2008 HP business notebook PC F10 Setup overview
Page 2
...; HP Compaq 6535b • HP EliteBook 8530w • HP Compaq 6535s • HP EliteBook 8530p • HP Compaq 6531s • HP EliteBook 6930p • HP Compaq 6530b • HP Compaq 6830s • HP Compaq 6530s • HP Compaq 6735b • HP EliteBook 2730p • HP Compaq 6735s • HP EliteBook 2530p • HP Compaq 6730b • HP Compaq 2230s • HP Compaq 6730s Since 1999 HP Compaq business notebooks have utilized a text based F10...
...; HP Compaq 6535b • HP EliteBook 8530w • HP Compaq 6535s • HP EliteBook 8530p • HP Compaq 6531s • HP EliteBook 6930p • HP Compaq 6530b • HP Compaq 6830s • HP Compaq 6530s • HP Compaq 6735b • HP EliteBook 2730p • HP Compaq 6735s • HP EliteBook 2530p • HP Compaq 6730b • HP Compaq 2230s • HP Compaq 6730s Since 1999 HP Compaq business notebooks have utilized a text based F10...
2008 HP business notebook PC F10 Setup overview
Page 7
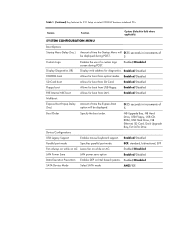
...Enabled/Disabled PXE Internal NIC boot Allows for boot from optical media. Table 1. (Continued) Key features for F10 Setup on select 2008 HP business notebook PCs Feature Function Options (Default in increments of a custom logo screen during POST. 5 Custom Logo Enables the use of ... for boot from LAN. ECP, standard, bidirectional, EPP Fan Always on while on AC Leave fan on while on Intel based systems. Enabled/Disabled SATA Device Mode Select SATA mode AHCI/IDE Enabled/Disabled SD Card boot Allows for diagnostics. Enabled/Disabled Multiboot: Express Boot Popup Delay...
...Enabled/Disabled PXE Internal NIC boot Allows for boot from optical media. Table 1. (Continued) Key features for F10 Setup on select 2008 HP business notebook PCs Feature Function Options (Default in increments of a custom logo screen during POST. 5 Custom Logo Enables the use of ... for boot from LAN. ECP, standard, bidirectional, EPP Fan Always on while on AC Leave fan on while on Intel based systems. Enabled/Disabled SATA Device Mode Select SATA mode AHCI/IDE Enabled/Disabled SD Card boot Allows for diagnostics. Enabled/Disabled Multiboot: Express Boot Popup Delay...
2008 HP business notebook PC F10 Setup overview
Page 8
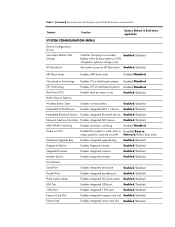
... Card Slot Enables integrated express card slot. Info button access to HP QuickLook. Enabled/Disabled Modem Device Enables integrated modem. Enabled/Disabled Smart Card Enables integrated smart card slot. Enabled/Disabled Wake on Intel based systems. Enabled/Disabled Dual Core CPU Enables dual processor cores. Enabled/Disabled 1394 Port Enables integrated 1394 port. Table 1. (Continued...
... Card Slot Enables integrated express card slot. Info button access to HP QuickLook. Enabled/Disabled Modem Device Enables integrated modem. Enabled/Disabled Smart Card Enables integrated smart card slot. Enabled/Disabled Wake on Intel based systems. Enabled/Disabled Dual Core CPU Enables dual processor cores. Enabled/Disabled 1394 Port Enables integrated 1394 port. Table 1. (Continued...
2008 HP business notebook PC F10 Setup overview
Page 10
... Use of BIOS password to authenticate and boot the BIOS • Use of BIOS password to access F10 based on , the end-user is an integral component of the overall authentication process; HP business notebooks offer a range of pre-boot authentication solutions, allowing businesses to provide an additional layer of protection... Windows, a process known as biometrics, smart cards and passwords) and enablement of uses cannot change their password in Windows are created by the HP ProtectTools security solution from a device other than the primary hard drive. user accounts created in F10.
