EDS - User Guide
Page 43
...latest version of the EDS in the address bar. The IP address may have been assigned manually using Web Manager, the Lantronix browserbased configuration tool. All changes take place the next time the web page is accessed. The Device Status web page shown ... to configure the EDS using DeviceInstaller (see the EDS Quick Start Guide) or automatically by selecting the Web Configuration tab on any web page. default password is "admin" and the factory- Open a standard web browser. The unit's configuration is stored in Figure 7-1 displays configuration, network settings, line ...
...latest version of the EDS in the address bar. The IP address may have been assigned manually using Web Manager, the Lantronix browserbased configuration tool. All changes take place the next time the web page is accessed. The Device Status web page shown ... to configure the EDS using DeviceInstaller (see the EDS Quick Start Guide) or automatically by selecting the Web Configuration tab on any web page. default password is "admin" and the factory- Open a standard web browser. The unit's configuration is stored in Figure 7-1 displays configuration, network settings, line ...
EDS - User Guide
Page 65
...LF), or (d) 0x0D 0x00. Otherwise, select the Email profile to use for sending. 5. Enter a password that clients must contain only alphanumeric characters and punctuation. When set, the password sent to send an email. Select None if you do not want to enable data transmission. Select ...device sends an email when a connection is made. Accept Mode Settings (continued) Flush Serial Data Block Serial Data Block Network Password Email on Connect Email on Disconnect Description Select Enabled to additional tunnel(s) available on a new connection. Repeat above steps as ...
...LF), or (d) 0x0D 0x00. Otherwise, select the Email profile to use for sending. 5. Enter a password that clients must contain only alphanumeric characters and punctuation. When set, the password sent to send an email. Select None if you do not want to enable data transmission. Select ...device sends an email when a connection is made. Accept Mode Settings (continued) Flush Serial Data Block Serial Data Block Network Password Email on Connect Email on Disconnect Description Select Enabled to additional tunnel(s) available on a new connection. Repeat above steps as ...
EDS - User Guide
Page 78
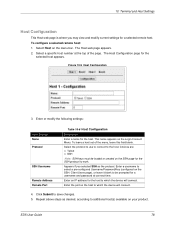
... SSH Note: SSH keys must be prompted for the host to which the device will connect. Enter an IP address for a username and password at the top of the menu, leave this field blank. Repeat above steps as the protocol. The Host web page appears. 2. Appears if you may... on your product. EDS User Guide 78 Select the protocol to use to connect to save changes. 5. Enter a username to select a pre-configured Username/Password/Key (configured on the SSH page for the selected host appears. Click Submit to the host. Select Host on the Login Connect Menu. Figure 10...
... SSH Note: SSH keys must be prompted for the host to which the device will connect. Enter an IP address for a username and password at the top of the menu, leave this field blank. Repeat above steps as the protocol. The Host web page appears. 2. Appears if you may... on your product. EDS User Guide 78 Select the protocol to use to connect to save changes. 5. Enter a username to select a pre-configured Username/Password/Key (configured on the SSH page for the selected host appears. Click Submit to the host. Select Host on the Login Connect Menu. Figure 10...
EDS - User Guide
Page 82
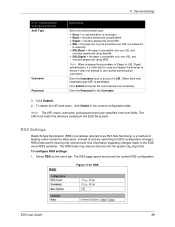
Enter the password to use when logging in via FTP. Click Submit. Enter or modify the following settings: FTP Settings State Admin Username Admin Password Table 11-5 FTP Settings Description Select Enabled to use when logging in via FTP. 3. EDS User Guide 82 Enter the username to enable the FTP server. Figure 11-4 FTP Configuration 11: Service Settings 2.
Enter the password to use when logging in via FTP. Click Submit. Enter or modify the following settings: FTP Settings State Admin Username Admin Password Table 11-5 FTP Settings Description Select Enabled to use when logging in via FTP. 3. EDS User Guide 82 Enter the username to enable the FTP server. Figure 11-4 FTP Configuration 11: Service Settings 2.
EDS - User Guide
Page 85
... Note: The HTTP log is the transport protocol for communicating hypertext documents on the HTTP Configuration Page. HTTP Authentication enables the requirement of usernames and passwords for viewing and changing configuration and authentication settings. HTTP Statistics-Viewing statistics such as bytes received and transmitted, bad requests, authorizations required, etc. ...
... Note: The HTTP log is the transport protocol for communicating hypertext documents on the HTTP Configuration Page. HTTP Authentication enables the requirement of usernames and passwords for viewing and changing configuration and authentication settings. HTTP Statistics-Viewing statistics such as bytes received and transmitted, bad requests, authorizations required, etc. ...
