Datasheet
Page 1
... Socket 2 Comparing to traditional stacking, IP clustering eliminates the use of failure. Enhanced Security Measures We are always committed to providing the highest level of a device such as an IP camera or a VoIP phone to be connected to. LED Indicators 2. SFP (Mini-GBIC) Slot 5....Managed Switch 24 GE with 4 Combo SFP + 4 10GE SFP Plus GTL-2880 H/W Version: 1 LevelOne GTL-2880 is equipped with advanced features such as Single IP Management which are allowed to virtually stack GEL-1072, GTL-2880, GTP-2880, and GTL-5280 together and manage them as one logical unit through a single IP ...
... Socket 2 Comparing to traditional stacking, IP clustering eliminates the use of failure. Enhanced Security Measures We are always committed to providing the highest level of a device such as an IP camera or a VoIP phone to be connected to. LED Indicators 2. SFP (Mini-GBIC) Slot 5....Managed Switch 24 GE with 4 Combo SFP + 4 10GE SFP Plus GTL-2880 H/W Version: 1 LevelOne GTL-2880 is equipped with advanced features such as Single IP Management which are allowed to virtually stack GEL-1072, GTL-2880, GTP-2880, and GTL-5280 together and manage them as one logical unit through a single IP ...
Manual
Page 4
..., SWITCHES, ROUTERS, OR HUBS 5 CHAPTER 2 SYSTEM CONFIGURATION 7 2-1 SYSTEM INFORMATION ...7 2-1.1 Information ...7 2-1.2 Configuration...9 2-1.3 CPU Load ...10 2-2 TIME ...11 2-2.1 Manual...11 2-2.2 NTP ...13 2-3 ACCOUNT ...14 2-3.1 Users ...14 2-3.2 Privilege Level ...16 2-4 IP...18 2-4.1 IPV4 ...18 2-4.2 IPV6 ...20 2-5 SYSLOG ...21 2-5.1 Configuration...21 2-5.2 Log ...22 2-5.3 Detailed Log ...23 2-6 SNMP ...24 2-6.1 System ...24 2-6.2 Communities ...25 2-6.3 Users ...26 2-6.4 Groups...
..., SWITCHES, ROUTERS, OR HUBS 5 CHAPTER 2 SYSTEM CONFIGURATION 7 2-1 SYSTEM INFORMATION ...7 2-1.1 Information ...7 2-1.2 Configuration...9 2-1.3 CPU Load ...10 2-2 TIME ...11 2-2.1 Manual...11 2-2.2 NTP ...13 2-3 ACCOUNT ...14 2-3.1 Users ...14 2-3.2 Privilege Level ...16 2-4 IP...18 2-4.1 IPV4 ...18 2-4.2 IPV6 ...20 2-5 SYSLOG ...21 2-5.1 Configuration...21 2-5.2 Log ...22 2-5.3 Detailed Log ...23 2-6 SNMP ...24 2-6.1 System ...24 2-6.2 Communities ...25 2-6.3 Users ...26 2-6.4 Groups...
Manual
Page 9
...availability of your critical business applications, protect your sensitive information, and optimize your network system but configure and monitor the GTL-2880 by (RS-232) serial interface or through the web and Ethernet ports step-by-step. It provides the ideal ...Web-based Management" Chapter 2 "Maintenance" LED Mode button rule : press for entry level networking includes small business or enterprise application and helps you create a more effectively. GTL-2880 Managed Switches provide 28 ports in detail of hardware and software functions are shown as well as follows...
...availability of your critical business applications, protect your sensitive information, and optimize your network system but configure and monitor the GTL-2880 by (RS-232) serial interface or through the web and Ethernet ports step-by-step. It provides the ideal ...Web-based Management" Chapter 2 "Maintenance" LED Mode button rule : press for entry level networking includes small business or enterprise application and helps you create a more effectively. GTL-2880 Managed Switches provide 28 ports in detail of hardware and software functions are shown as well as follows...
Manual
Page 23
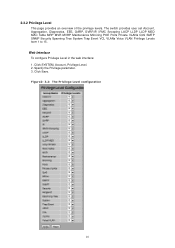
...groups, i.e. To type the password again. But others value need user privilege level 15. The allowed range is 1 to each group privilege level. that is 15, it can be same or greater than the group privilege level to have the access of the device. By default setting, most groups privilege... level 5 has the read-only access and privilege level 10 has the read-write access. If the privilege level value is granted the fully control of that group...
