User Guide
Page 42
...list, certificates must be used during authentication. The fields in the system; The identity value can be used for enhanced security. Asterisks appear instead of characters for MD5-Challenge or LEAP authentication. see Certificates on the network and acts as the ... both Phase I and Phase II. Tunneled authentication area Tunneled authentication parameters are entered in Phase 2 of authentication, and after the secure tunnel has been established. Field Description Identity This is sent outside the protection of the encrypted tunnel. When used by MD5 and...
...list, certificates must be used during authentication. The fields in the system; The identity value can be used for enhanced security. Asterisks appear instead of characters for MD5-Challenge or LEAP authentication. see Certificates on the network and acts as the ... both Phase I and Phase II. Tunneled authentication area Tunneled authentication parameters are entered in Phase 2 of authentication, and after the secure tunnel has been established. Field Description Identity This is sent outside the protection of the encrypted tunnel. When used by MD5 and...
User Guide
Page 49
... WPA with every frame for improved security and includes a message integrity capability for authentication. WEP uses a single encryption key of the encryption methods. This field activates if you select WPA PSK as the mode. Image Kiosk 8560/8570 User's Guide Rev B 3/1/... Key (PSK) information entered in the field below. Select the desired encryption. • WEP: The least secure of either 40 or 104 bits. Field WPA Mode Encryption PSK pass-phrase Description This drop-down list contains the... the WEP Mgmt tab is selected. Note: The current Image Kiosk hardware does not support AES.
... WPA with every frame for improved security and includes a message integrity capability for authentication. WEP uses a single encryption key of the encryption methods. This field activates if you select WPA PSK as the mode. Image Kiosk 8560/8570 User's Guide Rev B 3/1/... Key (PSK) information entered in the field below. Select the desired encryption. • WEP: The least secure of either 40 or 104 bits. Field WPA Mode Encryption PSK pass-phrase Description This drop-down list contains the... the WEP Mgmt tab is selected. Note: The current Image Kiosk hardware does not support AES.
User Guide
Page 64
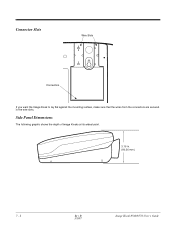
Connector Slots Wire Slots Connectors If you want the Image Kiosk to lay flat against the mounting surface, make sure that the wires from the connectors are secured in . (80.26 mm.) 7 - 2 Rev B Image Kiosk 8560/8570 User's Guide 3/1/07 Side Panel Dimensions The following graphic shows the depth of Image Kiosks at its widest point. 3.16 in the wire slots.
Connector Slots Wire Slots Connectors If you want the Image Kiosk to lay flat against the mounting surface, make sure that the wires from the connectors are secured in . (80.26 mm.) 7 - 2 Rev B Image Kiosk 8560/8570 User's Guide 3/1/07 Side Panel Dimensions The following graphic shows the depth of Image Kiosks at its widest point. 3.16 in the wire slots.