Data Sheet
Page 1
... Band, which Complies with Windows 98SE/ME/2000/XP/2003 • Supports WEP and WPA/WPA2 Encryptions • Supports Wireless Multimedia Enhancements Quality of Service (QoS) • Low Interference and High Susceptibility Guarantee Reliable Performance • Low Power Consumption and Easy Configurations • Range of 35~100 meters indoor, 100~300 meters outdoor (depends on the environment) • Simple User Setup & Diagnostics Utilities • 3-Year Warranty TEW-604UB...
... Band, which Complies with Windows 98SE/ME/2000/XP/2003 • Supports WEP and WPA/WPA2 Encryptions • Supports Wireless Multimedia Enhancements Quality of Service (QoS) • Low Interference and High Susceptibility Guarantee Reliable Performance • Low Power Consumption and Easy Configurations • Range of 35~100 meters indoor, 100~300 meters outdoor (depends on the environment) • Simple User Setup & Diagnostics Utilities • 3-Year Warranty TEW-604UB...
Data Sheet
Page 2
... Smart Wireless USB 2.0 Adapter (TEW-604UB) Notebook with 108Mbps Smart Wireless USB 2.0 Adapter (TEW-604UB) Internet PACKAGE CONTENTS • TW-604UB • Quick Installation Guide • Utility & Driver CD-ROM • USB 2.0 Cable (1.5m/4.9ft.) RELATED PRODUCTS TEW-601PC TEW-603PI TEW-610APB 108Mbps 802.11g MIMO Wireless PC Card 108Mbps 802.11g MIMO Wireless PCI Adapter 108Mbps 802.11g MIMO Wireless Access Point ORDERING INFORMATION Workstation with 108Mbps Wireless PCI Adapter (TEW-603PI) 108Mbps Wireless Router (TEW-611BRP) USB 108Mbps Wireless Cable/DSL Modem 3135...
... Smart Wireless USB 2.0 Adapter (TEW-604UB) Notebook with 108Mbps Smart Wireless USB 2.0 Adapter (TEW-604UB) Internet PACKAGE CONTENTS • TW-604UB • Quick Installation Guide • Utility & Driver CD-ROM • USB 2.0 Cable (1.5m/4.9ft.) RELATED PRODUCTS TEW-601PC TEW-603PI TEW-610APB 108Mbps 802.11g MIMO Wireless PC Card 108Mbps 802.11g MIMO Wireless PCI Adapter 108Mbps 802.11g MIMO Wireless Access Point ORDERING INFORMATION Workstation with 108Mbps Wireless PCI Adapter (TEW-603PI) 108Mbps Wireless Router (TEW-611BRP) USB 108Mbps Wireless Cable/DSL Modem 3135...
User Guide
Page 2
... with the instructions, may cause harmful interference to radio communications. TRENDnet declares that may not cause harmful interference. (2) This device must accept any other antenna or transmitter. 2. This transmitter must not be required to provide reasonable protection against harmful interference in conjunction with any interference received, including interference that TEW-604UB, (FCC ID: S9ZTEW604UB) is connected. -Consult the...
... with the instructions, may cause harmful interference to radio communications. TRENDnet declares that may not cause harmful interference. (2) This device must accept any other antenna or transmitter. 2. This transmitter must not be required to provide reasonable protection against harmful interference in conjunction with any interference received, including interference that TEW-604UB, (FCC ID: S9ZTEW604UB) is connected. -Consult the...