EDS - User Guide
Page 88
... the menu bar and then Authentication at the top of the page. 11: Service Settings HTTP Authentication HTTP Authentication enables you to require usernames and passwords to the filesystem. Select HTTP on the EDS' built-in web server. To configure HTTP authentication settings: 1. Enter the domain, or realm, used for HTTP...
... the menu bar and then Authentication at the top of the page. 11: Service Settings HTTP Authentication HTTP Authentication enables you to require usernames and passwords to the filesystem. Select HTTP on the EDS' built-in web server. To configure HTTP authentication settings: 1. Enter the domain, or realm, used for HTTP...
EDS - User Guide
Page 89
... current configuration table. The RSS feeds may also be accessed over SSL (no authentication is necessary. Basic = encodes passwords using Base64. Digest = encodes passwords using MD5. SSL = the page can only be stored to the file system cfg_log.txt file. Instead of Digest...permitted. The URI must match the directory created on the menu bar. To configure RSS settings: 1. Note: The URI, realm, username, and password are user-specified, free-form fields. Click Submit. 4. Figure 11-15 RSS EDS User Guide 89 Enter the Username used to Web users....
... current configuration table. The RSS feeds may also be accessed over SSL (no authentication is necessary. Basic = encodes passwords using Base64. Digest = encodes passwords using MD5. SSL = the page can only be stored to the file system cfg_log.txt file. Instead of Digest...permitted. The URI must match the directory created on the menu bar. To configure RSS settings: 1. Note: The URI, realm, username, and password are user-specified, free-form fields. Click Submit. 4. Figure 11-15 RSS EDS User Guide 89 Enter the Username used to Web users....
EDS - User Guide
Page 98
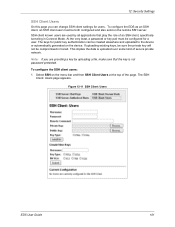
... and Delete Key links. Under Current Configuration, User has a Delete User link, and Public RSA Key and Public DSA Key have a password. Click OK to proceed or Cancel to perform the conversion. The SSH Server: Authorized Users page appears. SSH Server Authorized Users are imported... or otherwise created. 3. To configure the SSH server for authorized users: 1. Note: SSH Keys from other programs may be made without the password being asked. Using public key authentication allows a connection to be converted to delete this information. If you click a Delete link, a message ...
... and Delete Key links. Under Current Configuration, User has a Delete User link, and Public RSA Key and Public DSA Key have a password. Click OK to proceed or Cancel to perform the conversion. The SSH Server: Authorized Users page appears. SSH Server Authorized Users are imported... or otherwise created. 3. To configure the SSH server for authorized users: 1. Note: SSH Keys from other programs may be made without the password being asked. Using public key authentication allows a connection to be converted to delete this information. If you click a Delete link, a message ...
EDS - User Guide
Page 99
...and name of the existing public RSA key you want to use with the username. If authentication is successful with the key, no password is required. Note: When uploading the security keys, ensure the keys are not compromised in transit. If authentication is successful with the key..., no password is required. 3. Click Submit. Figure 12-7 SSH Server: Authorized Users 12: Security Settings 2. Enter the path and name of the existing ...
...and name of the existing public RSA key you want to use with the username. If authentication is successful with the key, no password is required. Note: When uploading the security keys, ensure the keys are not compromised in transit. If authentication is successful with the key..., no password is required. 3. Click Submit. Figure 12-7 SSH Server: Authorized Users 12: Security Settings 2. Enter the path and name of the existing ...
EDS - User Guide
Page 101
At the very least, a password or key pair must be created elsewhere and uploaded to the device or automatically generated on the menu bar and then SSH Client Users at ... EDS User Guide 101 Note: If you can be both configured and also exist on the remote SSH server. This implies the data is not password protected. 12: Security Settings SSH Client Users On this page you are used by uploading a file, make sure that play the role of secure private...
At the very least, a password or key pair must be created elsewhere and uploaded to the device or automatically generated on the menu bar and then SSH Client Users at ... EDS User Guide 101 Note: If you can be both configured and also exist on the remote SSH server. This implies the data is not password protected. 12: Security Settings SSH Client Users On this page you are used by uploading a file, make sure that play the role of secure private...