... Use of BIOS password to authenticate and boot the BIOS • Use of BIOS password to access F10 based on , the end-user is an integral component of the overall authentication process; HP business notebooks offer a range of pre-boot authentication solutions, allowing businesses to provide an additional layer of protection... Windows, a process known as biometrics, smart cards and passwords) and enablement of uses cannot change their password in Windows are created by the HP ProtectTools security solution from a device other than the primary hard drive. user accounts created in F10.
2008 HP business notebook PC F10 Setup overview
Page 14
...and performance to contact the IT helpdesk for assistance, thus saving considerable time for the user and helpdesk expense for EFI based utilities - HP QuickLook is a storage interface bus used by pressing a single button. Timings may vary depending on EFI and the Q ...& A What is a set of modular interfaces that replaces the set of Independent Disks (RAID) technology, which is a Personal Information Manager (PIM) viewer for connecting mass storage devices...
...and performance to contact the IT helpdesk for assistance, thus saving considerable time for the user and helpdesk expense for EFI based utilities - HP QuickLook is a storage interface bus used by pressing a single button. Timings may vary depending on EFI and the Q ...& A What is a set of modular interfaces that replaces the set of Independent Disks (RAID) technology, which is a Personal Information Manager (PIM) viewer for connecting mass storage devices...
installing UEFi-based Microsoft Windows Vista SP1 (x64) on HP EliteBook and Compaq Notebook PCs
Page 4
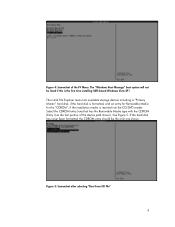
... hard disk has never been formatted, the CDROM entry should be listed if this is the first time installing UEFI-based Windows Vista SP1 The initial File Explorer menu lists available storage devices including a "Primary Master" hard disk, if the hard disk is formatted, and an entry for Removable Media for the... the only one that has the Removable Media type with the CDROM (Entry1) as the last portion of the F9 Menu. Figure 4: Screenshot of the device path shown). Figure 5: Screenshot after selecting "Boot from EFI File" 4
... hard disk has never been formatted, the CDROM entry should be listed if this is the first time installing UEFI-based Windows Vista SP1 The initial File Explorer menu lists available storage devices including a "Primary Master" hard disk, if the hard disk is formatted, and an entry for Removable Media for the... the only one that has the Removable Media type with the CDROM (Entry1) as the last portion of the F9 Menu. Figure 4: Screenshot of the device path shown). Figure 5: Screenshot after selecting "Boot from EFI File" 4
Installing Windows 7 on HP Compaq and EliteBook Notebook PCs
Page 6
...HP 3D DriveGuard will exhibit anomalous behavior when an external display device is connected directly to resume from hibernation with BitLocker enabled might lock when resuming from hibernation. Docking / external video switching Anomaly: Some models lock up when attempting to the system or through a docking base...disc encryption. Unrecognized devices in Device Manager Anomaly: Several devices aren't recognized after installing Windows 7 Beta Description: Base System Device, Fingerprint Sensor, PCI Serial Port, PCI Simple Communications Controller, and Unknown devices lack drivers in ...
...HP 3D DriveGuard will exhibit anomalous behavior when an external display device is connected directly to resume from hibernation with BitLocker enabled might lock when resuming from hibernation. Docking / external video switching Anomaly: Some models lock up when attempting to the system or through a docking base...disc encryption. Unrecognized devices in Device Manager Anomaly: Several devices aren't recognized after installing Windows 7 Beta Description: Base System Device, Fingerprint Sensor, PCI Serial Port, PCI Simple Communications Controller, and Unknown devices lack drivers in ...
Trusted Execution Technology and Tboot Implementation
Page 2
Based on DVD. 2. Locked, Enabled and Activated, VT- Go to ...TXT- Go to Security Æ Setup BIOS Administrator Password to Security Æ TPM Embedded Security Æ Embedded Security Device State Æ Enabled 3. Go to verify the Intel TXT 'verified launch processes. Launch Control Policy (LCP) is... arguments (hit tab) at some point in the future, then it is a verification mechanism used to System Configuration Æ Device Configurations Æ Virtualization Technology Æ Enabled 4. Go to max 2 Fedora Installation 1. kernel/VMM module that uses Intel(R) ...