User Guide
Page 3
...Chapter 1 - Getting Started About Your Super G Smart Wireless USB 2.0 Adapter 9 Package Content 9 System Requirement 9 LED Definition 9 Wireless Utility and Adapter Hardware Installation 10 Using the Utility to Configure Your Network 14 Link Information 15 Site Survey 16 Profile 17 Chapter 3 - Maintenance Uninstalling the Driver 22 Uninstall the Client Utility 22 Upgrading the Wireless Utility 22 Glossary 23 3 Table of Wireless Networks 4 Ad-Hoc (IBSS) Network 4 Infrastructure (BSS) Network 5 Wireless LAN Security 7 Data Encryption with WEP 8 Chapter 2 -
...Chapter 1 - Getting Started About Your Super G Smart Wireless USB 2.0 Adapter 9 Package Content 9 System Requirement 9 LED Definition 9 Wireless Utility and Adapter Hardware Installation 10 Using the Utility to Configure Your Network 14 Link Information 15 Site Survey 16 Profile 17 Chapter 3 - Maintenance Uninstalling the Driver 22 Uninstall the Client Utility 22 Upgrading the Wireless Utility 22 Glossary 23 3 Table of Wireless Networks 4 Ad-Hoc (IBSS) Network 4 Infrastructure (BSS) Network 5 Wireless LAN Security 7 Data Encryption with WEP 8 Chapter 2 -
User Guide
Page 4
... using access points, set up an ad-hoc network, configure all the stations in either of Wireless Networks Wireless LAN networking works in ad-hoc mode. Each access point and its wireless devices are known as peer-to a lower transmission (data) rate. CHANGING NETWORK SETTINGS AND PARTICULARLY SECURITY SETTTINGS SHOULD ONLY BE DONE BY AN AUTHORIZED ADMINISTRATOR. To set up an independent wireless workgroup without an access point, use an access point. This setting allows your adapter to a wired LAN via access points...
... using access points, set up an ad-hoc network, configure all the stations in either of Wireless Networks Wireless LAN networking works in ad-hoc mode. Each access point and its wireless devices are known as peer-to a lower transmission (data) rate. CHANGING NETWORK SETTINGS AND PARTICULARLY SECURITY SETTTINGS SHOULD ONLY BE DONE BY AN AUTHORIZED ADMINISTRATOR. To set up an independent wireless workgroup without an access point, use an access point. This setting allows your adapter to a wired LAN via access points...
User Guide
Page 5
When a number of wireless stations are connected using a single access point, you have a Basic Service Set (BSS). 5
When a number of wireless stations are connected using a single access point, you have a Basic Service Set (BSS). 5
User Guide
Page 7
... a RADIUS (Remote Authentication Dial-In User Service) server either on your adapter starting with RADIUS Server authentication 3. WEP Encryption 4. EAP (Extensible Authentication Protocol) is vital that security settings are not as secure as wired networks, it is used for wireless stations. 1. Wi-Fi Protected Access (WPA) 2. W IRELESS LAN SECURITY Because wireless networks are clearly understood and applied. The list below shows the possible wireless security levels on the WAN or the LAN to provide authentication service for authentication and utilizes dynamic WEP key exchange...
... a RADIUS (Remote Authentication Dial-In User Service) server either on your adapter starting with RADIUS Server authentication 3. WEP Encryption 4. EAP (Extensible Authentication Protocol) is vital that security settings are not as secure as wired networks, it is used for wireless stations. 1. Wi-Fi Protected Access (WPA) 2. W IRELESS LAN SECURITY Because wireless networks are clearly understood and applied. The list below shows the possible wireless security levels on the WAN or the LAN to provide authentication service for authentication and utilizes dynamic WEP key exchange...
User Guide
Page 8
... use the same WEP key for all data packets transmitted between the adapter and the access point or other wireless stations to create WEP keys in the other WLAN adapter(s). THE 152-BIT WEP MUST COMPLY WITH THE WEP SETTING OF YOUR ACCESS POINT OR ROUTER. 8 WEP encryption scrambles all WLAN adapters with this feature in the same WLAN. • For WLAN adapters without the passphrase feature, you to configure up to make wireless networks as secure as the default...
... use the same WEP key for all data packets transmitted between the adapter and the access point or other wireless stations to create WEP keys in the other WLAN adapter(s). THE 152-BIT WEP MUST COMPLY WITH THE WEP SETTING OF YOUR ACCESS POINT OR ROUTER. 8 WEP encryption scrambles all WLAN adapters with this feature in the same WLAN. • For WLAN adapters without the passphrase feature, you to configure up to make wireless networks as secure as the default...
