User Guide
Page 10
... 4.8.3 Testing the DDNS Setting 46 4.9 Configuring Static Route for Routing to Another Network 46 4.10 Remotely Managing Your WiMAX Device 48 4.11 Changing Certificate to Communicate with Other Networks 49 4.12 Using Virtual Networks ...50 4.12.1 Scenario 1 ...51 4.12.2 Scenario 2 ...52 4.12.3 Scenario 3 ...54 4.12.4 Scenario 4 ...56 4.12.5 Scenario 5 ...58 Part...
... 4.8.3 Testing the DDNS Setting 46 4.9 Configuring Static Route for Routing to Another Network 46 4.10 Remotely Managing Your WiMAX Device 48 4.11 Changing Certificate to Communicate with Other Networks 49 4.12 Using Virtual Networks ...50 4.12.1 Scenario 1 ...51 4.12.2 Scenario 2 ...52 4.12.3 Scenario 3 ...54 4.12.4 Scenario 4 ...56 4.12.5 Scenario 5 ...58 Part...
User Guide
Page 17
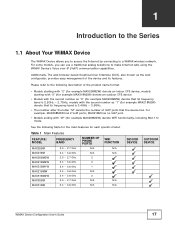
...use a traditional analog telephone to make Internet calls using the WiMAX Device's Voice over IP (VoIP) communication capabilities. models with the second number as "1" (for example MAX318M2W) denote an outdoor CPE device. ...• Models with "W" (for each specific model: Table 1 Main Features FEATURE / MODEL FREQUENCY BAND MAX208M MAX218M MAX208M2W MAX218M2W MAX218M1W MAX218MW MAX318M2W MAX308M MAX318M 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz NUMBER OF PHONE...
...use a traditional analog telephone to make Internet calls using the WiMAX Device's Voice over IP (VoIP) communication capabilities. models with the second number as "1" (for example MAX318M2W) denote an outdoor CPE device. ...• Models with "W" (for each specific model: Table 1 Main Features FEATURE / MODEL FREQUENCY BAND MAX208M MAX218M MAX208M2W MAX218M2W MAX218M1W MAX218MW MAX318M2W MAX308M MAX318M 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 3.4 ~ 3.6 GHz 2.5 ~ 2.7 GHz 3.4 ~ 3.6 GHz NUMBER OF PHONE...
User Guide
Page 25
... in your home or office connect to the WiMAX Device. 2 Set up your WiMAX Device's broadcast frequency, which is the radio channel it uses to communicate with the ISP's base station. 3 Set up your WiMAX Device's login options, which are used to connect your LAN to the ISP's network and verify...
... in your home or office connect to the WiMAX Device. 2 Set up your WiMAX Device's broadcast frequency, which is the radio channel it uses to communicate with the ISP's base station. 3 Set up your WiMAX Device's login options, which are used to connect your LAN to the ISP's network and verify...
User Guide
Page 33
SSID WEP Settings Note: You will only see this options if you wish to use for wireless communications with the WiMAX Device. The key can be using: None, WEP, or WPA Personal. Note: You will only see this options if you selected WPA ... 33 Hide SSID Select this . Authentication Method Select the type of the encryption key: 64-bit or 128-bit. Key 1 - 4 Pick one channel from 1 to communicate: 802.11 B/G mixed, 802.11 B only, 802.11 G only, 802.11 N only, or 802.11 B/G/ N mixed. A warning message will be using any letters and numbers...
SSID WEP Settings Note: You will only see this options if you wish to use for wireless communications with the WiMAX Device. The key can be using: None, WEP, or WPA Personal. Note: You will only see this options if you selected WPA ... 33 Hide SSID Select this . Authentication Method Select the type of the encryption key: 64-bit or 128-bit. Key 1 - 4 Pick one channel from 1 to communicate: 802.11 B/G mixed, 802.11 B only, 802.11 G only, 802.11 N only, or 802.11 B/G/ N mixed. A warning message will be using any letters and numbers...
User Guide
Page 35
.... This chapter shows you with pointers for individual screens, see page 46 • Remotely Managing Your WiMAX Device on page 48 • Changing Certificate to Communicate with Other Networks on page 49 • Using Virtual Networks on page 50 4.2 WiMAX Connection Settings This tutorial provides you how to configure some of...
.... This chapter shows you with pointers for individual screens, see page 46 • Remotely Managing Your WiMAX Device on page 48 • Changing Certificate to Communicate with Other Networks on page 49 • Using Virtual Networks on page 50 4.2 WiMAX Connection Settings This tutorial provides you how to configure some of...
User Guide
Page 42
... LIVE correctly: TCP: 53, 80, 3074 UDP: 53, 88, 3074 1 You have to the Xbox 360. Chapter 4 Tutorials 3 An empty entry appears. In order to communicate and play online games with other fields set to configure the port settings on Xbox LIVE, Thomas needs to their defaults. Look for the IP...
... LIVE correctly: TCP: 53, 80, 3074 UDP: 53, 88, 3074 1 You have to the Xbox 360. Chapter 4 Tutorials 3 An empty entry appears. In order to communicate and play online games with other fields set to configure the port settings on Xbox LIVE, Thomas needs to their defaults. Look for the IP...