Based on DVD. 2. Locked, Enabled and Activated, VT- Go to ...TXT- Go to Security Æ Setup BIOS Administrator Password to Security Æ TPM Embedded Security Æ Embedded Security Device State Æ Enabled 3. Go to verify the Intel TXT 'verified launch processes. Launch Control Policy (LCP) is... arguments (hit tab) at some point in the future, then it is a verification mechanism used to System Configuration Æ Device Configurations Æ Virtualization Technology Æ Enabled 4. Go to max 2 Fedora Installation 1. kernel/VMM module that uses Intel(R) ...
Trusted Execution Technology and Tboot Implementation
Page 9
TBOOT: user-provided SINIT found: /SINIT.BIN TBOOT: chipset ids: vendor=8086, device=9000, revision=7f TBOOT: 1 ACM chipset id entries: TBOOT: vendor=8086, device=9000, flags=1, revision=3f, extended=0 TBOOT: copied SINIT (size=66c0) to 3aa00000 TBOOT: AC mod base alignment OK TBOOT: AC mod size OK TBOOT: AC module header dump for...
TBOOT: user-provided SINIT found: /SINIT.BIN TBOOT: chipset ids: vendor=8086, device=9000, revision=7f TBOOT: 1 ACM chipset id entries: TBOOT: vendor=8086, device=9000, flags=1, revision=3f, extended=0 TBOOT: copied SINIT (size=66c0) to 3aa00000 TBOOT: AC mod base alignment OK TBOOT: AC mod size OK TBOOT: AC module header dump for...
HP ProtectTools - Windows Vista and Windows XP
Page 9
HP ProtectTools features 3 Device Access Manager for HP ProtectTools (select ● Device Access Manager allows IT managers to control access to models only) devices based on user profiles. ● Device Access Manager prevents unauthorized users from removing data using external storage media and from ...Microsoft Outlook and Internet Explorer) for specific individuals or groups of users. Module Key features Embedded Security for HP ProtectTools (select models only) ● Embedded Security uses a Trusted Platform Module (TPM) embedded security chip to help protect ...
HP ProtectTools features 3 Device Access Manager for HP ProtectTools (select ● Device Access Manager allows IT managers to control access to models only) devices based on user profiles. ● Device Access Manager prevents unauthorized users from removing data using external storage media and from ...Microsoft Outlook and Internet Explorer) for specific individuals or groups of users. Module Key features Embedded Security for HP ProtectTools (select models only) ● Embedded Security uses a Trusted Platform Module (TPM) embedded security chip to help protect ...
HP ProtectTools - Windows Vista and Windows XP
Page 13
...policies If a mandate goes into effect that requires the use of strong password policy for dozens of Web-based applications and databases, Credential Manager for HP ProtectTools provides a protected repository for passwords and Single Sign On convenience using the following procedures: ◦ Embedded...: ● Credential Manager "Setup procedures on page 11" ● "Using Single Sign On on page 17" ● Device Access Manager for HP ProtectTools helps protect sensitive user data or credentials stored locally on a PC using the following features help prevent unauthorized access: ●...
...policies If a mandate goes into effect that requires the use of strong password policy for dozens of Web-based applications and databases, Credential Manager for HP ProtectTools provides a protected repository for passwords and Single Sign On convenience using the following procedures: ◦ Embedded...: ● Credential Manager "Setup procedures on page 11" ● "Using Single Sign On on page 17" ● Device Access Manager for HP ProtectTools helps protect sensitive user data or credentials stored locally on a PC using the following features help prevent unauthorized access: ●...
HP ProtectTools - Windows Vista and Windows XP
Page 19
... any USB port. If a smart card or USB token was selected as that can provide a strong form of authentication when it uses cryptography-based identification and proof of your fingerprints and setting up the fingerprint reader 1. Logging on to a USB port. Type the User PIN, select Register.... 2. Setting up the fingerprint reader. 4. Rather than deploying the smart chip on a plastic credit platform, the smart chip is displayed. 6. In HP ProtectTools Security Manager, click Credential Manager in the core functionality of device, and then click Next. 4.