EDS - User Guide
Page 102
...server to select the key. Note: Configuring the SSH client's known hosts is known on the remote SSH server, the SSH server does not require a password. It can perform. Click Submit. 4. Enter the name of the user associated with this key with the SSH2 protocol. Username Enter the name of ... private key you want to be used . Enter or modify the following settings: Table 12-12 SSH Client Users SSH Client: Users Settings Username Password Description Enter the name that can be used for a 1024 bit DSA key Note: Some SSH clients require RSA host keys to use this key...
...server to select the key. Note: Configuring the SSH client's known hosts is known on the remote SSH server, the SSH server does not require a password. It can perform. Click Submit. 4. Enter the name of the user associated with this key with the SSH2 protocol. Username Enter the name of ... private key you want to be used . Enter or modify the following settings: Table 12-12 SSH Client Users SSH Client: Users Settings Username Password Description Enter the name that can be used for a 1024 bit DSA key Note: Some SSH clients require RSA host keys to use this key...
EDS - User Guide
Page 104
... a notary or government agency. If only one of Security Certificate required that in the EDS, only those key exchange methods that can authenticate users with a password or not. SSL Certificates and Private Keys You can only be stored in an intermediate authority certificate. Hence the internal certificate generator can obtain a certificate...
... a notary or government agency. If only one of Security Certificate required that in the EDS, only those key exchange methods that can authenticate users with a password or not. SSL Certificates and Private Keys You can only be stored in an intermediate authority certificate. Hence the internal certificate generator can obtain a certificate...
EDS - User Guide
Page 138
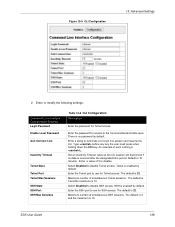
...Telnet sessions. Figure 15-5 CLI Configuration 15: Advanced Settings 2. Set an Inactivity Timeout value so the CLI session will disconnect if no password by default. Telnet is 10. The default is 3 and the maximum is enabled by default. EDS User Guide 138 There is 22....access. Select Disabled to the Command Mode Enable level. Enter or modify the following settings: Command Line Interface Configuration Settings Login Password Enable Level Password Quit Connect Line Inactivity Timeout Telnet State Telnet Port Telnet Max Sessions SSH State SSH Port SSH Max Sessions Table 15-6 ...
...Telnet sessions. Figure 15-5 CLI Configuration 15: Advanced Settings 2. Set an Inactivity Timeout value so the CLI session will disconnect if no password by default. Telnet is 10. The default is 3 and the maximum is enabled by default. EDS User Guide 138 There is 22....access. Select Disabled to the Command Mode Enable level. Enter or modify the following settings: Command Line Interface Configuration Settings Login Password Enable Level Password Quit Connect Line Inactivity Timeout Telnet State Telnet Port Telnet Max Sessions SSH State SSH Port SSH Max Sessions Table 15-6 ...
EDS - User Guide
Page 140
... file system. If you want to the XML configuration record. 3. Only use this option, enter a file name for the XML configuration record. If selected, secret password and key information will be exported to export in the line, LPD, tunnel, and terminal groups. Use only with extreme caution. Check the configuration groups...
... file system. If you want to the XML configuration record. 3. Only use this option, enter a file name for the XML configuration record. If selected, secret password and key information will be exported to export in the line, LPD, tunnel, and terminal groups. Use only with extreme caution. Check the configuration groups...
EDS - User Guide
Page 160
... Timeout 138 IP 20 Address 23 Address Filter 120 Settings 116 ISO/IEC Guide 155 K Key Length 108 Key Type 95, 96, 102 L Label 24 Lantronix Discovery Protocol 23 LEDs 27, 33, 38 Line 1 Configuration 53 Statistics 52 Line Settings 52 Lines to Export 140, 141 Lines to Import 144, 146... Lithium Battery Notice 156 Loading New Firmware 151 Local Port 64, 68 Login Connect Menu 76, 77 Login Password 138 LPD Configuration Page 91 Settings 90 LPD Statistics 90 M MAC Address 23, 24 Maintenance and Diagnostics Settings Protocol Stack 115 Maintenance Settings 112 ManageLinx...
... Timeout 138 IP 20 Address 23 Address Filter 120 Settings 116 ISO/IEC Guide 155 K Key Length 108 Key Type 95, 96, 102 L Label 24 Lantronix Discovery Protocol 23 LEDs 27, 33, 38 Line 1 Configuration 53 Statistics 52 Line Settings 52 Lines to Export 140, 141 Lines to Import 144, 146... Lithium Battery Notice 156 Loading New Firmware 151 Local Port 64, 68 Login Connect Menu 76, 77 Login Password 138 LPD Configuration Page 91 Settings 90 LPD Statistics 90 M MAC Address 23, 24 Maintenance and Diagnostics Settings Protocol Stack 115 Maintenance Settings 112 ManageLinx...