User Guide
Page 9
... network security. 9 Supports IEEE802.1x, WPA/WPA2, WPA-PSK/WPA2-PSK (Wi-Fi Protected Access). 9 Low CPU utilization allowing more computer system resources for other programs. 9 Smart Antenna design. 9 Driver support for Windows 98SE/ME/2000/XP. 2.2 Package Content ¾ Super G Smart Wireless USB 2.0 Adapter ¾ Driver and Utility CD-ROM ¾ Multi-Language Quick Installation Guide 2.3 System Requirement z Pentium class notebook computers with other IEEE 802.11b/g compliant wireless devices...
... network security. 9 Supports IEEE802.1x, WPA/WPA2, WPA-PSK/WPA2-PSK (Wi-Fi Protected Access). 9 Low CPU utilization allowing more computer system resources for other programs. 9 Smart Antenna design. 9 Driver support for Windows 98SE/ME/2000/XP. 2.2 Package Content ¾ Super G Smart Wireless USB 2.0 Adapter ¾ Driver and Utility CD-ROM ¾ Multi-Language Quick Installation Guide 2.3 System Requirement z Pentium class notebook computers with other IEEE 802.11b/g compliant wireless devices...
User Guide
Page 10
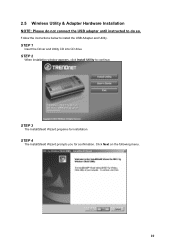
STEP 3 The InstallShield Wizard prepares for confirmation. STEP 4 The InstallShield Wizard prompts you for installation. 2.5 Wireless Utility & Adapter Hardware Installation NOTE: Please do not connect the USB adapter until instructed to install the USB Adapter and Utility. Click Next on the following menu. 10 Follow the instructions below to do so. STEP 1 Insert the Driver and Utility CD into CD drive STEP 2 When installation window appears, click Install Utility to continue.
STEP 3 The InstallShield Wizard prepares for confirmation. STEP 4 The InstallShield Wizard prompts you for installation. 2.5 Wireless Utility & Adapter Hardware Installation NOTE: Please do not connect the USB adapter until instructed to install the USB Adapter and Utility. Click Next on the following menu. 10 Follow the instructions below to do so. STEP 1 Insert the Driver and Utility CD into CD drive STEP 2 When installation window appears, click Install Utility to continue.
User Guide
Page 14
2.6 Using the Utility to Configure Your Network The following are explanations on how to open the Wireless Client Utility. The Wireless Client Utility window as shown below will automatically appear in the IEEE 802.11 Wireless Client Utility. 14 After completing the installation procedure, a new icon as shown below will appear. The user can now use the Utility program. Hold your mouse pointer over the icon, and press the right mouse button to configure and use any of the management functions available in the lower right tray bar.
2.6 Using the Utility to Configure Your Network The following are explanations on how to open the Wireless Client Utility. The Wireless Client Utility window as shown below will automatically appear in the IEEE 802.11 Wireless Client Utility. 14 After completing the installation procedure, a new icon as shown below will appear. The user can now use the Utility program. Hold your mouse pointer over the icon, and press the right mouse button to configure and use any of the management functions available in the lower right tray bar.
User Guide
Page 15
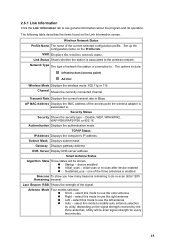
... mode to use the left antenna „ Auto - Disable, WEP, WPA/WPA2, WAP-PSK/WAP2-PSK or 802.1X Authentication Displays the authentication mode. select this mode to use the omni antenna „ Right - Set up the configuration name on the Link Information screen. initial scan or re-scan after device enabled „ Sustained_use - 2.6.1 Link Information Click the Link Information tab to . Network Type The type of the signal. Subnet Mask Displays subnet mask Gateway Displays gateway address DNS Server Display DNS server address Smart Antenna Status...
