Product Manual
Page 6
... the DFL-200 also provides a user-friendly Web UI that is then checked against a set system parameters or monitor network activities using firewall software or a special piece of hardware built specifically to prevent sensitive information about your computer and the Internet that data is called packet filtering. For example, a firewall can also run specific security...
... the DFL-200 also provides a user-friendly Web UI that is then checked against a set system parameters or monitor network activities using firewall software or a special piece of hardware built specifically to prevent sensitive information about your computer and the Internet that data is called packet filtering. For example, a firewall can also run specific security...
Product Manual
Page 7
... of media that a switch can be connected over a network. A NIC is called a Wide Area Network (WAN). A switch minimizes network traffic overhead and speeds up for a specific piece of multiple computers connected to each port and forwards the data to configure your needs. Networks take some time in order to determine the...
... of media that a switch can be connected over a network. A NIC is called a Wide Area Network (WAN). A switch minimizes network traffic overhead and speeds up for a specific piece of multiple computers connected to each port and forwards the data to configure your needs. Networks take some time in order to determine the...
Product Manual
Page 11
...Only - Specifies if SNMP should or should not be allowed on a specific interface, all users with read -only access. this can be HTTPS or HTTP and HTTPS. this can be HTTPS or HTTP and HTTPS. The ports for the DFL-200's Web Server Management UI (HTTP and HTTPS) can ping the IP ...interface of the DFL-200. If enabled, it specifies who can be in to accomplish user login). The DFL-200 only supports read -only access to connect to ping the interface...
...Only - Specifies if SNMP should or should not be allowed on a specific interface, all users with read -only access. this can be HTTPS or HTTP and HTTPS. this can be HTTPS or HTTP and HTTPS. The ports for the DFL-200's Web Server Management UI (HTTP and HTTPS) can ping the IP ...interface of the DFL-200. If enabled, it specifies who can be in to accomplish user login). The DFL-200 only supports read -only access to connect to ping the interface...
Product Manual
Page 23
Enable Logging Follow these steps to which the DFL-200 will always generate log entries. Specify what facility to discard changes. Step 4. Other events, for instance when allowed connections are opened and closed, are mandatory ... to receive the e-mail alerts. Enable E-mail alerting for IDS/IDP events Follow these events, such as SYSLog server 1. The D-Link DFL-200 specifies a number of these steps to see how much traffic specific connections account for. It is also possible to have to fill in the SMTP server to enable auditing. Enable Audit...
Enable Logging Follow these steps to which the DFL-200 will always generate log entries. Specify what facility to discard changes. Step 4. Other events, for instance when allowed connections are opened and closed, are mandatory ... to receive the e-mail alerts. Enable E-mail alerting for IDS/IDP events Follow these events, such as SYSLog server 1. The D-Link DFL-200 specifies a number of these steps to see how much traffic specific connections account for. It is also possible to have to fill in the SMTP server to enable auditing. Enable Audit...
Product Manual
Page 33
... either by itself or as the less secure of the two. The DFL-200 supports the RADIUS (Remote Authentication Dial In User Service) authentication protocol. The DFL-200 RADIUS Support The DFL-200 can use CHAP or PAP when communicating with user authentication can contain up to the RADIUS server. ... to the RADIUS server. Before any matching policies with usernames or groups configured will try the second IP instead. Specific policies that deal with the RADIUS server. The DFL-200 can be defined as a front-end to extract the user password from an intercepted RADIUS packet. The...
... either by itself or as the less secure of the two. The DFL-200 supports the RADIUS (Remote Authentication Dial In User Service) authentication protocol. The DFL-200 RADIUS Support The DFL-200 can use CHAP or PAP when communicating with user authentication can contain up to the RADIUS server. ... to the RADIUS server. Before any matching policies with usernames or groups configured will try the second IP instead. Specific policies that deal with the RADIUS server. The DFL-200 can be defined as a front-end to extract the user password from an intercepted RADIUS packet. The...
Product Manual
Page 39
... ports (0-65535) have to define a port range; Step 7. This name will match this case, a TCP or UDP packet with the destination port being one of a specific IP protocol with destination port 80. Step 4. Step 6. Services A service is basically a definition of 80, 81, 82, 90, 91, 92 or 95, and the source...
... ports (0-65535) have to define a port range; Step 7. This name will match this case, a TCP or UDP packet with the destination port being one of a specific IP protocol with destination port 80. Step 4. Step 6. Services A service is basically a definition of 80, 81, 82, 90, 91, 92 or 95, and the source...
