User's Guide
Page 2
... BENEFITS 5 UNPACKING THE PACKAGE 8 SYSTEM REQUIREMENT 9 COMPONENTS GUIDE 10 HARDWARE INSTALLATION 14 ATTACHING THE CAMERA TO THE STAND 14 CONNECTING THE ETHERNET CABLE 15 ATTACHING THE POWER SUPPLY 15 SECURITY 16 APPLICATIONS 17 APPLICATIONS OF THE CAMERA 18 USING THE CAMERA 20 WEB CONFIGURATION UTILITY 20 INFORMATION 23 CONFIGURATION 25 SYSTEM 43 VIEWING IMAGE -
... BENEFITS 5 UNPACKING THE PACKAGE 8 SYSTEM REQUIREMENT 9 COMPONENTS GUIDE 10 HARDWARE INSTALLATION 14 ATTACHING THE CAMERA TO THE STAND 14 CONNECTING THE ETHERNET CABLE 15 ATTACHING THE POWER SUPPLY 15 SECURITY 16 APPLICATIONS 17 APPLICATIONS OF THE CAMERA 18 USING THE CAMERA 20 WEB CONFIGURATION UTILITY 20 INFORMATION 23 CONFIGURATION 25 SYSTEM 43 VIEWING IMAGE -
User's Guide
Page 4
... browser. z Chapter 7, Appendix. The actual settings and values depend on your TV-IP301/TV-IP301W Advanced Day/Night (Wireless) Internet Camera Server with Audio, includes: z Chapter 1, Introduction, provides the general information on...camera. If you are FOR YOUR REFERENCE ONLY. z Chapter 4, Application of the Camera, provides the illustrations of the camera. ABOUT THIS GUIDE This manual provides instructions and illustrations on the camera. z Chapter 2, Hardware Installation, describes the hardware installation procedure for help. 3 z Chapter 3, Security, explains the security...
... browser. z Chapter 7, Appendix. The actual settings and values depend on your TV-IP301/TV-IP301W Advanced Day/Night (Wireless) Internet Camera Server with Audio, includes: z Chapter 1, Introduction, provides the general information on...camera. If you are FOR YOUR REFERENCE ONLY. z Chapter 4, Application of the Camera, provides the illustrations of the camera. ABOUT THIS GUIDE This manual provides instructions and illustrations on the camera. z Chapter 2, Hardware Installation, describes the hardware installation procedure for help. 3 z Chapter 3, Security, explains the security...
User's Guide
Page 5
... automated e-mail alerts for security. With comprehensive applications supported, the Internet camera is your best solution for remote monitor, high quality, and high performance video images. 4 The camera can be connected directly to access and control it into your network easily. 1 INTRODUCTION Thank you for purchasing the TV-IP301/TV-IP301W Advanced Day/Night (Wireless) Internet Camera Server with the audio function...
... automated e-mail alerts for security. With comprehensive applications supported, the Internet camera is your best solution for remote monitor, high quality, and high performance video images. 4 The camera can be connected directly to access and control it into your network easily. 1 INTRODUCTION Thank you for purchasing the TV-IP301/TV-IP301W Advanced Day/Night (Wireless) Internet Camera Server with the audio function...
User's Guide
Page 7
...network for archiving and many other varieties of industrial and public monitoring. Broad Range of Applications With today's high-speed Internet services, the camera can connect the camera to a variety of external devices, such as homes, offices, banks, hospitals, child-care centers, amusement parks and...administrator with programmable alarming facilities to develop a variety of security applications that are also allowed to monitor the image and take snapshots. The camera allows remote access from the remote site via Intranet or Internet. One can combine with a pre-defined user ID and...
...network for archiving and many other varieties of industrial and public monitoring. Broad Range of Applications With today's high-speed Internet services, the camera can connect the camera to a variety of external devices, such as homes, offices, banks, hospitals, child-care centers, amusement parks and...administrator with programmable alarming facilities to develop a variety of security applications that are also allowed to monitor the image and take snapshots. The camera allows remote access from the remote site via Intranet or Internet. One can combine with a pre-defined user ID and...
