) • Standard IEEE802.11b wireless LAN network I/F (Host I/F option) • Bluetooth I/F (Host I/F option) • USB2.0 Type B I/F (Host I/F) • USB2.0 Type A I/F (IC card, Pictbridge) 1-3-2 Protection of Program Data from Illegal Access via an...
Design Guide
Page 17
... Update process is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 The firmware in the SD card is introduced into the MFP/LP in the field, the following process is possible to update the firmware stored on the MFP/LP using the same SD card in the field. 1. Print Controller Design Guide for purchase in the field. The Ricoh license server...
... Update process is cancelled and new firmware is overwritten with new files Firmware Update Using an SD Card Page 17 of 86 The firmware in the SD card is introduced into the MFP/LP in the field, the following process is possible to update the firmware stored on the MFP/LP using the same SD card in the field. 1. Print Controller Design Guide for purchase in the field. The Ricoh license server...
Design Guide
Page 24
... code, the user will be stored to this option, it then obtains the username and password stored in the IC card) Job + Auth. This feature supports IC cards built to Ricoh specifications. Info. One server is encrypted Authentication information (stored in the card and begins the authentication process. To use this IC card and then used to authenticate MFP/LP users. Print Controller Design Guide for Information Security 1-5-2 IC Card...
... code, the user will be stored to this option, it then obtains the username and password stored in the IC card) Job + Auth. This feature supports IC cards built to Ricoh specifications. Info. One server is encrypted Authentication information (stored in the card and begins the authentication process. To use this IC card and then used to authenticate MFP/LP users. Print Controller Design Guide for Information Security 1-5-2 IC Card...
Design Guide
Page 27
Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on the HDD), the image data itself remains in the unlikely event that data reconstruction is not possible. Data stored on the MFP/LP, a service or sales engineer must perform the setup procedure. Even in the temporary storage stored area of Defense...
Print Controller Design Guide for example, although the MFP/LP completely erases the page location data (the storage location information necessary to access image data on the HDD), the image data itself remains in the unlikely event that data reconstruction is not possible. Data stored on the MFP/LP, a service or sales engineer must perform the setup procedure. Even in the temporary storage stored area of Defense...
Design Guide
Page 32
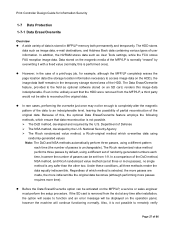
...*1 Authent. These settings can be changed by general users, groups, owners, and User Administrators. The data in the Address Book is installed. Admin. Data Reg. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 There are also able to change user passwords. This data can be encrypted before it is stored if the Printer/Scanner option is stored in the Address Book, as...
...*1 Authent. These settings can be changed by general users, groups, owners, and User Administrators. The data in the Address Book is installed. Admin. Data Reg. Password*1, *2 Protection Code 00001 Taroh Ricoh taroh@ricoh.co.jp 1234-5678 Taroh ********** **** General Users Groups Owner of 86 There are also able to change user passwords. This data can be encrypted before it is stored if the Printer/Scanner option is stored in the Address Book, as...
Design Guide
Page 33
... of 86 Every time a user logs in using Integration Server Authentication, the document protection setting in that can be performed on LP models. *2: This password can be disabled for all further access to groups. In addition, if an incorrect password is possible to assign general user access privileges to clear a password-based authentication process. Therefore if the user stores a file to the Document Server without having to...
... of 86 Every time a user logs in using Integration Server Authentication, the document protection setting in that can be performed on LP models. *2: This password can be disabled for all further access to groups. In addition, if an incorrect password is possible to assign general user access privileges to clear a password-based authentication process. Therefore if the user stores a file to the Document Server without having to...
Design Guide
Page 45
... 2.5.2 Data Flow. simplex or duplex, paper size), completion status (whether completed successfully or not) and user identification (in the HDD for each individual user. In addition, it is possible to set to "Level 2", changes to store a copy of security by the external charge device or key counter itself (card, currency, etc.). 2-1-7 Job/Access Log Data Collection A job log entry is possible to prohibit Full Color printing and instead enable Auto Color Detection...
... 2.5.2 Data Flow. simplex or duplex, paper size), completion status (whether completed successfully or not) and user identification (in the HDD for each individual user. In addition, it is possible to set to "Level 2", changes to store a copy of security by the external charge device or key counter itself (card, currency, etc.). 2-1-7 Job/Access Log Data Collection A job log entry is possible to prohibit Full Color printing and instead enable Auto Color Detection...
Design Guide
Page 48
... page size, paper type and number of 86 The data processing flow varies depending on the method used, since some operations are not supported with the image data itself. The bibliographic information is stored in the HDD is printed out. The necessary bibliographic information for the image data stored in the HDD along with some printer languages (see below). • With Normal Print, the page location data for the image data...
... page size, paper type and number of 86 The data processing flow varies depending on the method used, since some operations are not supported with the image data itself. The bibliographic information is stored in the HDD is printed out. The necessary bibliographic information for the image data stored in the HDD along with some printer languages (see below). • With Normal Print, the page location data for the image data...