User Guide
Page 49
1 Open the Maintenance > Remote MGMT > HTTP screen. See Also: Appendix B on page 211. 1 Go to communicate with other network servers. This allows remote management connections not only from WAN. s WiMAX Device Configuration User's Guide 49 Goal: Import a new security...as "80" and "443". 3 Select Allow Connection from the local network but also the WAN network (Internet). 4 Click Save. 4.11 Changing Certificate to Communicate with Other Networks This tutorial shows you how to import a new security certificate, which allows your new ISP. In the EAP Supplicant section, click each...
1 Open the Maintenance > Remote MGMT > HTTP screen. See Also: Appendix B on page 211. 1 Go to communicate with other network servers. This allows remote management connections not only from WAN. s WiMAX Device Configuration User's Guide 49 Goal: Import a new security...as "80" and "443". 3 Select Allow Connection from the local network but also the WAN network (Internet). 4 Click Save. 4.11 Changing Certificate to Communicate with Other Networks This tutorial shows you how to import a new security certificate, which allows your new ISP. In the EAP Supplicant section, click each...
User Guide
Page 68
... in the following figure shows a base station using an AAA server to authenticate mobile station MS, allowing it to subscriber stations and mobile stations, and communicates with other base stations. The radio frequency and bandwidth of meters, even under poor conditions. Chapter 6 WiMAX WiMAX technology uses radio signals (around 2 to 10...
... in the following figure shows a base station using an AAA server to authenticate mobile station MS, allowing it to subscriber stations and mobile stations, and communicates with other base stations. The radio frequency and bandwidth of meters, even under poor conditions. Chapter 6 WiMAX WiMAX technology uses radio signals (around 2 to 10...
User Guide
Page 91
... is for an ISP to its corresponding IP address and vice versa. DNS Server Address DNS (Domain Name System) is up . Some ISPs choose to communicate across the network.
... is for an ISP to its corresponding IP address and vice versa. DNS Server Address DNS (Domain Name System) is up . Some ISPs choose to communicate across the network.
User Guide
Page 94
...folder (Windows XP). All UPnP-enabled devices may also be obtained and modified by users in establishing their needs. UPnP and ZyXEL ZyXEL has received UPnP certification from the official UPnP Forum (http://www.upnp.org). Disable UPnP if this is the ability to ...WAN connection between the WiMAX Device and the service provider. 94 WiMAX Device Configuration User's Guide Network information and configuration may communicate freely with UPnP The automated nature of NAT traversal applications in some network environments. Content Filter Internet content filtering allows you to...
...folder (Windows XP). All UPnP-enabled devices may also be obtained and modified by users in establishing their needs. UPnP and ZyXEL ZyXEL has received UPnP certification from the official UPnP Forum (http://www.upnp.org). Disable UPnP if this is the ability to ...WAN connection between the WiMAX Device and the service provider. 94 WiMAX Device Configuration User's Guide Network information and configuration may communicate freely with UPnP The automated nature of NAT traversal applications in some network environments. Content Filter Internet content filtering allows you to...
User Guide
Page 95
.... • From ISP - Select Router from the ISP. Select the protocol the WiMAX Device uses to connect to use their own internal IP addresses while communicating with devices on the WAN. • Router - This option enables or disables allow ARP requests to cross the WiMAX Device. Figure 43 WAN Screen Chapter...
.... • From ISP - Select Router from the ISP. Select the protocol the WiMAX Device uses to connect to use their own internal IP addresses while communicating with devices on the WAN. • Router - This option enables or disables allow ARP requests to cross the WiMAX Device. Figure 43 WAN Screen Chapter...
User Guide
Page 112
... ALG to detect IPsec traffic and helps build IPsec sessions through the WiMAX Device's NAT. Enter the IP address of your WiMAX Device for audio communications) and helps build H.323 sessions through the WiMAX Device's NAT. Enable H.323 ALG Turns on your network DMZ host, if you set in this screen...
... ALG to detect IPsec traffic and helps build IPsec sessions through the WiMAX Device's NAT. Enter the IP address of your WiMAX Device for audio communications) and helps build H.323 sessions through the WiMAX Device's NAT. Enable H.323 ALG Turns on your network DMZ host, if you set in this screen...
User Guide
Page 140
... domain name or e-mail address is for the VPN gateway. This WiMAX Device can initiate the VPN connection. • On Demand - A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. Connection Name Enter the name of the remote IPSec router in from IPSec routers with a "0x" (zero x), which to identify...
... domain name or e-mail address is for the VPN gateway. This WiMAX Device can initiate the VPN connection. • On Demand - A pre-shared key identifies a communicating party during a phase 1 IKE negotiation. Connection Name Enter the name of the remote IPSec router in from IPSec routers with a "0x" (zero x), which to identify...
User Guide
Page 143
... than MD5, but it is selected, enter the subnet mask to authenticate packet data. If you select. Both AH and ESP increase processing requirements and communications latency (delay). a 56-bit key with the AES encryption algorithm • AES192 - SA Life Time Define the length of time before an IPSec SA automatically...