... mode to use the left antenna „ Auto - Disable, WEP, WPA/WPA2, WAP-PSK/WAP2-PSK or 802.1X Authentication Displays the authentication mode. select this mode to use the omni antenna „ Right - Set up the configuration name on the Link Information screen. initial scan or re-scan after device enabled „ Sustained_use - 2.6.1 Link Information Click the Link Information tab to . Network Type The type of the signal. Subnet Mask Displays subnet mask Gateway Displays gateway address DNS Server Display DNS server address Smart Antenna Status...
User Guide
Page 19
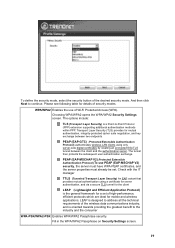
... security mode, select the security button of the wireless data communications industry, and is oriented towards providing the greatest benefit to the industry and the consumer WPA-PSK/WPA2-PSK Enables WPA/WPA2 Passphrase security. Please see following table for mutual authentication, integrity-protected cipher suite negotiation, and key exchange between the client and the authentication server. Choosing WPA/WPA2 opens the WPA/WPA2 Security Settings screen. LEAP is a Point...
... security mode, select the security button of the wireless data communications industry, and is oriented towards providing the greatest benefit to the industry and the consumer WPA-PSK/WPA2-PSK Enables WPA/WPA2 Passphrase security. Please see following table for mutual authentication, integrity-protected cipher suite negotiation, and key exchange between the client and the authentication server. Choosing WPA/WPA2 opens the WPA/WPA2 Security Settings screen. LEAP is a Point...
User Guide
Page 20
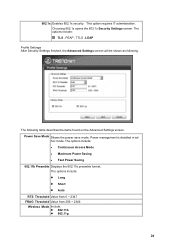
... 256 ~ 2346 Wireless Mode Include: z 802.11b z 802.11g 20 Power Save Mode Shows the power save mode. Power management is disabled in ad hoc mode. The options include: TLS , PEAP , TTLS , LEAP Profile Settings After Security Settings finished, the Advanced Settings screen will be shown as following table describes the items found on the Advanced Settings screen. The options include: z Continuous Access Mode z Maximum Power Saving z Fast Power Saving 802.11b...
... 256 ~ 2346 Wireless Mode Include: z 802.11b z 802.11g 20 Power Save Mode Shows the power save mode. Power management is disabled in ad hoc mode. The options include: TLS , PEAP , TTLS , LEAP Profile Settings After Security Settings finished, the Advanced Settings screen will be shown as following table describes the items found on the Advanced Settings screen. The options include: z Continuous Access Mode z Maximum Power Saving z Fast Power Saving 802.11b...
User Guide
Page 23
... confidentiality, integrity, and authenticity of a base station (access point). By using an external RADIUS server. IEEE 802.1X The IEEE 802.1X standard outlines enhanced security methods for entries elsewhere in order to interact with an EAP-compatible RADIUS server, an access point helps a wireless station and a RADIUS server perform authentication. CHANNEL A radio frequency used below, look for both the authentication of user authentication. EAP AUTHENTICATION EAP (Extensible Authentication Protocol) is the maximum data fragment size...
... confidentiality, integrity, and authenticity of a base station (access point). By using an external RADIUS server. IEEE 802.1X The IEEE 802.1X standard outlines enhanced security methods for entries elsewhere in order to interact with an EAP-compatible RADIUS server, an access point helps a wireless station and a RADIUS server perform authentication. CHANNEL A radio frequency used below, look for both the authentication of user authentication. EAP AUTHENTICATION EAP (Extensible Authentication Protocol) is the maximum data fragment size...
User Guide
Page 24
... SSID (Service Set Identity) is a unique name shared among other factors. Wireless devices must use WPA-PSK/WPA2-PSK (WPA -Pre-Shared Key) that defines stronger encryption, authentication and key management than WPA. 24 USER AUTHENTICATION WPA applies IEEE 802.1X and Extensible Authentication Protocol (EAP) to the network. Both the wireless stations and the access points must have an external RADIUS server, use the same WEP key for choosing the most appropriate AP depending on the signal strength, network utilization...