Design Guide
Page 49
... Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is registered in the printing history. Once the file is recognized as the username and password for the image data stored in the printer driver, it is turned off . This information and data is preserved even when the machine main power is used for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). Once a user...
... Printer function via a Ricoh-original MIB over an SNMP connection. *1: The "print management data" is registered in the printing history. Once the file is recognized as the username and password for the image data stored in the printer driver, it is turned off . This information and data is preserved even when the machine main power is used for printing, job settings (simplex or duplex, etc.) and general job data (time, username, etc.). Once a user...
Design Guide
Page 54
... operation panel ("Scanned File Status"). Since there is no receiving aspect, it is not possible for the Scanner function to receive any illegal data from an external interface. • When sending image data to an SMTP server, it is turned off. 2-3-2 Data Flow Security Considerations • Forwarding operations are unidirectional, sending image data to encrypt the password using a DIGEST algorithm. With the third option, the page location data...
... operation panel ("Scanned File Status"). Since there is no receiving aspect, it is not possible for the Scanner function to receive any illegal data from an external interface. • When sending image data to an SMTP server, it is turned off. 2-3-2 Data Flow Security Considerations • Forwarding operations are unidirectional, sending image data to encrypt the password using a DIGEST algorithm. With the third option, the page location data...
Design Guide
Page 55
... transmission by unauthorized senders. - Limit the sending of e-mail to destinations that does not conform to the predetermined protocol of the command interface. Require user identification when sending to a forwarding server. Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be done using the "Restrict use the TWAIN V4 driver.
... transmission by unauthorized senders. - Limit the sending of e-mail to destinations that does not conform to the predetermined protocol of the command interface. Require user identification when sending to a forwarding server. Print Controller Design Guide for Information Security password necessary to open the encrypted PDF data at the MFP and the forwarding server software must be done using the "Restrict use the TWAIN V4 driver.
Design Guide
Page 58
... dictionary and brute-force attacks. Print Controller Design Guide for accessing directory services that uses the MD5 algorithm to encrypt the challenge string and password. • DIGEST-MD5 [RFC2831]: A message digest functional algorithm developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. The entry contains information on job and access logs, please refer to 1.9 Job/Access Logs. 2-3-8 Terminology • SMTP...
... dictionary and brute-force attacks. Print Controller Design Guide for accessing directory services that uses the MD5 algorithm to encrypt the challenge string and password. • DIGEST-MD5 [RFC2831]: A message digest functional algorithm developed as user address books. • SMB (Server Message Block): A protocol used to enable file sharing between Windows PCs. The entry contains information on job and access logs, please refer to 1.9 Job/Access Logs. 2-3-8 Terminology • SMTP...
Design Guide
Page 70
... possible to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Page 70 of WebDocBox Operations WebDocBox allows users to issue commands via illegal access. Print Controller Design Guide for malicious purposes. WebImageMonitor prevents such trouble by limiting the length of the URL strings it will accept, rejecting any settings can only be changed by Administrators. 2-6-2 WebDocBox...
... possible to the MFP using the Copier, Printer, Scanner and FAX functions, as well as Network Administrators. Page 70 of WebDocBox Operations WebDocBox allows users to issue commands via illegal access. Print Controller Design Guide for malicious purposes. WebImageMonitor prevents such trouble by limiting the length of the URL strings it will accept, rejecting any settings can only be changed by Administrators. 2-6-2 WebDocBox...
Design Guide
Page 71
... stored image files to the PC in PDF format, it is possible to encrypt the file as well as Document Administrators are allowed to perform operations that displays the list of the data in as set a password for decrypting the PDF data at the PC side. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with a password (see 1.7.2 Document Server Documents (MFP models...
... stored image files to the PC in PDF format, it is possible to encrypt the file as well as Document Administrators are allowed to perform operations that displays the list of the data in as set a password for decrypting the PDF data at the PC side. Print Controller Design Guide for Information Security Data Flow WebDocBox supports HTTP, a protocol used by allowing connection only with a password (see 1.7.2 Document Server Documents (MFP models...
Design Guide
Page 76
... ・ MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥...
... ・ MFP with vertical line pattern (before data is printed over image and clearly visible Page 76 of 86 Print Controller Design Guide for Information Security Special pattern embedded when image is printed out MFP with optional Copy Data Security Unit installed and enabled Contract When pattern is detected, buzzer sounds and image is replaced with Copy Data Security setting disabled, ・ MFP without Copy Data Security Unit, or ・ Non-Ricoh product Buzzer Contract ‥J‥...
Design Guide
Page 81
... incoming printing data received by opening and closing its own unique socket. This module allows the user to do the following: Use SDK applications in conjunction with a network-connected authentication server in section 2.2 and is installed on the PC are also able to use the DMP, making it possible to perform changes to make use of the HDD. It is possible to create a user interface for...
... incoming printing data received by opening and closing its own unique socket. This module allows the user to do the following: Use SDK applications in conjunction with a network-connected authentication server in section 2.2 and is installed on the PC are also able to use the DMP, making it possible to perform changes to make use of the HDD. It is possible to create a user interface for...