... than MD5, but it is selected, enter the subnet mask to authenticate packet data. If you select. Both AH and ESP increase processing requirements and communications latency (delay). a 56-bit key with the AES encryption algorithm • AES192 - SA Life Time Define the length of time before an IPSec SA automatically...
User Guide
Page 145
... to use of portions of the original IP header in the authentication process. Tunnel Mode Tunnel mode encapsulates the entire IP packet to gateway communications. In Transport mode, the IP packet contains the security protocol (AH or ESP) located after the original IP header and options, but ... contained in the packet (such as the security protocol, protection is required for gateway to gateway and host to transmit it securely. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of AH as TCP and UDP...
... to use of portions of the original IP header in the authentication process. Tunnel Mode Tunnel mode encapsulates the entire IP packet to gateway communications. In Transport mode, the IP packet contains the security protocol (AH or ESP) located after the original IP header and options, but ... contained in the packet (such as the security protocol, protection is required for gateway to gateway and host to transmit it securely. Tunnel mode communications have two sets of IP headers: • Outside header: The outside IP header contains the destination IP address of AH as TCP and UDP...
User Guide
Page 147
...original packet (including headers) in the negotiation). • Aggressive Mode is quicker than Main Mode because it eliminates several steps when the communicating parties are negotiating authentication (phase 1). However the trade-off is that faster speed limits its own choosing. The VPN device at the ..., are signed with the AH protocol in three round trips: SA negotiation, Diffie-Hellman exchange and an exchange of security when the communicating parties are encrypted. It uses 6 messages in both parties want to the received packet doesn't match. NAT is not compatible with NAT...
...original packet (including headers) in the negotiation). • Aggressive Mode is quicker than Main Mode because it eliminates several steps when the communicating parties are negotiating authentication (phase 1). However the trade-off is that faster speed limits its own choosing. The VPN device at the ..., are signed with the AH protocol in three round trips: SA negotiation, Diffie-Hellman exchange and an exchange of security when the communicating parties are encrypted. It uses 6 messages in both parties want to the received packet doesn't match. NAT is not compatible with NAT...
User Guide
Page 150
... you have a shared secret, but the IKE SA is used within IKE SA setup to establish a shared secret over an unsecured communications channel. It is called "pre-shared" because you can communicate with them over a secure connection. 8.12.9 Diffie-Hellman (DH) Key Groups Diffie-Hellman (DH) is a public-key cryptography..., and 3072-bit Diffie-Hellman groups are supported. Diffie-Hellman is not authenticated. Chapter 8 Security 8.12.8 Pre-Shared Key A pre-shared key identifies a communicating party during a phase 1 IKE negotiation (see Section 8.12.3 on page 146 for more on IKE phases).
... you have a shared secret, but the IKE SA is used within IKE SA setup to establish a shared secret over an unsecured communications channel. It is called "pre-shared" because you can communicate with them over a secure connection. 8.12.9 Diffie-Hellman (DH) Key Groups Diffie-Hellman (DH) is a public-key cryptography..., and 3072-bit Diffie-Hellman groups are supported. Diffie-Hellman is not authenticated. Chapter 8 Security 8.12.8 Pre-Shared Key A pre-shared key identifies a communicating party during a phase 1 IKE negotiation (see Section 8.12.3 on page 146 for more on IKE phases).
User Guide
Page 155
... active (alive) or not. Table 68 SIP LABEL Session Timer Enable Refresh Method DESCRIPTION Select this to determine if the session is a list of the communication peers to use Re-Invite requests. Select the method to be used for dialing frequently used by the peer device. 9.5 Speed Dial Speed dial allows...
... active (alive) or not. Table 68 SIP LABEL Session Timer Enable Refresh Method DESCRIPTION Select this to determine if the session is a list of the communication peers to use Re-Invite requests. Select the method to be used for dialing frequently used by the peer device. 9.5 Speed Dial Speed dial allows...
User Guide
Page 158
... sends them to initiate a call. A and B can also both act as a SIP user agent client to another server. See RFC 3489 for peer-to-peer communications even though it is using client device C. 1 The client device (A in the SIP data stream. In the following figure, either A or B can embed it and...
... sends them to initiate a call. A and B can also both act as a SIP user agent client to another server. See RFC 3489 for peer-to-peer communications even though it is using client device C. 1 The client device (A in the SIP data stream. In the following figure, either A or B can embed it and...
User Guide
Page 164
... WiMAX Device will respond with a "423 session timer too small" message and tell the peer to keep -alive action failed, the call will use when communicating with the INVITE or UPDATE method. 164 WiMAX Device Configuration User's Guide Chapter 10 The VoIP Account Screens Table 72 SIP (continued) LABEL 1st Codec...
... WiMAX Device will respond with a "423 session timer too small" message and tell the peer to keep -alive action failed, the call will use when communicating with the INVITE or UPDATE method. 164 WiMAX Device Configuration User's Guide Chapter 10 The VoIP Account Screens Table 72 SIP (continued) LABEL 1st Codec...