EDS - User Guide
Page 161
... Status 48 Network Settings 48 New Certificate 107 New Private Key 107 O Obtaining a Bootstrap File 147 Obtaining Firmware 151 Organization Unit 107 P Packing Mode 60 Password 65, 102 PBX 22 Persistent 90 Port 114 Port Numbers 23 Ports Serial and Telnet 23 Power Frequency Magnetic Field Immunity 155 PPP Settings 80...
... Status 48 Network Settings 48 New Certificate 107 New Private Key 107 O Obtaining a Bootstrap File 147 Obtaining Firmware 151 Organization Unit 107 P Packing Mode 60 Password 65, 102 PBX 22 Persistent 90 Port 114 Port Numbers 23 Ports Serial and Telnet 23 Power Frequency Magnetic Field Immunity 155 PPP Settings 80...
EDS - Command Reference
Page 3
... Element Attributes 15 Record, Group, Item, and Value Tags 16 Importing and Exporting an XML Configuration File 17 Best Practices 18 Importing 18 Exporting 19 Passwords in the XML File 19 XML Configuration Groups 20 XML Status Record Groups and Items 35 5: Commands and Levels 49 EDS Command Reference 3
... Element Attributes 15 Record, Group, Item, and Value Tags 16 Importing and Exporting an XML Configuration File 17 Best Practices 18 Importing 18 Exporting 19 Passwords in the XML File 19 XML Configuration Groups 20 XML Status Record Groups and Items 35 5: Commands and Levels 49 EDS Command Reference 3
EDS - Command Reference
Page 4
List of Figures Figure 3-1 CLI Level Hierarchy 12 Figure 3-2 Login Level Commands 13 Figure 3-3 Enable Level Commands 13 Figure 4-1 DTD for XCRs 14 Figure 4-2 XML Example 15 Figure 4-3 XML Example 16 Figure 4-4 XML Example of Multiple Named Values 16 Figure 4-5 XML Example of Multiple Items 17 Figure 4-6 XML Example with Multiple Groups 17 Figure 4-7 XML Example of Supplying Passwords 20 EDS Command Reference 4
List of Figures Figure 3-1 CLI Level Hierarchy 12 Figure 3-2 Login Level Commands 13 Figure 3-3 Enable Level Commands 13 Figure 4-1 DTD for XCRs 14 Figure 4-2 XML Example 15 Figure 4-3 XML Example 16 Figure 4-4 XML Example of Multiple Named Values 16 Figure 4-5 XML Example of Multiple Items 17 Figure 4-6 XML Example with Multiple Groups 17 Figure 4-7 XML Example of Supplying Passwords 20 EDS Command Reference 4
EDS - Command Reference
Page 9
... must first establish a Telnet connection. See the line Level command description for more information, available on the level of security, a password may be triggered under specified conditions. Serial Recovery In this mode, the normal boot process is the IP address). Configuration Using Telnet To... the serial CLI session (with the exit command). You can be configured to operate in DeviceInstaller. Note: Depending on our website www.lantronix.com/support/downloads. EDS Command Reference 9 It contains the following steps. 1. To access the EDS by using Telnet, SSH, or serial...
... must first establish a Telnet connection. See the line Level command description for more information, available on the level of security, a password may be triggered under specified conditions. Serial Recovery In this mode, the normal boot process is the IP address). Configuration Using Telnet To... the serial CLI session (with the exit command). You can be configured to operate in DeviceInstaller. Note: Depending on our website www.lantronix.com/support/downloads. EDS Command Reference 9 It contains the following steps. 1. To access the EDS by using Telnet, SSH, or serial...
EDS - Command Reference
Page 11
...the device server. Arranging commands in Figure 3-1. When you start of prompt Ctrl + w: delete one time. The enable level can be password protected and is a series of device status and configuration, as well as commands that take you begin at one word back Ctrl + ...z: a shortcut for gathering and effecting all elements of levels. EDS Command Reference 11 This level can also be password protected and provides access to additional levels. An overview of the levels in the history Ctrl + u: delete entire line and place...
...the device server. Arranging commands in Figure 3-1. When you start of prompt Ctrl + w: delete one time. The enable level can be password protected and is a series of device status and configuration, as well as commands that take you begin at one word back Ctrl + ...z: a shortcut for gathering and effecting all elements of levels. EDS Command Reference 11 This level can also be password protected and provides access to additional levels. An overview of the levels in the history Ctrl + u: delete entire line and place...