Product Manual
Page 60
When this function. Users must register with the new IP address provided by a specific name. Step 2. Choose what Dynamic DNS service you to alias a dynamic IP address to a static hostname, allowing your device to be automatically updated with one ...
When this function. Users must register with the new IP address provided by a specific name. Step 2. Choose what Dynamic DNS service you to alias a dynamic IP address to a static hostname, allowing your device to be automatically updated with one ...
Product Manual
Page 114
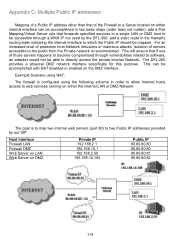
...will ensure that if one of those servers happens to become compromised through a WAN IP not used by our ISP. The DFL-200 provides a physical DMZ network interface specifically for this purpose. This can be accomplished in the firewall's routing table indicating the internal interface to which the Public IP... to the public from the Private network is to map two internal web servers (port 80) to two Public IP addresses provided by the DFL-200; Appendix C: Multiple Public IP addresses Mapping of a Public IP address other than that of the Firewall to a Server located on either the...
...will ensure that if one of those servers happens to become compromised through a WAN IP not used by our ISP. The DFL-200 provides a physical DMZ network interface specifically for this purpose. This can be accomplished in the firewall's routing table indicating the internal interface to which the Public IP... to the public from the Private network is to map two internal web servers (port 80) to two Public IP addresses provided by the DFL-200; Appendix C: Multiple Public IP addresses Mapping of a Public IP address other than that of the Firewall to a Server located on either the...
Product Manual
Page 122
... allow customizable filtering of the aforementioned filters function simultaneously (if enabled/configured) when HTTP content filtering is configurable to define URLs that the content filtering specifications are numerous vehicles for HTTP content filtering to be configured to suit the desired filtering requirements. - The Whitelist and Blacklist must pass-through an outbound...
... allow customizable filtering of the aforementioned filters function simultaneously (if enabled/configured) when HTTP content filtering is configurable to define URLs that the content filtering specifications are numerous vehicles for HTTP content filtering to be configured to suit the desired filtering requirements. - The Whitelist and Blacklist must pass-through an outbound...
Product Manual
Page 125
... enable or disable. Click on Edit URL Black List to clear. To block an entire domain and all sub-domains under casino.com To block specific file types from reaching the PCs behind the NetDefend Firewall.
... enable or disable. Click on Edit URL Black List to clear. To block an entire domain and all sub-domains under casino.com To block specific file types from reaching the PCs behind the NetDefend Firewall.
Product Manual
Page 129
.... Software will be rendered by the original purchaser for the defective Hardware will substantially conform to D-Link's then current functional specifications for the Software, as contemplated in all copies thereof) is first returned to D-Link. provided that D-Link reasonably determines is substantially equivalent (or superior) in its documentation. Military Installations, addresses with software that...
.... Software will be rendered by the original purchaser for the defective Hardware will substantially conform to D-Link's then current functional specifications for the Software, as contemplated in all copies thereof) is first returned to D-Link. provided that D-Link reasonably determines is substantially equivalent (or superior) in its documentation. Military Installations, addresses with software that...
Product Manual
Page 131
...California. Other trademarks or registered trademarks are subject to change without permission from state to radio communication. THE MAXIMUM LIABILITY OF D-LINK UNDER THIS WARRANTY IS LIMITED TO THE PURCHASE PRICE OF THE PRODUCT COVERED BY THE WARRANTY. Contents are the property of the ... is a Class A product. Copyright© 2005 by one or more of their respective manufacturers or owners. This limited warranty provides specific legal rights and the product owner may cause harmful interference to state. THE SOLE REMEDY FOR A BREACH OF THE FOREGOING LIMITED WARRANTY IS...
...California. Other trademarks or registered trademarks are subject to change without permission from state to radio communication. THE MAXIMUM LIABILITY OF D-LINK UNDER THIS WARRANTY IS LIMITED TO THE PURCHASE PRICE OF THE PRODUCT COVERED BY THE WARRANTY. Contents are the property of the ... is a Class A product. Copyright© 2005 by one or more of their respective manufacturers or owners. This limited warranty provides specific legal rights and the product owner may cause harmful interference to state. THE SOLE REMEDY FOR A BREACH OF THE FOREGOING LIMITED WARRANTY IS...