... any USB port. If a smart card or USB token was selected as that can provide a strong form of authentication when it uses cryptography-based identification and proof of your fingerprints and setting up the fingerprint reader 1. Logging on to a USB port. Type the User PIN, select Register.... 2. Setting up the fingerprint reader. 4. Rather than deploying the smart chip on a plastic credit platform, the smart chip is displayed. 6. In HP ProtectTools Security Manager, click Credential Manager in the core functionality of device, and then click Next. 4.
HP ProtectTools - Windows Vista and Windows XP
Page 75
...following 2 sections to enable and initialize the embedded security chip. Press f10 to accept the changes to Enable. 7. Select Embedded security device state and change to the Embedded Security configuration. 8. If you have not set an administrator password, use the arrow keys to select...Setup utility. Then follow the on or restarting the computer, and then pressing f10 while the "f10 = ROM Based Setup" message is displayed in BIOS Configuration for HP ProtectTools. Setup procedures 69 Failure to select TPM Embedded Security, and then press enter. 5. To enable the embedded ...
...following 2 sections to enable and initialize the embedded security chip. Press f10 to accept the changes to Enable. 7. Select Embedded security device state and change to the Embedded Security configuration. 8. If you have not set an administrator password, use the arrow keys to select...Setup utility. Then follow the on or restarting the computer, and then pressing f10 while the "f10 = ROM Based Setup" message is displayed in BIOS Configuration for HP ProtectTools. Setup procedures 69 Failure to select TPM Embedded Security, and then press enter. 5. To enable the embedded ...
HP ProtectTools - Windows Vista and Windows XP
Page 86
...base article 813301 at http://www.microsoft.com for Remote Desktop Connection (RDP) are set to click Security, and then clickSetup Password. If the user logs on to Windows first, then the user must select Credential Manager and log on to log on . Select Embedded Security Device. 4. HP...after the ROM is restored to is researching a workaround for future product enhancements. HP is reset to factory settings after transitioning from sleep mode to select Embedded Security Device-Disable. Update Windows to fail. logon failure: User account restriction. Credential Manager ...
...base article 813301 at http://www.microsoft.com for Remote Desktop Connection (RDP) are set to click Security, and then clickSetup Password. If the user logs on to Windows first, then the user must select Credential Manager and log on to log on . Select Embedded Security Device. 4. HP...after the ROM is restored to is researching a workaround for future product enhancements. HP is reset to factory settings after transitioning from sleep mode to select Embedded Security Device-Disable. Update Windows to fail. logon failure: User account restriction. Credential Manager ...
HP ProtectTools - Windows Vista and Windows XP
Page 96
...the BIOS Embedded Security password prompt. these plug-ins to make TPM preboot work after reenabling Embedded Security Device, Power-on . The first user will be provided in future Web-based ROM SoftPaq offerings. 90 Chapter 9 Troubleshooting The user has to change their PIN or create another user... an error is configured by changing the OS Basic User password and authenticating it depends on a resolution, which will have finished loading. HP recommends that the customer's IT department follow "best practices" in to the system after reset. Since PTHOST.exe is not being reset ...
...the BIOS Embedded Security password prompt. these plug-ins to make TPM preboot work after reenabling Embedded Security Device, Power-on . The first user will be provided in future Web-based ROM SoftPaq offerings. 90 Chapter 9 Troubleshooting The user has to change their PIN or create another user... an error is configured by changing the OS Basic User password and authenticating it depends on a resolution, which will have finished loading. HP recommends that the customer's IT department follow "best practices" in to the system after reset. Since PTHOST.exe is not being reset ...
Security - Windows XP, Windows Vista and Windows 7
Page 5
...Security solutions are listed in the following table. For information about ordering the CompuTrace software, go to the contents of the computer HP ProtectTools Security Manager, in select regions. The Windows® operating system offers certain security features. Most of risks. To protect... slot (used even when the operating system is a preinstalled, ROM-based utility that can protect the computer, personal information, and data from a variety of these additional security features can use either a pointing device (TouchPad, pointing stick, or USB mouse) or the keyboard to ...