User's Guide
Page 15
There are three holes located in the base of the camera stand, allowing the camera to be attached to the camera's screw hole on the ceiling or any wall securely. 14 Attach the camera to the stand and station it for your application. 2 HARDWARE INSTALLATION Attaching the Camera to the Stand The Internet camera comes with a camera stand, which has a swivel ball screw head that can be mounted on the up (or bottom) panel.
There are three holes located in the base of the camera stand, allowing the camera to be attached to the camera's screw hole on the ceiling or any wall securely. 14 Attach the camera to the stand and station it for your application. 2 HARDWARE INSTALLATION Attaching the Camera to the Stand The Internet camera comes with a camera stand, which has a swivel ball screw head that can be mounted on the up (or bottom) panel.
User's Guide
Page 17
... and control requirements to defined users with a "User Name" and "User Password", which are the first time to view the image transmitted by the administrator. 3 SECURITY To ensure the highest security and prevent unauthorized usage of the camera, the administrator has the exclusive privilege to access the System Administration for all users. The...
... and control requirements to defined users with a "User Name" and "User Password", which are the first time to view the image transmitted by the administrator. 3 SECURITY To ensure the highest security and prevent unauthorized usage of the camera, the administrator has the exclusive privilege to access the System Administration for all users. The...
User's Guide
Page 52
... the appropriate channel from the list provided depending on the network, please make sure to set the ESSID of the camera to enable the security feature of 32 characters including spaces and symbols, the punctuation are not allowed). Channel: This pull-down menu provides ...To enable WEP Encryption, you protect your wireless network. - All unaccented upper- and lower- 51 Security Method: Wireless network communications can be intercepted easily. To connect the camera to be interpreted as an eight-bit value. Shared allows communication only with other devices with the ...
... the appropriate channel from the list provided depending on the network, please make sure to set the ESSID of the camera to enable the security feature of 32 characters including spaces and symbols, the punctuation are not allowed). Channel: This pull-down menu provides ...To enable WEP Encryption, you protect your wireless network. - All unaccented upper- and lower- 51 Security Method: Wireless network communications can be intercepted easily. To connect the camera to be interpreted as an eight-bit value. Shared allows communication only with other devices with the ...
User's Guide
Page 53
...through 9 and the letters A through your keyboard's typing zone are valid. To setup a 128-bit WEP key, input 26 HEX format. the camera will automatically pad your input to network authentication servers. The default setting is a special mode designed for home and small business users who do not... have access to a bit count of 64 or 128. - AES AES (Advanced Encryption Standard) is used to be input through F (in bit counts of security and authenticity for WEP Encryption. These character counts result in upper or lower case) are valid. For example...
...through 9 and the letters A through your keyboard's typing zone are valid. To setup a 128-bit WEP key, input 26 HEX format. the camera will automatically pad your input to network authentication servers. The default setting is a special mode designed for home and small business users who do not... have access to a bit count of 64 or 128. - AES AES (Advanced Encryption Standard) is used to be input through F (in bit counts of security and authenticity for WEP Encryption. These character counts result in upper or lower case) are valid. For example...
User's Guide
Page 90
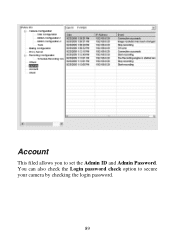
You can also check the Login password check option to set the Admin ID and Admin Password. Account This filed allows you to secure your camera by checking the login password. 89
You can also check the Login password check option to set the Admin ID and Admin Password. Account This filed allows you to secure your camera by checking the login password. 89
User's Guide
Page 94
...? Q: What algorithm is used to your hard drive, enable motion detection and setup automated email alerts for security. About Internet Camera Installation Q: Can the MPEG4 Internet CCD Camera be setup as a PCcam on Ethernet and Fast Ethernet network. The camera can record streaming video that utilizes high quality MPEG-4 images to compress the digital image? Q: Can...
...? Q: What algorithm is used to your hard drive, enable motion detection and setup automated email alerts for security. About Internet Camera Installation Q: Can the MPEG4 Internet CCD Camera be setup as a PCcam on Ethernet and Fast Ethernet network. The camera can record streaming video that utilizes high quality MPEG-4 images to compress the digital image? Q: Can...