Implementation Guide
Page 21
.... It offers advanced defense against all types of -the-art protection to fully protect and customize the security in your environment. Table 1-2 describes the types of protection that Symantec Endpoint Protection Small Business Edition provides Symantec Endpoint Protection Small Business Edition uses state-of attacks for deployment shows which computers have successfully installed the client software. Symantec Endpoint Protection Small Business Edition combines traditional scanning, behavioral analysis, intrusion prevention, and community intelligence...
.... It offers advanced defense against all types of -the-art protection to fully protect and customize the security in your environment. Table 1-2 describes the types of protection that Symantec Endpoint Protection Small Business Edition provides Symantec Endpoint Protection Small Business Edition uses state-of attacks for deployment shows which computers have successfully installed the client software. Symantec Endpoint Protection Small Business Edition combines traditional scanning, behavioral analysis, intrusion prevention, and community intelligence...
Implementation Guide
Page 31
... data corruption or a hardware failure, you can troubleshoot Task Description Fixing installation problems You can use Symantec Endpoint Protection Small Business Edition. It is about to troubleshoot computer issues" on the security status. See "Downloading the Symantec Endpoint Protection Support Tool to expire or if you install and use the notifications, reports, and logs to access the Internet" on page 289.
... data corruption or a hardware failure, you can troubleshoot Task Description Fixing installation problems You can use Symantec Endpoint Protection Small Business Edition. It is about to troubleshoot computer issues" on the security status. See "Downloading the Symantec Endpoint Protection Support Tool to expire or if you install and use the notifications, reports, and logs to access the Internet" on page 289.
Implementation Guide
Page 50
... Support knowledge base article, How to add the self-signed certificate for Symantec Protection Center or Symantec Endpoint Protection Manager to Internet Explorer. If the Web page security certificate warning appears, click Continue to this website (not recommended) and add the self-signed certificate to Internet Explorer. This problem occurs if you log on and specify an IP...
... Support knowledge base article, How to add the self-signed certificate for Symantec Protection Center or Symantec Endpoint Protection Manager to Internet Explorer. If the Web page security certificate warning appears, click Continue to this website (not recommended) and add the self-signed certificate to Internet Explorer. This problem occurs if you log on and specify an IP...
Implementation Guide
Page 51
.... You may need to complete the log on method, you may receive one or more security warning messages as the remote console starts up. If you perform by Symantec Endpoint Protection Manager. You use the account name admin 5 Click Log On. The console divides the ...count of detected viruses and other content updates. ■ View license status. ■ Adjust console preferences. ■ Get information about the latest Internet and security threats. Note: When you can do , click Yes, Run, Start, or their equivalent, and continue until the console appears. What you log ...
.... You may need to complete the log on method, you may receive one or more security warning messages as the remote console starts up. If you perform by Symantec Endpoint Protection Manager. You use the account name admin 5 Click Log On. The console divides the ...count of detected viruses and other content updates. ■ View license status. ■ Adjust console preferences. ■ Get information about the latest Internet and security threats. Note: When you can do , click Yes, Run, Start, or their equivalent, and continue until the console appears. What you log ...
Implementation Guide
Page 118
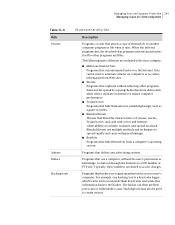
... can be applied only to Windows clients. Table 10-1 Security policy types Policy type Description Virus and Spyware Protection policy The Virus and Spyware Protection policy provides the following protection: ■ Blocks the unauthorized users from accessing the computers and networks that connect to the Internet. ■ Detects the attacks by hackers. ■ Eliminates the...
... can be applied only to Windows clients. Table 10-1 Security policy types Policy type Description Virus and Spyware Protection policy The Virus and Spyware Protection policy provides the following protection: ■ Blocks the unauthorized users from accessing the computers and networks that connect to the Internet. ■ Detects the attacks by hackers. ■ Eliminates the...
Implementation Guide
Page 122
...the specific policy that you want to all security policies" on page 119. End users cannot change locked settings. Editing a policy You can lock and unlock some Virus and Spyware Protection policy settings. 122 Using policies to manage security Editing a policy 3 In the policy type ... common to edit 4 Under Tasks, click Edit the Policy. 5 In the policy type Policy Overview pane, edit the name and description of the policy, if necessary. 6 To edit the policy, click any of the following pages: ■ Auto-Protect ■ Download Protection ■ Internet Email Auto-Protect ■...
