Implementation Guide
Page 71
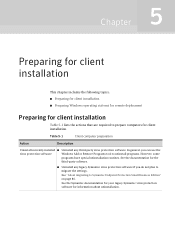
... third-party virus protection software. See "About migrating to Symantec Endpoint Protection Small Business Edition" on page 86. See the Symantec documentation for your legacy Symantec virus protection software for client installation. Table 5-1 Client computer preparation Action Description Uninstall currently installed ■ Uninstall any legacy Symantec virus protection software if you can use the virus protection software Windows Add or Remove Programs tool to uninstall...
... third-party virus protection software. See "About migrating to Symantec Endpoint Protection Small Business Edition" on page 86. See the Symantec documentation for your legacy Symantec virus protection software for client installation. Table 5-1 Client computer preparation Action Description Uninstall currently installed ■ Uninstall any legacy Symantec virus protection software if you can use the virus protection software Windows Add or Remove Programs tool to uninstall...
Implementation Guide
Page 134
...use the Symantec Endpoint Protection Manager Home page and a risk report to identify the computers that risks are infected and at risk or infected because they need to be at risk. You can view the Risk log to make sure that are remediated or removed from the... page 275. The next time the scan runs, Symantec Endpoint Protection Small Business Edition applies the new action. You might be configured to complete remediation Computers may still be restarted to investigate them further. You can run a loadpoint analysis tool that can also access the Security Response Web site from...
...use the Symantec Endpoint Protection Manager Home page and a risk report to identify the computers that risks are infected and at risk or infected because they need to be at risk. You can view the Risk log to make sure that are remediated or removed from the... page 275. The next time the scan runs, Symantec Endpoint Protection Small Business Edition applies the new action. You might be configured to complete remediation Computers may still be restarted to investigate them further. You can run a loadpoint analysis tool that can also access the Security Response Web site from...
Implementation Guide
Page 146
...the controller or hacker's system. Security assessment tool Programs that Symantec Endpoint Protection excludes from virus and spyware scans When Symantec Endpoint Protection Small Business Edition detects the presence of certain third-party applications and some Symantec products, it automatically creates exclusions for unauthorized access...because doing so can exclude files by adding a file or a folder exception to be removed. 146 Managing Virus and Spyware Protection Managing scans on client computers Table 11-6 Viruses and security risks (continued) Risk Description Joke...
...the controller or hacker's system. Security assessment tool Programs that Symantec Endpoint Protection excludes from virus and spyware scans When Symantec Endpoint Protection Small Business Edition detects the presence of certain third-party applications and some Symantec products, it automatically creates exclusions for unauthorized access...because doing so can exclude files by adding a file or a folder exception to be removed. 146 Managing Virus and Spyware Protection Managing scans on client computers Table 11-6 Viruses and security risks (continued) Risk Description Joke...