...groups, i.e. To type the password again. But others value need user privilege level 15. The allowed range is 1 to each group privilege level. that is 15, it can be same or greater than the group privilege level to have the access of the device. By default setting, most groups privilege... level 5 has the read-only access and privilege level 10 has the read-write access. If the privilege level value is granted the fully control of that group...
Manual
Page 24
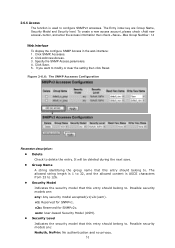
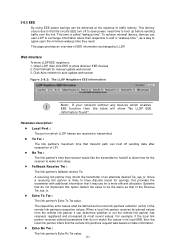
2-3.2 Privilege Level This page provides an overview of the privilege levels. Specify the Privilege parameter. 3. Figure2- 3.2: The Privilege Level configuration 16 Web Interface To configure Privilege Level in the web interface: 1. Click SYSTEM, Account, Privilege Level. 2. Click Save. The switch provides user set Account, Aggregation, Diagnostics, EEE, GARP, GVRP,IP, IPMC Snooping LACP LLDP LLDP MED MAC Table MRP MVR MVRP Maintenance Mirroring POE Ports Private VLANs QoS SMTP SNMP Security Spanning Tree System Trap Event VCL VLANs Voice VLAN Privilege Levels form 1 to 15 .
2-3.2 Privilege Level This page provides an overview of the privilege levels. Specify the Privilege parameter. 3. Figure2- 3.2: The Privilege Level configuration 16 Web Interface To configure Privilege Level in the web interface: 1. Click SYSTEM, Account, Privilege Level. 2. Click Save. The switch provides user set Account, Aggregation, Diagnostics, EEE, GARP, GVRP,IP, IPMC Snooping LACP LLDP LLDP MED MAC Table MRP MVR MVRP Maintenance Mirroring POE Ports Private VLANs QoS SMTP SNMP Security Spanning Tree System Trap Event VCL VLANs Voice VLAN Privilege Levels form 1 to 15 .
Manual
Page 25
...except 'VeriPHY'. Diagnostics: 'ping' and 'VeriPHY'. for the following description defines these privilege level groups in Maintenance. Privilege Levels Every group has an authorization Privilege level for clearing of a single module (e.g. Security: Authentication, System Access Management, Port (contains Dot1x... Save, Configuration Load and Firmware Load. In most cases, a privilege level group consists of statistics). User Privilege should be same or greater than one. Users, Privilege Levels and everything in details: System: Contact, Name, Location, Timezone, Log...
...except 'VeriPHY'. Diagnostics: 'ping' and 'VeriPHY'. for the following description defines these privilege level groups in Maintenance. Privilege Levels Every group has an authorization Privilege level for clearing of a single module (e.g. Security: Authentication, System Access Management, Port (contains Dot1x... Save, Configuration Load and Firmware Load. In most cases, a privilege level group consists of statistics). User Privilege should be same or greater than one. Users, Privilege Levels and everything in details: System: Contact, Name, Location, Timezone, Log...
Manual
Page 29
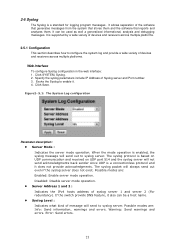
..., Syslog. 2. 2-5 Syslog The Syslog is a connectionless protocol and it . 4. Click Save. If the switch provide DNS feature, it also can be a host name. Syslog Level : Indicates what kind of message will not send acknowledgments back sender since UDP is a standard for logging program messages .
..., Syslog. 2. 2-5 Syslog The Syslog is a connectionless protocol and it . 4. Click Save. If the switch provide DNS feature, it also can be a host name. Syslog Level : Indicates what kind of message will not send acknowledgments back sender since UDP is a standard for logging program messages .
Manual
Page 30
Display the log information. Warning: Warning level of the system log entry. Message It will display the log record by manual, others for ...To evoke the auto-refresh icon then the device will refresh the log automatically. Level level of the system log entry. Time It will display the log detail message. All: All levels. ID ID (>= 1) of the system log entry. The message of the ...system log entry. Upper right icon (Refresh, clear...) You can click them by device time. Error: Error level of the system log. Click Syslog, Log. 2. The following...
Display the log information. Warning: Warning level of the system log entry. Message It will display the log record by manual, others for ...To evoke the auto-refresh icon then the device will refresh the log automatically. Level level of the system log entry. Time It will display the log detail message. All: All levels. ID ID (>= 1) of the system log entry. The message of the ...system log entry. Upper right icon (Refresh, clear...) You can click them by device time. Error: Error level of the system log. Click Syslog, Log. 2. The following...