... SSID (Service Set Identity) is a unique name shared among other factors. Wireless devices must use WPA-PSK/WPA2-PSK (WPA -Pre-Shared Key) that defines stronger encryption, authentication and key management than WPA. 24 USER AUTHENTICATION WPA applies IEEE 802.1X and Extensible Authentication Protocol (EAP) to the network. Both the wireless stations and the access points must have an external RADIUS server, use the same WEP key for choosing the most appropriate AP depending on the signal strength, network utilization...
User Guide
Page 25
...MISUSE, NEGLECT, IMPROPER INSTALLATION OR TESTING, UNAUTHORIZED ATTEMPTS TO REPAIR OR MODIFY, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDED USE, OR BY ACCIDENT, FIRE, LIGHTNING, OR OTHER HAZARD. AC/DC Power Adapter, Cooling Fan, and Power Supply carry 1 Year ...REPAIR, REPLACEMENT, OR REFUND OF THE PURCHASE PRICE PAID, AT TRENDWARE'S OPTION. Governing Law: This Limited Warranty shall be responsible for a Return Material Authorization (RMA) number, accompanied by the laws of the state of customer contained in the manual. All products that are no user serviceable parts...
...MISUSE, NEGLECT, IMPROPER INSTALLATION OR TESTING, UNAUTHORIZED ATTEMPTS TO REPAIR OR MODIFY, OR ANY OTHER CAUSE BEYOND THE RANGE OF THE INTENDED USE, OR BY ACCIDENT, FIRE, LIGHTNING, OR OTHER HAZARD. AC/DC Power Adapter, Cooling Fan, and Power Supply carry 1 Year ...REPAIR, REPLACEMENT, OR REFUND OF THE PURCHASE PRICE PAID, AT TRENDWARE'S OPTION. Governing Law: This Limited Warranty shall be responsible for a Return Material Authorization (RMA) number, accompanied by the laws of the state of customer contained in the manual. All products that are no user serviceable parts...
Quick Installation Guide
Page 8
Click Next. 6. 5. Refer to the steps below. Note: If your wireless network has wireless security, then the Wireless Client Utility will instruct you to enter wireless security settings before continuing to the User's Guide regarding Wireless Secuity. 7. Select Security corresponding to the wireless network and then click Next. Verify Advanced Settings and Wireless Mode and then click Next. 6 English
Click Next. 6. 5. Refer to the steps below. Note: If your wireless network has wireless security, then the Wireless Client Utility will instruct you to enter wireless security settings before continuing to the User's Guide regarding Wireless Secuity. 7. Select Security corresponding to the wireless network and then click Next. Verify Advanced Settings and Wireless Mode and then click Next. 6 English
Quick Installation Guide
Page 9
Click Activate Now. 9. For detailed information regarding the TEW-604UB configuration and advanced settings, please refer to the User's Guide included on the Utility & Driver CDROM or TRENDnet's website at www.trendnet.com 7 English Your installation is Connected. Verify that the Link Status is now complete. 8.
Click Activate Now. 9. For detailed information regarding the TEW-604UB configuration and advanced settings, please refer to the User's Guide included on the Utility & Driver CDROM or TRENDnet's website at www.trendnet.com 7 English Your installation is Connected. Verify that the Link Status is now complete. 8.
Quick Installation Guide
Page 10
... Trendnet's Technical Support Department. Third, you install the Wireless Client Utility (as specified in "D:\Autorun.exe" is selected. A3: Make sure your wireless router or wireless access point's SSID. What should I do ? A4: Go to check and see a networking device with FCC and CE Rules. To access your Device Manager to make sure that the Network Name (SSID) matches your computer meets the minimum requirements as described in the Quick Installation Guide, but my Wireless USB Adapter...
... Trendnet's Technical Support Department. Third, you install the Wireless Client Utility (as specified in "D:\Autorun.exe" is selected. A3: Make sure your wireless router or wireless access point's SSID. What should I do ? A4: Go to check and see a networking device with FCC and CE Rules. To access your Device Manager to make sure that the Network Name (SSID) matches your computer meets the minimum requirements as described in the Quick Installation Guide, but my Wireless USB Adapter...