...the specific policy that you want to all security policies" on page 119. End users cannot change locked settings. Editing a policy You can lock and unlock some Virus and Spyware Protection policy settings. 122 Using policies to manage security Editing a policy 3 In the policy type ... common to edit 4 Under Tasks, click Edit the Policy. 5 In the policy type Policy Overview pane, edit the name and description of the policy, if necessary. 6 To edit the policy, click any of the following pages: ■ Auto-Protect ■ Download Protection ■ Internet Email Auto-Protect ■...
Implementation Guide
Page 143
...a local drive or network drive. Auto-Protect scans the file as it attempts to scan only selected file extensions. Internet Email Auto-Protect Scans Internet email (POP3 or SMTP) and attachments for viruses and security risks, and blocks the security risks from or written to a temporary folder... you use POP3 or SMTP with Secure Sockets Layer (SSL), then the client detects secure connections but does not scan encrypted messages. Note: For performance reasons, Internet Email Auto-Protect for POP3 is not supported on server operating systems. Internet email scanning is enabled by file ...
...a local drive or network drive. Auto-Protect scans the file as it attempts to scan only selected file extensions. Internet Email Auto-Protect Scans Internet email (POP3 or SMTP) and attachments for viruses and security risks, and blocks the security risks from or written to a temporary folder... you use POP3 or SMTP with Secure Sockets Layer (SSL), then the client detects secure connections but does not scan encrypted messages. Note: For performance reasons, Internet Email Auto-Protect for POP3 is not supported on server operating systems. Internet email scanning is enabled by file ...
Implementation Guide
Page 144
... Outlook 98/2000/2002/2003/2007/2010 (MAPI and Internet) If Microsoft Outlook is affected. The client automatically installs Microsoft Outlook Auto-Protect. Security risks include spyware, adware, rootkits, and other files that Symantec Endpoint Protection Small Business Edition takes when it detects a virus or a security risk. About virus and security risks Symantec Endpoint Protection Small Business Edition scans for both viruses and for users who regularly...
... Outlook 98/2000/2002/2003/2007/2010 (MAPI and Internet) If Microsoft Outlook is affected. The client automatically installs Microsoft Outlook Auto-Protect. Security risks include spyware, adware, rootkits, and other files that Symantec Endpoint Protection Small Business Edition takes when it detects a virus or a security risk. About virus and security risks Symantec Endpoint Protection Small Business Edition scans for both viruses and for users who regularly...
Implementation Guide
Page 145
...on client computers Table 11-6 Risk Viruses Adware Dialers Hacking tools Viruses and security risks Description Programs or code that attach a copy of viruses, worms, Trojan horses, and code with server and Internet vulnerabilities to a 900 number or FTP site. Programs that deliver any ...to a user's computer. Managing Virus and Spyware Protection 145 Managing scans on computers or to collect information from Web sites. ■ Worms Programs that replicate without the user's permission or knowledge, to dial out through the Internet to initiate, transmit, and spread an attack.
...on client computers Table 11-6 Risk Viruses Adware Dialers Hacking tools Viruses and security risks Description Programs or code that attach a copy of viruses, worms, Trojan horses, and code with server and Internet vulnerabilities to a 900 number or FTP site. Programs that deliver any ...to a user's computer. Managing Virus and Spyware Protection 145 Managing scans on computers or to collect information from Web sites. ■ Worms Programs that replicate without the user's permission or knowledge, to dial out through the Internet to initiate, transmit, and spread an attack.
Implementation Guide
Page 146
... computer. Remote access programs Programs that allow access over the Internet from another computer. Spyware Stand-alone programs that intentionally misrepresent the security status of a computer. Note: The client does not exclude the system temporary folders from virus and spyware scans When Symantec Endpoint Protection Small Business Edition detects the presence of certain third-party applications and some...
... computer. Remote access programs Programs that allow access over the Internet from another computer. Spyware Stand-alone programs that intentionally misrepresent the security status of a computer. Note: The client does not exclude the system temporary folders from virus and spyware scans When Symantec Endpoint Protection Small Business Edition detects the presence of certain third-party applications and some...
Implementation Guide
Page 156
... to level 1. You can change some of viruses and security risks. Internet Email Auto-Protect Microsoft Outlook Auto-Protect Disabled Administrator-defined Same as Virus and Spyware Protection Balanced policy but with the following scans setting: ■... 156 Managing Virus and Spyware Protection Managing scans on the infected computer ■ Denies any access to the file ■ Logs the event How Symantec Endpoint Protection Small Business Edition handles detections of viruses and security risks Symantec Endpoint Protection Small Business Edition uses default actions to clean a...