Manual
Page 34
... belong to . The allowed string length is 1 to 32, and the allowed content is ASCII characters from 33 to 126. Security Level Indicates the security model that this entry should belong to . Possible security models are : None: No authentication protocol. That means it must first ... SNMP, Users. 2. To create a new UserName account, please check button, and enter the user information then check . The value of security level cannot be deleted during the next save. User Name A string identifying the user name that this entry should belong to configure SNMPv3 user.
... belong to . The allowed string length is 1 to 32, and the allowed content is ASCII characters from 33 to 126. Security Level Indicates the security model that this entry should belong to . Possible security models are : None: No authentication protocol. That means it must first ... SNMP, Users. 2. To create a new UserName account, please check button, and enter the user information then check . The value of security level cannot be deleted during the next save. User Name A string identifying the user name that this entry should belong to configure SNMPv3 user.
Manual
Page 35
.... Possible privacy protocols are: None: No privacy protocol. SHA: An optional flag to indicate that this entry should belong to 32. The value of security level cannot be modified if entry already exists. For MD5 authentication protocol, the allowed string length is 8 to . protocol.
.... Possible privacy protocols are: None: No privacy protocol. SHA: An optional flag to indicate that this entry should belong to 32. The value of security level cannot be modified if entry already exists. For MD5 authentication protocol, the allowed string length is 8 to . protocol.
Manual
Page 39
... or clear the setting then click Reset. . v2c: Reserved for SNMPv1. Possible security models are Group Name, Security Model and Security level. usm: User-based Security Model (USM). Security Level Indicates the security model that this entry should belong to configure SNMPv3 accesses. The Entry index key are : any: Any security...
... or clear the setting then click Reset. . v2c: Reserved for SNMPv1. Possible security models are Group Name, Security Model and Security level. usm: User-based Security Model (USM). Security Level Indicates the security model that this entry should belong to configure SNMPv3 accesses. The Entry index key are : any: Any security...
Manual
Page 42
... and privacy. Authentication Protocol: You can set DES encryption for authentication. Authentication Password: The length of message will send to Security Level. Possible modes are three kinds of ' Privacy Password ' is restricted to 8 - 32. 34 The length of 'SHA Authentication Password' is restricted to...choices. Community / Security Name: The length of "Community / Security Name" string is restricted to 1-32. Security Level: Indicates what kind of 'MD5 Authentication Password' is restricted to 8 - 32. Error: Send errors. Security...
... and privacy. Authentication Protocol: You can set DES encryption for authentication. Authentication Password: The length of message will send to Security Level. Possible modes are three kinds of ' Privacy Password ' is restricted to 8 - 32. 34 The length of 'SHA Authentication Password' is restricted to...choices. Community / Security Name: The length of "Community / Security Name" string is restricted to 1-32. Security Level: Indicates what kind of 'MD5 Authentication Password' is restricted to 8 - 32. Error: Send errors. Security...
Manual
Page 54
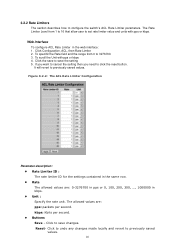
... Limiters The section describes how to click the reset button. It will revert to save the setting 5. Click to previously saved values. The Rate Limiter Level from 0 to save changes. Click to undo any changes made locally and revert to set rate limiter value and units with pps or kbps 4 . Figure...
... Limiters The section describes how to click the reset button. It will revert to save the setting 5. Click to previously saved values. The Rate Limiter Level from 0 to save changes. Click to undo any changes made locally and revert to set rate limiter value and units with pps or kbps 4 . Figure...
Manual
Page 112
... 0.0 is to be used when referencing locations on water/sea/ocean. 104 This datum pair is meaningful even outside a building, and represents ground level at the main entrance. Map Datum : The Map Datum is detected, will temporarily speed up the transmission of the LLDPDU to start ... to specify the direction to either East of the prime meridian or West of 4 digits. Inside a building, 0.0 represents the floor level associated with inappropriate knowledge of Altitude defined by the vertical datum specified. The recommended value is 4 times, given that can come with ground...