...Security solutions are listed in the following table. For information about ordering the CompuTrace software, go to the contents of the computer HP ProtectTools Security Manager, in select regions. The Windows® operating system offers certain security features. Most of risks. To protect... slot (used even when the operating system is a preinstalled, ROM-based utility that can protect the computer, personal information, and data from a variety of these additional security features can use either a pointing device (TouchPad, pointing stick, or USB mouse) or the keyboard to ...
Wireless (Select Models Only) - Windows Vista and Windows XP
Page 5
...GHz. ● 802.11g supports data rates of up to 54 Mbps and operates at 2.4 GHz or 5 GHz, making it may operate at a frequency of 5 GHz. In a WLAN, each other devices, and devices... mobile wireless device communicates with a wireless router or a wireless access point. ● HP Mobile Broadband Module-A wireless wide area network (WWAN) device that provides ...be relatively close together- In a WWAN, each device communicates directly with other . In a PAN, each mobile device communicates to a mobile network operator's base station. If the final specifications differ from the draft...
...GHz. ● 802.11g supports data rates of up to 54 Mbps and operates at 2.4 GHz or 5 GHz, making it may operate at a frequency of 5 GHz. In a WLAN, each other devices, and devices... mobile wireless device communicates with a wireless router or a wireless access point. ● HP Mobile Broadband Module-A wireless wide area network (WWAN) device that provides ...be relatively close together- In a WWAN, each device communicates directly with other . In a PAN, each mobile device communicates to a mobile network operator's base station. If the final specifications differ from the draft...
Wireless (Select Models Only) - Windows Vista and Windows XP
Page 12
...unauthorized access. With the correct wireless transmitter, you set up your own key, generate a different key, or choose other WLAN devices can allow the network to well-known and well-documented security weaknesses. It also generates different sets of sophisticated encryption protocols is ... noncritical e-mail and basic Internet surfing. Protecting your WLAN Because the WLAN standard was designed with built-in security Many wireless base stations, gateways, and routers provide built-in many varieties, both software and hardware. If you can set up unprotected signals...
...unauthorized access. With the correct wireless transmitter, you set up your own key, generate a different key, or choose other WLAN devices can allow the network to well-known and well-documented security weaknesses. It also generates different sets of sophisticated encryption protocols is ... noncritical e-mail and basic Internet surfing. Protecting your WLAN Because the WLAN standard was designed with built-in security Many wireless base stations, gateways, and routers provide built-in many varieties, both software and hardware. If you can set up unprotected signals...
Wireless (Select Models Only) - Windows XP
Page 5
...the draft specifications, it backward compatible with a wireless router or a wireless access point. ● HP Mobile Broadband Module-A wireless wide area network (WWAN) device that provides access to information wherever mobile network operator service is not compatible with 802.11b and 802... of up to 54 Mbps and operates at a frequency of each mobile device communicates to a mobile network operator's base station. typically within 10 meters (approximately 33 feet) of 5 GHz. 1 Using wireless devices (select models only) Wireless technology transfers data across entire states, regions, ...
...the draft specifications, it backward compatible with a wireless router or a wireless access point. ● HP Mobile Broadband Module-A wireless wide area network (WWAN) device that provides access to information wherever mobile network operator service is not compatible with 802.11b and 802... of up to 54 Mbps and operates at a frequency of each mobile device communicates to a mobile network operator's base station. typically within 10 meters (approximately 33 feet) of 5 GHz. 1 Using wireless devices (select models only) Wireless technology transfers data across entire states, regions, ...
Wireless (Select Models Only) - Windows XP
Page 12
... generate a different key, or choose other advanced options. New technologies are less likely to know or remember the SSID to connect new devices to the network. Because wireless radio signals travel outside the network, other computers are being sent across it is a barrier that your ...network exists. Protecting your WLAN Because the WLAN standard was designed with built-in security Many wireless base stations, gateways, and routers provide built-in security features such as WEP does, WPA uses temporal key integrity protocol (TKIP) to ...
... generate a different key, or choose other advanced options. New technologies are less likely to know or remember the SSID to connect new devices to the network. Because wireless radio signals travel outside the network, other computers are being sent across it is a barrier that your ...network exists. Protecting your WLAN Because the WLAN standard was designed with built-in security Many wireless base stations, gateways, and routers provide built-in security features such as WEP does, WPA uses temporal key integrity protocol (TKIP) to ...