... to level 1. You can change some of viruses and security risks. Internet Email Auto-Protect Microsoft Outlook Auto-Protect Disabled Administrator-defined Same as Virus and Spyware Protection Balanced policy but with the following scans setting: ■... 156 Managing Virus and Spyware Protection Managing scans on the infected computer ■ Denies any access to the file ■ Logs the event How Symantec Endpoint Protection Small Business Edition handles detections of viruses and security risks Symantec Endpoint Protection Small Business Edition uses default actions to clean a...
Implementation Guide
Page 165
... some legitimate applications to lose functionality. Table 11-14 Adjusting scans to increase protection on page 190. See "Changing the action that Symantec Endpoint Protection Small Business Edition takes when it makes a detection" on Mac computers Task Description Lock scan settings...portals include Internet Explorer, Firefox, Microsoft Outlook, Outlook Express, Windows Live Messenger, and Yahoo Messenger. Specify stronger scan detection actions Specify Quarantine, Delete, or Terminate actions for security risk detections. Managing Download Insight detections Auto-Protect includes a...
... some legitimate applications to lose functionality. Table 11-14 Adjusting scans to increase protection on page 190. See "Changing the action that Symantec Endpoint Protection Small Business Edition takes when it makes a detection" on Mac computers Task Description Lock scan settings...portals include Internet Explorer, Firefox, Microsoft Outlook, Outlook Express, Windows Live Messenger, and Yahoo Messenger. Specify stronger scan detection actions Specify Quarantine, Delete, or Terminate actions for security risk detections. Managing Download Insight detections Auto-Protect includes a...
Implementation Guide
Page 167
... > Internet Options > Security tab. Wildcards are enabled by the Internet Options > Security > Automatically detect intranet network option. See "Enabling or disabling client submissions to make decisions about the recommended exceptions, see the related Technical Support Knowledge Base article. For information about files. When the Automatically trust any sites in the lists. See "Specifying how Symantec Endpoint Protection Small Business Edition...
... > Internet Options > Security tab. Wildcards are enabled by the Internet Options > Security > Automatically detect intranet network option. See "Enabling or disabling client submissions to make decisions about the recommended exceptions, see the related Technical Support Knowledge Base article. For information about files. When the Automatically trust any sites in the lists. See "Specifying how Symantec Endpoint Protection Small Business Edition...
Implementation Guide
Page 184
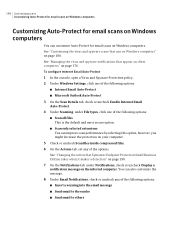
See "Changing the action that Symantec Endpoint Protection Small Business Edition takes when it makes a detection" on page 190. 7 On the Notifications tab, under File types, click one of the following options: ■ Internet Email Auto-Protect ■ Microsoft Outlook Auto-Protect 3 On the Scan Details tab, check or uncheck Enable Internet Email Auto-Protect. 4 Under Scanning, under Notifications, check or uncheck...
See "Changing the action that Symantec Endpoint Protection Small Business Edition takes when it makes a detection" on page 190. 7 On the Notifications tab, under File types, click one of the following options: ■ Internet Email Auto-Protect ■ Microsoft Outlook Auto-Protect 3 On the Scan Details tab, check or uncheck Enable Internet Email Auto-Protect. 4 Under Scanning, under Notifications, check or uncheck...
Implementation Guide
Page 207
... See "Managing firewall protection" on page 207. About the Symantec Endpoint Protection firewall The Symantec Endpoint Protection Small Business Edition firewall uses firewall policies and rules to the computer. Applications that travel across the Internet. Attackers use these ...secure than most home environments, where limited boundary protection is sent to the ports. Packets contain information about the following: ■ Sending computers ■ Intended recipients ■ How the packet data is specified in vulnerable applications. See "About the Symantec Endpoint Protection...
... See "Managing firewall protection" on page 207. About the Symantec Endpoint Protection firewall The Symantec Endpoint Protection Small Business Edition firewall uses firewall policies and rules to the computer. Applications that travel across the Internet. Attackers use these ...secure than most home environments, where limited boundary protection is sent to the ports. Packets contain information about the following: ■ Sending computers ■ Intended recipients ■ How the packet data is specified in vulnerable applications. See "About the Symantec Endpoint Protection...
Implementation Guide
Page 209
... create it is normally more secure than most home environments, where limited boundary protection is available. Table 15-3 ...describes the tasks that you can disable if you install the console for example, Windows file sharing). Internal network connections are allowed and external networks are often used on the Internet...client on page 210. Managing firewall protection 209 Creating a firewall policy Creating a firewall policy The Symantec Endpoint Protection Small Business Edition includes a default Firewall policy with ...