... 0.0 is to be used when referencing locations on water/sea/ocean. 104 This datum pair is meaningful even outside a building, and represents ground level at the main entrance. Map Datum : The Map Datum is detected, will temporarily speed up the transmission of the LLDPDU to start ... to specify the direction to either East of the prime meridian or West of 4 digits. Inside a building, 0.0 represents the floor level associated with inappropriate knowledge of Altitude defined by the vertical datum specified. The recommended value is 4 times, given that can come with ground...
Manual
Page 115
... specific VLAN. for the specified application type. Guest Voice - for the voice media. This application type should not be mapped to use of eight priority levels (0 through 63). Video Signalling (conditional) - Untagged indicates that require a different policy for the guest voice signalling than for use in RFC 2475. Adding a new...
... specific VLAN. for the specified application type. Guest Voice - for the voice media. This application type should not be mapped to use of eight priority levels (0 through 63). Video Signalling (conditional) - Untagged indicates that require a different policy for the guest voice signalling than for use in RFC 2475. Adding a new...
Manual
Page 119
for the video media. Policy : Policy indicates that only the IEEE 802.1D priority level is significant and the default PVID of the eight priority levels (0 through 63). 111 Untagged: The device is the DSCP value to be an intended use by IEEE 802.1Q-2003. Contain one of this application ...
for the video media. Policy : Policy indicates that only the IEEE 802.1D priority level is significant and the default PVID of the eight priority levels (0 through 63). 111 Untagged: The device is the DSCP value to be an intended use by IEEE 802.1Q-2003. Contain one of this application ...
Manual
Page 120
... a more efficient allocation. A receiving link partner may use LLDP to exchange information about their respective tx and rx "wakeup time ", as a way to have discrete levels for the receiver to show discover EEE devices 2. This page provides an overview of an alternate desired Tw_sys_tx. Click Refresh for auto-update web screen...
... a more efficient allocation. A receiving link partner may use LLDP to exchange information about their respective tx and rx "wakeup time ", as a way to have discrete levels for the receiver to show discover EEE devices 2. This page provides an overview of an alternate desired Tw_sys_tx. Click Refresh for auto-update web screen...
Manual
Page 153
High flexibility in a QoS control list (QCL). Click Configuration, QoS, Port Classification 2. It will revert to select QoS class, DP Level, PCP and DEI parameters 3. Scroll to previously saved values Figure 3-14.1: The QoS Configuration 145 The QoS classification looks for all switch ports. and the ...
High flexibility in a QoS control list (QCL). Click Configuration, QoS, Port Classification 2. It will revert to select QoS class, DP Level, PCP and DEI parameters 3. Scroll to previously saved values Figure 3-14.1: The QoS Configuration 145 The QoS classification looks for all switch ports. and the ...
Manual
Page 154
...an acronym for Drop Eligible Indicator. bit field in order to configure the mode and/or mapping. DSCP Based : Click to Qos class & DP level = 1 , 1 Result will find (a) Packet all past, and (b) packets all drop 146 PCP & DEI = 0 0 , via configured map to ...Enable DSCP Based QoS Ingress Port Classification. Buttons: Save - PCP : PCP is a one to a Drop Precedence Level (DP level), which the configuration below applies. QoS class : Controls the default QoS class, i.e., the QoS class for frames not classified in any other way....
...an acronym for Drop Eligible Indicator. bit field in order to configure the mode and/or mapping. DSCP Based : Click to Qos class & DP level = 1 , 1 Result will find (a) Packet all past, and (b) packets all drop 146 PCP & DEI = 0 0 , via configured map to ...Enable DSCP Based QoS Ingress Port Classification. Buttons: Save - PCP : PCP is a one to a Drop Precedence Level (DP level), which the configuration below applies. QoS class : Controls the default QoS class, i.e., the QoS class for frames not classified in any other way....
Manual
Page 163
3-14.5 Port Tag Remarking The Section provides user to get an overview of QoS class and DP level. Tag Remarking Mode : To scroll to select the tag remarking mode for this port. Web Interface To display the QoS Port Tag Remarking in ... remarking. Mode : Shows the tag remarking mode for the settings contained in the web interface: 1. Mapped: Use mapped versions of QoS class and DP level. Buttons: 155
3-14.5 Port Tag Remarking The Section provides user to get an overview of QoS class and DP level. Tag Remarking Mode : To scroll to select the tag remarking mode for this port. Web Interface To display the QoS Port Tag Remarking in ... remarking. Mode : Shows the tag remarking mode for the settings contained in the web interface: 1. Mapped: Use mapped versions of QoS class and DP level. Buttons: 155