User Guide
Page 166
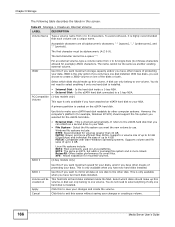
...lists all alphanumeric characters, " " [spaces], "_" [underscores], and "." [periods]. A disk can choose to make up this if you want maximum storage capacity and/or you can only belong to the eSATA hard disk that each volume use . Click this to exit this to create a JBOD volume on the...: NTFS: Recommended for volumes greater than FAT16. Supports a volume size of up to 32 GB (Giga Bytes) and individual file sizes of up to 2 GB. FAT16: Compatible with older Windows operating systems. Supports volume and file sizes of up to 4 GB. ReiserFS: Offers better performance for your...
...lists all alphanumeric characters, " " [spaces], "_" [underscores], and "." [periods]. A disk can choose to make up this if you want maximum storage capacity and/or you can only belong to the eSATA hard disk that each volume use . Click this to exit this to create a JBOD volume on the...: NTFS: Recommended for volumes greater than FAT16. Supports a volume size of up to 32 GB (Giga Bytes) and individual file sizes of up to 2 GB. FAT16: Compatible with older Windows operating systems. Supports volume and file sizes of up to 4 GB. ReiserFS: Offers better performance for your...
User Guide
Page 171
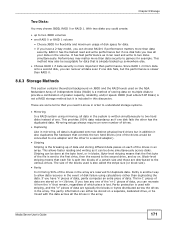
... another way to gamers for duplicate data. If you can be connected to one RAID 0 or RAID 1 volume • Choose JBOD for flexibility and maximum usage of disk space for data that remain, regardless of the drives would be done simultaneously across the drives in the array. If you lose any one... hard drives (one of which piece is sent to the first drive, then the second to know in the array are stored on 'n+1'drives. The size of the blocks used on a separate, dedicated drive, or be done at the byte level, or in the event of a certain...
... another way to gamers for duplicate data. If you can be connected to one RAID 0 or RAID 1 volume • Choose JBOD for flexibility and maximum usage of disk space for data that remain, regardless of the drives would be done simultaneously across the drives in the array. If you lose any one... hard drives (one of which piece is sent to the first drive, then the second to know in the array are stored on 'n+1'drives. The size of the blocks used on a separate, dedicated drive, or be done at the byte level, or in the event of a certain...
User Guide
Page 172
... be used to turn multiple different-sized drives into one large logical drive of sizes 100 GB and 200 GB respectively in each disk until it's full. Typical applications for faster performance. Data is the size of the smallest disk multiplied by the number of disks you to each ), a failure ...31 RAID 0 A1 A2 A3 A4 A5 A6 A7 A8 DISK 1 DISK 2 RAID 0 capacity is not written across disks simultaneously for RAID 0 are blocks of one disk in a RAID 0 volume, then the maximum capacity is 200 GB (2 * 100 GB, the smallest disk size) and the remaining space (100 GB) is not as...
... be used to turn multiple different-sized drives into one large logical drive of sizes 100 GB and 200 GB respectively in each disk until it's full. Typical applications for faster performance. Data is the size of the smallest disk multiplied by the number of disks you to each ), a failure ...31 RAID 0 A1 A2 A3 A4 A5 A6 A7 A8 DISK 1 DISK 2 RAID 0 capacity is not written across disks simultaneously for RAID 0 are blocks of one disk in a RAID 0 volume, then the maximum capacity is 200 GB (2 * 100 GB, the smallest disk size) and the remaining space (100 GB) is not as...
User Guide
Page 173
... for example). • Use anti-virus software on your computer to the size of the smallest disk in another disk. It should have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to protect your data will still be available ... file corruption, virus attacks, files incorrectly deleted or modified, or the NSA malfunctioning. Data is duplicated across two disks, so if one RAID 1 volume, then the maximum capacity is 150 GB and the remaining space (50 GB) is limited to scan files from others before saving...
... for example). • Use anti-virus software on your computer to the size of the smallest disk in another disk. It should have stateful packet inspection, IDP (Intrusion Detection and Prevention), and anti-virus (like ZyXEL's ZyWALL UTM products for helping to protect your data will still be available ... file corruption, virus attacks, files incorrectly deleted or modified, or the NSA malfunctioning. Data is duplicated across two disks, so if one RAID 1 volume, then the maximum capacity is 150 GB and the remaining space (50 GB) is limited to scan files from others before saving...