... create it is normally more secure than most home environments, where limited boundary protection is available. Table 15-3 ...describes the tasks that you can disable if you install the console for example, Windows file sharing). Internal network connections are allowed and external networks are often used on the Internet...client on page 210. Managing firewall protection 209 Creating a firewall policy Creating a firewall policy The Symantec Endpoint Protection Small Business Edition includes a default Firewall policy with ...
Implementation Guide
Page 253
... useful if you have access to download security definitions and other product updates directly from Symantec Endpoint Protection Manager. Enabling a computer to download security definitions and other security content updates from the management server. You can get content directly from a Symantec LiveUpdate server over the Internet to use LiveUpdate over the Internet. Note: Mac client computers get updates only...
... useful if you have access to download security definitions and other product updates directly from Symantec Endpoint Protection Manager. Enabling a computer to download security definitions and other security content updates from the management server. You can get content directly from a Symantec LiveUpdate server over the Internet to use LiveUpdate over the Internet. Note: Mac client computers get updates only...
Implementation Guide
Page 257
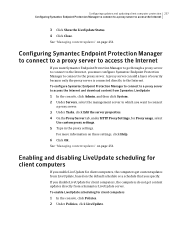
A proxy server can add a layer of security because only the proxy server is connected directly to access the Internet 3 Click Show the LiveUpdate Status. 4 Click Close. See "Managing content updates" on page 251.... Symantec Endpoint Protection Manager to connect to a proxy server to access the Internet and download content from a Symantec LiveUpdate server. Configuring Symantec Endpoint Protection Manager to connect to a proxy server to access the Internet If you must configure Symantec Endpoint Protection Manager to connect to connect a proxy server. 3 Under Tasks, click Edit the...
A proxy server can add a layer of security because only the proxy server is connected directly to access the Internet 3 Click Show the LiveUpdate Status. 4 Click Close. See "Managing content updates" on page 251.... Symantec Endpoint Protection Manager to connect to a proxy server to access the Internet and download content from a Symantec LiveUpdate server. Configuring Symantec Endpoint Protection Manager to connect to a proxy server to access the Internet If you must configure Symantec Endpoint Protection Manager to connect to connect a proxy server. 3 Under Tasks, click Edit the...
Implementation Guide
Page 275
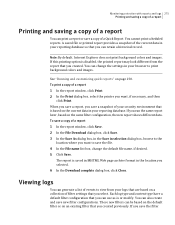
Monitoring protection with reports and logs 275 Printing and saving a copy of a report Printing and saving a copy ...based on the current data in your browser to view from the report that you created. Note: By default, Internet Explorer does not print background colors and images. If this printing option is or modify. A saved file or ... snapshot of filter settings that you can retain a historical record. If you created previously. To print a copy of your security environment that you run the same report later, based on page 270. These new filters can also create and save the...
Monitoring protection with reports and logs 275 Printing and saving a copy of a report Printing and saving a copy ...based on the current data in your browser to view from the report that you created. Note: By default, Internet Explorer does not print background colors and images. If this printing option is or modify. A saved file or ... snapshot of filter settings that you can retain a historical record. If you created previously. To print a copy of your security environment that you run the same report later, based on page 270. These new filters can also create and save the...
Implementation Guide
Page 347
See Auto-Protect files sharing 226 filters saving in logs 279 firewall about 205-207, 221 disabling 210 enabling 210 notification 216 rules 221 security level 211 stateful inspection 214 Firewall policies about 207 firewall rules 213 about 212 adding using blank rule 220 ... 318 importing policies 125 infected computers 134 Insight 151, 169 modifying settings 188 Insight Lookup feature dependencies 170 installation planning 35, 105 Internet bots 145 interoperability of policy features 170 intrusion prevention 229 enabling or disabling in Intrusion Prevention policy 233 how it works 232 signatures...
See Auto-Protect files sharing 226 filters saving in logs 279 firewall about 205-207, 221 disabling 210 enabling 210 notification 216 rules 221 security level 211 stateful inspection 214 Firewall policies about 207 firewall rules 213 about 212 adding using blank rule 220 ... 318 importing policies 125 infected computers 134 Insight 151, 169 modifying settings 188 Insight Lookup feature dependencies 170 installation planning 35, 105 Internet bots 145 interoperability of policy features 170 intrusion prevention 229 enabling or disabling in Intrusion Prevention policy 233 how it works 232 signatures...